Stream Cipher is a kind of symmetric key encryption technique. The question concerns with the stream...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
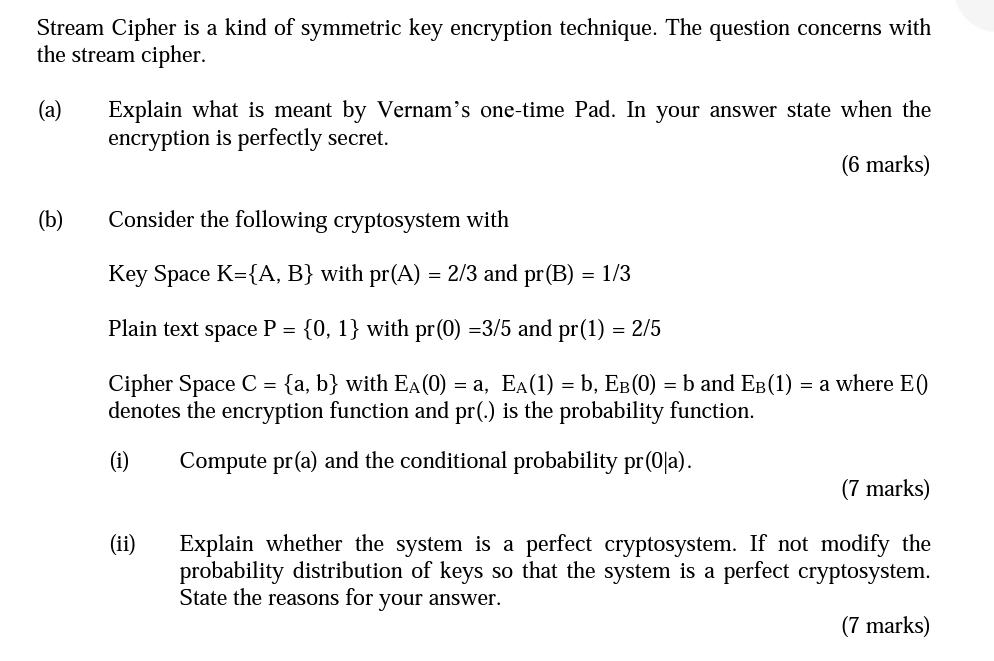
Stream Cipher is a kind of symmetric key encryption technique. The question concerns with the stream cipher. (a) (b) Explain what is meant by Vernam's one-time Pad. In your answer state when the encryption is perfectly secret. (6 marks) Consider the following cryptosystem with Key Space K={A, B} with pr(A) = 2/3 and pr(B) = 1/3 Plain text space P = {0, 1} with pr(0) =3/5 and pr(1) = 2/5 Cipher Space C = {a, b} with EÃ(0) = a, EÃ(1) = b, E³(0) = b and E³ (1) = a where E (0) denotes the encryption function and pr(.) is the probability function. (i) Compute pr(a) and the conditional probability pr(0|a). (ii) (7 marks) Explain whether the system is a perfect cryptosystem. If not modify the probability distribution of keys so that the system is a perfect cryptosystem. State the reasons for your answer. (7 marks) Stream Cipher is a kind of symmetric key encryption technique. The question concerns with the stream cipher. (a) (b) Explain what is meant by Vernam's one-time Pad. In your answer state when the encryption is perfectly secret. (6 marks) Consider the following cryptosystem with Key Space K={A, B} with pr(A) = 2/3 and pr(B) = 1/3 Plain text space P = {0, 1} with pr(0) =3/5 and pr(1) = 2/5 Cipher Space C = {a, b} with EÃ(0) = a, EÃ(1) = b, E³(0) = b and E³ (1) = a where E (0) denotes the encryption function and pr(.) is the probability function. (i) Compute pr(a) and the conditional probability pr(0|a). (ii) (7 marks) Explain whether the system is a perfect cryptosystem. If not modify the probability distribution of keys so that the system is a perfect cryptosystem. State the reasons for your answer. (7 marks)
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
How can you demonstrate the following in the workplace Mutual respect Tolerance of diversity ?
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Factor completely. 3(r + 5) - 11(r + 5) 4
-
An X-ray scattering from a free electron is observed to change its wavelength by 3.03 pm. At what angle to the incident direction does the scattered X-ray move?
-
What are the salient factors that have contributed to the evolution of the PSM profession?
-
Presented below are selected financial data for two competitors. Discuss why the return onequity decreased for each firm. Company X. Company Y. Return on Equity Return Financial on Sales Asset...
-
Dr. Sherry Bird is employed by Dental Associates. Dental Associates recently installed a computerized job-order costing system to help monitor the cost of its services. Each patient is treated as a...
-
Current Attempt in Progress Your answer is partially correct. Wayne Company is considering a long-term investment project called ZIP.ZIP will require an investment of $120,000. It will have a useful...
-
Give a correct name for a. (CH3)2CHCH2OCH2CH3 b. c. O- CH2CH2CH,
-
Del Gato Clinic's cash account shows an $13,899 debit balance and its bank statement shows $12,886 on deposit at the close of business on June 30. a. Outstanding checks as of June 30 total $1.131. b....
-
1. Why do you think college grads earn so much more than those who start but doesn't complete a degree? 2. Do you think wage gaps based on educational attainment will increase or decrease in the...
-
CONTEXT Agridex Industries has grown out of the amalgamation of more than twenty small-scale producers of pork. Originally, each of the companies operated independently, and established its own...
-
Interview of a person from another generation It should be apparent to you by now that Native Americans value their ancestors. After all, the wisdom of generations resides with our older relatives....
-
1. Use a Lagrange interpolating polynomial of the first and second order to evaluate the value of y at x = 25 based on the data in the following table; X 10 30 50 0.424 7.7 1.6 y a) Solve by hand by...
-
You drive 5.50 km in a straight line in a direction 10 East of North. (a) Find the distances (in km) you would have to drive straight East and then straight North to arrive at the same point. (This...
-
A firm will generate 43% averate return from its optimum investments. The firm needs to borrow $3,865 at a market rate of 15% to maintain its optimum investment of $18,466. Assuming two-period...
-
What is an insurable interest? Why is it important?
-
How would two-factor authentication improve the security of user accounts?
-
How are digital certificates and drivers' licenses similar, and how are they different?
-
(a) What architecture do most firms actually use? (b) In the hybrid TCP/IP-OSI architecture, which layers come from OSI? (d) From what standards architecture do application layer standards come?
-
The consistency principle stipulates that when a company begins using a given inventory valuation method (FIFO, LIFO, or the weighted-average cost method), the company should continue to use that...
-
How does an individual know if all cash transactions have been properly accounted for on the statement of cash flows?
-
How are the cash flows originating from a company's financing activities identified?

Study smarter with the SolutionInn App


