Suppose you are working for a financial institution and you are asked to implement a fraud...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
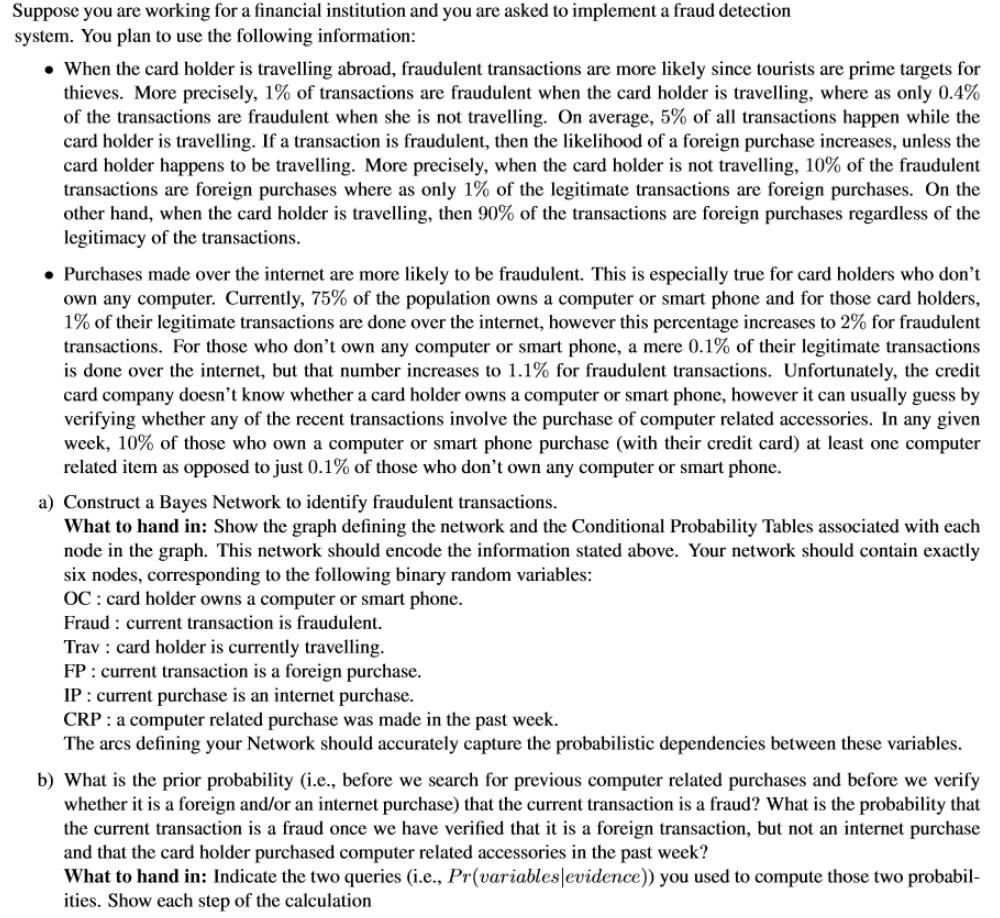
Suppose you are working for a financial institution and you are asked to implement a fraud detection system. You plan to use the following information: • When the card holder is travelling abroad, fraudulent transactions are more likely since tourists are prime targets for thieves. More precisely, 1% of transactions are fraudulent when the card holder is travelling, where as only 0.4% of the transactions are fraudulent when she is not travelling. On average, 5% of all transactions happen while the card holder is travelling. If a transaction is fraudulent, then the likelihood of a foreign purchase increases, unless the card holder happens to be travelling. More precisely, when the card holder is not travelling, 10% of the fraudulent transactions are foreign purchases where as only 1% of the legitimate transactions are foreign purchases. On the other hand, when the card holder is travelling, then 90% of the transactions are foreign purchases regardless of the legitimacy of the transactions. • Purchases made over the internet are more likely to be fraudulent. This is especially true for card holders who don't own any computer. Currently, 75% of the population owns a computer or smart phone and for those card holders, 1% of their legitimate transactions are done over the internet, however this percentage increases to 2% for fraudulent transactions. For those who don't own any computer or smart phone, a mere 0.1% of their legitimate transactions is done over the internet, but that number increases to 1.1% for fraudulent transactions. Unfortunately, the credit card company doesn't know whether a card holder owns a computer or smart phone, however it can usually guess by verifying whether any of the recent transactions involve the purchase of computer related accessories. In any given week, 10% of those who own a computer or smart phone purchase (with their credit card) at least one computer related item as opposed to just 0.1% of those who don't own any computer or smart phone. a) Construct a Bayes Network to identify fraudulent transactions. What to hand in: Show the graph defining the network and the Conditional Probability Tables associated with each node in the graph. This network should encode the information stated above. Your network should contain exactly six nodes, corresponding to the following binary random variables: OC: card holder owns a computer or smart phone. Fraud : current transaction is fraudulent. Trav : card holder is currently travelling. FP : current transaction is a foreign purchase. IP : current purchase is an internet purchase. CRP : a computer related purchase was made in the past week. The arcs defining your Network should accurately capture the probabilistic dependencies between these variables. b) What is the prior probability (i.e., before we search for previous computer related purchases and before we verify whether it is a foreign and/or an internet purchase) that the current transaction is a fraud? What is the probability that the current transaction is a fraud once we have verified that it is a foreign transaction, but not an internet purchase and that the card holder purchased computer related accessories in the past week? What to hand in: Indicate the two queries (i.e., Pr(variables evidence)) you used to compute those two probabil- ities. Show each step of the calculation Suppose you are working for a financial institution and you are asked to implement a fraud detection system. You plan to use the following information: • When the card holder is travelling