The code below implements a function QU2 which has an input arr of type Array of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
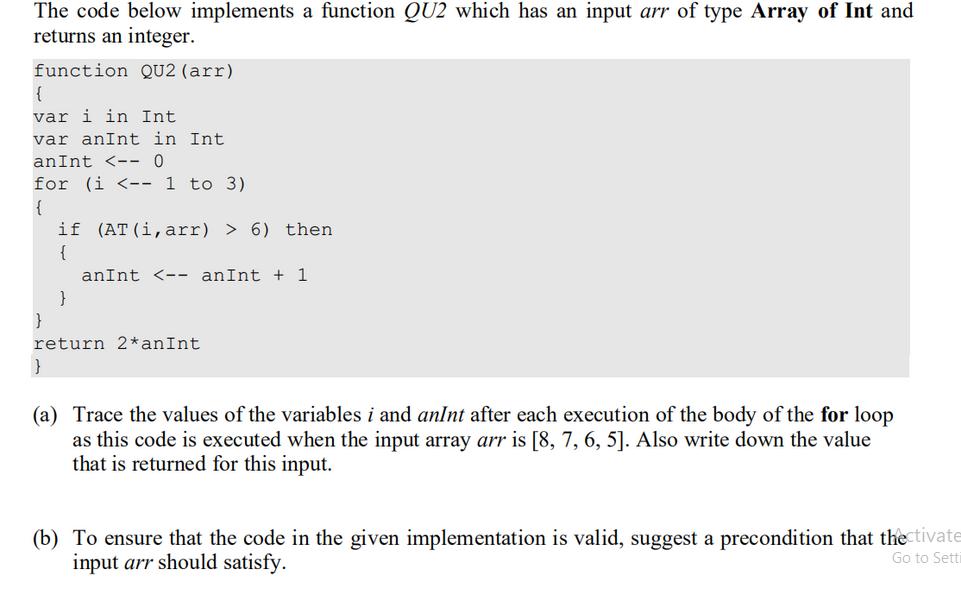
The code below implements a function QU2 which has an input arr of type Array of Int and returns an integer. function QU2 (arr) { var i in Int var anInt in Int anInt <-- 0 for (i <-- 1 to 3) { if (AT (i, arr) > 6) then { } anInt <-- an Int + 1 return 2* an Int } (a) Trace the values of the variables i and anInt after each execution of the body of the for loop as this code is executed when the input array arr is [8, 7, 6, 5]. Also write down the value that is returned for this input. (b) To ensure that the code in the given implementation is valid, suggest a precondition that the tivate input arr should satisfy. Go to Setti The code below implements a function QU2 which has an input arr of type Array of Int and returns an integer. function QU2 (arr) { var i in Int var anInt in Int anInt <-- 0 for (i <-- 1 to 3) { if (AT (i, arr) > 6) then { } anInt <-- an Int + 1 return 2* an Int } (a) Trace the values of the variables i and anInt after each execution of the body of the for loop as this code is executed when the input array arr is [8, 7, 6, 5]. Also write down the value that is returned for this input. (b) To ensure that the code in the given implementation is valid, suggest a precondition that the tivate input arr should satisfy. Go to Setti
Expert Answer:
Related Book For 

Posted Date:
Students also viewed these programming questions
-
Example(2). Maximize Z (S) = 40 x + 50x2 Subject to x1 + 2x 2 40 4x1 + 3x2 120 xx20
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Use any method to evaluate the limit or show that it does not exist. lim (x,y) (0,0) x - y x + y
-
A box holding pennies, nickels and dimes contains thirteen coins with a total value of 83 cents. How many coins of each type are in the box? (These are US coins; a penny is 1 cent, a nickel is 5...
-
The following table provides a revenue analysis for Crocs Inc. from 2019 to 2020. In this table, Crocs reports their wholesale revenues recognized by each of its three reportable segments (and...
-
Forms are provided in the Working Papers. Obtain the present value factors from the tables in the lesson illustrations. Your instructor will guide you through the following examples. 1. Calculate the...
-
Major Bill Bligh, director of the Army War College's new 6-month attach training program, is concerned about how the 20 officers taking the course spend their precious time while in his charge. Major...
-
Journalize the following transactions for Sheridan Company. (a) Purchased 5,900 units of raw materials on account for $16,930. The standard cost was $17,700. (b) Issued 5,800 units of raw materials...
-
On January 1, 2019, Concord Corp. signs a contract to lease nonspecialized manufacturing equipment from Stone Inc. Concord agrees to make lease payments of $47,500 per year. Additional information...
-
Given the method mystery below, show all output printed for the method call mystery(test), where test is the array [15, 20, 25, 30]. Write down JUST the output. public static void systery(int[] arr)...
-
Illustrate and define typical symbols for horizontal flowcharts and for vertical flowcharts.
-
Which of the following most likely represents a weakness in internal con- trol of an IT system? a. The systems analyst reviews output and controls the distribution of output from the IT department....
-
What is an easy way to identify control points when preparing flowcharts? What are control points?
-
Which car is more likely to be more fuel-efficient: one with sharp corners or one that is contoured to resemble an ellipse? Why?
-
What is an ICQ?
-
The figure to the right shows the area of regions bounded by the graph of f and the x-axis. Evaluate the following integral. ff(x)dx a a [f(x)dx=(Type an integer or a simplified fraction.) (...) 0 15...
-
suppose a nickel-contaminated soil 15 cm deep contained 800 mg/kg Ni, Vegetation was planted to remove the nickel by phytoremediation. The above-ground plant parts average 1% Ni on a dry-weight bas...
-
Write a program that uses the following functions: Fill_array() takes as arguments the name of an array of double values and an array size. It prompts the user to enter double values to be entered in...
-
Suppose your main() function has the following line: cout < < Please enter your PIN: ; And suppose the compiler complains that cout is an unknown identifier.What is the likely cause of this...
-
Write a program that requests the user to enter two integers.The program should then calculate and report the sum of all the integers between and including the two integers. At this point, assume...
-
Browne \& Company has no-par value common stock outstanding that is selling at \(\$ 40\) per share. The company's CEO believes that the stock price is undervalued and decides to buy back 10,000...
-
Calculate the dividend yield for Evans \& Sons for 2018 and 2019. Did the dividend yield improve from 2018 to 2019? Evans \& Sons, Inc., disclosed the following information in a recent annual report:...
-
Calculate the dividend payout for Evans \& Sons for 2018 and 2019. Did the dividend payout increase from 2018 to 2019 ? Evans \& Sons, Inc., disclosed the following information in a recent annual...

Study smarter with the SolutionInn App