Question 3: Write the iptables configurations to enable that all computers inside of campus (Lan1, Lan2,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
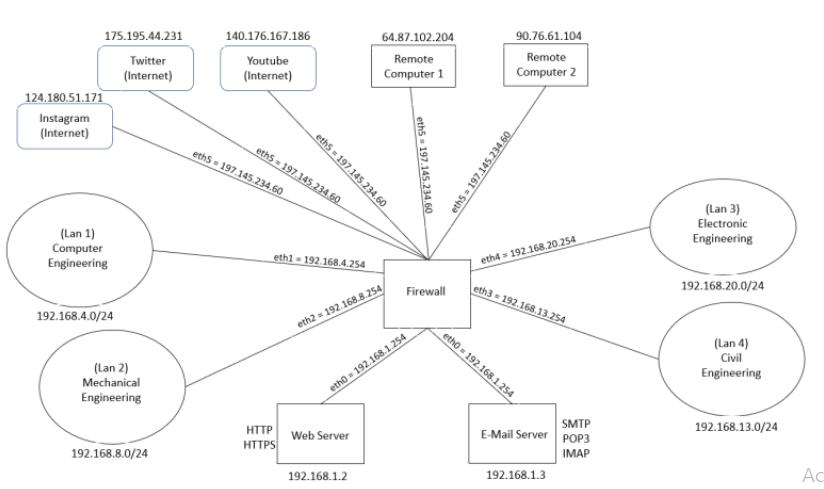
Question 3: Write the iptables configurations to enable that all computers inside of campus (Lan1, Lan2, Lan3, Lan4) and outside of campus can start HTTP/HTTPS communication to Web Server and SMTP communication to E-mail Server machine. Question 4: Write the iptables configurations to enable that all computers inside of campus (Lan1, Lan2, Lan3, Lan4) can start POP3 and IMAP communication to E-mail Server machine. Question 5: Write the necessary configurations for that the Remote computer 1 and Remote Computer 2 can start SSH communication to computers in Computer Engineering Lan and Electronic Engineering Lan. Question 6: Write the necessary configurations so that more than 50 computers cannot access HTTPS port of the Web Server simultaneously. Question 7: All computers inside Lan1, Lan2, Lan3, Lan4 can ping each other. 175.195.44.231 Twitter (Internet) 124.180.51.171 Instagram (Internet) (Lan 1) Computer Engineering 192.168.4.0/24 (Lan 2) Mechanical Engineering 192.168.8.0/24 140.176.167.186 Youtube (Internet) eth5 197.145.234.60 eth5197.145.234.60 eth5 197.145.234.60 eth1-192.168.4.254 HTTP HTTPS eth2 192.168.8.254 64.87.102.204 Remote Computer 1 Web Server 192.168.1.2 eth5 197.145.234.60 eth0 192.168.1.254 Firewall eth5 197.145.234.60 90.76.61.104 Remote Computer 2 eth4 = 192.168.20.254 eth3=192.168.13.254 eth0 192.168.1.254 SMTP E-Mail Server POP3 IMAP 192.168.1.3 (Lan 3) Electronic Engineering 192.168.20.0/24 (Lan 4) Civil Engineering 192.168.13.0/24 Ac Question 3: Write the iptables configurations to enable that all computers inside of campus (Lan1, Lan2, Lan3, Lan4) and outside of campus can start HTTP/HTTPS communication to Web Server and SMTP communication to E-mail Server machine. Question 4: Write the iptables configurations to enable that all computers inside of campus (Lan1, Lan2, Lan3, Lan4) can start POP3 and IMAP communication to E-mail Server machine. Question 5: Write the necessary configurations for that the Remote computer 1 and Remote Computer 2 can start SSH communication to computers in Computer Engineering Lan and Electronic Engineering Lan. Question 6: Write the necessary configurations so that more than 50 computers cannot access HTTPS port of the Web Server simultaneously. Question 7: All computers inside Lan1, Lan2, Lan3, Lan4 can ping each other. 175.195.44.231 Twitter (Internet) 124.180.51.171 Instagram (Internet) (Lan 1) Computer Engineering 192.168.4.0/24 (Lan 2) Mechanical Engineering 192.168.8.0/24 140.176.167.186 Youtube (Internet) eth5 197.145.234.60 eth5197.145.234.60 eth5 197.145.234.60 eth1-192.168.4.254 HTTP HTTPS eth2 192.168.8.254 64.87.102.204 Remote Computer 1 Web Server 192.168.1.2 eth5 197.145.234.60 eth0 192.168.1.254 Firewall eth5 197.145.234.60 90.76.61.104 Remote Computer 2 eth4 = 192.168.20.254 eth3=192.168.13.254 eth0 192.168.1.254 SMTP E-Mail Server POP3 IMAP 192.168.1.3 (Lan 3) Electronic Engineering 192.168.20.0/24 (Lan 4) Civil Engineering 192.168.13.0/24 Ac
Expert Answer:
Answer rating: 100% (QA)
Question 3 Allowing HTTPHTTPS communication to Web Server and SMTP communication to Email Server fro... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Brilliant Accents Company manufactures and sells three styles of kitchen faucets: Brass, Chrome, and White. The following additional data apply: Selling price Direct materials Direct labor Overhead...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
On December 31, 2021, L Inc. had a $1,600,000 note payable outstanding, due July 31, 2022. L borrowed the money to finance construction of a new plant. L planned to refinance the note by issuing...
