Encryption is the process of converting information algorithmically so that only a valid recipient can read...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
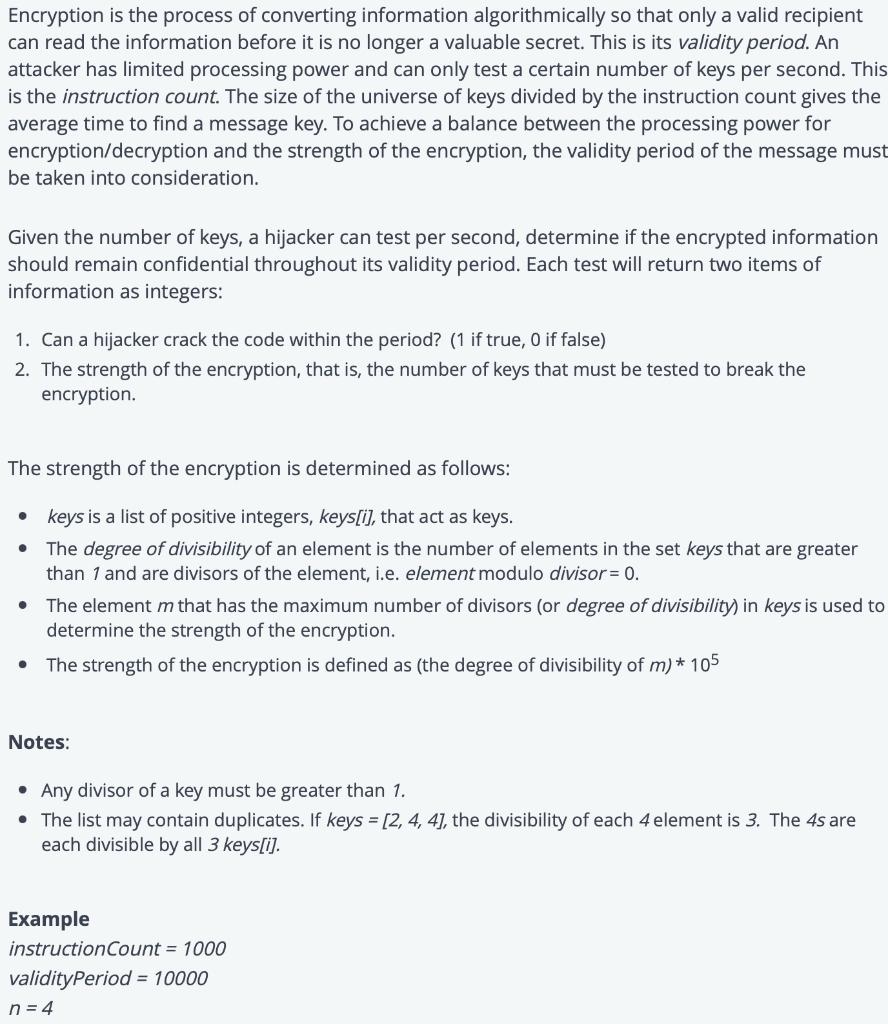
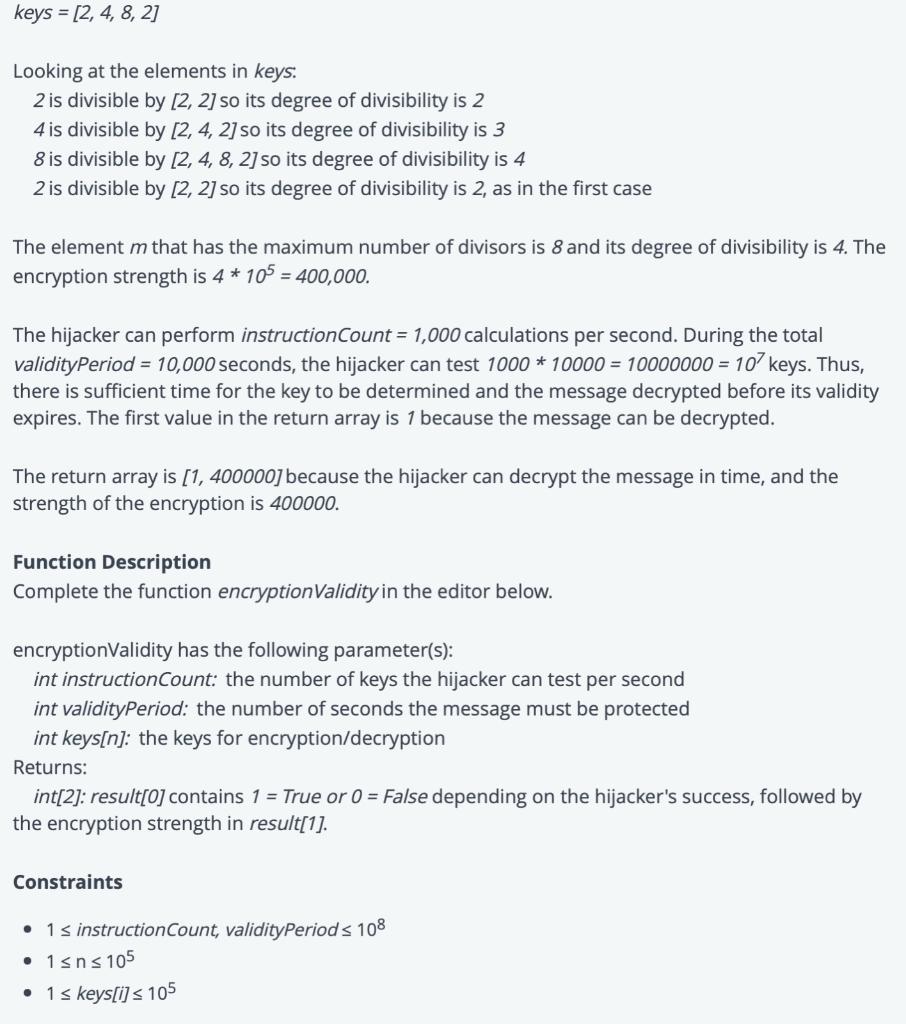
Encryption is the process of converting information algorithmically so that only a valid recipient can read the information before it is no longer a valuable secret. This is its validity period. An attacker has limited processing power and can only test a certain number of keys per second. This is the instruction count. The size of the universe of keys divided by the instruction count gives the average time to find a message key. To achieve a balance between the processing power for encryption/decryption and the strength of the encryption, the validity period of the message must be taken into consideration. Given the number of keys, a hijacker can test per second, determine if the encrypted information should remain confidential throughout its validity period. Each test will return two items of information as integers: 1. Can a hijacker crack the code within the period? (1 if true, 0 if false) 2. The strength of the encryption, that is, the number of keys that must be tested to break the encryption. The strength of the encryption is determined as follows: • keys is a list of positive integers, keys[i], that act as keys. The degree of divisibility of an element is the number of elements in the set keys that are greater than 1 and are divisors of the element, i.e. element modulo divisor = 0. ● The element m that has the maximum number of divisors (or degree of divisibility) in keys is used to determine the strength of the encryption. The strength of the encryption is defined as (the degree of divisibility of m) * 105 Notes: • Any divisor of a key must be greater than 1. • The list may contain duplicates. If keys = [2, 4, 4], the divisibility of each 4 element is 3. The 4s are each divisible by all 3 keys[i]. Example instruction Count = 1000 validityPeriod = 10000 n=4 keys = [2, 4, 8, 2] Looking at the elements in keys: 2 is divisible by [2, 2] so its degree of divisibility is 2 4 is divisible by [2, 4, 2] so its degree of divisibility is 3 8 is divisible by [2, 4, 8, 2] so its degree of divisibility is 4 2 is divisible by [2, 2] so its degree of divisibility is 2, as in the first case The element m that has the maximum number of divisors is 8 and its degree of