Objective: To explore Linux file system security Task: 1. 2. Create two text files in your...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
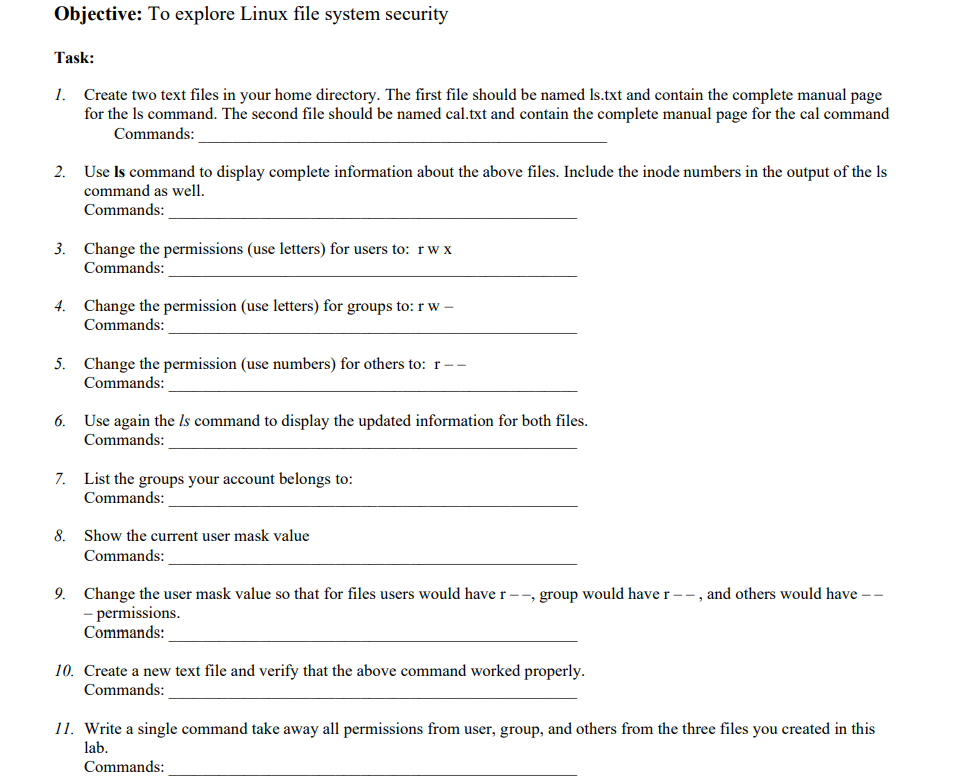
Objective: To explore Linux file system security Task: 1. 2. Create two text files in your home directory. The first file should be named Is.txt and contain the complete manual page for the Is command. The second file should be named cal.txt and contain the complete manual page for the cal command Commands: Use Is command to display complete information about the above files. Include the inode numbers in the output of the Is command as well. Commands: 3. Change the permissions (use letters) for users to: rwx Commands: 4. Change the permission (use letters) for groups to: rw - Commands: 5. Change the permission (use numbers) for others to: r-- Commands: 6. Use again the Is command to display the updated information for both files. Commands: 8. 7. List the groups your account belongs to: Commands: Show the current user mask value Commands: 9. Change the user mask value so that for files users would have r--, group would have r--, and others would have -- - permissions. Commands: 10. Create a new text file and verify that the above command worked properly. Commands: 11. Write a single command take away all permissions from user, group, and others from the three files you created in this lab. Commands: Objective: To explore Linux file system security Task: 1. 2. Create two text files in your home directory. The first file should be named Is.txt and contain the complete manual page for the Is command. The second file should be named cal.txt and contain the complete manual page for the cal command Commands: Use Is command to display complete information about the above files. Include the inode numbers in the output of the Is command as well. Commands: 3. Change the permissions (use letters) for users to: rwx Commands: 4. Change the permission (use letters) for groups to: rw - Commands: 5. Change the permission (use numbers) for others to: r-- Commands: 6. Use again the Is command to display the updated information for both files. Commands: 8. 7. List the groups your account belongs to: Commands: Show the current user mask value Commands: 9. Change the user mask value so that for files users would have r--, group would have r--, and others would have -- - permissions. Commands: 10. Create a new text file and verify that the above command worked properly. Commands: 11. Write a single command take away all permissions from user, group, and others from the three files you created in this lab. Commands:
Expert Answer:
Answer rating: 100% (QA)
It appears youre looking for commands to execute various file system securityrelated tasks in a Linu... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these programming questions
-
Suppose that a system consists of four subsystems. For the baseline configuration, the system will fail if each subsystem fails. The reliability data of each unit that comprise each subsystem in the...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Gems Co. uses the indirect method to prepare its statement of cash flows. The following comparative statement of financial position for 2021 and 2022 are presented: At December 31 2022 2021 Property,...
