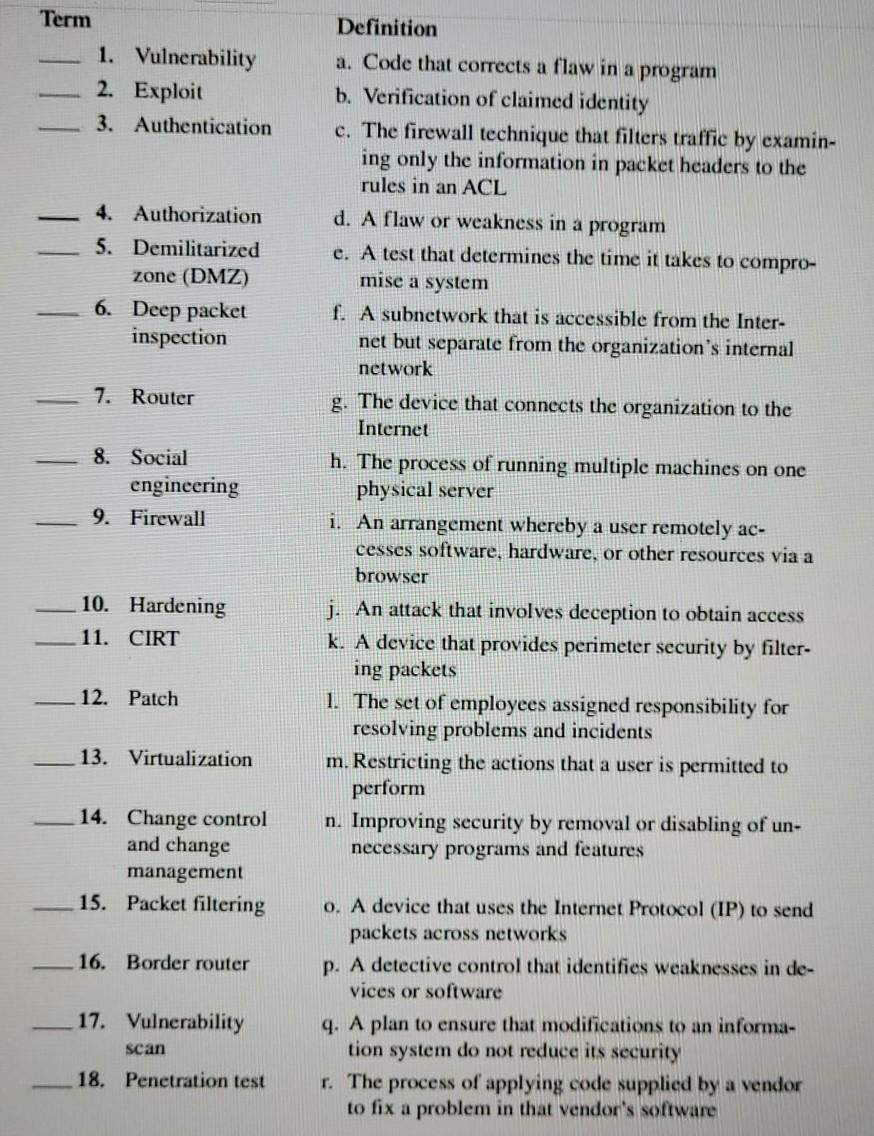
Term - 1. Vulnerability 2. Exploit 3. Authentication 4. Authorization 5. Demilitarized zone (DMZ) 6. Deep...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Term - 1. Vulnerability 2. Exploit 3. Authentication 4. Authorization 5. Demilitarized zone (DMZ) 6. Deep packet inspection 7. Router 8. Social 9. Firewall 10. Hardening 11. CIRT 12. Patch 13. Virtualization 14. Change control and change management 15. Packet filtering 16. Border router 17. Vulnerability scan 18. Penetration test engineering Definition a. Code that corrects a flaw in a program b. Verification of claimed identity c. The firewall technique that filters traffic by examin- ing only the information in packet headers to the rules in an ACL d. A flaw or weakness in a program e. A test that determines the time it takes to compro- mise a system f. A subnetwork that is accessible from the Inter- net but separate from the organization's internal network g. The device that connects the organization to the Internet h. The process of running multiple machines on one physical server i. An arrangement whereby a user remotely ac- cesses software, hardware, or other resources via a browser j. An attack that involves deception to obtain access k. A device that provides perimeter security by filter- ing packets 1. The set of employees assigned responsibility for resolving problems and incidents m. Restricting the actions that a user is permitted to perform n. Improving security by removal or disabling of un- necessary programs and features o. A device that uses the Internet Protocol (IP) to send packets across networks p. A detective control that identifies weaknesses in de- vices or software q. A plan to ensure that modifications to an informa- tion system do not reduce its security r. The process of applying code supplied by a vendor to fix a problem in that vendor's software Term - 1. Vulnerability 2. Exploit 3. Authentication 4. Authorization 5. Demilitarized zone (DMZ) 6. Deep packet inspection 7. Router 8. Social 9. Firewall 10. Hardening 11. CIRT 12. Patch 13. Virtualization 14. Change control and change management 15. Packet filtering 16. Border router 17. Vulnerability scan 18. Penetration test engineering Definition a. Code that corrects a flaw in a program b. Verification of claimed identity c. The firewall technique that filters traffic by examin- ing only the information in packet headers to the rules in an ACL d. A flaw or weakness in a program e. A test that determines the time it takes to compro- mise a system f. A subnetwork that is accessible from the Inter- net but separate from the organization's internal network g. The device that connects the organization to the Internet h. The process of running multiple machines on one physical server i. An arrangement whereby a user remotely ac- cesses software, hardware, or other resources via a browser j. An attack that involves deception to obtain access k. A device that provides perimeter security by filter- ing packets 1. The set of employees assigned responsibility for resolving problems and incidents m. Restricting the actions that a user is permitted to perform n. Improving security by removal or disabling of un- necessary programs and features o. A device that uses the Internet Protocol (IP) to send packets across networks p. A detective control that identifies weaknesses in de- vices or software q. A plan to ensure that modifications to an informa- tion system do not reduce its security r. The process of applying code supplied by a vendor to fix a problem in that vendor's software
Expert Answer:
Answer rating: 100% (QA)
answers Term Definition d 1 Vulnerability a Code that corrects a flaw in a program s 2 Exploit b Ver... View the full answer

