Java network assignment and want to apologize for not having a starter code of this assignment. Step
Fantastic news! We've Found the answer you've been seeking!
Question:
Java network assignment and want to apologize for not having a starter code of this assignment.
Transcribed Image Text:
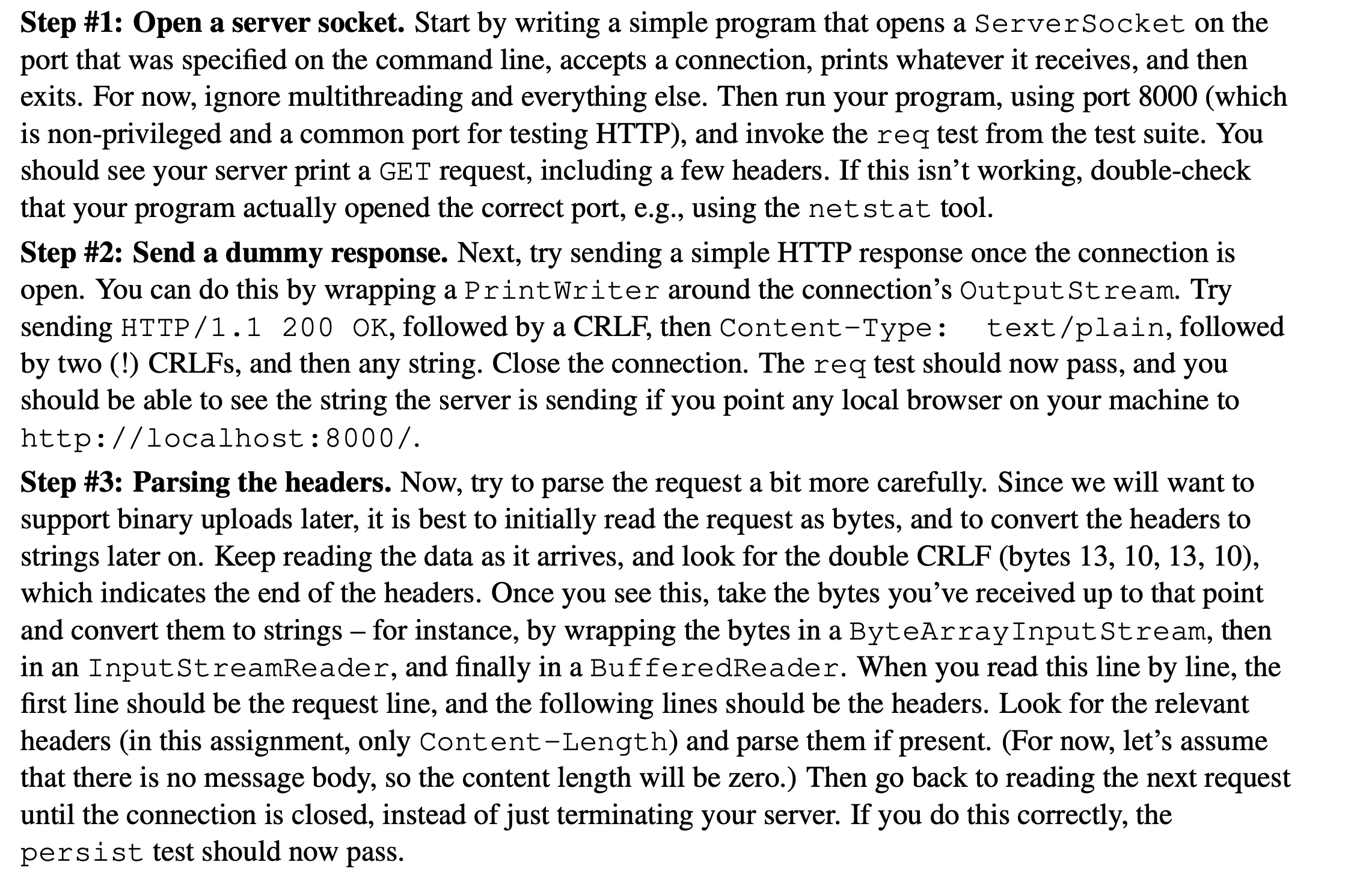
Step #1: Open a server socket. Start by writing a simple program that opens a ServerSocket on the port that was specified on the command line, accepts a connection, prints whatever it receives, and then exits. For now, ignore multithreading and everything else. Then run your program, using port 8000 (which is non-privileged and a common port for testing HTTP), and invoke the req test from the test suite. You should see your server print a GET request, including a few headers. If this isn't working, double-check that your program actually opened the correct port, e.g., using the netstat tool. Step #2: Send a dummy response. Next, try sending a simple HTTP response once the connection is open. You can do this by wrapping a Print Writer around the connection's OutputStream. Try sending HTTP/1.1 200 OK, followed by a CRLF, then Content-Type: text/plain, followed by two (!) CRLFs, and then any string. Close the connection. The req test should now pass, and you should be able to see the string the server is sending if you point any local browser on your machine to http://localhost:8000/. Step #3: Parsing the headers. Now, try to parse the request a bit more carefully. Since we will want to support binary uploads later, it is best to initially read the request as bytes, and to convert the headers to strings later on. Keep reading the data as it arrives, and look for the double CRLF (bytes 13, 10, 13, 10), which indicates the end of the headers. Once you see this, take the bytes you've received up to that point and convert them to strings - for instance, by wrapping the bytes in a ByteArrayInputStream, then in an InputStreamReader, and finally in a BufferedReader. When you read this line by line, the first line should be the request line, and the following lines should be the headers. Look for the relevant headers (in this assignment, only Content-Length) and parse them if present. (For now, let's assume that there is no message body, so the content length will be zero.) Then go back to reading the next request until the connection is closed, instead of just terminating your server. If you do this correctly, the persist test should now pass. Step #1: Open a server socket. Start by writing a simple program that opens a ServerSocket on the port that was specified on the command line, accepts a connection, prints whatever it receives, and then exits. For now, ignore multithreading and everything else. Then run your program, using port 8000 (which is non-privileged and a common port for testing HTTP), and invoke the req test from the test suite. You should see your server print a GET request, including a few headers. If this isn't working, double-check that your program actually opened the correct port, e.g., using the netstat tool. Step #2: Send a dummy response. Next, try sending a simple HTTP response once the connection is open. You can do this by wrapping a Print Writer around the connection's OutputStream. Try sending HTTP/1.1 200 OK, followed by a CRLF, then Content-Type: text/plain, followed by two (!) CRLFs, and then any string. Close the