divisibility is 4. The encryption strength is 4 * 105 = 400,000. The hijacker can perform instruction Count = 1,000 calculations per second. During the total validityPeriod = 10,000 seconds, the hijacker can test 1000 * 10000 = 10000000=107 keys. Thus, there is sufficient time for the key to be determined and the message decrypted before its validity expires. The first value in the return array is 1 because the message can be decrypted. The return array is [1, 400000] because the hijacker can decrypt the message in time, and the strength of the encryption is 400000. Function Description Complete the function encryptionValidity in the editor below. encryptionValidity has the following parameter(s): int instructionCount: the number of keys the hijacker can test per second int validityPeriod: the number of seconds the message must be protected int keys[n]: the keys for encryption/decryption Returns: int[2]: result[0] contains 1 = True or 0= False depending on the hijacker's success, followed by the encryption strength in result[1]. Constraints ● 1 ≤ instruction Count, validityPeriod ≤ 108 • 1≤n≤105 • 1 ≤ keys[i] ≤ 105 Encryption is the process of converting information algorithmically so that only a valid recipient can read the information before it is no longer a valuable secret. This is its validity period. An attacker has limited processing power and can only test a certain number of keys per second. This is the instruction count. The size of the universe of keys divided by the instruction count gives the average time to find a message key. To achieve a balance between the processing power for encryption/decryption and the strength of the encryption, the validity period of the message must be taken into consideration. Given the number of keys, a hijacker can test per second, determine if the encrypted information should remain confidential throughout its validity period. Each test will return two items of information as integers: 1. Can a hijacker crack the code within the period? (1 if true, 0 if false) 2. The strength of the encryption, that is, the number of keys that must be tested to break the encryption. The strength of the encryption is determined as follows: • keys is a list of positive integers, keys[i], that act as keys. The degree of divisibility of an element is the number of elements in the set keys that are greater than 1 and are divisors of the element, i.e. element modulo divisor = 0. ● The