4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
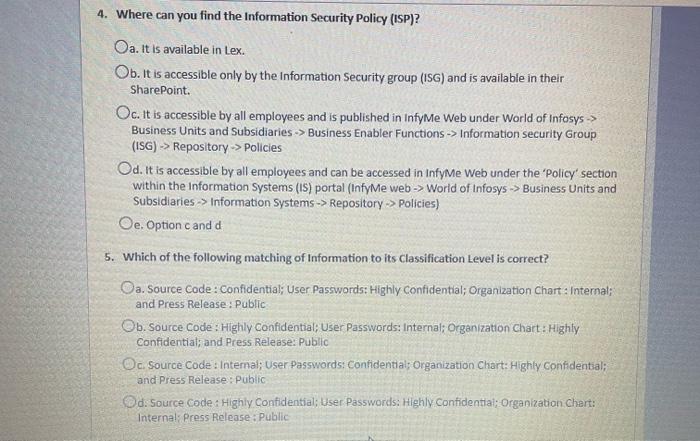
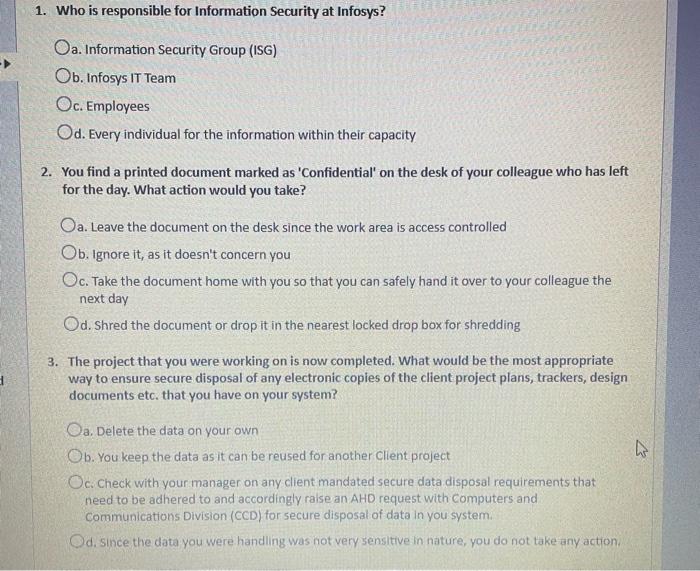
4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex. Ob. It is accessible only by the Information Security group (ISG) and is available in their SharePoint. Oc. It is accessible by all employees and is published in InfyMe Web under World of Infosys > Business Units and Subsidiaries > Business Enabler Functions -> Information security Group (ISG) -> Repository-> Policies Od. It is accessible by all employees and can be accessed in InfyMe Web under the 'Policy' section within the Information Systems (IS) portal (InfyMe web-> World of Infosys > Business Units and Subsidiaries > Information Systems -> Repository-> Policies) Oe. Option c and d 5. Which of the following matching of Information to its Classification Level is correct? Oa. Source Code : Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; and Press Release: Public Ob. Source Code: Highly Confidential; User Passwords: Internal; Organization Chart: Highly Confidential; and Press Release: Public Oc. Source Code: Internal; User Passwords: Confidential; Organization Chart: Highly Confidential; and Press Release: Public Od: Source Code: Highly Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; Press Release: Public 1. Who is responsible for Information Security at Infosys? Oa. Information Security Group (ISG) Ob. Infosys IT Team Oc. Employees Od. Every individual for the information within their capacity 2. You find a printed document marked as 'Confidential' on the desk of your colleague who has left for the day. What action would you take? Oa. Leave the document on the desk since the work area is access controlled Ob. Ignore it, as it doesn't concern you Oc. Take the document home with you so that you can safely hand it over to your colleague the next day Od. Shred the document or drop it in the nearest locked drop box for shredding 3. The project that you were working on is now completed. What would be the most appropriate way to ensure secure disposal of any electronic copies of the client project plans, trackers, design documents etc. that you have on your system? Oa. Delete the data on your own Ob. You keep the data as it can be reused for another Client project Oc. Check with your manager on any client mandated secure data disposal requirements that need to be adhered to and accordingly raise an AHD request with Computers and Communications Division (CCD) for secure disposal of data in you system. Od. Since the data you were handling was not very sensitive in nature, you do not take any action, 4 4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex. Ob. It is accessible only by the Information Security group (ISG) and is available in their SharePoint. Oc. It is accessible by all employees and is published in InfyMe Web under World of Infosys > Business Units and Subsidiaries > Business Enabler Functions -> Information security Group (ISG) -> Repository-> Policies Od. It is accessible by all employees and can be accessed in InfyMe Web under the 'Policy' section within the Information Systems (IS) portal (InfyMe web-> World of Infosys > Business Units and Subsidiaries > Information Systems -> Repository-> Policies) Oe. Option c and d 5. Which of the following matching of Information to its Classification Level is correct? Oa. Source Code : Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; and Press Release: Public Ob. Source Code: Highly Confidential; User Passwords: Internal; Organization Chart: Highly Confidential; and Press Release: Public Oc. Source Code: Internal; User Passwords: Confidential; Organization Chart: Highly Confidential; and Press Release: Public Od: Source Code: Highly Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; Press Release: Public 1. Who is responsible for Information Security at Infosys? Oa. Information Security Group (ISG) Ob. Infosys IT Team Oc. Employees Od. Every individual for the information within their capacity 2. You find a printed document marked as 'Confidential' on the desk of your colleague who has left for the day. What action would you take? Oa. Leave the document on the desk since the work area is access controlled Ob. Ignore it, as it doesn't concern you Oc. Take the document home with you so that you can safely hand it over to your colleague the next day Od. Shred the document or drop it in the nearest locked drop box for shredding 3. The project that you were working on is now completed. What would be the most appropriate way to ensure secure disposal of any electronic copies of the client project plans, trackers, design documents etc. that you have on your system? Oa. Delete the data on your own Ob. You keep the data as it can be reused for another Client project Oc. Check with your manager on any client mandated secure data disposal requirements that need to be adhered to and accordingly raise an AHD request with Computers and Communications Division (CCD) for secure disposal of data in you system. Od. Since the data you were handling was not very sensitive in nature, you do not take any action, 4
Expert Answer:
Answer rating: 100% (QA)
Question Answer 1 The Information Security group ISC Reason The Information Security group ISG is th... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these finance questions
-
urgent, please help me get the output of GAMS code, but it is too large to post it here so please if you can provide help answer me with your email address to send it, if not please tell me to find...
