Seneca COLLEGE Summer 2022 DCF255, Assignment 01 Introduction and Format: This Assignment is an individual task...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
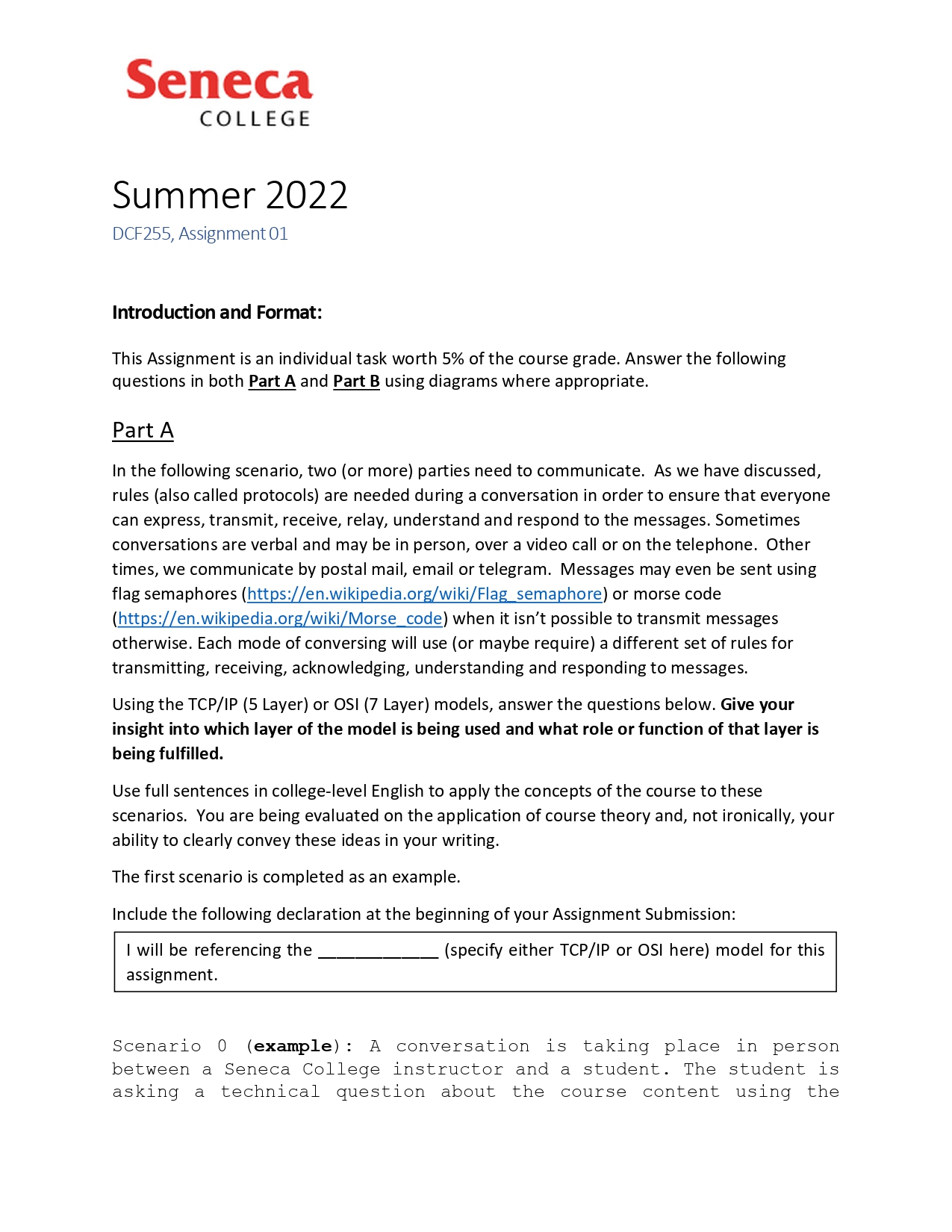
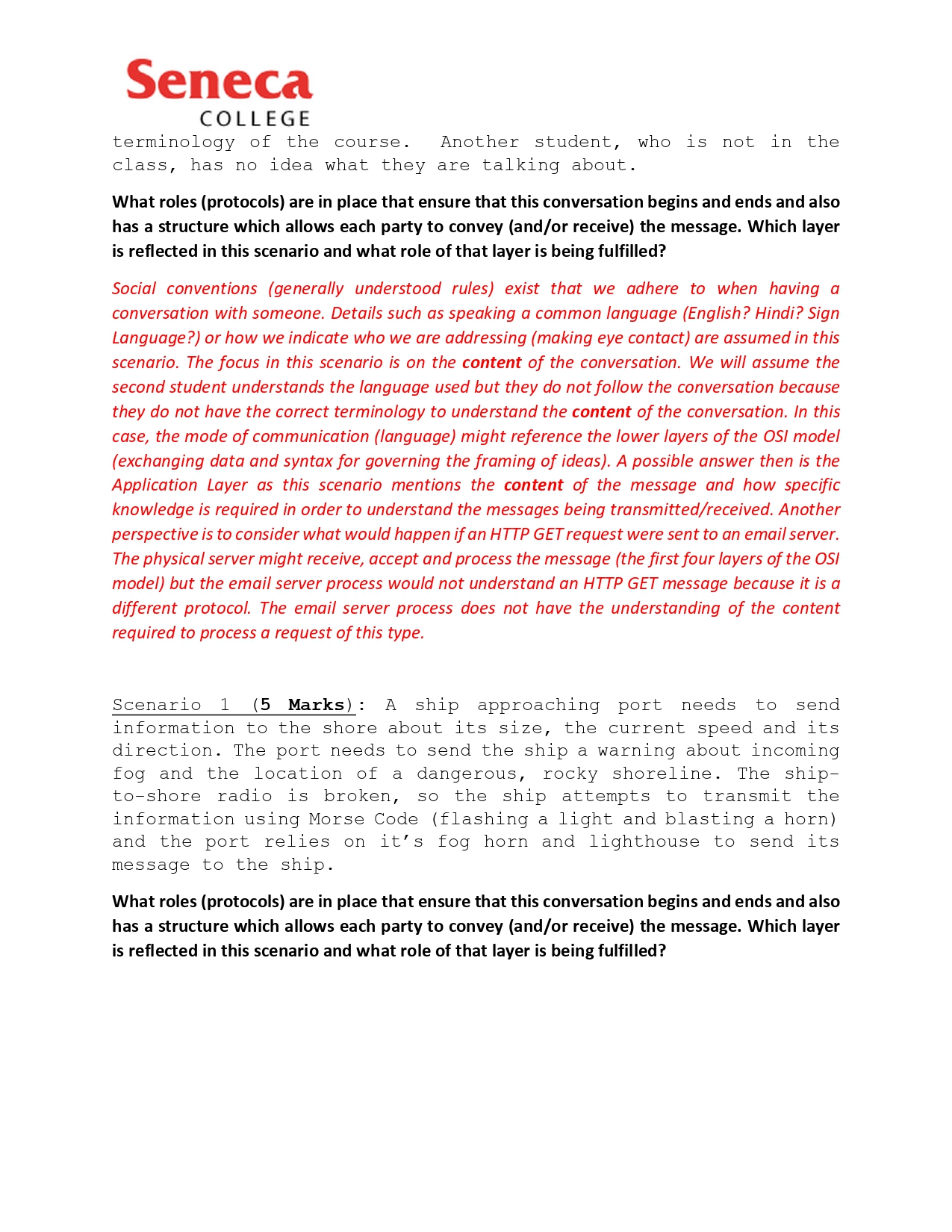
Seneca COLLEGE Summer 2022 DCF255, Assignment 01 Introduction and Format: This Assignment is an individual task worth 5% of the course grade. Answer the following questions in both Part A and Part B using diagrams where appropriate. Part A In the following scenario, two (or more) parties need to communicate. As we have discussed, rules (also called protocols) are needed during a conversation in order to ensure that everyone can express, transmit, receive, relay, understand and respond to the messages. Sometimes conversations are verbal and may be in person, over a video call or on the telephone. Other times, we communicate by postal mail, email or telegram. Messages may even be sent using flag semaphores (https://en.wikipedia.org/wiki/Flag_semaphore) or morse code (https://en.wikipedia.org/wiki/Morse_code) when it isn't possible to transmit messages otherwise. Each mode of conversing will use (or maybe require) a different set of rules for transmitting, receiving, acknowledging, understanding and responding to messages. Using the TCP/IP (5 Layer) or OSI (7 Layer) models, answer the questions below. Give your insight into which layer of the model is being used and what role or function of that layer is being fulfilled. Use full sentences in college-level English to apply the concepts of the course to these scenarios. You are being evaluated on the application of course theory and, not ironically, your ability to clearly convey these ideas in your writing. The first scenario is completed as an example. Include the following declaration at the beginning of your Assignment Submission: I will be referencing the assignment. (specify either TCP/IP or OSI here) model for this Scenario 0 (example): A conversation is taking place in person between a Seneca College instructor and a student. The student is asking a technical question about the course content using the Seneca COLLEGE terminology of the course. Another student, who is not in the class, has no idea what they are talking about. What roles (protocols) are in place that ensure that this conversation begins and ends and also has a structure which allows each party to convey (and/or receive) the message. Which layer is reflected in this scenario and what role of that layer is being fulfilled? Social conventions (generally understood rules) exist that we adhere to when having a conversation with someone. Details such as speaking a common language (English? Hindi? Sign Language?) or how we indicate who we are addressing (making eye contact) are assumed in this scenario. The focus in this scenario is on