Most organizations have a number of information security controls. However, without an information security management system...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
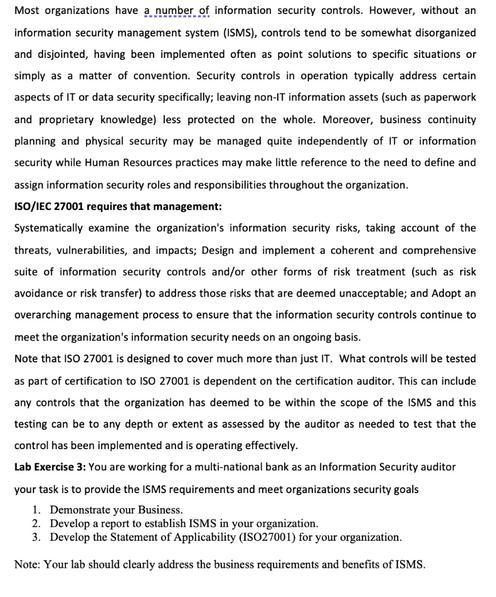
Most organizations have a number of information security controls. However, without an information security management system (ISMS), controls tend to be somewhat disorganized and disjointed, having been implemented often as point solutions to specific situations or simply as a matter of convention. Security controls in operation typically address certain aspects of IT or data security specifically; leaving non-IT information assets (such as paperwork and proprietary knowledge) less protected on the whole. Moreover, business continuity planning and physical security may be managed quite independently of IT or information security while Human Resources practices may make little reference to the need to define and assign information security roles and responsibilities throughout the organization. ISO/IEC 27001 requires that management: Systematically examine the organization's information security risks, taking account of the threats, vulnerabilities, and impacts; Design and implement a coherent and comprehensive suite of information security controls and/or other forms of risk treatment (such as risk avoidance or risk transfer) to address those risks that are deemed unacceptable; and Adopt an overarching management process to ensure that the information security controls continue to meet the organization's information security needs on an ongoing basis. Note that ISO 27001 is designed to cover much more than just IT. What controls will be tested as part of certification to ISO 27001 is dependent on the certification auditor. This can include any controls that the organization has deemed to be within the scope of the ISMS and this testing can be to any depth or extent as assessed by the auditor as needed to test that the control has been implemented and is operating effectively. Lab Exercise 3: You are working for a multi-national bank as an Information Security auditor your task is to provide the ISMS requirements and meet organizations security goals 1. Demonstrate your Business. 2. Develop a report to establish ISMS in your organization. 3. Develop the Statement of Applicability (ISO27001) for your organization. Note: Your lab should clearly address the business requirements and benefits of ISMS. Most organizations have a number of information security controls. However, without an information security management system (ISMS), controls tend to be somewhat disorganized and disjointed, having been implemented often as point solutions to specific situations or simply as a matter of convention. Security controls in operation typically address certain aspects of IT or data security specifically; leaving non-IT information assets (such as paperwork and proprietary knowledge) less protected on the whole. Moreover, business continuity planning and physical security may be managed quite independently of IT or information security while Human Resources practices may make little reference to the need to define and assign information security roles and responsibilities throughout the organization. ISO/IEC 27001 requires that management: Systematically examine the organization's information security risks, taking account of the threats, vulnerabilities, and impacts; Design and implement a coherent and comprehensive suite of information security controls and/or other forms of risk treatment (such as risk avoidance or risk transfer) to address those risks that are deemed unacceptable; and Adopt an overarching management process to ensure that the information security controls continue to meet the organization's information security needs on an ongoing basis. Note that ISO 27001 is designed to cover much more than just IT. What controls will be tested as part of certification to ISO 27001 is dependent on the certification auditor. This can include any controls that the organization has deemed to be within the scope of the ISMS and this testing can be to any depth or extent as assessed by the auditor as needed to test that the control has been implemented and is operating effectively. Lab Exercise 3: You are working for a multi-national bank as an Information Security auditor your task is to provide the ISMS requirements and meet organizations security goals 1. Demonstrate your Business. 2. Develop a report to establish ISMS in your organization. 3. Develop the Statement of Applicability (ISO27001) for your organization. Note: Your lab should clearly address the business requirements and benefits of ISMS.
Expert Answer:
Answer rating: 100% (QA)
It appears that you have been provided with a task as part of an Information Security ... View the full answer

