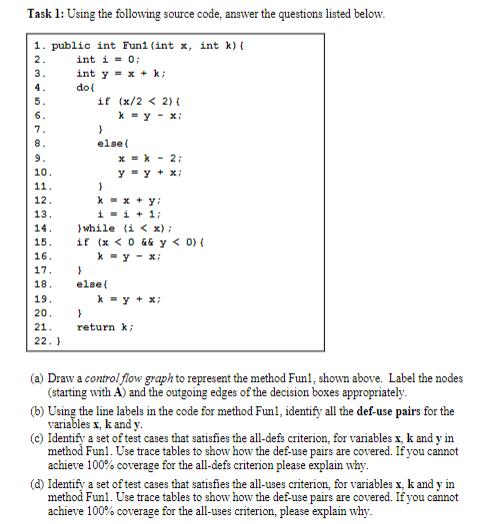
Task 1: Using the following source code, answer the questions listed below. 1. public int Funi...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Task 1: Using the following source code, answer the questions listed below. 1. public int Funi (int x, int k) { 2. int i=0; 3. int y x+k; 4. do ( 5. if (x/2 < 2) { 6. ky x; 7. } 8. else{ 9. xk2; 10. y = y + x; 11. 12. 13. 14. 15. 16. 17. } 18. kxy: i=i+1; while (ix); if (x < 0 && y < 0) { k-y-x; else{ 19. k = y + x; 20. 21. 22.) } return k; (a) Draw a control flow graph to represent the method Fun!, shown above. Label the nodes (starting with A) and the outgoing edges of the decision boxes appropriately. (b) Using the line labels in the code for method Fun!, identify all the def-use pairs for the variables x, k and y. (c) Identify a set of test cases that satisfies the all-defs criterion, for variables x, k and y in method Funl. Use trace tables to show how the def-use pairs are covered. If you cannot achieve 100% coverage for the all-defs criterion please explain why. (d) Identify a set of test cases that satisfies the all-uses criterion, for variables x, k and y in method Funl. Use trace tables to show how the def-use pairs are covered. If you cannot achieve 100% coverage for the all-uses criterion, please explain why. Task 1: Using the following source code, answer the questions listed below. 1. public int Funi (int x, int k) { 2. int i=0; 3. int y x+k; 4. do ( 5. if (x/2 < 2) { 6. ky x; 7. } 8. else{ 9. xk2; 10. y = y + x; 11. 12. 13. 14. 15. 16. 17. } 18. kxy: i=i+1; while (ix); if (x < 0 && y < 0) { k-y-x; else{ 19. k = y + x; 20. 21. 22.) } return k; (a) Draw a control flow graph to represent the method Fun!, shown above. Label the nodes (starting with A) and the outgoing edges of the decision boxes appropriately. (b) Using the line labels in the code for method Fun!, identify all the def-use pairs for the variables x, k and y. (c) Identify a set of test cases that satisfies the all-defs criterion, for variables x, k and y in method Funl. Use trace tables to show how the def-use pairs are covered. If you cannot achieve 100% coverage for the all-defs criterion please explain why. (d) Identify a set of test cases that satisfies the all-uses criterion, for variables x, k and y in method Funl. Use trace tables to show how the def-use pairs are covered. If you cannot achieve 100% coverage for the all-uses criterion, please explain why.
Expert Answer:
Answer rating: 100% (QA)
Answer a Heres the control flow graph CFG for the Fun1 method A ... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
If the focal length of a lens is 3 centimeters and the image distance is 5 centimeters from the lens, what is the distance from the object to the lens?
-
Four hospitals located in one county are cooperating to establish a centralized blood-bank facility to serve them all. On an xy coordinate grid of the county, the hospitals are found at the following...
-
When surveyed for brand recognition, 95% of consumers recognize Coke (based on data from Total Research Corporation). A new survey of 1200 randomly selected consumers is to be conducted. For such a...
-
Simplify the given algebraic expressions. A + (h 2A) 3A
-
Data extracted from a year-end balance sheet are shown below. Compute the working capital for this firm. What would the current ratio be, and what is the significance for this firm? Accounts payable...
-
Martin and Carrie Jones insured their home and personal property under an unendorsed Homeowners 3 policy. The home has a current replacement cost of $300,000. The policy contains the following...
-
6. Three charges qi, q2 and qs are arranged as shown. The charges are 9.5 C, -1.8C and -5.8 C respectively. What is the force acting on q? (6 marks) 0. 91 0.30 m 0.50 m 92 0.40 m 93
-
A Reflective Summary on the Electronic Market Hypothesis please prepare a one-page summary focused on how Malone and his colleagues (1987) utilized the transaction cost approach to arrive at the...
-
For each critical audit matter identified in the current year's audit, PCAOB auditing standards require the auditor's report to include communication of all of the following, except for...
-
Problem 3-4 (Past exam question: 40 minutes) (Text: Ch. 3) Graham Grepzer has come to you in connection with two offers of employment as a salesperson from two rival dry-goods manufacturing...
-
Dale, a 40 year old single taxpayer, incurs medical expenses for the year as follows: Medical insurance premiums: $11,000 Doctors and hospital fees: $3,500 Hearing aids : $ 350 General purpose...
-
David Harbert recently started a business. During the first few days of operation, Mr. Harbert transferred cash from his personal account into a business account for a company he named Harbert...
-
1. Define 5D in your own words. If it was defined as an operation that uses "trochoidal passes with a big and tightly controlled maximal radial engagement", what operation is being referred to? 2. Is...
-
Patching ICS/SCADA systems are riskier than traditional IT systems, and the book refers to three fundamentals of patching ICS/SCADA. Requirement: Find an article about ICS/SCADA patch and /or change...
-
A police officer pulls you over and asks to search your vehicle because he suspects you have illegal drugs inside your car. Since he doesn't have reasonable suspicion to search your car, legally he...
-
Ferns that eject spores generally do so in pairs, with two spores flying off in opposite directions. The structure from which the spores are launched is quite lightweight. If it takes a certain...
-
A dog can provide sufficient power to pull a sled with a 60 N force at a steady 2.0 m/s. Suppose the dog is hitched to a different sled that requires 120 N to move at a constant speed. How fast can...
-
Most of the energy you expend in cycling is dissipated by the drag force. If you double your speed, you increase the drag force by a factor of 4. This increases the power to cycle at this greater...

Study smarter with the SolutionInn App