In this discussion board post, you will analyze how Zero Trust can help protect against malicious...
Fantastic news! We've Found the answer you've been seeking!
Question:

Transcribed Image Text:
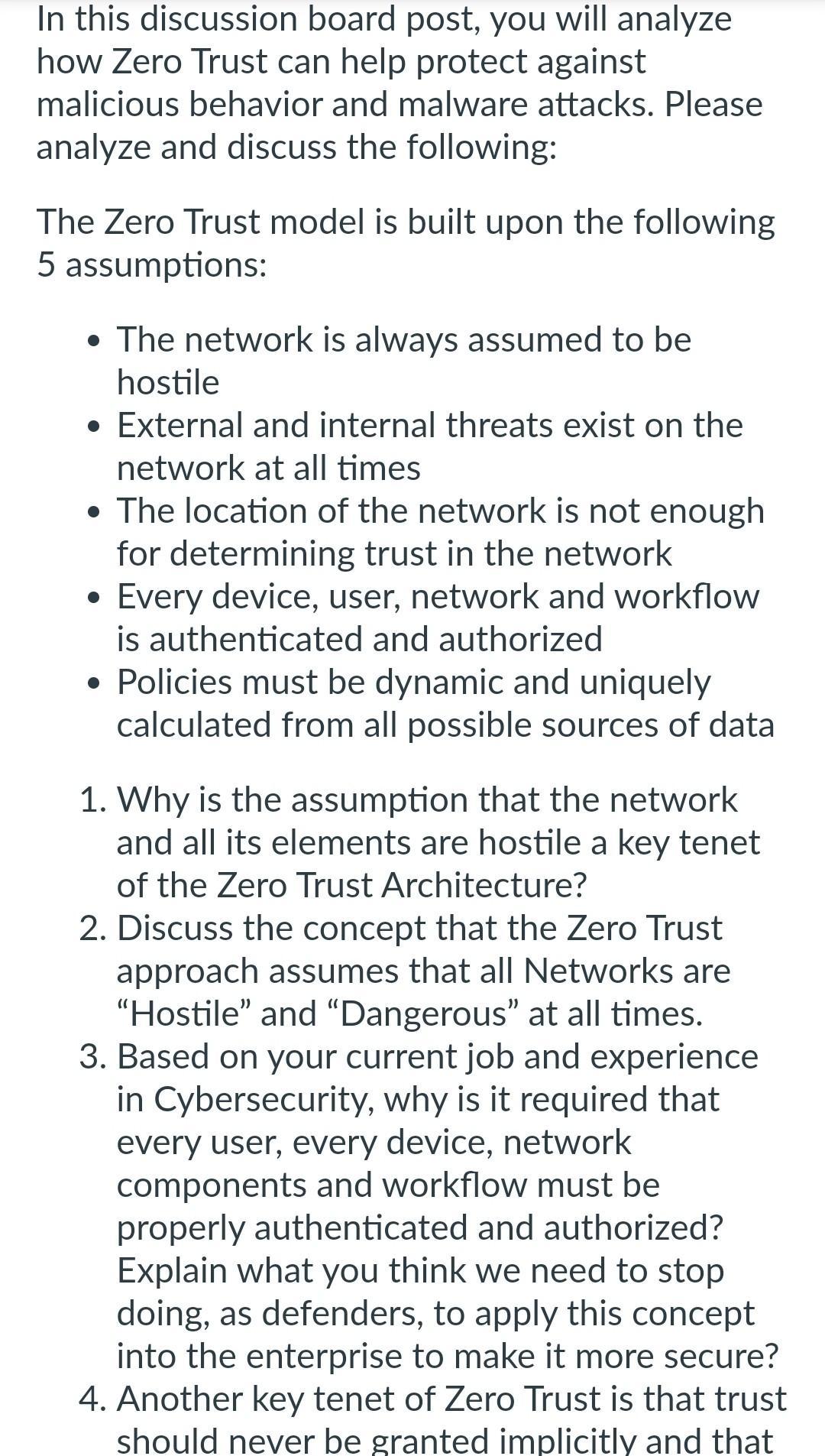
In this discussion board post, you will analyze how Zero Trust can help protect against malicious behavior and malware attacks. Please analyze and discuss the following: The Zero Trust model is built upon the following 5 assumptions: The network is always assumed to be hostile • External and internal threats exist on the network at all times The location of the network is not enough for determining trust in the network • Every device, user, network and workflow is authenticated and authorized • Policies must be dynamic and uniquely calculated from all possible sources of data 1. Why is the assumption that the network and all its elements are hostile a key tenet of the Zero Trust Architecture? 2. Discuss the concept that the Zero Trust approach assumes that all Networks are "Hostile" and "Dangerous" at all times. 3. Based on your current job and experience in Cybersecurity, why is it required that every user, every device, network components and workflow must be properly authenticated and authorized? Explain what you think we need to stop doing, as defenders, to apply this concept into the enterprise to make it more secure? 4. Another key tenet of Zero Trust is that trust should never be granted implicitly and that any trust given needs to be constantly evaluated. Discuss this concept and explain the value and the pros and cons associated with this approach. In this discussion board post, you will analyze how Zero Trust can help protect against malicious behavior and malware attacks. Please analyze and discuss the following: The Zero Trust model is built upon the following 5 assumptions: The network is always assumed to be hostile • External and internal threats exist on the network at all times The location of the network is not enough for determining trust in the network • Every device, user, network and workflow is authenticated and authorized • Policies must be dynamic and uniquely calculated from all possible sources of data 1. Why is the assumption that the network and all its elements are hostile a key tenet of the Zero Trust Architecture? 2. Discuss the concept that the Zero Trust approach assumes that all Networks are "Hostile" and "Dangerous" at all times. 3. Based on your current job and experience in Cybersecurity, why is it required that every user, every device, network components and workflow must be properly authenticated and authorized? Explain what you think we need to stop doing, as defenders, to apply this concept into the enterprise to make it more secure? 4. Another key tenet of Zero Trust is that trust should never be granted implicitly and that any trust given needs to be constantly evaluated. Discuss this concept and explain the value and the pros and cons associated with this approach.
