Part 1 (25 points): Unencrypted File Transfer In Part 1, you will use network sockets to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
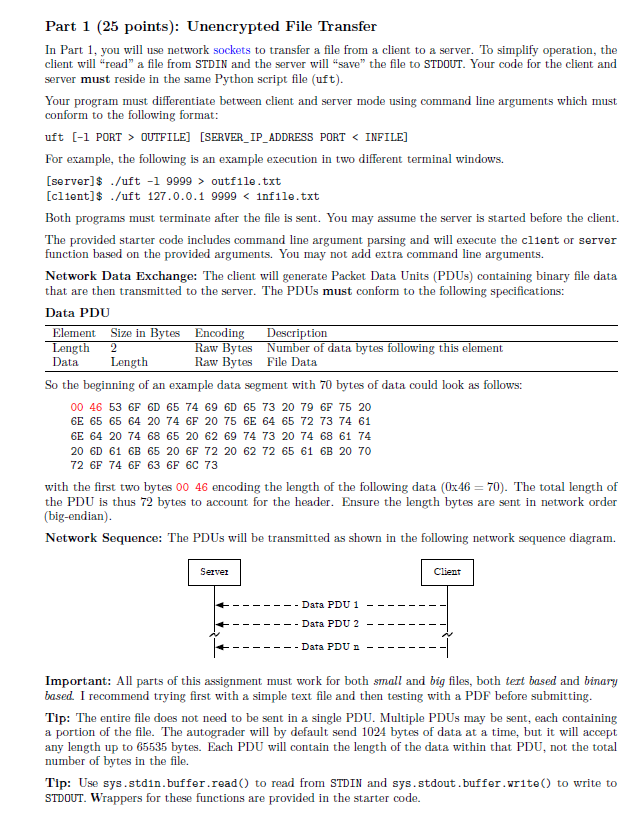
Part 1 (25 points): Unencrypted File Transfer In Part 1, you will use network sockets to transfer a file from a client to a server. To simplify operation, the client will "read" a file from STDIN and the server will "save" the file to STDOUT. Your code for the client and server must reside in the same Python script file (uft). Your program must differentiate between client and server mode using command line arguments which must conform to the following format: uft [-1 PORT > OUTFILE] [SERVER_IP_ADDRESS PORT < INFILE] For example, the following is an example execution in two different terminal windows. [server]$ ./uft -1 9999> outfile.txt [client]$ /uft 127.0.0.1 9999 < infile.txt Both programs must terminate after the file is sent. You may assume the server is started before the client. The provided starter code includes command line argument parsing and will execute the client or server function based on the provided arguments. You may not add extra command line arguments. Network Data Exchange: The client will generate Packet Data Units (PDUs) containing binary file data that are then transmitted to the server. The PDUs must conform to the following specifications: Data PDU Element Size in Bytes Encoding Length 2 Data Length Raw Bytes Raw Bytes Description Number of data bytes following this element File Data So the beginning of an example data segment with 70 bytes of data could look as follows: 00 46 53 6F 6D 65 74 69 6D 65 73 20 79 6F 75 20 6E 65 65 64 20 74 6F 20 75 6E 64 65 72 73 74 61 6E 64 20 74 68 65 20 62 69 74 73 20 74 68 61 74 20 6D 61 6B 65 20 6F 72 20 62 72 65 61 6B 20 70 72 6F 74 6F 63 6F 6C 73 with the first two bytes 00 46 encoding the length of the following data (0x46=70). The total length of the PDU is thus 72 bytes to account for the header. Ensure the length bytes are sent in network order (big-endian). Network Sequence: The PDUs will be transmitted as shown in the following network sequence diagram. Server Data PDU 1 Data PDU 2 Client - Data PDU n -1 Important: All parts of this assignment must work for both small and big files, both text based and binary based. I recommend trying first with a simple text file and then testing with a PDF before submitting. Tip: The entire file does not need to be sent in a single PDU. Multiple PDUs may be sent, each containing a portion of the file. The autograder will by default send 1024 bytes of data at a time, but it will accept any length up to 65535 bytes. Each PDU will contain the length of the data within that PDU, not the total number of bytes in the file. Tip: Use sys.stdn.buffer.read() to read from STDIN and sys.stdout. buffer.write() to write to STDOUT. Wrappers for these functions are provided in the starter code. Part 1 (25 points): Unencrypted File Transfer In Part 1, you will use network sockets to transfer a file from a client to a server. To simplify operation, the client will "read" a file from STDIN and the server will "save" the file to STDOUT. Your code for the client and server must reside in the same Python script file (uft). Your program must differentiate between client and server mode using command line arguments which must conform to the following format: uft [-1 PORT > OUTFILE] [SERVER_IP_ADDRESS PORT < INFILE] For example, the following is an example execution in two different terminal windows. [server]$ ./uft -1 9999> outfile.txt [client]$ /uft 127.0.0.1 9999 < infile.txt Both programs must terminate after the file is sent. You may assume the server is started before the client. The provided starter code includes command line argument parsing and will execute the client or server function based on the provided arguments. You may not add extra command line arguments. Network Data Exchange: The client will generate Packet Data Units (PDUs) containing binary file data that are then transmitted to the server. The PDUs must conform to the following specifications: Data PDU Element Size in Bytes Encoding Length 2 Data Length Raw Bytes Raw Bytes Description Number of data bytes following this element File Data So the beginning of an example data segment with 70 bytes of data could look as follows: 00 46 53 6F 6D 65 74 69 6D 65 73 20 79 6F 75 20 6E 65 65 64 20 74 6F 20 75 6E 64 65 72 73 74 61 6E 64 20 74 68 65 20 62 69 74 73 20 74 68 61 74 20 6D 61 6B 65 20 6F 72 20 62 72 65 61 6B 20 70 72 6F 74 6F 63 6F 6C 73 with the first two bytes 00 46 encoding the length of the following data (0x46=70). The total length of the PDU is thus 72 bytes to account for the header. Ensure the length bytes are sent in network order (big-endian). Network Sequence: The PDUs will be