QUESTIONS NUMBERS ONE a) List five types of systems b) Explain the following characteristics of a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
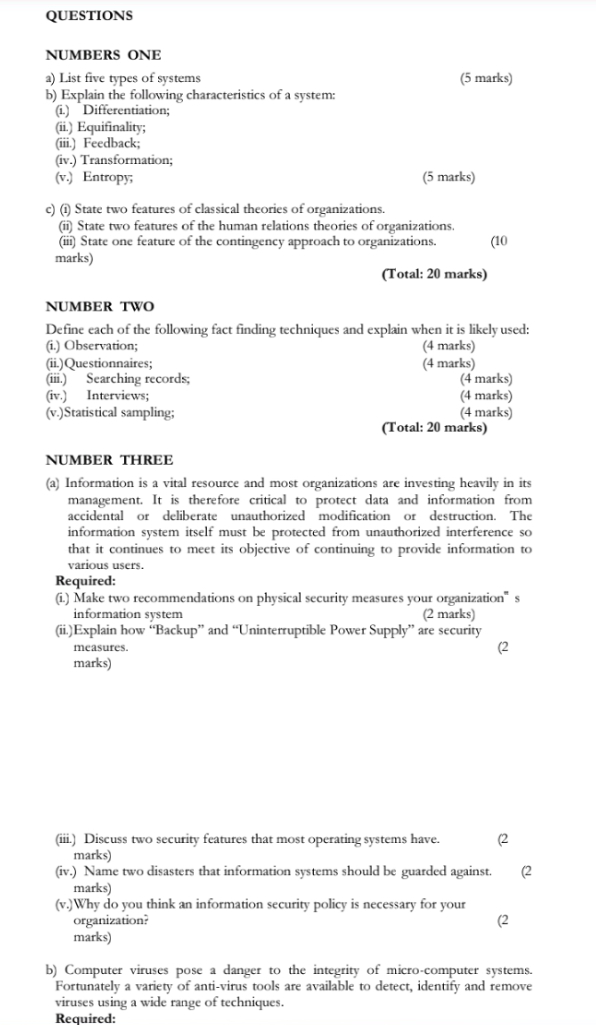
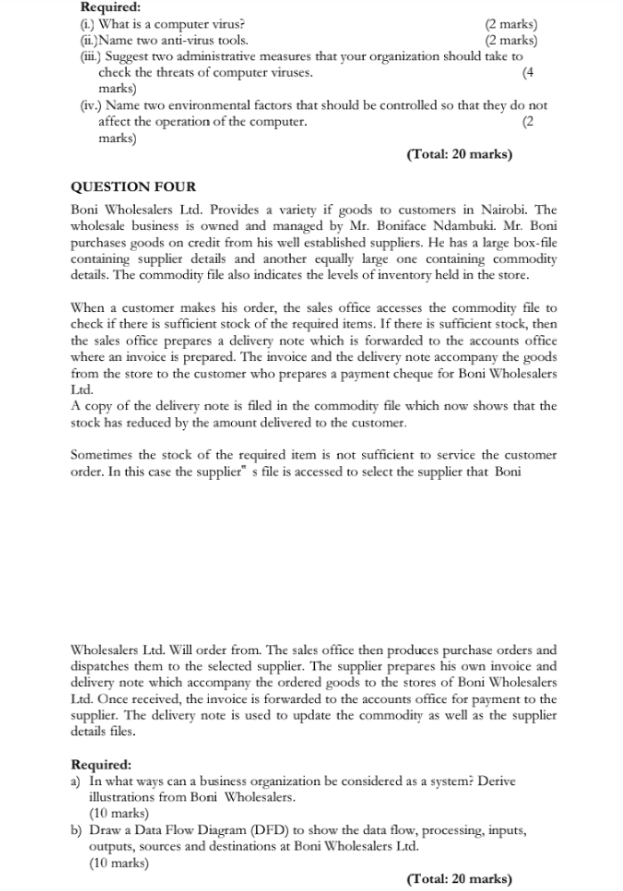
QUESTIONS NUMBERS ONE a) List five types of systems b) Explain the following characteristics of a system: (i) Differentiation; (ii) Equifinality; (iii) Feedback; (iv.) Transformation; (5 marks) (v.) Entropy; c) (i) State two features of classical theories of organizations. (5 marks) (ii) State two features of the human relations theories of organizations. (iii) State one feature of the contingency approach to organizations. marks) (10 (Total: 20 marks) NUMBER TWO Define each of the following fact finding techniques and explain when it is likely used: (i.) Observation; (ii) Questionnaires; (iii.) Searching records; (iv.) Interviews; (v.)Statistical sampling; NUMBER THREE (4 marks) (4 marks) (4 marks) (4 marks) (4 marks) (Total: 20 marks) (a) Information is a vital resource and most organizations are investing heavily in its management. It is therefore critical to protect data and information from accidental or deliberate unauthorized modification or destruction. The information system itself must be protected from unauthorized interference so that it continues to meet its objective of continuing to provide information to various users. Required: (i) Make two recommendations on physical security measures your organization" s information system (2 marks) (ii.) Explain how "Backup” and “Uninterruptible Power Supply" are security measures. marks) (2 (iii) Discuss two security features that most operating systems have. marks) (2 (iv.) Name two disasters that information systems should be guarded against. marks) (2 (v.)Why do you think an information security policy is necessary for your organization? (2 marks) b) Computer viruses pose a danger to the integrity of micro-computer systems. Fortunately a variety of anti-virus tools are available to detect, identify and remove viruses using a wide range of techniques. Required: Required: (i.) What is a computer virus? (ii)Name two anti-virus tools. (2 marks) (2 marks) (iii) Suggest two administrative measures that your organization should take to check the threats of computer viruses. marks) (4 (iv.) Name two environmental factors that should be controlled so that they do not affect the operation of the computer. marks) QUESTION FOUR (2 (Total: 20 marks) Boni Wholesalers Ltd. Provides a variety if goods to customers in Nairobi. The wholesale business is owned and managed by Mr. Boniface Ndambuki. Mr. Boni purchases goods on credit from his well established suppliers. He has a large box-file containing supplier details and another equally large one containing commodity details. The commodity file also indicates the levels of inventory held in the store. When a customer makes his order, the sales office accesses the commodity file to check if there is sufficient stock of the required items. If there is sufficient stock, then the sales office prepares a delivery note which is forwarded to the accounts office where an invoice is prepared. The invoice and the delivery note accompany the goods from the store to the customer who prepares a payment cheque for Boni Wholesalers Ltd. A copy of the delivery note is filed in the commodity file which now shows that the stock has reduced by the amount delivered to the customer. Sometimes the stock of the required item is not sufficient to service the customer order. In this case the supplier" s file is accessed to select the supplier that Boni Wholesalers Ltd. Will order from. The sales office then produces purchase orders and dispatches them to the selected supplier. The supplier prepares his own invoice and delivery note which accompany the ordered goods to the stores of Boni Wholesalers Ltd. Once received, the invoice is forwarded to the accounts office for payment to the supplier. The delivery note is used to update the commodity as well as the supplier details files. Required: a) In what ways can a business organization be considered as a system? Derive illustrations from Boni Wholesalers. (10 marks) b) Draw a Data Flow Diagram (DFD) to show the data flow, processing, inputs, outputs, sources and destinations at Boni Wholesalers Ltd. (10 marks) (Total: 20 marks) (Total: 20 marks) NUMBER FIVE