-
Find the photoelectric threshold for zinc and the maximum velocity of photoelectrons liberated from its surface by electromagnetic radiation with wavelength 250 nm.
-
Discuss two major reasons why journalists need to be sensitive while covering crime, those accused of crime and victims. Consider the effect coverage has on your audience and the community at large.
-
Visit the website www.nielsen.com and choose one of the reports published. Write a brief analysis of the findings and solutions presented by the report.
-
If you were trying to assess the financial health of a government administered pension plan, which financial statements or schedules would you review and why?
-
A firm sells to a single consumer using the optimal two-part tariff. Briefly explain why this firm has MR(Q) = P(Q). Provide an intuitive explanation.
-
Pacific Cruise Lines is a defendant in litigation involving a swimming accident on one of its three cruise ships. Required: For each of the following scenarios, determine the appropriate way to...
-
Why do people are resistant to change? What can an organization do to assist with easing this resistance? Can you cite a workplace example you have experienced?
-
What is Cayley-Hamilton theorem? p(A) = A - 24-34 + 6I - I = A - 5A +5I || || || 3 1 3 1 12 12 HI H 10 5 5 5 15 5 5 10 3 1 12 50 05 H ]-[:] 00 = 00 10 + [ 11 +5 01 10-15+5 5-5+0 5-5+0 5-10+5
-
Consider the causal LTID system represented in block diagram shown in Fig. 5.19. (a) Determine the difference equation relating the output \(\boldsymbol{y}[\boldsymbol{n}]\) and input...
-
What are the advantages of state space model over that of transfer function model?
-
Consider the following T.F. of continuous-time system. Form the state space equation in canonical form II model. H (2) = 5s+68 +2s + 10 s3 +7s + 4s +5
-
A/an __________ is a way to label the subject of a tweet so that others can find it more easily.
-
Question 1 During an experiment, a group of students took equal volumes of blood from the same person containing 50 red blood cells and were suspended in salt solutions A, B, and C. After an hour the...
-
Critical reading SAT scores are distributed as N(500, 100). a. Find the SAT score at the 75th percentile. b. Find the SAT score at the 25th percentile. c. Find the interquartile range for SAT scores....
-
True or False: The person responsible for the storage, maintenance, and protection of the information is the data custodian.
-
What is used to dial every number in a configured range and checks to see if a person, answering machine, or modem picks up? a. War dialer b. Number redialer c. Modem redialer d. Incident redialer
-
I. Compare and contrast an Internet vulnerability assessment with an intranet vulnerability assessment. Explain the differences and similarities. II. Construct the sequence of processes that make up...
-
Assume you want to use random tests on an FIR filter program. How would you know when the program under test is executing correctly?
-
Three devices are attached to a microprocessor: Device 1 has highest priority and device 3 has lowest priority. Each devices interrupt handler takes 5 time units to execute. Show what interrupt...
-
Provide examples of how each of the following can occur in a typical program: a. compulsory miss b. capacity miss c. conflict miss

Study smarter with the SolutionInn App