the content of the conversation. We will assume the second student understands the language used but they do not follow the conversation because they do not have the correct terminology to understand the content of the conversation. In this case, the mode of communication (language) might reference the lower layers of the OSI model (exchanging data and syntax for governing the framing of ideas). A possible answer then is the Application Layer as this scenario mentions the content of the message and how specific knowledge is required in order to understand the messages being transmitted/received. Another perspective is to consider what would happen if an HTTP GET request were sent to an email server. The physical server might receive, accept and process the message (the first four layers of the OSI model) but the email server process would not understand an HTTP GET message because it is a different protocol. The email server process does not have the understanding of the content required to process a request this type. Scenario 1 (5 Marks): A ship approaching port needs to send information to the shore about its size, the current speed and its direction. The port needs to send the ship a warning about incoming fog and the location of a dangerous, rocky shoreline. The ship- to-shore radio is broken, SO the ship attempts to transmit the information using Morse Code (flashing a light and blasting a horn) and the port relies on it's fog horn and lighthouse to send its message to the ship. What roles (protocols) are in place that ensure that this conversation begins and ends and also has a structure which allows each party to convey (and/or receive) the message. Which layer is reflected in this scenario and what role of that layer is being fulfilled? Seneca COLLEGE Part B The following is an exchange of messages between two systems, captured using a Protocol Analyzer (Wireshark). While this is not usually your first troubleshooting or diagnostic step, it is useful to be able to interpret the output of a packet trace. This exercise is intended to incorporate knowledge from the first half of the term to allow you to demonstrate critical thinking skills in applying this knowledge to a common situation. Consider the scenario where you are meeting with a team, you being the programmer of the team. http.cap Eile Edit View Go Capture Analyze Statistics Telephony Wireless Jools Help IXC8+? No. Apply a display filter... Time Source 07 http.cap Destination Protocol Length 10.000000 145.254.160.237 65.208.228.223 TCP 20.911310 65.208.228.223 145.254.160.237 TCP 30.911310 145.254.160.237 65.208.228.223 TCP 40.911310 145.254.160.237 65.208.228.223 HTTP 51.472116 65.208.228.223 145.254.160.237 TCP 61.682419 65.208.228.223 145.254.160.237 TCP 71.812606 145.254.160.237 65.208.228.223 TCP 81.812606 65.208.228.223 