element m that has the maximum number of divisors (or degree of divisibility) in keys is used to determine the strength of the encryption. The strength of the encryption is defined as (the degree of divisibility of m) * 105 Notes: • Any divisor of a key must be greater than 1. • The list may contain duplicates. If keys = [2, 4, 4], the divisibility of each 4 element is 3. The 4s are each divisible by all 3 keys[i]. Example instruction Count = 1000 validityPeriod = 10000 n=4 keys = [2, 4, 8, 2] Looking at the elements in keys: 2 is divisible by [2, 2] so its degree of divisibility is 2 4 is divisible by [2, 4, 2] so its degree of divisibility is 3 8 is divisible by [2, 4, 8, 2] so its degree of divisibility is 4 2 is divisible by [2, 2] so its degree of divisibility is 2, as in the first case The element m that has the maximum number of divisors is 8 and its degree of divisibility is 4. The encryption strength is 4 * 105 = 400,000. The hijacker can perform instruction Count = 1,000 calculations per second. During the total validityPeriod = 10,000 seconds, the hijacker can test 1000 * 10000 = 10000000=107 keys. Thus, there is sufficient time for the key to be determined and the message decrypted before its validity expires. The first value in the return array is 1 because the message can be decrypted. The return array is [1, 400000] because the hijacker can decrypt the message in time, and the strength of the encryption is 400000. Function Description Complete the function encryptionValidity in the editor below. encryptionValidity has the following parameter(s): int instructionCount: the number of keys the hijacker can test per second int validityPeriod: the number of seconds the message must be protected int keys[n]: the keys for encryption/decryption Returns: int[2]: result[0] contains 1 = True or 0= False depending on the hijacker's success, followed by the encryption strength in result[1]. Constraints ● 1 ≤ instruction Count, validityPeriod ≤ 108 • 1≤n≤105 • 1 ≤ keys[i] ≤ 105
Expert Answer:

Related Book For 

Intermediate Accounting
ISBN: 978-1260481952
10th edition
Authors: J. David Spiceland, James Sepe, Mark Nelson, Wayne Thomas
Posted Date:
Students also viewed these programming questions
-
Write a Python code for this question: In the given set-up, plot the E fields inside both dielectrics if a. No charge is present in the interface. b. Charge is present in the interface (p, is nonzero...
