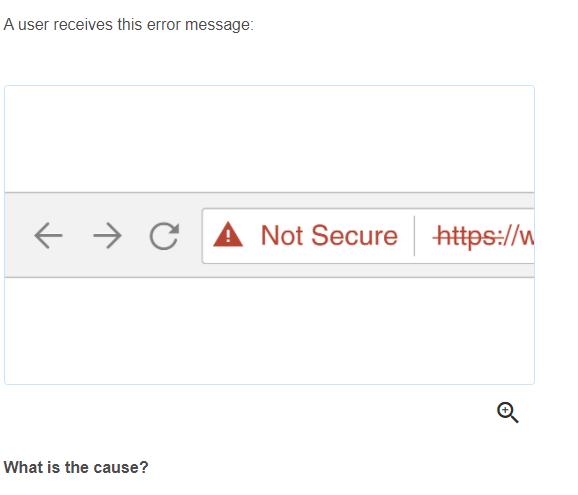
A user receives this error message: CA Not Secure https://w What is the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
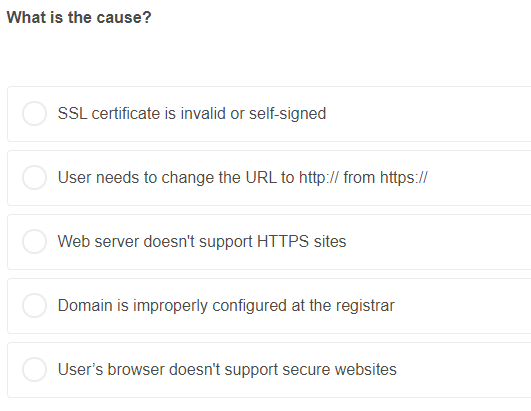
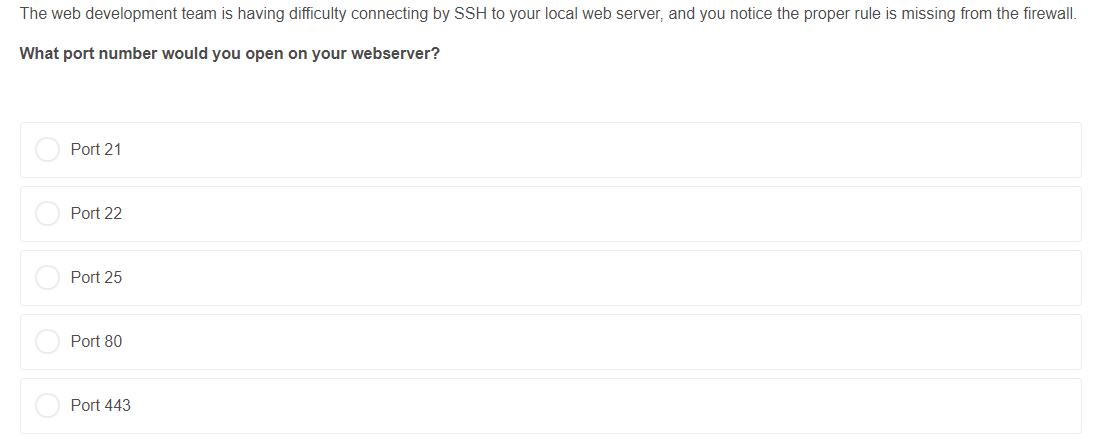
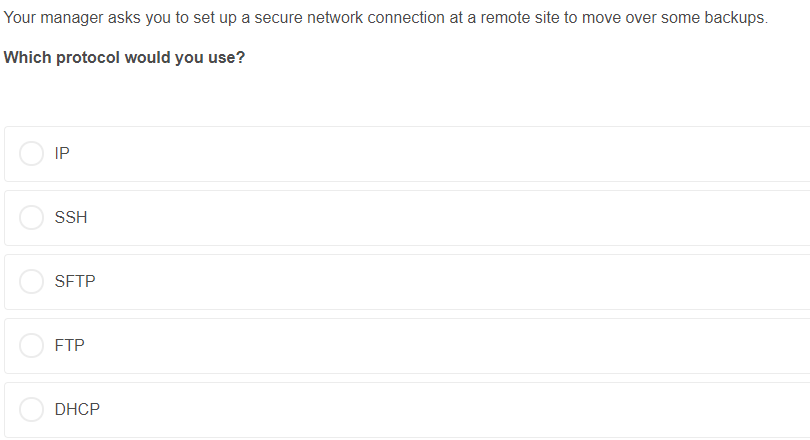
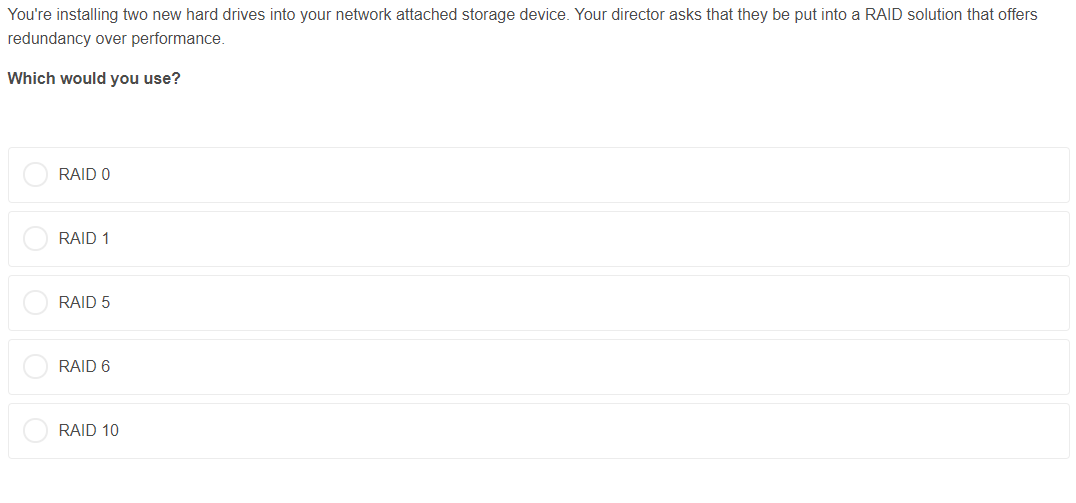
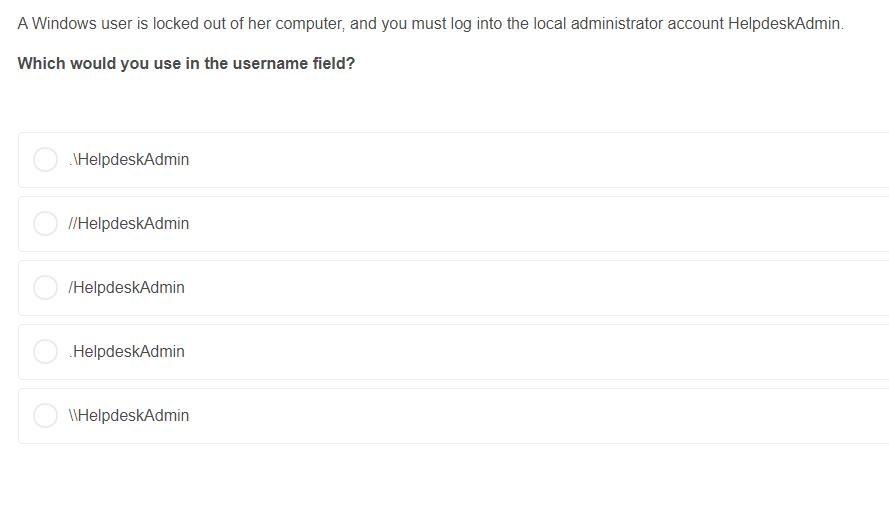
A user receives this error message: ← CA Not Secure https://w → ㅈ What is the cause? What is the cause? SSL certificate is invalid or self-signed User needs to change the URL to http:// from https:// Web server doesn't support HTTPS sites Domain is improperly configured at the registrar User's browser doesn't support secure websites The web development team is having difficulty connecting by SSH to your local web server, and you notice the proper rule is missing from the firewall. What port number would you open on your webserver? Port 21 Port 22 Port 25 Port 80 Port 443 Your internet is out, and devices connected by WiFi and ethernet will not connect. You check several websites, and all your packets fail. You then ping a website with an IP address, and to your surprise, it's a success. Which would you do next? Open the Network settings on your router and try turning off your firewall Open the DNS settings on your router and try using a different DNS Open the DHCP settings on your router and try using a different pool of private IP addresses Open the Port Forwarding settings on your router and try turning on UPnP Open the Network settings on your router and try adjusting the default gateway Your manager asks you to set up a secure network connection at a remote site to move over some backups. Which protocol would you use? IP SSH SFTP FTP DHCP You're installing two new hard drives into your network attached storage device. Your director asks that they be put into a RAID solution that offers redundancy over performance. Which would you use? RAID 0 RAID 1 RAID 5 RAID 6 RAID 10 A Windows user is locked out of her computer, and you must log into the local administrator account HelpdeskAdmin. Which would you use in the username field? \HelpdeskAdmin //HelpdeskAdmin /HelpdeskAdmin .HelpdeskAdmin \\HelpdeskAdmin A user receives this error message: ← CA Not Secure https://w → ㅈ What is the cause? What is the cause? SSL certificate is invalid or self-signed User needs to change the URL to http:// from https:// Web server doesn't support HTTPS sites Domain is improperly configured at the registrar User's browser doesn't support secure websites The web development team is having difficulty connecting by SSH to your local web