145.254.160.237 TCP 92.012894 145.254.160.237 65.208.228.223 TCP 10 2.443513 65.208.228.223 145.254.160.237 TCP 112.553672 65.208.228.223 145.254.160.237 TCP 12 2.553672 145.254.160.237 65.208.228.223 TCP DUC 160 327 445 50 Info 62 3372 80 [SYN] Seq=0 Win=> 62 80 3372 [SYN, ACK] Seq=0 54 3372 80 [ACK] Seq=1 Ack=1 533 GET /download.html HTTP/1.: 54 80 3372 [ACK] Seq=1 Ack= 1434 80 3372 [ACK] Seq=1 Ack= 54 3372 80 [ACK] Seq=480 Acl 1434 80 3372 [ACK] Seq=1381 A 54 3372 80 [ACK] Seq=480 Acl 1434 80 3372 [ACK] Seq-2761 Au 1434 80 3372 [PSH, ACK] Seq=4 54 3372 80 [ACK] Seq=480 Acl standing Frame 1: 62 bytes on wire (496 bits), 62 bytes captured (496 bits) Ethernet II, Src: Xerox 00:00:00 (00:00:01:00:00:00), Dst: fe:ff:20:00:01:00 (fe:ff:20: Internet Protocol Version 4, Src: 145.254.160.237, Dst: 65.208.228.223 Packets: 43 Displayed: 43 (100.0%) + 0.0037 Figure 1 Credit Wireshark Sample HTTP Capture https://wiki.wireshark.org/SampleCaptures Profile: Default Based solely on the information presented here, answer the following questions (1 Mark each) 1. Using the definitions from the course, which IP Address is the client in this exchange and which is the server? 2. Are these two systems on the same network or are they on different networks? 3. Which well known application-layer protocol is in use? How do you know (be specific)? 4. What is the purpose of the messages exchanged? 5. Briefly describe one way that viewing this exchange might help you, as a programmer, to troubleshoot the performance of your web-based application? Seneca COLLEGE Summer 2022 DCF255, Assignment 01 Introduction and Format: This Assignment is an individual task worth 5% of the course grade. Answer the following questions in both Part A and Part B using diagrams where appropriate. Part A In the following scenario, two (or more) parties need to communicate. As we have discussed, rules (also called protocols) are needed during a conversation in order to ensure that everyone can express, transmit, receive, relay, understand and respond to the messages. Sometimes conversations are verbal and may be in person, over a video call or on the telephone. Other times, we communicate by postal mail, email or telegram. Messages may even be sent using flag semaphores (https://en.wikipedia.org/wiki/Flag_semaphore) or morse code (https://en.wikipedia.org/wiki/Morse_code) when it isn't possible to transmit messages otherwise. Each mode of conversing will use (or maybe require) a different set of rules for transmitting, receiving, acknowledging, understanding and responding to messages. Using the TCP/IP (5 Layer) or OSI (7 Layer) models, answer the questions below. Give your insight into which layer of the model is being used and what role or function of that layer is being fulfilled. Use full sentences in college-level English to apply the