Expert Answer:
Answer rating: 100% (QA)
In this discussion board post you will analyze how Zero Trust can help protect against malicious behaviour and malware attacks Please analyze and discuss the following The Zero Trust model is built up... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
What advantages do traditional banks have over non-banks? Alternately, what competitive advantages do non-banks have?
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
In the Young's double slit experiment, interference fringes are formed using Na-light of 589 nm and 589.5 nm. Obtain the region on the screen where the fringe pattern will disappear. You may assume...
-
A coin is placed 13.0 cm from the axis of a rotating turntable of variable speed. When the speed of the turntable is slowly increased, the coin remains fixed on the turntable until a rate of 38.0 rpm...
-
The growth of social media has spawned many platforms dedicated to customer reviews and complaintsfor example, Angi, which profiles local service companies, contractors, and professionalsor Yelp, a...
-
4. LEGISLATION Bills originate in congressional committees and go from there to the full House of Representatives or Senate. If both houses pass the bill, the legislation normally must go to a...
-
Nona Inc., which produces a single product, has prepared the following standard cost sheet for one unit of the product. Direct materials (8 pounds at $2.50 per pound) ....$20 Direct labor (3 hours at...
-
Financial analysis can be defined as the process of assessing the financial condition of a firm. It can be very useful in understanding the financial position of a company. There are varieties of...
-
1. Which process should VBB choose to produce?? 2. How much would VBP be willing to pay for the testing that is currently offered, for each batch?? 3. Would we be considered a perfect test, at twice...
-
A system uses the Stop-and Wait ARQ Protocol to send 1 Mbits ofdata from sender to receiver.(a) If each frame carries L=1 Kbits of data, how many frames arerequired to send 1 million bits of data? A...
-
Discuss the advancements in photovoltaic (PV) technology, focusing on the development of high-efficiency solar cells, such as perovskite and tandem cells, and their implications for the evolution of...
-
Suppose you have just purchased a 10-year General Electric 100 million zero-coupon bond at 8% YTM. The exchange rate is USD1.1/EUR. What will be your rate of return if one year from now the YTM on...
-
For the purpose of a cash receipts budget, we are not primarily thinking terms of sales in a month, but we see the amount of cash received in a month comes from multiple months. That cash received...
-
How does the application of advanced statistical mechanics and quantum thermodynamics contribute to a deeper understanding of phase transitions and critical phenomena in complex systems, particularly...
-
Select two techniques for forecasting human resources demand and discuss in detail. In your response,explain whether the technique would be more appropriate for a small or a large organization, and...
-
complete the asset disposal account for the sake of the Kia picanto on 32 May
-
The landing gear of an aircraft with: mass of 2000 kg the spring-mass-damper system Consider that the runway surface is y(t) = 0.2 cos 157.08t stiffness of the spring is 5 x 105 N/m. What is the...
-
Which algorithm was the first public-key encryption algorithm developed (in 1977) and published for commercial use? a. 3DES b. Blowfish c. RSA d. Diffle-Hellman
-
I. Define what a project milestone is and the importance of establishing them early in the project process. II. Comprehend the understanding that start and end dates can be added as needed.
-
Explain the numerous factors that project planners must consider about what they need to include in a comprehensive workplan.
-
Prepare a consolidated balance sheet from the following details as at 31 March 2006. During the year, Pa sold goods which had cost 1,900 to Daughter for 2,800. None of these goods had been sold by...
-
The following information relates to Heather Limited and its subsidiary, Thistle*Limited. 1. Heather Limited Retained profits as at 31 March 2008 700,000. 80,000 ordinary shares were purchased in...
-
Draw up a consolidated balance sheet as at 31 December 2007 from the following: At the balance sheet date, Child owes Parent 3,200. During the year Parent sold goods which had cost 6,000 to Child for...

Study smarter with the SolutionInn App