server, and you notice the proper rule is missing from the firewall. What port number would you open on your webserver? Port 21 Port 22 Port 25 Port 80 Port 443 Your internet is out, and devices connected by WiFi and ethernet will not connect. You check several websites, and all your packets fail. You then ping a website with an IP address, and to your surprise, it's a success. Which would you do next? Open the Network settings on your router and try turning off your firewall Open the DNS settings on your router and try using a different DNS Open the DHCP settings on your router and try using a different pool of private IP addresses Open the Port Forwarding settings on your router and try turning on UPnP Open the Network settings on your router and try adjusting the default gateway Your manager asks you to set up a secure network connection at a remote site to move over some backups. Which protocol would you use? IP SSH SFTP FTP DHCP You're installing two new hard drives into your network attached storage device. Your director asks that they be put into a RAID solution that offers redundancy over performance. Which would you use? RAID 0 RAID 1 RAID 5 RAID 6 RAID 10 A Windows user is locked out of her computer, and you must log into the local administrator account HelpdeskAdmin. Which would you use in the username field? \HelpdeskAdmin //HelpdeskAdmin /HelpdeskAdmin .HelpdeskAdmin \\HelpdeskAdmin
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below 1 What is the cause Ans A SSL certificate is invalid or selfsigned Explanation The most common cause for a website to show Not Secure is th... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
What is the cause of spherical aberration?
-
What is the cause of reaction-type residual stresses?
-
What is the cause of Newton's rings?
-
Water flowing in a positive x-direction passes through a 90 elbow in a 6-inch-diameter pipeline and heads in a positive y-direction with a flow rate of 3.05 ft3/sec. Compute the magnitude and...
-
Using Exhibit 3, what is the present value of $3,000 to be received in seven years, if the market rate of interest is 12% compounded annually?
-
Use the Clark and Wright savings heuristic to determine an acceptable delivery route for the following network of customers, starting from location 1. Assume that any diagonal trip must pass through...
-
When a party may be compelled to defend an action in a particular court?
-
EnviroFriend Structures, Inc., builds environmentally sensitive structures. The companys 2018 revenues totaled $2,780 million. At December 31, 2018, and 2017, the company had, respectively, $656...