concepts of the course to these scenarios. You are being evaluated on the application of course theory and, not ironically, your ability to clearly convey these ideas in your writing. The first scenario is completed as an example. Include the following declaration at the beginning of your Assignment Submission: I will be referencing the assignment. (specify either TCP/IP or OSI here) model for this Scenario 0 (example): A conversation is taking place in person between a Seneca College instructor and a student. The student is asking a technical question about the course content using the Seneca COLLEGE terminology of the course. Another student, who is not in the class, has no idea what they are talking about. What roles (protocols) are in place that ensure that this conversation begins and ends and also has a structure which allows each party to convey (and/or receive) the message. Which layer is reflected in this scenario and what role of that layer is being fulfilled? Social conventions (generally understood rules) exist that we adhere to when having a conversation with someone. Details such as speaking a common language (English? Hindi? Sign Language?) or how we indicate who we are addressing (making eye contact) are assumed in this scenario. The focus in this scenario is on the content of the conversation. We will assume the second student understands the language used but they do not follow the conversation because they do not have the correct terminology to understand the content of the conversation. In this case, the mode of communication (language) might reference the lower layers of the OSI model (exchanging data and syntax for governing the framing of ideas). A possible answer then is the Application Layer as this scenario mentions the content of the message and how specific knowledge is required in order to understand the messages being transmitted/received. Another perspective is to consider what would happen if an HTTP GET request were sent to an email server. The physical server might receive, accept and process the message (the first four layers of the OSI model) but the email server process would not understand an HTTP GET message because it is a different protocol. The email server process does not have the understanding of the content required to process a request this type. Scenario 1 (5 Marks): A ship approaching port needs to send information to the shore about its size, the current speed and its direction. The port needs to send the ship a warning about incoming fog and the location of a dangerous, rocky shoreline. The ship- to-shore radio is broken, SO the ship attempts to transmit the information using Morse Code (flashing a light and blasting a horn) and the port relies on it's fog horn and lighthouse to send its message to the ship. What roles (protocols) are in place