Secret Sharing is an important class of protocols in cryptography. In this problem we take a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
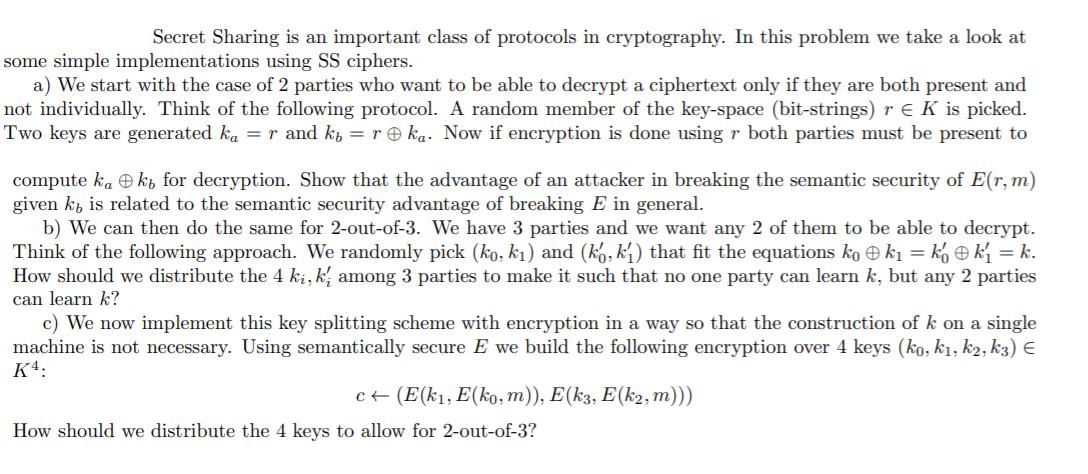
Secret Sharing is an important class of protocols in cryptography. In this problem we take a look at some simple implementations using SS ciphers. a) We start with the case of 2 parties who want to be able to decrypt a ciphertext only if they are both present and not individually. Think of the following protocol. A random member of the key-space (bit-strings) re K is picked. Two keys are generated ka = r and kb = r ka. Now if encryption is done using r both parties must be present to compute kak, for decryption. Show that the advantage of an attacker in breaking the semantic security of E(r, m) given k is related to the semantic security advantage of breaking E in general. b) We can then do the same for 2-out-of-3. We have 3 parties and we want any 2 of them to be able to decrypt. Think of the following approach. We randomly pick (ko, k₁) and (ko, k₁) that fit the equations kok₁ = kỵ k₁ = k. How should we distribute the 4 ki, ki among 3 parties to make it such that no one party can learn but any 2 parties can learn k? c) We now implement this key splitting scheme with encryption in a way so that the construction of k on a single machine is not necessary. Using semantically secure E we build the following encryption over 4 keys (ko, k₁, k2, k3) € K4: c← (E(k₁, E(ko, m)), E(k3, E(k2, m))) How should we distribute the 4 keys to allow for 2-out-of-3? Secret Sharing is an important class of protocols in cryptography. In this problem we take a look at some simple implementations using SS ciphers. a) We start with the case of 2 parties who want to be able to decrypt a ciphertext only if they are both present and not individually. Think of the following protocol. A random member of the key-space (bit-strings) re K is picked. Two keys are generated ka = r and kb = r ka. Now if encryption is done using r both parties must be present to compute kak, for decryption. Show that the advantage of an attacker in breaking the semantic security of E(r, m) given k is related to the semantic security advantage of breaking E in general. b) We can then do the same for 2-out-of-3. We have 3 parties and we want any 2 of them to be able to decrypt. Think of the following approach. We randomly pick (ko, k₁) and (ko, k₁) that fit the equations kok₁ = kỵ k₁ = k. How should we distribute the 4 ki, ki among 3 parties to make it such that no one party can learn but any 2 parties can learn k? c) We now implement this key splitting scheme with encryption in a way so that the construction of k on a single machine is not necessary. Using semantically secure E we build the following encryption over 4 keys (ko, k₁, k2, k3) € K4: c← (E(k₁, E(ko, m)), E(k3, E(k2, m))) How should we distribute the 4 keys to allow for 2-out-of-3?
Expert Answer:
Answer rating: 100% (QA)
a The advantage of an attacker in breaking the semantic security of Erm given k ... View the full answer