Explain each of the following micro computer hardware/software devices: (a) Cache memory; (b) Coprocessor; (c) Device driver; (d) Disk caching; (e) Expansion card; (4 marks) (4 marks) (4 marks) (4 marks) (4 marks) (Total: 20 marks) QUESTIONS NUMBERS ONE a) List five types of systems b) Explain the following characteristics of a system: (i) Differentiation; (ii) Equifinality; (iii) Feedback; (iv.) Transformation; (5 marks) (v.) Entropy; c) (i) State two features of classical theories of organizations. (5 marks) (ii) State two features of the human relations theories of organizations. (iii) State one feature of the contingency approach to organizations. marks) (10 (Total: 20 marks) NUMBER TWO Define each of the following fact finding techniques and explain when it is likely used: (i.) Observation; (ii) Questionnaires; (iii.) Searching records; (iv.) Interviews; (v.)Statistical sampling; NUMBER THREE (4 marks) (4 marks) (4 marks) (4 marks) (4 marks) (Total: 20 marks) (a) Information is a vital resource and most organizations are investing heavily in its management. It is therefore critical to protect data and information from accidental or deliberate unauthorized modification or destruction. The information system itself must be protected from unauthorized interference so that it continues to meet its objective of continuing to provide information to various users. Required: (i) Make two recommendations on physical security measures your organization" s information system (2 marks) (ii.) Explain how "Backup” and “Uninterruptible Power Supply" are security measures. marks) (2 (iii) Discuss two security features that most operating systems have. marks) (2 (iv.) Name two disasters that information systems should be guarded against. marks) (2 (v.)Why do you think an information security policy is necessary for your organization? (2 marks) b) Computer viruses pose a danger to the integrity of micro-computer systems. Fortunately a variety of anti-virus tools are available to detect, identify and remove viruses using a wide range of techniques. Required: Required: (i.) What is a computer virus? (ii)Name two anti-virus tools. (2 marks) (2 marks) (iii) Suggest two administrative measures that your organization should take to check the threats of computer viruses. marks) (4 (iv.) Name two environmental factors that should be controlled so that they do not affect the operation of the computer. marks) QUESTION FOUR (2 (Total: 20 marks) Boni Wholesalers Ltd. Provides a variety if goods to customers in Nairobi. The wholesale business is owned and managed by Mr. Boniface Ndambuki. Mr. Boni purchases goods on credit from his well established suppliers. He has a large box-file containing supplier details and another equally large one containing commodity details. The commodity file also indicates the levels of inventory held in the store. When a customer makes his order, the sales office accesses the commodity file to check if there is sufficient stock of the required items. If there is sufficient stock, then the sales office prepares a delivery note which is forwarded to the accounts office where an invoice is prepared. The invoice and the delivery note accompany the goods from the store to the customer who prepares a payment cheque for Boni Wholesalers Ltd. A copy of the delivery note is filed in the commodity file which now shows that the stock has reduced by the amount delivered to the customer. Sometimes the stock of the required item is not sufficient to service the customer order. In this case the supplier" s file is accessed to select the supplier that Boni Wholesalers Ltd. Will order from. The sales office then produces purchase orders and dispatches them to the selected supplier. The supplier prepares his own invoice and delivery note which accompany the ordered goods to the stores of Boni Wholesalers Ltd. Once received, the invoice is forwarded to the accounts office for payment to the supplier. The delivery note is used to update the commodity as well as the supplier details files. Required: a) In what ways can a business organization be considered as a system? Derive illustrations from Boni Wholesalers. (10 marks) b) Draw a Data Flow Diagram (DFD) to show the data flow, processing, inputs, outputs, sources and destinations at Boni Wholesalers Ltd. (10 marks) (Total: 20 marks) (Total: 20 marks) NUMBER FIVE Explain each of the following micro computer hardware/software devices: (a) Cache memory; (b) Coprocessor; (c) Device driver; (d) Disk caching; (e) Expansion card; (4 marks) (4 marks) (4 marks) (4 marks) (4 marks) (Total: 20 marks)