-
Conductance is analogous to O a. Flux O b. Permeance O C. Inductance O d. Reluctance
-
waiting someone to get me help with it please try to solve as soon as possible..thanks i appreciate Simple Harmonic Motion IsoinnosT ylggA ANO0ESMEM Q1). A simple harmonic system (energy is...
-
Consider a group of 12 employees of whom five are in management and seven do clerical work. Select at random a sample of size 4. What is the probability that there will be one manager in this sample?
-
On the death of their mother, the children of Jane Smith gave their interests in their mothers estate to their father in consideration of his payment of $1 to each of them and his promise to leave...
-
List three inhibitors of empowerment and how they can be overcome.
-
James is mixing soil for a raised garden, in which he plans to grow a variety of vegetables. For the soil to be suitable, he determines that \(\frac{2}{5}\) of the soil can be topsoil, but...
-
Ocean Atlantic Co. is a merchandising business. The account balances for Ocean Atlantic Co. as of July 1, 2012 (unless otherwise indicated), are as follows: During July, the last month of the fiscal...
-
Round to the nearest 2 decimal places. suppose you invest $63,926 today in an account that earns 2% interest annually. how much money will be in the account in 5 years from today? what is the value...
-
Aaron, Deanne, and Keon formed the Blue Bell General Partnership at the beginning of the current year. Aaron and Deanne each contributed $110,000 and Keon transferred an acre of undeveloped land to...
-
Classify the following expense categories into (a) front desk only expenses: (b) housekeeping only expenses (c) shared expenses: front office salaries, housekeeping salaries, payroll taxes and...
-
ABC Company issues 700 common stock options to eligible employees on January 2, year 2. The stock has a $3 par value and the market price at issuance is $12 per share. The employees must work 3 years...
-
Bower Enterprises has total equity of $ 1 2 0 , 0 0 0 , a profit margin of 5 . 5 percent, an equity multiplier of 1 . 1 , and a total asset turnover of 1 . 7 . What is the amount of the firms sales?
-
The incidents of officer-involved shootings are greater than many realize. While the circumstances of each incident have their own facts and circumstances, a common question remains in each case: Was...
-
At the beginning of the year, the long-term debt of a firm was 89,162 and total debt was 145,678. At the end of the year, long-term debt was 76,340 and total debt was 170,266. The interest paid was...
-
A new investment in inventory being considered by Quincy Corporation requires an initial outlay of $100,000 on January 1, year 1. The inventory is expected to be liquidated at the end of 5 years for...
-
What would be an objective for the LGBTQ to a suicide prevention program for an at-risk population? Comer, R. J., & Comer, J. S. (2021). Abnormal psychology (11th ed.).Worth Publishers. ISBN:...
-
In Exercises delete part of the domain so that the function that remains is one-to-one. Find the inverse function of the remaining function and give the domain of the inverse function. f(x) = 16x4 -3...
-
Sally and Charles Heck received the following dividends and interest during 2012: Assuming the Hecks file a joint tax return, complete Schedule B of Form 1040 (on page 2-33) for them for the 2012 tax...
-
Please answer the following questions regarding the taxability of Social Security: a. A 68-year-old taxpayer has $20,000 in Social Security income and $100,000 in tax-free municipal bond income. Does...
-
For each of the following situations, indicate whether the taxpayer(s) is (are) required to file a tax return for 2012. Explain your answer. a. Helen is a single taxpayer with interest income in 2012...
-
Consider a model of a food chain of three species. Assume that each population on its own can be modeled by logistic growth. Let the species be labeled by \(x(t), y(t)\), and \(z(t)\). Assume that...
-
The Lorenz Model is a simple model for atmospheric convection developed by Edward Lorenz in 1963. The system is given by three equations: \[\begin{aligned} \frac{d x}{d t} & =\sigma(y-x) \\ \frac{d...
-
Show that the system \(x^{\prime}=x-y-x^{3}, y^{\prime}=x+y-y^{3}\), has at least one limit cycle by picking an appropriate \(\psi(x, y)\) in Dulac's Criteria.

Study smarter with the SolutionInn App


