Question 9 In computer forensics, in order to show a file is original, once we get...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
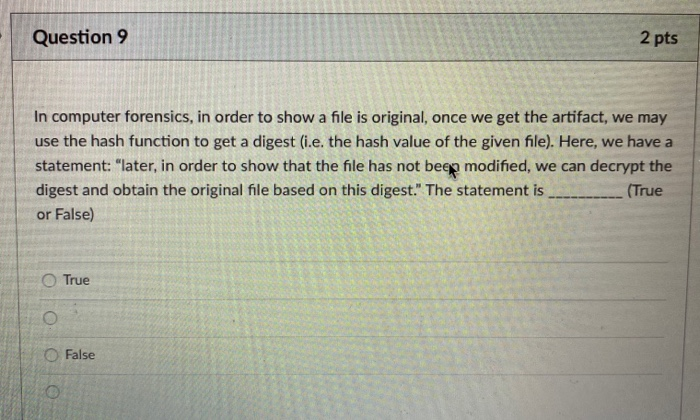
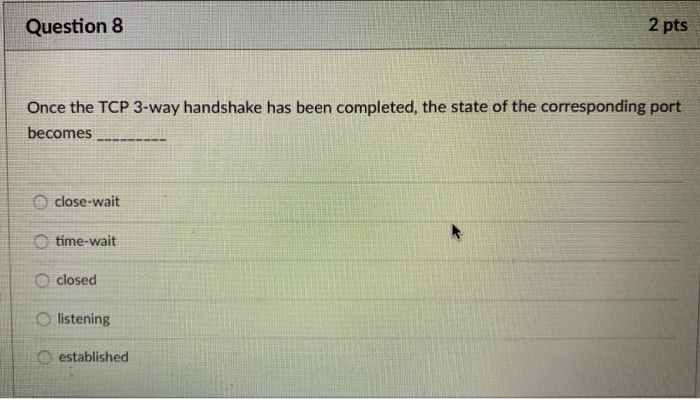
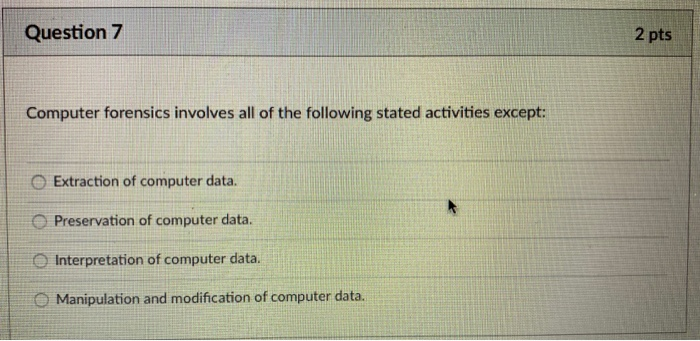
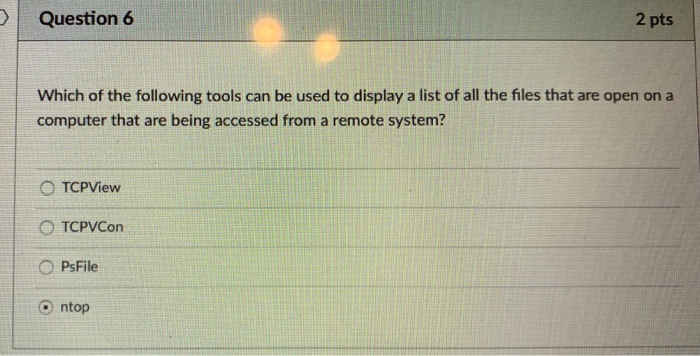
Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop Question 9 In computer forensics, in order to show a file is original, once we get the artifact, we may use the hash function to get a digest (i.e. the hash value of the given file). Here, we have a statement: "later, in order to show that the file has not been modified, we can decrypt the digest and obtain the original file based on this digest." The statement is (True or False) 0 0 0 о True 2 pts O False Question 8 Once the TCP 3-way handshake has been completed, the state of the corresponding port becomes close-wait time-wait closed Olistening 2 pts established Question 7 Computer forensics involves all of the following stated activities except: Extraction of computer data. Preservation of computer data. Interpretation of computer data. Manipulation and modification of computer data. 2 pts D Question 6 Which of the following tools can be used to display a list of all the files that are open on a computer that are being accessed from a remote system? OTCPView OTCPVCon OPsFile 2 pts ntop
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below 6 The correct answer is c PsFile PsFile is a commandline utility that displays a list of files that are open on a computer that are being a... View the full answer