abroad, fraudulent transactions are more likely since tourists are prime targets for thieves. More precisely, 1% of transactions are fraudulent when the card holder is travelling, where as only 0.4% of the transactions are fraudulent when she is not travelling. On average, 5% of all transactions happen while the card holder is travelling. If a transaction is fraudulent, then the likelihood of a foreign purchase increases, unless the card holder happens to be travelling. More precisely, when the card holder is not travelling, 10% of the fraudulent transactions are foreign purchases where as only 1% of the legitimate transactions are foreign purchases. On the other hand, when the card holder is travelling, then 90% of the transactions are foreign purchases regardless of the legitimacy of the transactions. • Purchases made over the internet are more likely to be fraudulent. This is especially true for card holders who don't own any computer. Currently, 75% of the population owns a computer or smart phone and for those card holders, 1% of their legitimate transactions are done over the internet, however this percentage increases to 2% for fraudulent transactions. For those who don't own any computer or smart phone, a mere 0.1% of their legitimate transactions is done over the internet, but that number increases to 1.1% for fraudulent transactions. Unfortunately, the credit card company doesn't know whether a card holder owns a computer or smart phone, however it can usually guess by verifying whether any of the recent transactions involve the purchase of computer related accessories. In any given week, 10% of those who own a computer or smart phone purchase (with their credit card) at least one computer related item as opposed to just 0.1% of those who don't own any computer or smart phone. a) Construct a Bayes Network to identify fraudulent transactions. What to hand in: Show the graph defining the network and the Conditional Probability Tables associated with each node in the graph. This network should encode the information stated above. Your network should contain exactly six nodes, corresponding to the following binary random variables: OC: card holder owns a computer or smart phone. Fraud : current transaction is fraudulent. Trav : card holder is currently travelling. FP : current transaction is a foreign purchase. IP : current purchase is an internet purchase. CRP : a computer related purchase was made in the past week. The arcs defining your Network should accurately capture the probabilistic dependencies between these variables. b) What is the prior probability (i.e., before we search for previous computer related purchases and before we verify whether it is a foreign and/or an internet purchase) that the current transaction is a fraud? What is the probability that the current transaction is a fraud once we have verified that it is a foreign transaction, but not an internet purchase and that the card holder purchased computer related accessories in the past week? What to hand in: Indicate the two queries (i.e., Pr(variables evidence)) you used to compute those two probabil- ities. Show each step of the calculation
Expert Answer:
Answer rating: 100% (QA)
Step 1 Establish project objectives measurement measures and resource allocationDefining the project goals is the first stage in every data science projectWhat kind of fraud cases did we wish to findW... View the full answer

Related Book For 

Posted Date:
Students also viewed these general management questions
-
Suppose you are working for a company that does business with Australia. Your company has closed a deal where you will provide consulting services to the Australian firm and they will pay you a sum...
