Let f {0, 1}2 {0, 1} be the function defined by f(x, y) = xy. Design...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
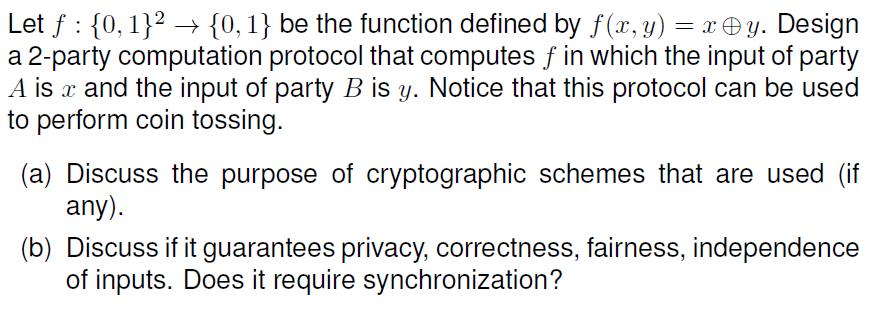
Let f {0, 1}2 {0, 1} be the function defined by f(x, y) = xy. Design a 2-party computation protocol that computes f in which the input of party A is x and the input of party B is y. Notice that this protocol can be used to perform coin tossing. (a) Discuss the purpose of cryptographic schemes that are used (if any). (b) Discuss if it guarantees privacy, correctness, fairness, independence of inputs. Does it require synchronization? Let f {0, 1}2 {0, 1} be the function defined by f(x, y) = xy. Design a 2-party computation protocol that computes f in which the input of party A is x and the input of party B is y. Notice that this protocol can be used to perform coin tossing. (a) Discuss the purpose of cryptographic schemes that are used (if any). (b) Discuss if it guarantees privacy, correctness, fairness, independence of inputs. Does it require synchronization?
Expert Answer:

Related Book For 

Discrete and Combinatorial Mathematics An Applied Introduction
ISBN: 978-0201726343
5th edition
Authors: Ralph P. Grimaldi
Posted Date:
Students also viewed these programming questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
In a test on 2000 electric bulbs, it was found that the life of a particular make was normally distributed with an average life of 2040 hos & S.D of bohos Estimate the ne of likely to burn for it...
-
Oak Creek Company is preparing its budgeted income statement for 2016. Relevant data pertaining to its sales, production, and direct materials budgets are found in D10-12. In addition, Oak Creek...
-
Two cards are drawn at random from a pack of cards with replacement. Let the random variable .V be the number of cards drawn from the heart suit. (a) Construct the probability mass function. (b)...
-
What is the frequency range of a seismometer?
-
State whether the following provisions in a note impair or preclude negotiability, the instrument in each instance being otherwise in proper form. Answer each statement with either the word...
-
You have been hired by FAB Corporation, a manufacturer of a new garage door opening device. The President has asked you to review the company's costing system to control manufacturing overhead costs....
-
What are the main issues in designing organizational structure? List and explain at least three issues.
-
A bottle filling machine is designed so that when it is operating properly it fills bottles with a mean of 64 ounces and a standard deviation of 0.73 ounces. To test themachine to see if it is...
-
Strategize the best location for new hubs for the service arm and the best location and set up strategies for the manufacturing arm. In your calculations, consider methodologies such as: Weighted...
-
For this problem, how do we get the values used for fixed asset turnover ratio? I understand that it is total revenue/net fixed asset. For total revenue we are given $3,269,404 but I am not sure what...
-
subject :business research method Research methodology is the specific procedures or techniques used to identify, select, process, and analyze information about a topic. In a research paper, the...
-
Better Mousetraps has developed a new trap. It can go into production for an initial investment in equipment of $5.4 million. The equipment will be depreciated straight-line over 6 years, but, in...
-
There is a need to write a program which computes the cube of the number entered from the keyboard. The number can be any number between 0 and 9. For example, if the number entered from the keyboard...
-
In what ways does a well-designed enterprise search software vary from popular search engines (e.g., Bing, DuckDuckGo, and Google)?
-
For each of the following pairs of statements determine whether the proposed negation is correct. If correct, determine which is true: the original statement or the proposed negation. If the proposed...
-
Let T = (V, E) be a balanced complete m-ary tree of height h 2. If T has leaves and bh-1 internal vertices at level h - 1, explain why = mh-1 + (m - 1)bh-1.
-
One bag contains 15 identical (in shape) coins - nine of silver and six of gold. A second bag contains 16 more of these coins - six silver and 10 gold. Bruno reaches in and selects one coin from the...
-
In Fig. 1.69, find the equivalent spring constant of the system in the direction of \(\theta\). k1 00000 K2 00000 K3 00000 k12 FIGURE 1.69 A system of linear and torsional springs connected to...
-
A machine of mass \(m=500 \mathrm{~kg}\) is mounted on a simply supported steel beam of length \(l=2 \mathrm{~m}\) having a rectangular cross section (depth \(=0.1 \mathrm{~m}\), width \(=1.2...
-
A cantilever beam of length \(L\) and Young's modulus \(E\) is subjected to a bending force at its free end. Compare the spring constants of beams with cross sections in the form of a solid circle...

Study smarter with the SolutionInn App