transmitted as shown in the following network sequence diagram. Server Data PDU 1 Data PDU 2 Client - Data PDU n -1 Important: All parts of this assignment must work for both small and big files, both text based and binary based. I recommend trying first with a simple text file and then testing with a PDF before submitting. Tip: The entire file does not need to be sent in a single PDU. Multiple PDUs may be sent, each containing a portion of the file. The autograder will by default send 1024 bytes of data at a time, but it will accept any length up to 65535 bytes. Each PDU will contain the length of the data within that PDU, not the total number of bytes in the file. Tip: Use sys.stdn.buffer.read() to read from STDIN and sys.stdout. buffer.write() to write to STDOUT. Wrappers for these functions are provided in the starter code.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these algorithms questions
-
2. [4 marks] (a) How many different strings of 4 letters can be formed from the letters of the word sandworm, without repetition? (b) If a 4-letter string from the letters in sandworm is chosen at...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
Describe how you plan to allocate your budget to each promotional activity. Provide a brief rationale. First, when developing a marketing budget plan, you want to start with the total budget...
-
Repeat Problem 25 for C = 72,000 + 60x R = 200x - x2/30 P = R - C Where production is increasing at a rate of 500 calculators per week at a production level of 1,500 calculators. Problem 25 Suppose...
-
Assess the content of the separate letter issued by Longeta's vice president of sales to Magicon. Document your conclusion about how the content of the letter affects or does not affect revenue...
-
Why is activity-based costing growing in popularity?
-
Prompt Parcel Service operates a fleet of delivery trucks in a large metropolitan area. A careful study by the companys cost analyst has determined that if a truck is driven 120,000 kilometres during...
-
O TRIGONOMETRIC IDENTITIES AND EQUATIONS Verifying a trigonometric identity: Problem typ Complete the proof of the identity by choosing the Ru (1 cosx)(1+cosx)= 1 1+ cotx To see a detailed...
-
Evaluate the matrix elements (or expectation values) given below. If any vanishes, explain why it vanishes using simple symmetry (or other) arguments. [In (a) and (b), |nlm stands for the energy...
-
QUESTION 8 Simplify. (19 9 01 0 O 19 90 9
-
A television newscaster invites viewers to tweet their opinions about whether the U.S. Congress is doing a good job in handling the economy. More than 100,000 people send in an opinion. In Exercises...
-
Observational studies are generally more reliable than randomized experiments. In Exercises 1116, determine whether the statement is true or false. If the statement is false, rewrite it as a true...
-
A persons height is an example of a continuous variable. In Exercises 1114, determine whether the statement is true or false. If the statement is false, rewrite it as a true statement.
-
A sample of convenience is never acceptable. In Exercises 1316, determine whether the statement is true or false. If the statement is false, rewrite it as a true statement.
-
In a cluster sample, the population is divided into groups, and a random sample from each group is drawn. In Exercises 1316, determine whether the statement is true or false. If the statement is...
-
Total production costs for the six months to June 200X are as follows; Month Units Cost produced Jan-0X 272 4,520 Feb-0X 240 4,320 Mar-0X 304 4,640 Apr-0X 336 4,920 May-0X 320 4,600 Jun-0X 288 4,532...
-
d. The characteristic equation of a control system is given by s+2s+8s+12s+20s+16+16=0. Determine the number of the roots of the equation which lie on the imaginary axis of s-plane
-
An image is 1600 1200 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 56-kbps modem channel? Over a 1-Mbps cable modem? Over a 10-Mbps...
-
A wireless LAN with one AP has 10 client stations. Four stations have data rates of 6 Mbps, four stations have data rates of 18 Mbps, and the last two stations have data rates of 54 Mbps. What is the...
-
Consider the extended LAN connected using bridges B1 and B2 in Fig. 4-41(b). Suppose the hash tables in the two bridges are empty. List all ports on which a packet will be forwarded for the following...
-
What do the terms lead and lag mean in the context of performance measures and why is this important?
-
a) Calculate the payback period, accounting rate of return and the net present value (at 5%) for each of these proposals. (12 marks) b) From a financial perspective, recommend which project the hotel...
-
What are the main weaknesses of traditional financial performance measures?

Study smarter with the SolutionInn App


