how to solve this problems in cryptography? Problems 1. (15 Points) There is nothing exclusively special about
Fantastic news! We've Found the answer you've been seeking!
Question:
how to solve this problems in cryptography? 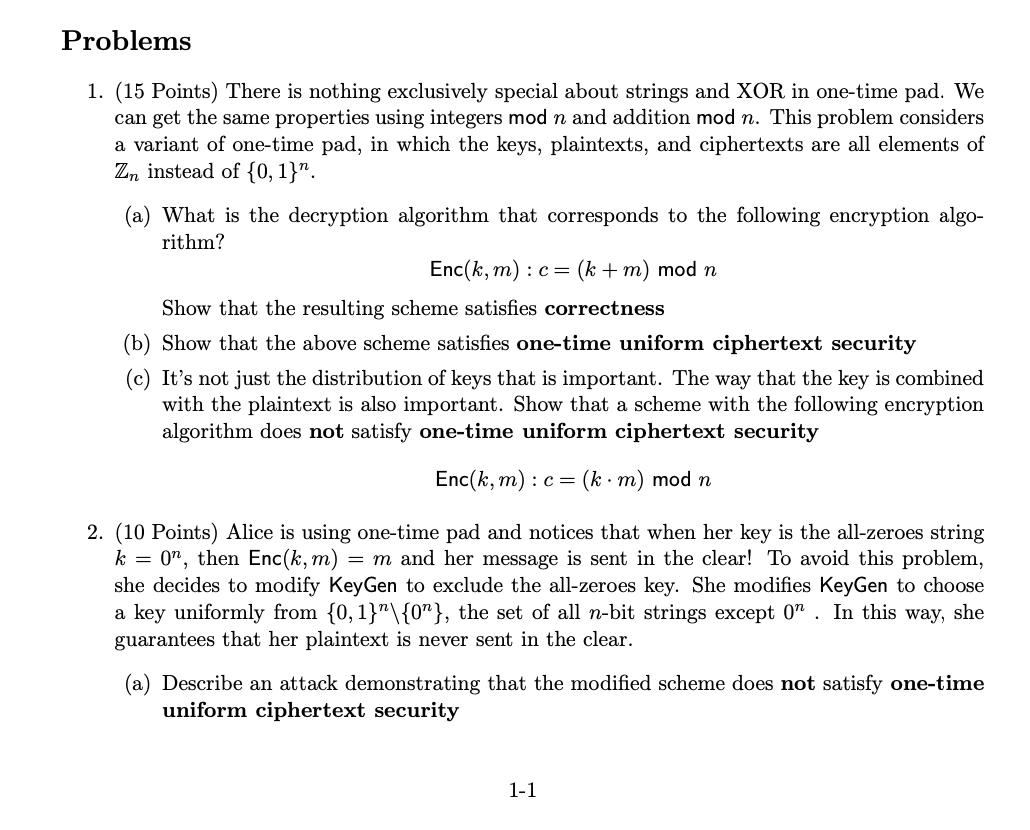

Transcribed Image Text:
Problems 1. (15 Points) There is nothing exclusively special about strings and XOR in one-time pad. We can get the same properties using integers mod n and addition mod n. This problem considers a variant of one-time pad, in which the keys, plaintexts, and ciphertexts are all elements of Zn instead of {0, 1}. (a) What is the decryption algorithm that corresponds to the following encryption algo- rithm? Enc(k, m) : c= (k + m) mod n Show that the resulting scheme satisfies correctness (b) Show that the above scheme satisfies one-time uniform ciphertext security (c) It's not just the distribution of keys that is important. The way that the key is combined with the plaintext is also important. Show that a scheme with the following encryption algorithm does not satisfy one-time uniform ciphertext security Enc(k, m) : c= (km) mod n 2. (10 Points) Alice is using one-time pad and notices that when her key is the all-zeroes string k = 0", then Enc(k, m) = m and her message is sent in the clear! To avoid this problem, she decides to modify KeyGen to exclude the all-zeroes key. She modifies KeyGen to choose a key uniformly from {0,1}"\{0"}, the set of all n-bit strings except on. In this way, she guarantees that her plaintext is never sent in the clear. (a) Describe an attack demonstrating that the modified scheme does not satisfy one-time uniform ciphertext security 1-1 Problems 1. (15 Points) There is nothing exclusively special about strings and XOR in one-time pad. We can get the same properties using integers mod n and addition mod n. This problem considers a variant of one-time pad, in which the keys, plaintexts, and ciphertexts are all elements of Zn instead of {0, 1}. (a) What is the decryption algorithm that corresponds to the following encryption algo- rithm? Enc(k, m) : c= (k + m) mod n Show that the resulting scheme satisfies correctness (b) Show that the above scheme satisfies one-time uniform ciphertext security (c) It's not just the distribution of keys that is important. The way that the key is combined with the plaintext is also important. Show that a scheme with the following encryption algorithm does not satisfy one-time uniform ciphertext security Enc(k, m) : c= (km) mod n 2. (10 Points) Alice is using one-time pad and notices that when her key is the all-zeroes string k = 0", then Enc(k, m) = m and her message is sent in the clear! To avoid this problem, she decides to modify KeyGen to exclude the all-zeroes key. She modifies KeyGen to choose a key uniformly from {0,1}"\{0"}, the set of all n-bit strings except on. In this way, she guarantees that her plaintext is never sent in the clear. (a) Describe an attack demonstrating that the modified scheme does not satisfy one-time uniform ciphertext security 1-1
Expert Answer:
Answer rating: 100% (QA)
1 a The dec ryption algorithm for this scheme is Dec k c m c k mod n To see why this scheme is correct note that Enc k m k m mod n Therefore c Enc k m k m mod n Thus Dec k c c k mod n k m k mod n m mo... View the full answer