Related Book For 

Posted Date:
Students also viewed these algorithms questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Fletcher, Inc. disposes of under- or over-applied overhead at year-end as an adjustment to cost of goods sold. Prior to disposal, the firm reported cost of goods sold of $619,000 in a year when...
-
Look in The Globe and Mail or National Post at the prices of gold futures quoted on the COMEX futures exchange. What is the date of the most distant contract? Suppose that you buy 100 ounces of gold...
-
Roll Board Inc. manufactures several models of high-quality skateboards. The companys ABC system has four activity cost pools, which are listed below along with their activity measures and activity...
-
Consider the gasoline mileage data in Table B.3. a. Fit a multiple linear regression model relatmg gasoline mileage $y$ (miles per gallon) to engine displacement $x_{1}$ and the number of carburetor...
-
Burgundy, Inc., and Violet Gomez are equal partners in the calendar year BV LLC. Burgundy uses a fiscal year ending April 30, and Violet uses a calendar year. Burgundy receives an annual guaranteed...
-
describe the difference between a swap broker and a swap dealer. 2. what is the necessary condition for a fixed -for-floating interest rate swap to be possible? 3. discuss the risks confronting an...
-
A company makes a range of products with total budgeted manufacturing overheads of 973 560 incurred in three production departments (A, B and C) and one service department. Department A has 10 direct...
-
Jackson and Associates is a financial services company that was formed as a sole proprietorship by its owner, Bob Jackson (SSN 222-22-2222), on March 2, 2018. As a result of having started a new...
-
Fill in the blanks with the lines of code that allow the program to compile. (Choose two.) A. Presents on line t1 B. @Presents on line t1 C. Gift value() on line t2 D. Presents.class on line t1 E....
-
Based on Ohalins estimates, the amount of joint venture shareholders equity at 31 December 2010 included on the consolidated financial statements of each venturer will most likely be: A. higher for...
-
Draw a graph to illustrate the soybean market when the soybean price was low. Show the quantity of soybeans produced, the subsidy farmers received, and the deadweight loss created. High corn and...
-
For what are behavior diagrams used? Give some examples of behavior diagrams.
-
The random variable Y is normally distributed with Y = 28.00 and Y = 10. Find the following values of b: (a) P(Y b) = .8106 (c) P(Y> b) = .0099 (d) P(Y
-
An individual (Resident citizen) earning compensation and business income provided the following income (within the Philippines unless otherwise stated) for the year: Director's fee 220,000 Basic...
-
Draw a Feynman diagram for the reaction n + v p + .
-
Briefly describe the eight typical phases of an audit engagement.
-
As the IT audit senior of the engagement, you are presenting to the IT manager and partner (as part of the planning meeting) the results of the risk assessment performed in Exhibit 3.3. Exhibit 3.3....
-
Explain why unauthorized remote access represents a risk to applications.
-
Reconsider the data from Problem 57 (Orpheum Productions lighting enhancement). Assume that any money not invested in the lighting enhancements will be placed in an interest-bearing account earning...
-
An investor has \($100,000\) to invest in a business venture, or she can earn 10 percent/year with a \($100,000\) certificate of deposit for 4 years. Three possible business ventures have been...
-
This problem is related to Problem 8. Jeff has $10,000 to invest for a period of 5 years. The following three alternatives are available at his bank: Data from problem 8 Jeff has $10,000 to invest...

Study smarter with the SolutionInn App