Related Book For 

Cost Management Measuring Monitoring and Motivating Performance
ISBN: 978-0470769423
2nd Canadian edition
Authors: Leslie G. Eldenburg, Susan Wolcott, Liang Hsuan Chen, Gail Cook
Posted Date:
Students also viewed these accounting questions
-
Take a look at the reasons why cartels collapse presented in this chapter. For each of the following pairs, choose the case where the cartel is more likely to stick together. a. An industry where its...
-
In this assignment, we will take a look at science and the scientific method. Then, you will design a (pretend) scientific study to answer a specific question based upon a observation. First choose...
-
Take a look at Figure 31-1. Why does "including externalities" cause the supply curve S2 to lie above the supply curve S1 that has been drawn "excluding externalities"?
-
10 1 Journalize the following transactions for Bigelow Company for the month of October. 31 Oct Stockholders invest cash in the company in exchange for common stock. 5 Oct The company buys a delivery...
-
A hotel has to schedule its receptionists according to hourly loads. Management has identified the number of receptionists needed to meet the hourly requirement, which changes from day to day. Assume...
-
Consider a desktop publishing system used to produce documents for various organizations. a. Give an example of a type of publication for which confidentiality of the stored data is the most...
-
Liberty's stock has traded recently around \(\$ 44\) per share. Use your answer to question 9 to measure the company's price/earnings ratio. a. 36 b. 44 c. 1.00 d. 69
-
What SQL command(s) would you use to add the date on which an employee was hired to the EMPLOYEE table represented in Figure? Name this new attribute Employment_ Date. Assume that the employees were...
-
Golden Yellow Manufacturing Company has a cycle time of 5 days, uses Raw and in Process account and charges all conversion costs to Cost of Sales. At the end of each period, all inventories are...
-
Consider the following six months of returns for two stocks and a portfolio of those two stocks where you invest 50% of your wealth in Stock A and 50% in Stock B. What is the expected return and...
-
Requirement #1 - The November 30, 2014 balances have been posted to your general ledger accounts. (The accounts given are the only accounts you are to use.) Prepare an unadjusted trial balance as of...
-
What, if anything, can economists learn from using functional magnetic resonance imaging (fMRI) or similar techniques to study cognitive processes? Outline the major findings of this type of research...
-
4. Find VR3 using superposition theorem: Rison E 20 V www R www 402 40 6 I 20 V 4 A 5. Find Thevenin's and Norton's equivalent circuits seen between terminals a and b: 3A R R3 www 202 SA 19 E b -12V...
-
2. In corn, the G gene encodes an enzyme that synthesizes anthocyanin and produces purple leaves. g/g plants have green leaves. A second gene R is required for smooth leaves and r/r plants have...
-
Find the limits (a) lim (2x+1)e. (b) lim 818 818 5e+1 2e-1'
-
The estimated Wins Above Replacement ( WAR ) of players A , B, and C , who play in different positions, are 6 , 3 and 3 , respectively. What player ( s ) enjoy a comparative advantage in the...
-
8. Assume Country A produces $1 trillion worth of goods and $3 trillion worth of services this year. The capital stock used to produce those goods and services depreciated by $500 billion. What is...
-
The Ranch 888 Noodle Company sells two types of dried noodles:ramen, at $6.50 per box, and chow fun, at $7.70 per box. So farthis year, the company has sold a total of 110,096 boxes ofnoodles,...
-
Refer to the information in Problem 5.48. Suppose you work for a CA firm and are part of the team auditing the financial statements of Flexible Manufacturers. You have been assigned the...
-
Joe Greco is thinking about starting a company to produce carved wooden clocks. He loves making the clocks and sees an opportunity to be his own boss, making a living doing what he likes best. Joe...
-
Forecasting the terminal value of equipment 20 years from now is difficult to do accurately, but errors in estimation probably have a small effect on the NPV? Explain.
-
The value of \(\Delta W=\int_{1}^{2} P d V\) of an ideal gas in a reversible isothermal process is (a) 0 (b) \(\frac{P_{1} V_{1}-P_{2} V_{2}}{\gamma-1}\) (c) \(P_{1} V_{1} \ln \frac{V_{2}}{V_{1}}\)...
-
On a Mollier chart, the slope of the curve representing a reversible isobaric process is equal to (a) \(T-\beta\) (b) \(T+\frac{1}{\beta}\) (c) \(T\) (d) \(\beta T-1\)
-
The work done in reversible polytropic steady flow processes is given by (a) \(\frac{P_{1} V_{1}-P_{2} V_{2}}{n-1}\) (b) \(\frac{n\left(P_{1} V_{1}-P_{2} V_{2} ight)}{n-1}\) (c) \(n\left(P_{1}...

Study smarter with the SolutionInn App