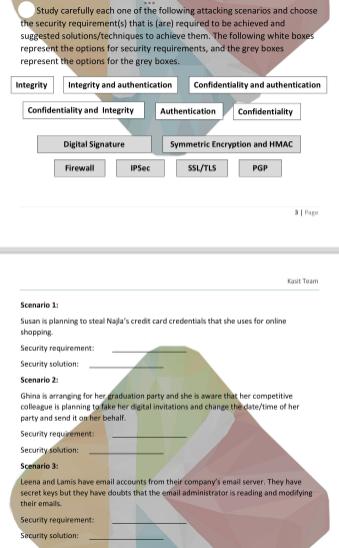
Study carefully each one of the following attacking scenarios and choose the security requirement(s) that is...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Study carefully each one of the following attacking scenarios and choose the security requirement(s) that is (are) required to be achieved and suggested solutions/techniques to achieve them. The following white boxes represent the options for security requirements, and the grey boxes represent the options for the grey boxes. Integrity Integrity and authentication Confidentiality and Integrity Digital Signature Firewall IPSec Confidentiality and authentication Authentication Confidentiality Security requirement: Security solution: Symmetric Encryption and HMAC SSL/TLS PGP Kait Team Scenario 1 Susan is planning to steal Najla's credit card credentials that she uses for online shopping. Security requirement: Security solution: Scenario 2: Ghina is arranging for her graduation party and she is aware that her competitive colleague is planning to take her digital invitations and change the date/time of her party and send it on her behalf. Security requirement Security solution: Scenario 3: Leena and Lamis have email accounts from their company's email server. They have secret keys but they have doubts that the email administrator is reading and modifying their emails Study carefully each one of the following attacking scenarios and choose the security requirement(s) that is (are) required to be achieved and suggested solutions/techniques to achieve them. The following white boxes represent the options for security requirements, and the grey boxes represent the options for the grey boxes. Integrity Integrity and authentication Confidentiality and Integrity Digital Signature Firewall IPSec Confidentiality and authentication Authentication Confidentiality Security requirement: Security solution: Symmetric Encryption and HMAC SSL/TLS PGP Kait Team Scenario 1 Susan is planning to steal Najla's credit card credentials that she uses for online shopping. Security requirement: Security solution: Scenario 2: Ghina is arranging for her graduation party and she is aware that her competitive colleague is planning to take her digital invitations and change the date/time of her party and send it on her behalf. Security requirement Security solution: Scenario 3: Leena and Lamis have email accounts from their company's email server. They have secret keys but they have doubts that the email administrator is reading and modifying their emails
Expert Answer:
Answer rating: 100% (QA)
The image youve provided displays a chart with various security requirements and solutions followed ... View the full answer

Related Book For 

Cornerstones of Financial and Managerial Accounting
ISBN: 978-1111879044
2nd edition
Authors: Rich, Jeff Jones, Dan Heitger, Maryanne Mowen, Don Hansen
Posted Date:
Students also viewed these programming questions
-
ABC Corp. makes products Alpha and Beta. Both products makes use of the same equipment. The following were provided to you with regard to these products in preparation for its budget next year. PESO...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
It is the post-apocalyptic era, and hardship and depression run rampant. You are currently at the bottom of a staircase in the basement of an abandoned building looking at what is pure...
-
The table contains real data. MySpace U.S. Advertising Revenue ($ millions) (a) Determine the maximum and minimum values for each variable in the table. (b) Use your results from part (a) to find an...
-
Sam Chase is the Finance Director of Flowers.co.ke, an Internet company that enables customers to order home deliveries of flowers by accessing its website. Flowers.co.ke has a network of florists...
-
The following information was taken from the 2019 annual report-statements of cash flows- of United Technologies Corporation (UTC), a diversified manufacturing conglomerate (dollars in millions)....
-
Refer to the data for E5-16A. However, instead of the FIFO method, assume Austins Jewelers uses the average cost method. Requirements 1. Prepare a perpetual inventory record for the watches on the...
-
Model 99 Hotels is considering the construction of a new hotel for $80 million. The expected life of the hotel is 20 years with no residual value. The hotel is expected to earn revenues of $15...
-
What is budgeting and what is the function of budgeting? What are the budgets allocation resources and communcation targets used for ? Explain the 3 types of budgets revenue budget, cost budgets, and...
-
YouPay is a Fintech company, which began as a digital wallet and has now evolved into an organisation taking on new verticals within payments many times over the years. To its credit, Paytm has...
-
A manufacturer of battery for cellular phone can produce the battery at a cost of $ 3 0 per unit. Fixed cost of this manufacturer is $ 2 5 0 , 0 0 0 per year and he can sell this product of $ 5 0 per...
-
Brown Company issued 109,000 shares of its $1 par common stock to the Mary Keim law firm as compensation for 4,900 hours of legal services performed. Keim's usual rate is $180 per hour. By what...
-
Consider the recent BHP announcement of its intention to form a global top 10 independent energy company through a merger of BHP's petroleum business with Woodside Discuss one likely scenario by...
-
From an investor's perspective, predict stock market fluctuations of Flight Center (share price surge/drop/unchanged within the context of the information discussed in the article. Your discussion...
-
You are provided the following data: Total estimated manufacturing overhead cost of $28,000 (consisting of $13,000 fixed and $15,000 variable) Estimated total allocation base of 7,500 direct labor...
-
Can the sponsor, or general partner, continue to achieve such high returns? Framed another way, can the general partner earn a 25+% return on the $6,305,000 received at the end of the 10th year? If...
-
When is the bargaining power of buyers high?
-
Identify one local business that uses a perpetual inventory system and another that uses a periodic system. Interview an individual in each organization who is familiar with the inventory system and...
-
What are strategic risks?
-
Ein Company began operations in February 2011. Eins accounting records provide the following data for the remainder of 2011 for one of the items the company sells: Ein uses a perpetual inventory...
-
Refer to the information in Cornerstone Exercise 16-24 for data. Now, assume that Hallett has decided to use a plantwide overhead rate based on direct labor hours. At the beginning of the year,...
-
A machine of mass \(m=500 \mathrm{~kg}\) is mounted on a simply supported steel beam of length \(l=2 \mathrm{~m}\) having a rectangular cross section (depth \(=0.1 \mathrm{~m}\), width \(=1.2...
-
An electronic instrument, weighing \(1000 \mathrm{~N}\), is supported on a rubber mounting whose forcedeflection relationship is given by \(F(x)=157 x+0.2 x^{3}\), where the force \((F)\) and the...
-
The force-deflection relation of a steel helical spring used in an engine is found experimentally as \(F(x)=34.6 x+0.34 x^{2}+0.002 x^{3}\), where the force \((F)\) and deflection \((x)\) are...

Study smarter with the SolutionInn App