that ensure that this conversation begins and ends and also has a structure which allows each party to convey (and/or receive) the message. Which layer is reflected in this scenario and what role of that layer is being fulfilled? Seneca COLLEGE Part B The following is an exchange of messages between two systems, captured using a Protocol Analyzer (Wireshark). While this is not usually your first troubleshooting or diagnostic step, it is useful to be able to interpret the output of a packet trace. This exercise is intended to incorporate knowledge from the first half of the term to allow you to demonstrate critical thinking skills in applying this knowledge to a common situation. Consider the scenario where you are meeting with a team, you being the programmer of the team. http.cap Eile Edit View Go Capture Analyze Statistics Telephony Wireless Jools Help IXC8+? No. Apply a display filter... Time Source 07 http.cap Destination Protocol Length 10.000000 145.254.160.237 65.208.228.223 TCP 20.911310 65.208.228.223 145.254.160.237 TCP 30.911310 145.254.160.237 65.208.228.223 TCP 40.911310 145.254.160.237 65.208.228.223 HTTP 51.472116 65.208.228.223 145.254.160.237 TCP 61.682419 65.208.228.223 145.254.160.237 TCP 71.812606 145.254.160.237 65.208.228.223 TCP 81.812606 65.208.228.223 145.254.160.237 TCP 92.012894 145.254.160.237 65.208.228.223 TCP 10 2.443513 65.208.228.223 145.254.160.237 TCP 112.553672 65.208.228.223 145.254.160.237 TCP 12 2.553672 145.254.160.237 65.208.228.223 TCP DUC 160 327 445 50 Info 62 3372 80 [SYN] Seq=0 Win=> 62 80 3372 [SYN, ACK] Seq=0 54 3372 80 [ACK] Seq=1 Ack=1 533 GET /download.html HTTP/1.: 54 80 3372 [ACK] Seq=1 Ack= 1434 80 3372 [ACK] Seq=1 Ack= 54 3372 80 [ACK] Seq=480 Acl 1434 80 3372 [ACK] Seq=1381 A 54 3372 80 [ACK] Seq=480 Acl 1434 80 3372 [ACK] Seq-2761 Au 1434 80 3372 [PSH, ACK] Seq=4 54 3372 80 [ACK] Seq=480 Acl standing Frame 1: 62 bytes on wire (496 bits), 62 bytes captured (496 bits) Ethernet II, Src: Xerox 00:00:00 (00:00:01:00:00:00), Dst: fe:ff:20:00:01:00 (fe:ff:20: Internet Protocol Version 4, Src: 145.254.160.237, Dst: 65.208.228.223 Packets: 43 Displayed: 43 (100.0%) + 0.0037 Figure 1 Credit Wireshark Sample HTTP Capture https://wiki.wireshark.org/SampleCaptures Profile: Default Based solely on the information presented here, answer the following questions (1 Mark each) 1. Using the definitions from the course, which IP Address is the client in this exchange and which is the server? 2. Are these two systems on the same network or are they on different networks? 3. Which well known application-layer protocol is in use? How do you know (be specific)? 4. What is the purpose of the messages exchanged? 5. Briefly describe one way that viewing this exchange might help you, as a programmer, to troubleshoot the performance of your web-based application?