Expert Answer:
Answer rating: 100% (QA)
NUMBER ONE a List five types of systems Biological systems Ecological systems Social systems Information systems Physical systems b Characteristics of a system i Differentiation The system is made up ... View the full answer

Related Book For 

Principles of Risk Management and Insurance
ISBN: 978-0132992916
12th edition
Authors: George E. Rejda, Michael McNamara
Posted Date:
Students also viewed these programming questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
importance of workalike balance for women as a leader in healthcare. 1. The purpose of the research; 2. Research question/s; 3. Findings and relevant data; 4. Any recommendations and; 5. The...
-
Page ranks. Design a graph in which the highest-ranking page has fewer links pointing to it than some other page.
-
Selected financial data for Shumway Ltd. are shown below. (a) Calculate for each of 2018 and 2017 the (1) Current ratio, (2) Receivables turnover ratio, and (3) Inventory turnover ratio . (b) Based...
-
Consider the functions f(x) = x - 2x + 2 and g(x) = -2x + 6. a. Find (f.g)(x) b. Find the domain of (f.g)(x). Write your answer in interval notation
-
The landing speed of a winged aircraft such as the Space Shuttle is dependent on the air density. By what percent must the landing speed be increased on a day when the temperature is \(110^{\circ}...
-
Blue Ridge Power and Light Company generates electrical power at four coal-fired power plants along the eastern seaboard in Virginia, North Carolina, Maryland, and Delaware. The company purchases...
-
1. The ball is thrown off the top of the building. If an initial velocity is VA and angle BA- 45 degrees find the time of travel from A to B. Also, find the magnitude of the ball's velocity...
-
5 I . 1 2 im 4 5 5 7 B SCENARIO & REQUIREMENTS SCENARIO: You have invented the first maintenance-free jet wax called "Jetwax 100." Jetwax 100 can last up to 1 year on any plane surface. In order to...
-
Complete Cable has an 70% retention rate. Each customer costs the company $75 monthly. The company offers three plans with monthly revenues as outlined in the table below. Assume a 12% discount rate...
-
Cost efficiency and product quality are two examples of ____________ objectives of organizations. (a) official (b) operating (c) informal (d) institutional
-
When one team member advises another team member that your behaviour is crossing the line in terms of our expectations for workplace civility, she is exercising a form of________ control over the...
-
What is the difference between focus and differentiation as competitive strategies?
-
When an automobile manufacturer is careful to purchase only the highest-quality components for use in production, this is an example of an attempt to ensure high performance through________ control....
-
A manufacturing business with a functional structure has recently developed three new product lines. The president of the company might consider shifting to a(n) ____________ structure to gain a...
-
A company hoping to assess employee satisfaction surveys employees by assigning computer-generated random numbers to each employee on a list of all employees and then contacting all those whose...
-
The following processes constitute the air-standard Diesel cycle: 12: isentropic compression,23: constant-volume energy addition (T and P increase),34: constant-pressure energy addition (v...
-
Jeff is a book dealer who purchased a building from Richard. Jeff obtained a loan from the Gateway Bank to purchase the building, which held a mortgage on the building. Jeff planned to store his...
-
Explain the law of large numbers.
-
The Lincoln Saltdogs is a professional minor league baseball team in the American Association league. The clubhouse is insured for $600,000 under a commercial property insurance policy with an 80...
-
How are the identifiable assets and liabilities acquired in a business combination measured?
-
What is meant by deferred consideration and how is it accounted for?
-
Distinguish between a business combination and a non-business acquisition.

Study smarter with the SolutionInn App