In this case, you are asked to attack an RSA encrypted message. Imagine being the attacker:...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
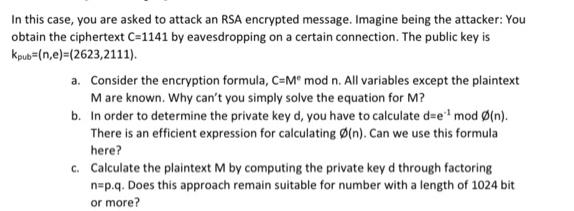
In this case, you are asked to attack an RSA encrypted message. Imagine being the attacker: You obtain the ciphertext C=1141 by eavesdropping on a certain connection. The public key is Kpub=(n,e)=(2623,2111). a. Consider the encryption formula, C=M mod n. All variables except the plaintext M are known. Why can't you simply solve the equation for M? b. In order to determine the private key d, you have to calculate d=e mod (n). There is an efficient expression for calculating (n). Can we use this formula here? c. Calculate the plaintext M by computing the private key d through factoring n=p.q. Does this approach remain suitable for number with a length of 1024 bit or more? In this case, you are asked to attack an RSA encrypted message. Imagine being the attacker: You obtain the ciphertext C=1141 by eavesdropping on a certain connection. The public key is Kpub=(n,e)=(2623,2111). a. Consider the encryption formula, C=M mod n. All variables except the plaintext M are known. Why can't you simply solve the equation for M? b. In order to determine the private key d, you have to calculate d=e mod (n). There is an efficient expression for calculating (n). Can we use this formula here? c. Calculate the plaintext M by computing the private key d through factoring n=p.q. Does this approach remain suitable for number with a length of 1024 bit or more?
Expert Answer:

Related Book For 

Principles of Auditing and Other Assurance Services
ISBN: 978-0078025617
19th edition
Authors: Ray Whittington, Kurt Pany
Posted Date:
Students also viewed these programming questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
On December 1, 2016, Masipag sold land in exchange for a P180,000 non-interest, 1-year promissory note. The 10% interest rate was going market rate for similar notes. Masipag had paid P66,000 to...
-
Ouellette & Associates records adjusting entries on an annual basis. The company has the following information available on accruals that must be recorded for the year ended December 31, 2014: 1....
-
If x and y are nonzero vectors in Rn and A = xyT, then the row echelon form of A will have exactly one nonzero row. In this case answer true if the statement is always true and false otherwise. In...
-
In a heat engine the heat always flows from (a) The higher-temperature region to the lower-temperature one and produces no work (b) The lower-temperature region to the higher-temperature one and...
-
Thorpe Company is a wholesale distributor of professional equipment and supplies. The companys sales have averaged about $900,000 annually for the three-year period 20072009. The firms total assets...
-
You can afford a $250 per month car payment. You\'ve found a 5year loan at 5% interest. How big of a loan can you afford?
-
Letang Company has three divisions (R, S, and T), organized as decentralized profit centers. Division R produces the basic chemical Ranbax (in multiples of 1,000 pounds) and transfers it to Divisions...
-
If the Fed orders an expansionary monetary policy, describe what will happen to the following variables relative to what would have happened without the policy: The money supply Interest rates...
-
The temperature inside a Carnot refrigerator is5.85C. What is the high temperature, Th, in Celsius needed to give this refrigerator a coefficient of performance of 10.5?
-
A 870-g quantity of a substance is at its melting point of -117.9C in the liquid state. The heat of fusion of ethanol is 1.63 105 J/kg, the molecular mass is 32.8 g/mol, and the ideal gas constant is...
-
Google's market price in mid-2008 by challenging the forecasts implicit in the market price. Tease out those forecasts using the abnormal earnings growth valuation model. In mid-2008, Google traded...
-
Imagine that you just completed a course in Financial Management for Entrepreneurs where you learned various techniques and tools in financial analysis. Your uncle Ben wants your advice regarding an...
-
Search for an article in the internet about applied economic and make an analysis. Follow the format: Title: By: (source) Screenshot of the Article/Website: Summary of the Article:...
-
Compute the 4-points DFT of the sequence x[n]-{2, 1) using the direct transformation formula. Compute also DFT, and compare the final results with input[n] sequence.
-
In Problem 8.43, determine the smallest value of for which the rod will not fall out of the pipe. IA -3 in.-
-
The firm of Wilson and Wiener (WW), CPAs, has had requests from a number of clients and prospective clients to perform various types of services. Please reply as to whether the appropriate...
-
Auditors consider financial statement assertions to identify appropriate audit procedures. For items a through f, match each assertion with the statement that most closely approximates its meaning....
-
Describe the additional documentation requirements of Generally Accepted Government Auditing Standards.
-
An electronic instrument is to be isolated from a panel that vibrates at frequencies ranging from \(25 \mathrm{~Hz}\) to \(35 \mathrm{~Hz}\). It is estimated that at least 80 percent vibration...
-
An exhaust fan, having a small unbalance, weights \(800 \mathrm{~N}\) and operates at a speed of \(600 \mathrm{rpm}\). It is desired to limit the response to a transmissibility of 2.5 as the fan...
-
The armature of a variable-speed electric motor, of mass \(200 \mathrm{~kg}\), has an unbalance due to manufacturing errors. The motor is mounted on an isolator having a stiffness of \(10 \mathrm{kN}...

Study smarter with the SolutionInn App