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Case Study: Quick Fix Dental Practice Technology requirements Application must be built using Visual Studio 2019 or Visual Studio 2017, professional or enterprise. The community edition is not...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Rhenium forms a series of solid oxides: Re2O7 (yellow), ReO3 (red), Re2O5 (blue), and ReO2 (brown). One of them has a crystal structure with the following unit cell: a. How many rhenium atoms (gray...
-
The volume of liquid fl owing per second is called the volume flow rate Q and has the dimensions of [L]3 / [T]. The flow rate of a liquid through a hypodermic needle during an injection can be...
-
Explain why it was so complicated to take out a mortgage loan to buy a house from a commercial bank in the 1870s.
-
An electromagnet in a physics laboratory is damaging electronic apparatus in its vicinity. You suspect that the damage is due to unusually large induced currents created each time the electromagnet...
-
The Fashion Shoe Company operates a chain of womens shoe shops around the country. The shops carry many styles of shoes that are all sold at the same price. Sales personnel in the shops are paid a...
-
A hiker and his dog have discovered a skeleton hidden deep in the woods. The medical examiner has identified this skeleton as female. What characteristics of the skeleton would help the examiner make...
-
Shown on the following page are responsibility income statements for Butterfield, Inc., for the month of March. Instructions a. The company plans to initiate an advertising campaign for one of the...
-
You are a security analyst responsible for following Jaguar's stock after it floats. (Assume the company had 100 million shares outstanding.) What is your estimate of Jaguar's stock price given a 10%...
-
If Congress passed a law limiting the deductibility of interest expense on loans used to purchase municipal bonds to 20%. For example, borrowing $1,000, only $20 of the $100 interest expense is...
-
what are some of the biggest differences between unix and linux operating systems?
-
Sam can only hire two full-time employees, but he needs even more help to make the two products he sells. Product Alpha has a contribution margin of $750 per unit of limited resource and Product Beta...
-
Trust Accounting Sometimes the bank statement closing balance and the trust trial balance will not match in a period. Suggest three different examples of discrepancies that might explain this for a...
-
Describe taxonomy and biological classification, including correct use of binomial nomenclature, the correct order of the levels of classification, and types of information used to classify organisms.
-
Determine with respect to x
-
Akramin just graduated with a Master of Engineering in Manufacturing Engineering and landed a new job in Melaka with a starting salary of RM 4,000 per month. There are a number of things that he...
-
The flow rate Q (volume of fluid per second) in a round pipe can be calculated by: For turbulent flow the velocity profile can be estimated by: v = vmax(1 r/R)l/n. Determine Q for R = 0.25 in., n =...
-
Create a column vector with 9 equally spaced elements in which the first element is -34 and the last element is -7. (A column vector can be created by the transpose of a row vector.)
-
A rectangular piece of cardboard, 40 in. long by in. wide is used for making a rectangular box (open top) by cutting out squares of x by x from the corners and folding up the sides. (a) Create a...
-
Recently Sparrow Ltd experienced temporary closure that affected a number of its operating plants. The group accountant of Sparrow Ltd indicated that it was not appropriate to report depreciation...
-
Crane Ltd has proposed that the company adopt the revaluation model for fixed assets. Some of these assets are hard to obtain and certain items have increased in value in the current period, however...
-
Seagull Ltd purchased land for use as its corporate headquarters. A small factory that was on the land when it was purchased was torn down before construction of the office building began....

Study smarter with the SolutionInn App