Related Book For 

Accounting Information Systems
ISBN: 978-0132552622
12th edition
Authors: Marshall B. Romney, Paul J. Steinbart
Posted Date:
Students also viewed these accounting questions
-
A stateful packet inspection border firewall contains a rule that permits external connections to an internal public webserver. However, the firewall does not permit access to this server. Come up...
-
It takes 16 s to raise a 2800-lb car and the supporting 650-lb hydraulic car-lift platform to a height of 6.5 ft. Knowing that the overall conversion efficiency from electric to mechanical power for...
-
A test of filtering software examined a sample of n = 100 messages. If the filtering software reduces the level of spam to 15%, this test only has a 33% chance of correctly rejecting H0: p 0.20....
-
Elizabeth Is a nurse, and she just administered 1.8 milliliters of medication to one of her patients. Elizabeth knows that the amount of medication remaining in the patient's body wi decrease by a...
-
Comment on the accuracy of the following statement: Since both significant deficiencies and material weaknesses must be reported to the audit committee, for practical purposes, there is no...
-
The diagram shows a triangle ABC in which A is (3, 2) and B is (15, 22). The gradients of AB, AC and BC are 2m, 2m and m respectively, where m is a positive constant. i. Find the gradient of AB and...
-
Explain why collaborative filtering is such a useful technique. How successful do you believe it can be? What might limit its efficacy?
-
A ventilation system has been designed for a large laboratory with a volume of 1100 m3. The volumetric flow rate of ventilation air is 700 m3/min at 22C and 1 atm. (The latter two values may also be...
-
(a) find the language accepted by the automaton in the referenced exercise, and (b) find a regular expression that defines the same language. 1 So 0 0 $3 1 $1 1 $2 1 0
-
2 Assume Airport "Zidlohovice" estimated its cost function as follows: C(q) = 100,000,000+ 0.1-q. C(q) is the total cost in PLN; q is the amount of take-offs and landings. Your demand for the current...
-
Given the following values R = 52, L = L= 2 H, C = 2 nF and C = 8 F. i, (t) C R ele i,(1) L |i (1) L (a) What is the order of the circuit? Explain. (b) Derive the characteristic equation for e(t)....
-
You have a new job at McDonald's, and your first assignment is to design a kiosk that will allow customers to place their orders. Your supervisor asks you how you will go about doing requirements...
-
5. An investment firm has just been instructed by one of its clients to invest $1,500,000 of his money. The client's goal is to maximize total projected return on investments. The analysts at the...
-
A pizza store is staffed by two employees: a pizza chef and an assistant. The store has an oven that can only bake one pizza at a time. The transformation process (sequence of steps) followed at the...
-
Which one of the following plots is an accurate representation of the number of G's of force vs. time for a single parabolic maneuver? A # of Gs # of Gs a. time (s) C time (s) 60 60 # of Gs # of Gs 0...
-
A flute may be thought of as a pipe open at both ends. When all the holes of a well-designed flute are covered and the temperature is 20.0C, it will produce sound with a frequency of 261.6 Hz (middle...
-
Demand is Normally distributed with mean of 28 per week and a weekly variance of 9. The ordering cost is $36.41. Lead time is 4 weeks. Shortages cost an estimated $1.84 per unit short to expedite...
-
Express these numbers in standard notation. a. 2.87 10-8 b. 1.78 1011 c. 1.381 10-23
-
Match the following terms with their definitions: 1. Business continuity plan (BCP) 2. Completeness check 3. Hash total 4. Incremental daily backup 5. Archive 6. Field check 7. Sign check 8. Change...
-
Create the spreadsheet shown in Figure 14-11. Write formulas to calculate the total depreciation expense and to display the correct values in the following three columns: Age, Depreciation Rate, and...
-
Match the following terms with their definitions TERM a. Data processing b. Source documents c. Turnaround documents d. Source data automation e. General ledger f. Subsidiary ledger g. Control...
-
Identify at least four methods by which investors and/or the entrepreneur in a new venture can harvest their investment in a new venture. Describe the costs and benefits of each, and provide a...
-
What are the key distinctions between corporate finance and entrepreneurial finance?
-
Explain what underpricing is and review the various explanations for why it might occur. How does underpricing figure into the cost of going public?

Study smarter with the SolutionInn App