connection. The req test should now pass, and you should be able to see the string the server is sending if you point any local browser on your machine to http://localhost:8000/. Step #3: Parsing the headers. Now, try to parse the request a bit more carefully. Since we will want to support binary uploads later, it is best to initially read the request as bytes, and to convert the headers to strings later on. Keep reading the data as it arrives, and look for the double CRLF (bytes 13, 10, 13, 10), which indicates the end of the headers. Once you see this, take the bytes you've received up to that point and convert them to strings - for instance, by wrapping the bytes in a ByteArrayInputStream, then in an InputStreamReader, and finally in a BufferedReader. When you read this line by line, the first line should be the request line, and the following lines should be the headers. Look for the relevant headers (in this assignment, only Content-Length) and parse them if present. (For now, let's assume that there is no message body, so the content length will be zero.) Then go back to reading the next request until the connection is closed, instead of just terminating your server. If you do this correctly, the persist test should now pass. Step #1: Open a server socket. Start by writing a simple program that opens a ServerSocket on the port that was specified on the command line, accepts a connection, prints whatever it receives, and then exits. For now, ignore multithreading and everything else. Then run your program, using port 8000 (which is non-privileged and a common port for testing HTTP), and invoke the req test from the test suite. You should see your server print a GET request, including a few headers. If this isn't working, double-check that your program actually opened the correct port, e.g., using the netstat tool. Step #2: Send a dummy response. Next, try sending a simple HTTP response once the connection is open. You can do this by wrapping a Print Writer around the connection's OutputStream. Try sending HTTP/1.1 200 OK, followed by a CRLF, then Content-Type: text/plain, followed by two (!) CRLFs, and then any string. Close the connection. The req test should now pass, and you should be able to see the string the server is sending if you point any local browser on your machine to http://localhost:8000/. Step #3: Parsing the headers. Now, try to parse the request a bit more carefully. Since we will want to support binary uploads later, it is best to initially read the request as bytes, and to convert the headers to strings later on. Keep reading the data as it arrives, and look for the double CRLF (bytes 13, 10, 13, 10), which indicates the end of the headers. Once you see this, take the bytes you've received up to that point and convert them to strings - for instance, by wrapping the bytes in a ByteArrayInputStream, then in an InputStreamReader, and finally in a BufferedReader. When you read this line by line, the first line should be the request line, and the following lines should be the headers. Look for the relevant headers (in this assignment, only Content-Length) and parse them if present. (For now, let's assume that there is no message body, so the content length will be zero.) Then go back to reading the next request until the connection is closed, instead of just terminating your server. If you do this correctly, the persist test should now pass.
