In the following program, the return value of a call to the method retrieveFromDB is a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
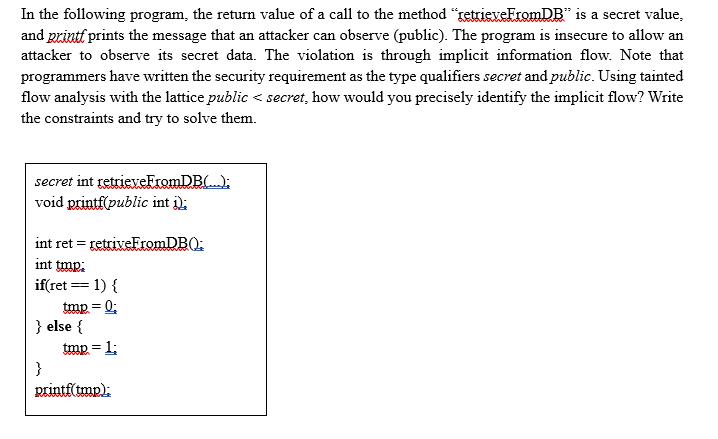
In the following program, the return value of a call to the method "retrieveFromDB" is a secret value, and printf prints the message that an attacker can observe (public). The program is insecure to allow an attacker to observe its secret data. The violation is through implicit information flow. Note that programmers have written the security requirement as the type qualifiers secret and public. Using tainted flow analysis with the lattice public < secret, how would you precisely identify the implicit flow? Write the constraints and try to solve them. secret int retrieveFromDB(...). void printf(public int i). int ret = retriveFromDB(). int tmp: if(ret == 1){ tmp =Q; } else { } tmp = 1; printf(tmp): In the following program, the return value of a call to the method "retrieveFromDB" is a secret value, and printf prints the message that an attacker can observe (public). The program is insecure to allow an attacker to observe its secret data. The violation is through implicit information flow. Note that programmers have written the security requirement as the type qualifiers secret and public. Using tainted flow analysis with the lattice public < secret, how would you precisely identify the implicit flow? Write the constraints and try to solve them. secret int retrieveFromDB(...). void printf(public int i). int ret = retriveFromDB(). int tmp: if(ret == 1){ tmp =Q; } else { } tmp = 1; printf(tmp):
Expert Answer:
Answer rating: 100% (QA)
The program snippet displayed in the image contains a security issue due to an implicit information flow This refers to a situation where information ... View the full answer

Related Book For 

Automate The Boring Stuff With Python Practical Programming For Total Beginners
ISBN: 9781593275990
1st Edition
Authors: Al Sweigart
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
You will design and implement your own data class. The class will store data that has been read as user input from the keyboard (see Getting Input below), and provide necessary operations. As the...
-
Name the types of consumer decision-making processes. List some products you have bought using each type. Have you ever bought a product on impulse? If so, describe the circumstances.
-
Briefly summarize three modes an SME can use to enter foreign markets.
-
Sorry Im late, sighs Fatima as she flops into a chair next to you at a local coffee shop. Something came up at work. Lately, theres always something going wrong. Fatima is part of your study group...
-
A batch of 100 mobile phones contains 5 smartphones. What is the probability that a sample of three phones will have (a) no smartphones? (b) all smartphones? (c) at least one smartphone? (d) at least...
-
If a 6%, 10-year, $800,000 bond is issued at face and interest is paid annually, what is the amount of the interest payment at the end of the first period?
-
Explain the principles of process safety engineering in the context of chemical process industries, including hazard identification, risk assessment methodologies, and mitigation strategies for...
-
John and Sandy Ferguson got married eight years ago and have a seven-year-old daughter, Samantha. In 2020, John worked as a computer technician at a local university earning a salary of $152,000, and...
-
what are the two examples of the means internationalisation?
-
Determine whether the ordered pair (8,5) is a solution to the following system. 5x-4y = 20 2x + 1 = 3y
-
Meyer Appliance Company makes cooling fans. The firm's income statement is as follows: Sales (7,000 fans at $20) $140,000 Less: Variable costs (7,000 fans at $8) 56,000 Fixed costs 44,000 Earnings...
-
Type of Bond Yield 1- year 0.2% 2- year 0.3 3- year 0.5 Using the expectations theory, compute the expected one-year interest rates in (a)the second year (Year 2 only) and (b)the third year (Year...
-
Fill in the missing values: Do not enter commas , % or $ signs. Remember to use 2 decimal places for all of your answers. Calculating Cost of Food Sold Food Sales $ 1 1 5 , 2 5 0 . 0 0 Opening...
-
The resolution of a telescope is ultimately limited by the diameter of its objective lens or mirror. A typical amateur astronomer's telescope may have a 6 . 0 5 in diameter mirror. What is the...
-
On April 2, 2017, AlJalai Inc. acquired a new machine. The cost was $180,000 with a residual value of $20,000 at the end of its estimated useful lifetime of 5 years. Instructions Prepare a complete...
-
Marc Company assembles products from a group of interconnecting parts. The company produces some of the parts and buys some from outside vendors. The vendor for Part X has just increased its price by...
-
What does an absolute path start with?
-
What does spam[-1] evaluate to?
-
Briefly describe the differences between the webbrowser, requests, BeautifulSoup, and selenium modules.
-
A fertilizer producing company purchases nitrates, phosphates, potash, and an inert chalk base and produces four different fertilizers A, B,C, and D. The cost of these nitrates, phosphates, potash,...
-
Heavy fuel oil, initially semisolid at $15^{\circ} \mathrm{C}$ is to be heated and pumped through a $15 \mathrm{~cm}$ diameter (inside) pipe at the rate of $20000 \mathrm{~kg} / \mathrm{h}$. The pipe...
-
The topological optimization is discussed in chapter 1. Here, we will consider a topological optimization problem for a chemical process plant. The layout of the chemical process plant has been shown...

Study smarter with the SolutionInn App