The following are the password rules used by a web site: A password must be...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
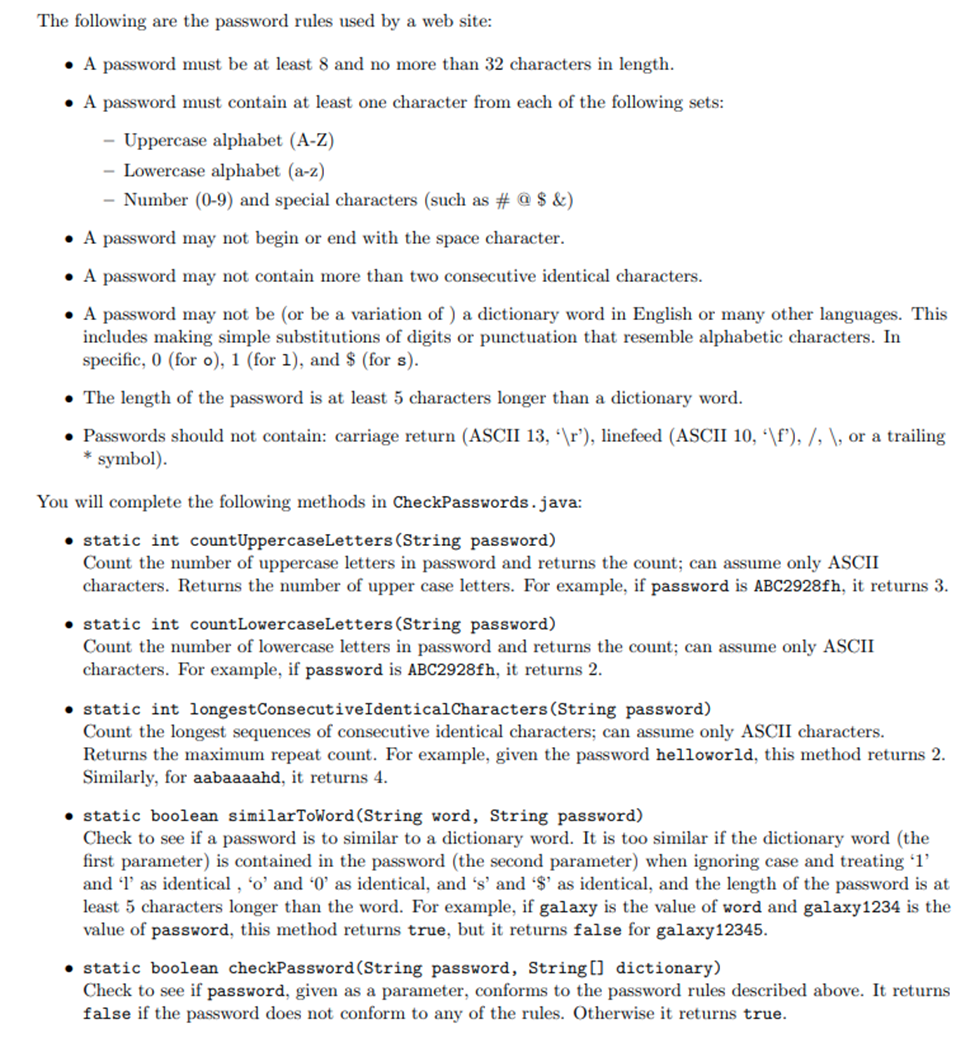
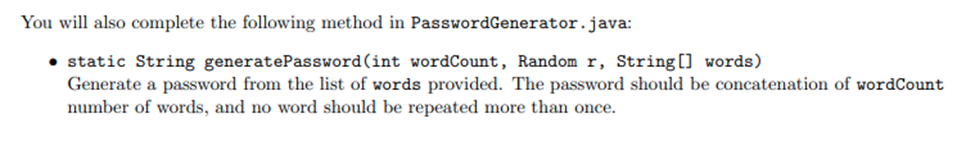
The following are the password rules used by a web site: • A password must be at least 8 and no more than 32 characters in length. • A password must contain at least one character from each of the following sets: Uppercase alphabet (A-Z) - Lowercase alphabet (a-z) - Number (0-9) and special characters (such as # @ $ &) • A password may not begin or end with the space character. • A password may not contain more than two consecutive identical characters. • A password may not be (or be a variation of) a dictionary word in English or many other languages. This includes making simple substitutions of digits or punctuation that resemble alphabetic characters. In specific, 0 (for o), 1 (for 1), and $ (for s). • The length of the password is at least 5 characters longer than a dictionary word. • Passwords should not contain: carriage return (ASCII 13, \r'), linefeed (ASCII 10, \f'), /, \, or a trailing symbol). You will complete the following methods in CheckPasswords.java: • static int countUppercaseLetters (String password) Count the number of uppercase letters in password and returns the count; can assume only ASCII characters. Returns the number of upper case letters. For example, if password is ABC2928fh, it returns 3. static int countLowercaseLetters (String password) Count the number of lowercase letters in password and returns the count; can assume only ASCII characters. For example, if password is ABC2928fh, it returns 2. static int longest Consecutive Identical Characters (String password) Count the longest sequences of consecutive identical characters; can assume only ASCII characters. Returns the maximum repeat count. For example, given the password helloworld, this method returns 2. Similarly, for aabaaaahd, it returns 4. • static boolean similarToWord (String word, String password) Check to see if a password is to similar to a dictionary word. It is too similar if the dictionary word (the first parameter) is contained in the password (the second parameter) when ignoring case and treating '1' and 'l' as identical, 'o' and '0' as identical, and 's' and '$' as identical, and the length of the password is at least 5 characters longer than the word. For example, if galaxy is the value of word and galaxy1234 is the value of password, this method returns true, but it returns false for galaxy12345. static boolean checkPassword (String password, String[] dictionary) Check to see if password, given as a parameter, conforms to the password rules described above. It returns false if the password does not conform to any of the rules. Otherwise it returns true. You will also complete the following method in PasswordGenerator.java: static String generatePassword (int wordCount, Random r, String[] words) Generate a password from the list of words provided. The password should be concatenation of wordCount number of words, and no word should be repeated more than once. • Format the code clearly with blank lines, spacing and indents • Use self-documenting, meaningful variable names • Use variable names that begin with lower case and then camel case (e.g., roomTemp if two words • Use capital letters (e.g., ALL_CAPS) for variables that encodes constant values that aren't updated • Use appropriate comments that indicate what a section, or a complicated line, does The following are the password rules used by a web site: • A password must be at least 8 and no more than 32 characters in