-
Make sure code in python and follow steps PLEASE I will give tip for good answers Although not everyone consider s game design a worthwhile activity, text adventure games (in which a player navigate...
-
WRITE IN PYTHON AND IN THE GIVEN CODE coderbyte medium Back-end Challenge In the Python file, write a program to perform a GET request on the route Time left: Unlimited time...
-
1) Assume that we want to build an application for special type of exams. The exam includes True/False questions. The number of questions per exam varies from one exam to other. Given below Question...
-
Royersford Knitting Mills, Ltd., sells a line of womens knit underwear. The firm now sells about 20,000 pairs a year at an average price of $10 each. Fixed costs amount to $60,000, and total variable...
-
On November 7, 2005, Briarwood signed an agreement to sell Toll Brothers a planned 66-acre, 41-lot subdivision property in the village of Pomona, New York, for $13,325,000. The agreement expressly...
-
Determine if pretrial conferences are required or authorized in California. Are there special rules in California that must be followed?
-
As a consultant to GBH Skiwear, you have been asked to compute the appropriate discount rate to use in the evaluation of the purchase of a new warehouse facility. You have determined the market value...
-
Buildstuff Ltd. is a construction company which in the past had a large market capitalisation and turnover, but, after the great recession of the late 2000's and the recent pandemic, finds itself...
-
The following data relate to the operations of Shilow Company, a wholesale distributor of consumer goods: Current assets as of March 31: Cash $ 8,000 Accounts receivable 20,000 Inventory 36,000...
-
Asoccer player heads a 0.75 kg ball. The ball approaches the player's head at 3.5 m/s and leaves 4.9 m/s at a 90 degree angle to its incoming pathway. What is the magnitude of the impulse delivere to...
-
Examine the use of unreliable narration in "The Catcher in the Rye." How does this technique affect the reader's perception of the protagonist, Holden Caulfield, and what does it suggest about his...
-
Write an appropriate C++ program segment that will ask the user to insert 15 positive integer numbers. Any negative number will not be counted as their input. From all the positive integer number...
-
Walton Sporting Goods Corporation makes two types of racquets, tennis and badminton. The company uses the same facility to make both products even though the processes are quite different. The...
-
Discuss the role of intertextuality in James Joyce's "Ulysses." How does Joyce reference and reinterpret classical texts to build the novel's layered narrative ?
-
The Fiat Lux lamp company manufactures metal lamps using a variety of different metals and their production is constrained by how much of each metal they have on hand. For the next month, the company...
-
Your company has earnings per share of $3. It has 1 million shares outstanding, each of which has a price of $36. You are thinking of buying TargetCo, which has earnings per share of $2, 1 million...
-
What are the six activities involved in the physical supply/distribution system?
-
Melody Lane Music Company was started by John Ross early in 2021. Initial capital was acquired by issuing shares of common stock to various investors and by obtaining a bank loan. The company...
-
Wynn Farms reported a net operating loss of $100,000 for financial reporting and tax purposes in 2021. The enacted tax rate is 25%. Taxable income, tax rates, and income taxes paid in Wynn?s first...
-
Lee Financial Services pays employees monthly. Payroll information is listed below for January 2021, the first month of Lees fiscal year. Assume that none of the employees exceeded any relevant base...
-
The area under the standard normal curve to the right of z = 0.51 is 0.6950. What is the area to the left of z = 0.51?
-
The area under the standard normal curve to the left of z = 1.75 is 0.0401. What is the area to the right of z = 1.75?
-
The area under the standard normal curve between z = 1.32 and z = 1.82 is 0.0590. What is the area between z = 1.82 and z = 1.32?

Study smarter with the SolutionInn App