-
You are working for a major U.S. corporation that wants to expand its reach globally and has narrowed the search to either Mexico or Japan. Your supervisor has asked you to prepare a memo that...
-
Suppose you are working for a fast-growing startup company, which we will call FastCo, and it is your job to write a software package that can maintain the set, E, of all the employees working for...
-
Dalmo Bhd is an investment holding company and currently it has 3 subsidiaries as stated below. Dalmo Bhd group of companies financial year end is 31st March. The shareholding structure of Dalmo...
-
If you make a lucky prediction about the prices of the stocks of the two companies in Question 1, will you earn more or less if you invest in that company rather than the portfolio?
-
As part of the June 30, 2019, audit of accounts payable of Milner Products Company, the auditor sent 22 confirmations of accounts payable to vendors in the form of requests for statements. Four of...
-
Suppose that \(x_{i}\) only takes on the values 0 and 1. Out of the \(n\) observations, \(n_{1}\) take on the value \(x=0\). The \(n_{1}\) observations have an average \(y\) value of \(\bar{y}_{1}\)....
-
Waymon Co. has net sales of $100,000, cost of goods sold of $70,000, and operating expenses of $18,000. What is its gross profit?
-
Wildhorse Manufacturing Company uses a job order cost system and keeps perpetual inventory records. June 1 Purchased raw materials for $24,400 on account. 8 Raw materials requisitioned by production:...
-
George Pharmacy is a pharmaceutical salesman who has been very successful at his job in the last few years. Unfortunately, his family life has not been very happy. Three years ago, his only child,...
-
The purpose of an organization's mission, vision, and values is to help in defining the future direction of the organization. The mission statement looks at how the organization will make their...
-
Two boxes each have a volume of \(1.50 \mathrm{~m}^{3}\). Box A contains 1000 helium atoms, and box B contains 2000 neon atoms. When the boxes are connected together by a very small tube, the atoms...
-
Show how Rademacher functions are related to Walsh functions. Then, find \(\varphi_{17}\) of a Walsh function set using Rademacher functions.
-
Both cycles in P3.2 and P3.9 resulted in extremely 'wet' steam (low quality) at the exit to the turbine. This would cause erosion of the blades, and should be avoided. One way of achieving this is to...
-
Consider two egg cartons, one with spaces for a dozen eggs and one with spaces for a half-dozen eggs. If each carton contains six eggs, all of different colors, what is the ratio of the number of...
-
The Nagle algorithm, built into most TCP implementations, requires the sender to hold a partial segments worth of data (even if PUSHed) until either a full segment accumulates or the most recent...
-
Choose a country other than the United States and research the following: What are the key diversity concerns for that country? Which groups are dominant and non-dominant? What are the participation...
-
What are the four types of poultry production systems? Explain each type.
-
What is the relationship between corruption in a country (i.e., bribe taking by government officials) and economic growth? Is corruption always bad?
-
What are the economic and political arguments for regional economic integration? Given these arguments, why dont we see more substantial examples of integration in the world economy?
-
Reread the Management Focus box on the alliance between Cisco and Fujitsu. What are the benefits to Cisco and Fujitsu respectively of the alliances? What are the risks to Cisco? How can Cisco...
-
Test the overall significance of a regression model and identify the components of this test from your computer output.
-
Identify the sample.
-
Based on the strategy, what type of sampling technique will be used to identify the sample? a. Why did you choose this type of technique?

Study smarter with the SolutionInn App