-
In January 2003, CFO.com featured an article titled "Where Are They Now? From Corporate Raiders to Earnings Management to Activity-Based Costing, We Take a Look at Some of Finance's Greatest Hits."...
-
Ace Patios applies overhead using direct labor hours as its activity base. At the beginning of the year, the company estimates total direct labor hours of 20,000 and total overhead costs of $600,000...
-
The following are six journal entries Keene Engineering, Inc., made during the month of April. Requirement 1. For each transaction shown, determine the accounts affected, the type of account, whether...
-
1. How was mismanagement at Krispy Kreme reflective of leadership failure? 2. Describe the financial shenanigans used by Krispy Kreme. In this regard, is earnings management always a sign of failed...
-
Suppose that the maximum unit sales in a quarter that Pappy's can achieve is121,000 units of each product. How many units of each model should Pappy's produce in a quarter?
-
A store maintains data on customers, products and purchase records in three tables: CUSTOMER, PRODUCT, PURCHASE. The store manager wants to know which product is on its maximum discount for each...
-
1. What is found in the class Node that makes linked lists different from array lists? How does that work? 2.Compare arrays versus linked lists as data structures to represent lists of elements and...
-
Identify at least two of the common problems that are associated with managing virtual teams. After identifying the problems, describe a team-building method that could be applied to each situation.
-
Solve V u = 0, 0 < x < 1, 0 < y < 1, - ur(0, y) = 0, ur(1, gy)=0, 0 < y <1, x uy(2,0) = 4 cos(x), Uy(x, 1) = 0, 0 < x < 1.
-
a) vividly Explains what are some of common barriers to employee's engagement with security initiatives and how can these barriers be overcome? b) Explain, what are some of the best practices are for...
-
In what type of trusted recovery process does the system recover against one or more failure types without administrator intervention while protecting itself against data loss?
-
Once a week track the price of your chosen stocks for three weeks after Feb 24 and create a simple line graph. Discuss the share price increase or decrease or trend and what you and your research...
-
Q1. According to Kepert model which of the following possess least common geometries with coordination number 6. (a) Octahedral (c) Octahedral and trigonal prismatic both (b) Trigonal prismatic (d)...
-
Four GWU students have been selected to taste food sold by 3 different food trucks labeled as food truck A, B and C on H & 22nd Streets every Monday for 3-weeks. For each student, food trucks are...
-
Robert Ramos (age 36) is a single taxpayer, living at 8765 Bay Dr., Monterey, CA 93940. His Social Security number is 976-23-5132. Robert's earnings and income tax withholding as the manager of a...
-
Dr. George E. Beeper is a single taxpayer. He lives at 45 Mountain View Dr., Apt. 321, Spokane, WA 99210. Dr. Beeper's Social Security number is 775-88-9531. Dr. Beeper works for the Pine Medical...
-
Quince Interests is a partnership with a tax year that ends September 30, 2012. During that year, Potter, a partner, received $3,000 per month as a guaranteed payment, and his share of partnership...
-
Ferguson Memorials Limited issued a \(\$ 1,000,000,5 \%\) annual interest non-convertible bond with detachable stock warrants. One warrant is attached to each \(\$ 1,000\) bond and allows the holder...
-
Convertible Debt, Investor's Option: Nero Solutions Company issued an \(\$ 800,000,6 \%\), three-year bond for \(\$ 806,000\). The bond pays interest annually, at each yearend. At maturity, the bond...
-
Convertible Bond, Investor's Option: Bixon Corp. Ltd. issued convertible bonds payable on 1 January \(20 \mathrm{Xl}\), when the market interest rate was \(10 \%\). The bond indenture stated: \(\$...

Study smarter with the SolutionInn App


