Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
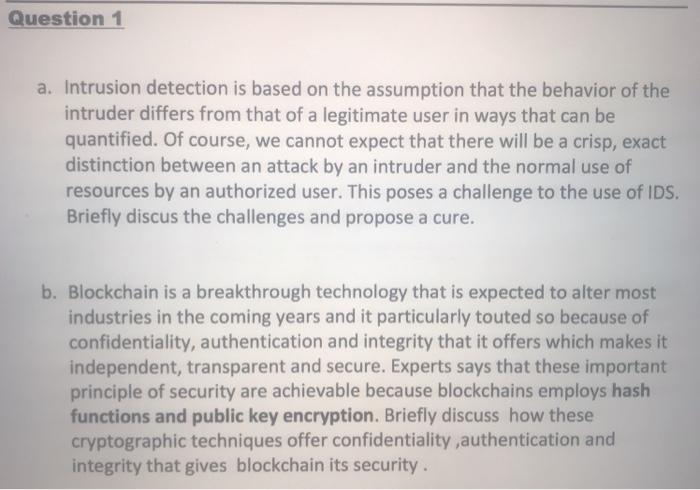
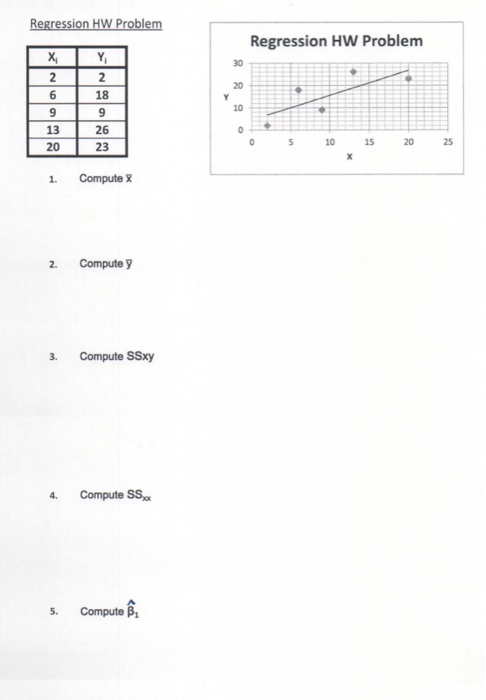
Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25 Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Question 1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there will be a crisp, exact distinction between an attack by an intruder and the normal use of resources by an authorized user. This poses a challenge to the use of IDS. Briefly discus the challenges and propose a cure. b. Blockchain is a breakthrough technology that is expected to alter most industries in the coming years and it particularly touted so because of confidentiality, authentication and integrity that it offers which makes it independent, transparent and secure. Experts says that these important principle of security are achievable because blockchains employs hash functions and public key encryption. Briefly discuss how these cryptographic techniques offer confidentiality,authentication and integrity that gives blockchain its security. Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25 Regression HW Problem Y X 26932 13 20 1. 2. 3. 4. 5. 29 18 26 23 Compute X Compute y Compute SSxy Compute SS Compute Y 30 20 10 0 Regression HW Problem 0 5 10 X 15 20 25
Expert Answer:

Related Book For 

Auditing and Assurance Services A Systematic Approach
ISBN: 978-0077732509
10th edition
Authors: William Messier Jr, Steven Glover, Douglas Prawitt
Posted Date:
Students also viewed these programming questions
-
1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there...
-
1 a. Intrusion detection is based on the assumption that the behavior of the intruder differs from that of a legitimate user in ways that can be quantified. Of course, we cannot expect that there...
-
In the previous problem, assume the equity increases by 1,500 solaris due to retained earnings. If the exchange rate at the end of the year is 1.24 solaris per dollar, what does the balance sheet...
-
Assume the following data describe the gasoline market: (a) Graph the demand and supply curves. (b) What is the equilibrium price? (c) If supply at every price is reduced by 6 gallons, what will the...
-
Given that log 8 y = log 8 (x-2)-2 log 8 x, express y in terms of x.
-
Allan and Koraev both owned condominiums in the same building. Koraevs unit was directly above Allans. While Allan lived in her own unit, Koraev leased his. The leasing of Koraevs unit was managed by...
-
The following jobs are waiting to be processed at Rick Solanos machine center. Solanos machine center has a rela-tively long backlog and sets a fresh schedule every 2 weeks, which does not disturb...
-
2024 2023 2022 Sales $ 78,000 Cost of goods sold 62,400 $ 70,000 60,900 $ 59,000 44,100 2021 $ 58,000 35,100 2020 $ 50,000 30,000 Required: Dollar amounts stated are in thousands. a. Compute trend...
-
Towerton Financial Services13 Towerton Financial Services, a brokerage firm, started with a focus on stock trading and mutual funds. As the business grew, Towerton diversified into two new product...
-
Design and develop an electronic prescription system that serves as a platform for doctors, patients and pharmacies. Doctors will use the system to issue prescriptions for their patients. Once a...
-
What is the relationship between population control and greenhouse gases? Explain
-
Assume the following: there is a 50% of IPOs are worth $20 per share and 50% are worth $30 per share. 1,000,000 shares will be sold in an IPO. There are 10,000 informed investors and 10,000...
-
The Army retains what type of control over Army units assigned or allocated to a combatant commander to allow the Army to meet its Title 10 responsibilities?
-
Agency A had a 30% increase in overhead expenses between the 1st and 2nd quarters of last year. In the 3rd quarter, overhead expenses further increased by 150% over the previous quarter. Due to some...
-
The stockholders equity accounts for Mystic Products appear below as of December 31: Retained earnings $104,000 Common stock, 40,000 shares authorized, 25,000 issued 12,000 Additional paid-in capital...
-
What Items should a communications management plan address?How can a stakeholder analysis assits in preparing and implementing parts of this plan?
-
What will be the final value of DI after executing the following piece of code? Execute the instructions dependently one after another. CLD MOU CX,OFOH MOU AX.02874H MOU DI,01000H MOU ES, DI SUB...
-
The "Accounts Receivable-Confirmation Statistics" working paper shown on the next page was prepared by an audit assistant for the 2015 audit of Lewis County Water Company, Inc., a continuing audit...
-
Phung, CPA, has been engaged to audit the financial statements of Vernon Distributors, Inc., a continuing audit client, for the year ended September 30. After obtaining an understanding of Vernon's...
-
Distinguish among the three categories of expenses. Provide an example of each type of expense.
-
If a person has a highly elastic demand, will he likely bear a large or small percentage of the burden of a tax?
-
Minneapolis Federal Reserve Bank economist Edward Prescott estimates the elasticity of the U.S. labor supply to be 3. Given this elasticity, what would be the impact of funding the Social Security...
-
How much of a $100 tax would a consumer pay if elasticity of demand is 0.2 and elasticity of supply is 1.8?

Study smarter with the SolutionInn App