Expert Answer:
Answer rating: 100% (QA)
It seems you are working on a network programming assignment in Java to create a simple HTTP server Below is a basic outline of how you can implement ... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Skip to main content Lab 11: A Web Server The goal of this lab is to write a simple, but functional, web server that is capable of sending files to a web browser on request. The web server must...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
In a bygone day, airlines issued discount tickets to students who would be willing to fly on a particular day, with no notice, at a discounted price, one needed to show proof of being of student. The...
-
What impulse occurs when the same force of 10 N acts on the cart for twice the time?
-
Add the given vectors by drawing the appropriate resultant.
-
Petitioner Atlantic Marine Company was a contractor located in Virginia. It entered into a subcontract with J-Crew Management, Inc., a Texas corporation, that contained a forum-selection clause...
-
Presidio, Inc. produces one model of mountain bike. Partial information for the company follows: Required: 1. Complete Presidios cost data table. 2. Calculate Presidios contribution margin ratio and...
-
Assume that Twigs has hired you as a database consultant to develop it's operational database having the three tables described at the end of Chapter 6. Assume that Twigs personnel are the owner, an...
-
Draw the decision table for the below given scenario. Omntel will give the discount on the mobile phones purchase through sales at their outlets in Oman. A customer who has postpaid account will get...
-
we will be looking for:- four major types of planned change: human process interventions, techno-structural interventions, human resource management interventions, and strategic change interventions?...
-
Organizational Behavior Scholarly Journals only. Find an article that focuses on organizational behavior topics such as leadership, or decision making in your chosen field ( human resources. For...
-
Why would a leader demonstrating emotional intelligence be especially motivating to followers? How is self-monitoring related to emotional intelligence? How are these concepts (self-monitoring and...
-
Identify the components of an information system using the five-component framework and provide a brief summary of each. Explain Porter's five forces model. Management information systems...
-
Analyze how Filtronic used Arena to eliminate its time-consuming struggles with its internally developed product development tool that made tracking, maintaining, and releasing products slow and...
-
Trifles Ltd acquired 280,000 shares in Bamburg Ltd on 01 July 2019 and as a result Trifles Ltd has a control of 80% in Bamburg. The purchased consideration transferred by Trifles Ltd in exchange of...
-
Citing a scientific article, explain in your own words, how DNA fingerprinting has been used in forensic science to solve crimes and why it may not always be accurate or effective.
-
Alice has been on a long trip without checking her e-mail. She then finds out that she has lost some e-mails or attachments her friends claim they have sent to her. What can be the problem?
-
Draw a bar chart to compare the different downloading data rates of common modems.
-
In Figure 17.5, do we have a loop problem if we change each hub in the LANs to a link-layer switch? Figure 17.5 Figure 17.5 Loop problem in a learning switch a. Station A sends a frame to station D...
-
a. Show that the mean-squared forecast error \(E\left[\left(\hat{y}_{T+1}-y_{T+1} ight)^{2} \mid I_{T} ight]\) for a forecast \(\hat{y}_{T+1}\), that depends only on past information \(I_{T}\), can...
-
Consider the AR(1) model \(y_{t}=\delta+\theta y_{t-1}+e_{t}\) where \(|\theta|)=0\) and \(\operatorname{var}\left(e_{t} \mid I_{t-1} ight)=\sigma^{2}\). Let \(\bar{y}_{-1}=\sum_{t=2}^{T} y_{t}...
-
Consider a stationary model that combines the \(\operatorname{AR}(2)\) model \(y_{t}=\delta+\theta_{1} y_{t-1}+\theta_{2} y_{t-2}+e_{t}\) with an \(\mathrm{AR}(1)\) error model \(e_{t}=ho...

Study smarter with the SolutionInn App