length. • A password must contain at least one character from each of the following sets: Uppercase alphabet (A-Z) - Lowercase alphabet (a-z) - Number (0-9) and special characters (such as # @ $ &) • A password may not begin or end with the space character. • A password may not contain more than two consecutive identical characters. • A password may not be (or be a variation of) a dictionary word in English or many other languages. This includes making simple substitutions of digits or punctuation that resemble alphabetic characters. In specific, 0 (for o), 1 (for 1), and $ (for s). • The length of the password is at least 5 characters longer than a dictionary word. • Passwords should not contain: carriage return (ASCII 13, \r'), linefeed (ASCII 10, \f'), /, \, or a trailing symbol). You will complete the following methods in CheckPasswords.java: • static int countUppercaseLetters (String password) Count the number of uppercase letters in password and returns the count; can assume only ASCII characters. Returns the number of upper case letters. For example, if password is ABC2928fh, it returns 3. static int countLowercaseLetters (String password) Count the number of lowercase letters in password and returns the count; can assume only ASCII characters. For example, if password is ABC2928fh, it returns 2. static int longest Consecutive Identical Characters (String password) Count the longest sequences of consecutive identical characters; can assume only ASCII characters. Returns the maximum repeat count. For example, given the password helloworld, this method returns 2. Similarly, for aabaaaahd, it returns 4. • static boolean similarToWord (String word, String password) Check to see if a password is to similar to a dictionary word. It is too similar if the dictionary word (the first parameter) is contained in the password (the second parameter) when ignoring case and treating '1' and 'l' as identical, 'o' and '0' as identical, and 's' and '$' as identical, and the length of the password is at least 5 characters longer than the word. For example, if galaxy is the value of word and galaxy1234 is the value of password, this method returns true, but it returns false for galaxy12345. static boolean checkPassword (String password, String[] dictionary) Check to see if password, given as a parameter, conforms to the password rules described above. It returns false if the password does not conform to any of the rules. Otherwise it returns true. You will also complete the following method in PasswordGenerator.java: static String generatePassword (int wordCount, Random r, String[] words) Generate a password from the list of words provided. The password should be concatenation of wordCount number of words, and no word should be repeated more than once. • Format the code clearly with blank lines, spacing and indents • Use self-documenting, meaningful variable names • Use variable names that begin with lower case and then camel case (e.g., roomTemp if two words • Use capital letters (e.g., ALL_CAPS) for variables that encodes constant values that aren't updated • Use appropriate comments that indicate what a section, or a complicated line, does
Expert Answer:
Answer rating: 100% (QA)
static boolean checkPasswordString passwordString dictionary Regex to check vali... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these programming questions
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
1. Write a program that translates a letter grade into a number grade. Letter grades are A, B, C, D, and F, possibly followed by + or -. Their numeric values are 4, 3, 2, 1 and 0. There is no F+ or...