Related Book For 

Understanding Basic Statistics
ISBN: 978-1111827021
6th edition
Authors: Charles Henry Brase, Corrinne Pellillo Brase
Posted Date:
Students also viewed these accounting questions
-
Let x be a random variable representing percentage change in neighborhood population in the past few years, and let y be a random variable representing crime rate (crimes per 1000 population). A...
-
Let x be a random variable that represents white blood cell count per cubic milliliter of whole blood. Assume that x has a distribution that is approximately normal, with mean μ = 7500...
-
Let X be a random variable taking on values a1, a2, . . . , pr with probabilities p1, p2, . . . , pr and with E(X) = μ. Define the spread of X as follows: This, like the standard deviation, is a...
-
A quality inspector selects a sample of 12 items at random from a collection of 60 items, of which 18 have excellent quality, 25 have good quality. 12 have poor quality, and 5 are defective. (a) What...
-
An analyst must decide between two different forecasting teclmiques for weekly sales of inline skates: a linear trend equation and the naive approach. The linear trend equation is yt = 124 + 2t, and...
-
In one or two paragraphs, explain the difference between a network access provider and an Internet service provider.
-
What is whirling?
-
Tapper Construction Company is composed of two divisions: (1) Home Construction and (2) Commercial Construction. The Home Construction Division is in the process of building 12 houses and the...
-
A novel space station design has been proposed to allow for experiments that leverage rotational motion to simulate low-gravity environments. This could, for instance, let astronauts conduct...
-
Reba Dixon is a fifth-grade school teacher who earned a salary of $38,000 in 2019. She is 45 years old and has been divorced for four years. She receives $1,200 of alimony payments each month from...
-
The purpose of this project is to develop and apply financial statement analysis skills based on an understanding of accounting. You are expected to complete the following tasks. You should submit a...
-
What is the output of the following application? A. 1235 B. 3215 C. 5123 D. 5321 E. The code does not compile. F. None of the above. package vortex; class TimeException extends Exception {} class...
-
What is the output of the following application? A. 12 B. 21 C. The code does not compile because of the MyDatabase nested class. D. The code does not compile because of the try-with-resources...
-
Which is the first line of code that causes an ArrayIndexOutOfBoundsException? A. m1 B. m2 C. m3 D. m4 E. The code does not compile. F. None of the above var matrix = new String [1] [2]; matrix [0]...
-
Which statement about the following application is correct? A. The code does not compile because of line w1. B. The code does not compile because of line w2. C. The code does not compile because of...
-
What is the output of the following application? A. Hello B. The code does not compile because of the ReadSign class. C. The code does not compile because of the MakeSign class. D. The code does not...
-
Laporte Engineering Company leased a machine on January 1, 2023, under a contract calling for four annual payments of $100000 on December 31, 2023 through 2026. The machine becomes the property of...
-
The trade-off theory relies on the threat of financial distress. But why should a public corporation ever have to land in financial distress? According to the theory, the firm should operate at the...
-
Sketch the areas under the standard normal curve over the indicated intervals and find the specified areas. Between z = 1.40 and z = 2.03
-
Suppose x has a mound-shaped distribution with = 3. (a) Find the minimal sample size required so that for a 95% confidence interval, the maximal margin of error is E = 0.4. (b) Based on this sample...
-
Education influences attitude and lifestyle. Differences in education are a big factor in the generation gap. Is the younger generation really better educated? Large surveys of people age 65 and...
-
The following table presents the average price, in U.S. dollars per gallon, of unleaded regular gasoline in several countries in the years 2014 and 2016. a. Find the mean and median gas price for...
-
The following table presents the number of active breweries for samples of states located east and west of the Mississippi River. a. Find the mean number of breweries for states east of the...
-
The following table presents prices, in thousands of dollars, of single-family homes for some of the largest metropolitan areas in the United States for the third quarter of 2015 and the third...

Study smarter with the SolutionInn App