The following security controls should be applied to the application (check the NIST Security Controls Database for
Question:
The following security controls should be applied to the application (check the NIST Security Controls
Database for details, description, and guidance for each control:
- AC-7 - UNSUCCESSFUL LOGON ATTEMPTS
- AC-8 - SYSTEM USE NOTIFICATION
- AU-3 - CONTENT OF AUDIT RECORDS
- AU-8 - TIME STAMPS
- IA-2(1) IDENTIFICATION AND AUTHENTICATION (ORGANIZATIONAL USERS) | NETWORK
ACCESS TO PRIVILEGED ACCOUNTS (Note this is an enhancement of an existing low-impact
security control)
- Select one additional low-impact security control and implement it. This can be an
enhancement or a required low-impact security control. Selecting a control that provides
documentation as opposed to code changes is also acceptable and encouraged.
Hints:
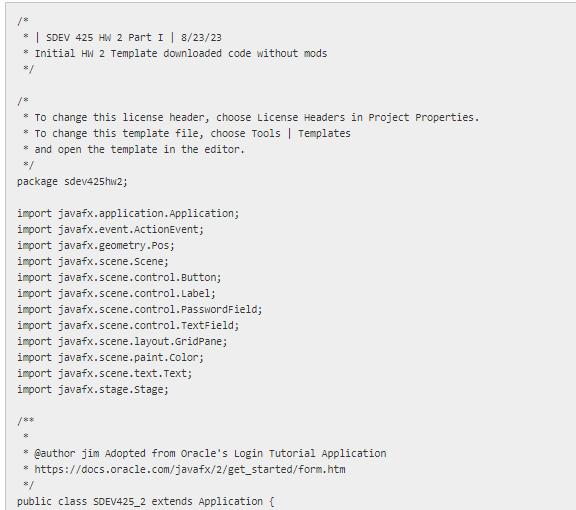
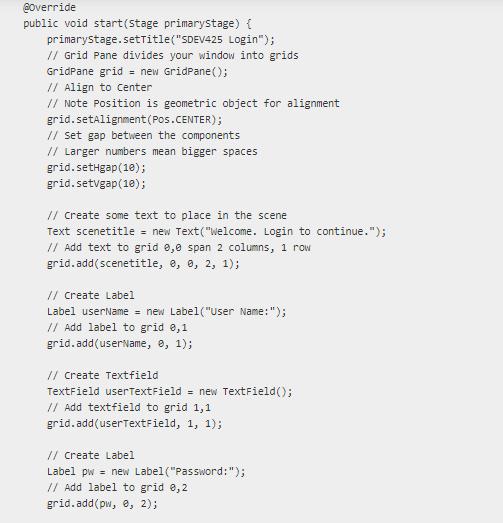
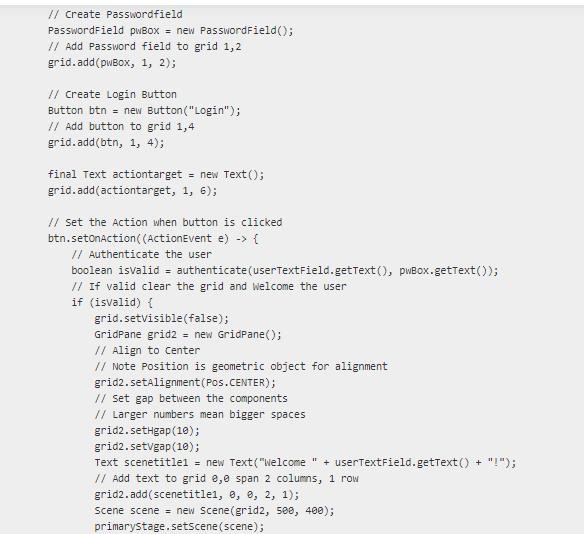
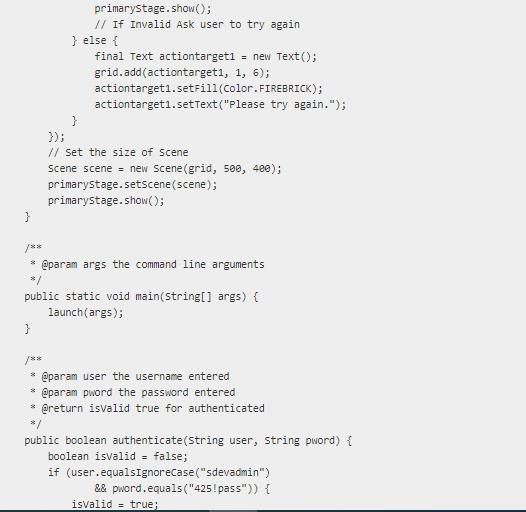
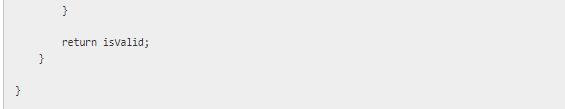
a. Start with the baseline Login Application and add methods (or additional classes) as needed to
comply with each of the security controls.
b. You will need to make some decisions for the implementation of the security audit/log files
format.
c. For the multi-factor authentication, keep it simple. One approach is to send an email to the user
with a security code. Then, have them check their email and enter the code. If the code
matches, they are properly authenticated.
d. JavaMail
e. Pay attention to the details of the NIST database description and make sure all of the selected
security controls for this project are fully implemented.
Looking for some additional guidance on how to apply these NIST security controls to the application in the code above.

Accounting Information Systems
ISBN: 9780132871938
11th Edition
Authors: George H. Bodnar, William S. Hopwood