-
Write a program, in Java, to convert from binary to decimal andfrom from binary to hexadecimal. Please use instance variables,preferably strings. The program must do the conversion withoutusing any...
-
At December 31, 2017, Nicholay Industries reports the following selected accounts from the unadjusted trial balance for its first year of operations: Instructions (a) Prepare the journal entry to...
-
A student group maintains that each day, the average student must travel at least 25 minutes one way to reach the college. The college admissions office obtained a random sample of 31 one-way travel...
-
If \(r\) is a CIR process and \(Z=r^{\alpha}\), prove that \[d Z_{t}=\left(\alpha Z_{t}^{1-1 / \alpha}\left(k \theta+(\alpha-1) \sigma^{2} / 2 ight)-Z_{t} \alpha k ight) d t+\alpha Z_{t}^{1-1 /(2...
-
Rochester Enterprises Purchased 500 shares of Newark Corporation for $15 per share on June 15, 2011, when Newark had approximately 10,000 equity shares outstanding. Rochester held the investment...
-
A successful marketing and strategy plan hinges on a deep understanding of your business, goals, target audience, and market conditions. Discuss?
-
A nonprofit organization has received a donation of $100,000 to be used to purchase a new van for transporting clients to and from medical appointments. The organization has received two quotes for...
-
The bank is offering a 25 year amortized mortgage loan at 5.25 percent with a 5 year term. a. Calculate your monthly payments for this loan. Show your work! (4 marks) b. Prepare an amortization table...
-
Jesse makes lamps. If he has $10,000 in fixed costs to produce his lamps, the product sells for $50, and the variable cost per unit is $25, How many lamps will Jesse need to sell to break even?
-
A researcher reports there is a statistically significant difference (p value = .01) in job satisfaction scores between male and female lawyers. The final sample size was adequate for an alpha of .05...
-
Giant Koala Stores Inc. has forecasted sales for July through October in the top row of the table. Purchases are 65% of sales. All purchases are made one month in advance of the sale. Ten percent...
-
Donovan Dressler has decided to try and cut his overhead by working from home. His mother is helping him with day-to-day office tasks until he can afford a new assistant. On Monday he returned from...
-
Write a local function called cosLineWidths that will plot cos (x) for x values ranging from - pi to pi in steps of 0.1, using black *'s. It will do this three times across in one Figure Window, with...
-
Suppose the market is semistrong form efficient. Can you expect to earn excess returns if you make trades based on? a. Your brokers information about record earnings for a stock? b. Rumors about a...
-
Patty Bayan is a single taxpayer living at 543 Space Drive, Houston, TX 77099. Her Social Security number is 466-33-1234. For 2012, Patty has no dependents, and her W-2 from her job at a local...
-
Cypress Corporation has regular taxable income of $170,000 (assume annual gross receipts are greater than $5 million) and regular tax liability of $49,550 for 2012. The corporation also has tax...
-
Your supervisor has asked you to research the following situation concerning Owen and Lisa Cordoncillo. Owen and Lisa are brother and sister. In May 2012, Owen and Lisa exchange business pickup...
-
The pendulum on a grandfather clock has a period of 2.00 s. If the clock is not wound, the pendulums amplitude begins to decay at a rate of 0.53% each pendulum period. a. What is the time constant of...
-
A block with a mass of 0.28 kg is attached to a horizontal spring. The block is pulled back from its equilibrium position until the spring exerts a force of 1.0 N on the block. When the block is...
-
The motion of a nightingales wingtips can be modeled as simple harmonic motion. In one study, the tips of a birds wings were found to move up and down with an amplitude of 8.8 cm and a period of 0.82...

Study smarter with the SolutionInn App


