We define a pair of vertices u and v in a directed graph is intimate if...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
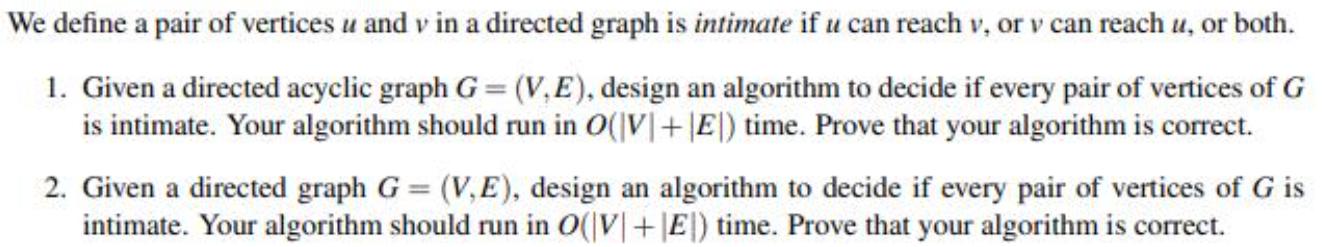
We define a pair of vertices u and v in a directed graph is intimate if u can reach v, or v can reach u, or both. 1. Given a directed acyclic graph G (V,E), design an algorithm to decide if every pair of vertices of G is intimate. Your algorithm should run in O(\V|+|E|) time. Prove that your algorithm is correct. 2. Given a directed graph G = (V,E), design an algorithm to decide if every pair of vertices of G is intimate. Your algorithm should run in O(|V|+|E|) time. Prove that your algorithm is correct. We define a pair of vertices u and v in a directed graph is intimate if u can reach v, or v can reach u, or both. 1. Given a directed acyclic graph G (V,E), design an algorithm to decide if every pair of vertices of G is intimate. Your algorithm should run in O(\V|+|E|) time. Prove that your algorithm is correct. 2. Given a directed graph G = (V,E), design an algorithm to decide if every pair of vertices of G is intimate. Your algorithm should run in O(|V|+|E|) time. Prove that your algorithm is correct.
Expert Answer:

Related Book For 

Data Structures and Algorithm Analysis in Java
ISBN: 978-0132576277
3rd edition
Authors: Mark A. Weiss
Posted Date:
Students also viewed these algorithms questions
-
Prove that for any pair of vertices u and v and any capacity and flow functions c and f, we have cf (u, v) + cf (v, u) = c(u, v) + c(v, u).
-
Prove that for any u and v in an inner product space V ||u||2 + ||u - v||2 = 2||u||2 + 2||v||2 Give a geometric interpretation of this result for the vector space R2
-
An Euler circuit in a directed graph is a cycle in which every edge is visited exactly once. a. Prove that a directed graph has an Euler circuit if and only if it is strongly connected and every...
-
How do the Uniform Trade Secrets Act (UTSA) and the Economic Espionage Act of 1996 differ? Why don't these acts always provide a sufficient remedy for the theft of trade secrets?
-
Here the stone is sliding down a friction-free incline. (a) Identify the forces that act on it, and draw appropriate force vectors, (b) By the parallelogram rule, construct the resultant force on the...
-
Spotlight Ltd has issued share capital of 60,000----8% redeemable cumulative preference shares of ~ 20 each and 4,00,000 equity shares of ~ 10 each. The preference shares are redeemable at a premium...
-
A 38.1-mm-diameter, \(0.0245-\mathrm{N}\) table tennis ball is released from the bottom of a 4-m-deep swimming pool. Assuming that the ball has reached its terminal velocity within \(1 \mathrm{~m}\),...
-
Jetaway, a small manufacturer of replacement parts for the aircraft industry, had always maintained a simple layoutall like machines were located together. That way the firm could be as flexible as...
-
2. You have a text file called employee.txt. This file contains the following information: Variable ID Name Depart Date Hire Description Employee ID Employee Name Desired Informat $3. $20. Department...
-
ALei Industries has credit sales of $150 million a year. ALeis management reviewed its credit policy and decided that it wants to maintain an average collection period of 40 days. a. What is the...
-
Melinda and Martin are getting married in May. They have agreed that if they divorce, Melinda will be able to keep her engagement ring. This agreement must be in writing to be enforceable. Question 8...
-
What would make a personality test reliable and valid?
-
Many companies use contra - revenue accounts to describe a reduction in Service Revenue ( also Sales Revenue ) . These accounts include Sales Discount, Sales Allowance, and Sales Returns. How would...
-
Suppose that someone's taxable income is $ 4 2 , 6 0 0 they're married but finally separately due to their partners immigration status calculate their taxes and show your work.
-
Discuss ways in which you could apply the lessons learned in Chapter 13 to improve your ability to read people. Provide specific examples to support your response.
-
"The Courts will intervene in certain exceptional judicial circumstances as a matter of justice by applying the concept of "Lifting the Corporate Veil" where the Courts have totally disregarded the...
-
The following exchange rates are simultaneously quoted in New York and Frankfurt 1.4355 $/ (New York) 0.6825 /$ (Frankfurt) (a) Is there any arbitrage opportunity with these quotations? (b) How would...
-
Privitera and Freeman (2012) constructed a scale to measure or estimate the daily fat intake of participants; the scale was called the estimated daily intake scale for fat (EDIS-F). To validate the...
-
Give an algorithm to find a maximum spanning tree. Is this harder than finding a minimum spanning tree?
-
a. Prove that 7 comparisons are required to sort 5 elements using any comparison based algorithm. b. Give an algorithm to sort 5 elements with 7 comparisons.
-
Find the strongly connected components in the graph of Figure 9.86. B A D
-
Consider a stochastic process such that the underlying security \(S\) follows the model: \[d S_{t}=\mu S_{t} d t+\sigma_{t} S_{t} d Z_{t}\] where \(Z\) is a standard Brownian motion. Suppose the...
-
Calculate the solution to the following SDE: \[d X_{t}=\alpha\left(m-X_{t} ight) d t+\sigma d B_{t}\] with \(X_{0}=x\). The process satisfying this equation is called the meanreverting...
-
If \(X_{t} \sim N\left(0, \sigma^{2} t ight)\) and \(Y_{t}=e^{X_{t}}\), calculate the pdf of \(Y_{t}\). Calculate \(\mathbf{E}\left[Y_{t} ight]\) and \(V\left(Y_{t} ight)\). Calculate the transition...

Study smarter with the SolutionInn App