Related Book For 

Management Accounting
ISBN: 978-0132570848
6th Canadian edition
Authors: Charles T. Horngren, Gary L. Sundem, William O. Stratton, Phillip Beaulieu
Posted Date:
Students also viewed these programming questions
-
Which of the following tools can be used to protect containersfrom attack? Software-defined visibility Software-defined networking Security-Enhanced Linux Virtual machine manager
-
List sample file types, based on use, on the VAX under VMS.
-
We can use the gambling interpretation given in Exercise 28 to find the expected number of tosses required to reach pattern B when we start with pattern A. To be a meaningful problem, we assume that...
-
M1 is a way to measure... a) the level of bank reserves b) a country's money supply c) the level of savings in a country d) a country's economic potential
-
Kio Outfitters estimated the following losses and probabilities from past experience: Loss Probability (%) $30,000 ......... 0.25 $15,000 ......... 0.75 $10,000 ........ 1.50 $5,000 ........ 2.50...
-
Show that the matrix has no inverse. -3 0 4 0
-
Once a litigation matter is appealed, what are the four types of decisions that an appellate court may make? Explain each type.
-
Cubicle Company is in need of another factory building. The building will cost $500,000. Cubicle is considering the following possible financing alternatives to acquire the building. (a) Lease the...
-
Robert Company, which applies overhead to production on the basis of machine hours, reported the following data for the period just ended: Actual units produced: 10,000 Actual variable overhead...
-
1. Case Exhibit 2 presents monthly data of units produced and sold, and actual costs incurred, for 24 months. B Create a scatterplot of costs and units. b. From your scatterplot, estimate the...
-
Team building is said to improve group performance; explain how team building helps groups to perform better and how does this contribute to the concept of the High Performance Organization (HPO)?
-
Which result set requires a JOIN? Showing invoice totals, invoice_dates, and customer_id's Showing invoice_dates with invoice totals Showing customer names with invoice_dates Showing invoice_dates...
-
A prosperous school district was subject to a court-ordered desegregation plan involving busing. After receiving the court order recognizing that the district had achieved unitary status, the...
-
Let f(x)=7x+8. Determine the derivative f'(x).
-
The following three vectors are all in R: A=31-23, B=-3 +4j, d=5i 1. Sketch and label all three of these vectors on the appended coordinate grid (and submit it with the rest of this Problem Set) such...
-
which of the three views of the human person you think is most likely to be true. The three views, again, are dualism, physicalism, and hylomorphism. This section should be one sentence. 2. Give what...
-
enum BODYWEIGHT ( UNDERWEIGHT, NORMAL, OVERWEIGHT, SEVERE OBESITY, MORBID_OBESITY, SUPER OBES } public class Main ( public static void main(String[] args) { BODYWEIGHT.values(); BODYWEIGHT bw[]...
-
Suppose the spot and six-month forward rates on the Norwegian krone are Kr 5.78 and Kr 5.86, respectively. The annual risk-free rate in the United States is 3.8 percent, and the annual risk-free rate...
-
ABC and JIT are alternative techniques for achieving competitiveness. Do you agree?
-
"There is a commonality of approach to various special decisions." Explain.
-
Suppose the Norlo Canadian Pacific Railway is considering replacement of a power jack tamper, used for maintenance of track, with a new automatic raising device that can be attached to a production...
-
a. Nonlinearity in mass b. Nonlinearity in damping c. Linear equation d. Nonlinearity in spring \(\ddot{x}+f \frac{\dot{x}}{|\dot{x}|}+\omega_{n}^{2} x=0\)
-
The equation of motion of a nonlinear system is given by \[\ddot{x}+c \dot{x}+k_{1} x+k_{2} x^{2}=a \cos 2 \omega t\] Investigate the subharmonic solution of order 2 for this system.
-
Prove that, for the system considered in Section 13.5.1, the minimum value of \(\omega^{2}\) for which the amplitude of subharmonic oscillations \(A\) will have a real value is given by...

Study smarter with the SolutionInn App