-
Intel Corporation. You may recall that this crisis was based around the Pentium chip error. A math Professor at Lynchburg College (Virginia) noticed that his Pentium-based computer was making...
-
Publishing Company, Inc. ("P") is a publicly traded C corporation engaged in the publication of professional textbooks. P has 5 million shares of voting common stock outstanding. The stock is...
-
How do emergent properties of complex adaptive systems manifest within organizational structures, influencing decision-making processes and strategic outcomes ?
-
- Walter Young, doing business as Walter Young Fashions, engaged the CPA partnership of Small \& Brown to examine his financial statements: During the examination, Small \& Brown discovered certain...
-
Gordon \& Groton, CPAs, were the auditors of Bank \& Company, a brokerage firm and member of a national stock exchange. Gordon \& Groton examined and reported on the financial statements of Bank...
-
Do all businesses use account numbers?
-
Barney \& Company, CPAs, has been engaged to perform an examination of the financial statements of Waldo, Inc., for several years. The terms of the engagement have been set out in an annual...
-
The Dandy Container Corporation engaged the accounting firm of Adams and Adams to examine financial statements to be used in connection with a public offering of securities. The audit was completed...
-
MinHeap Forthisassignment, you will be coding a MinHeap that is backed by an array of contiguous elements. Here is a tree and array representation of the same MinHeap: IMPORTANT: You will be given 5...
-
In Exercises discuss the continuity of each function. f(x) -3 1 x - 4 y 3 2 -1 -2 -3+ 3 X
-
Justify the merit of this certification as it is an innovative approach to the experience requirement that may prohibit others from being able to take other exams outlined in this section of the...
-
I. Explain that the BellLaPadula (BLP) model ensures the confidentiality of the modeled system by using MACs, data classification, and security clearances. II. Compare and contrast between the two...
-
True or False: Regardless of what information a company manages, it is shielded from local and state laws and regulations because the federal laws supersede them.
-
__________________ inside the potable water tank(s) pushes the water through distribution lines to the lavatories and galleys.
-
Pneumatic power may be used to back-up hydraulic system components without loss of performance by turning a __________________ pump.
-
What is used to heated potable water on passenger aircraft?

Study smarter with the SolutionInn App


