The following tables illustrate a list of RIS-V instruction formats and a list of RISC-V instructions...
Fantastic news! We've Found the answer you've been seeking!
Question:

Transcribed Image Text:
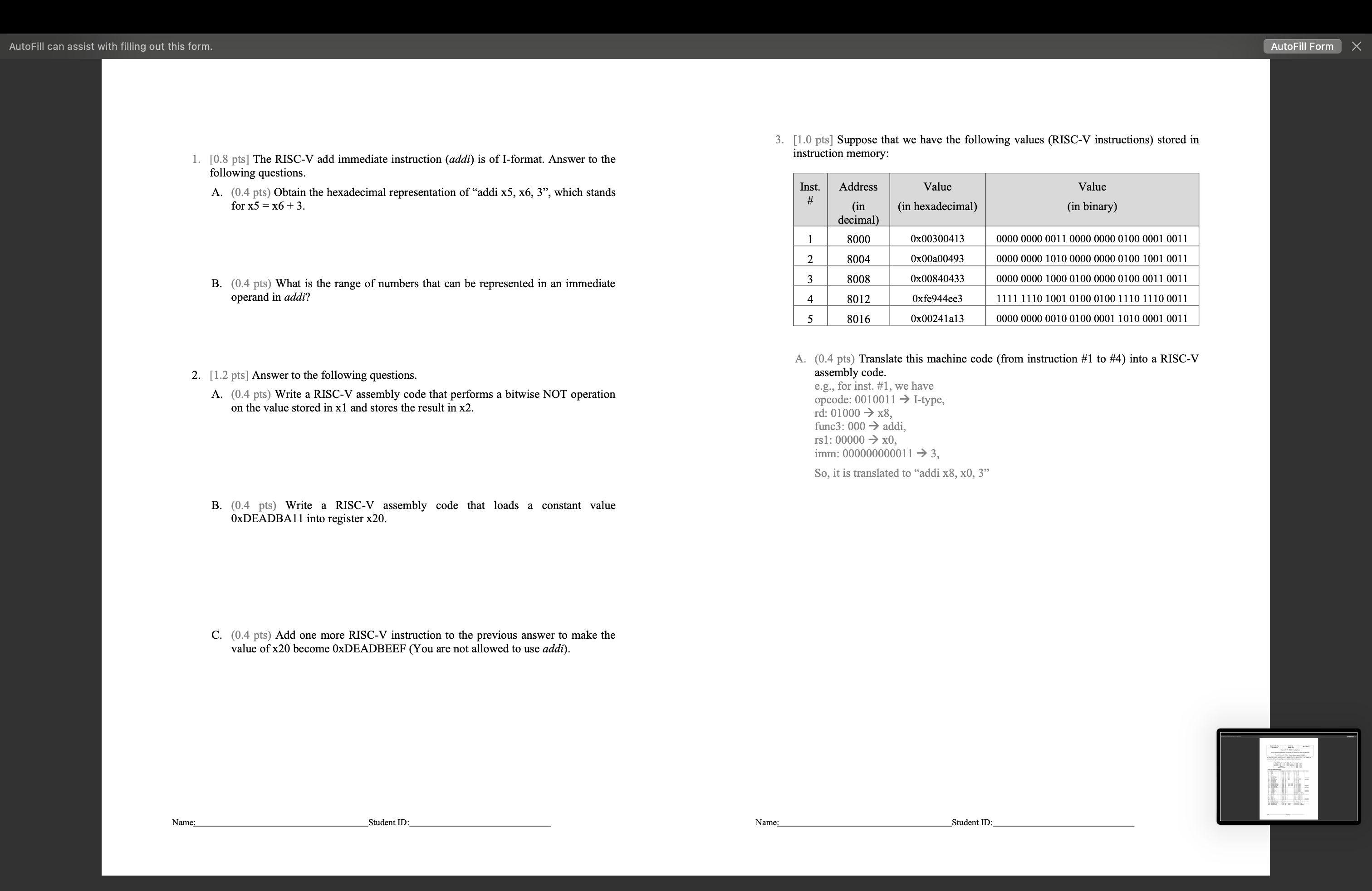
The following tables illustrate a list of RIS-V instruction formats and a list of RISC-V instructions and the corresponding opcode and funct3/func7 information. Core Instruction Formats xor or and sll srl sra slt sltu addi xori ori andi slli srli srai slti sltiu RV321 Base Integer Instructions Inst add sub lb 1h lw lbu 1hu sb sh SW beq bne blt bge bltu bgeu jal jalr lui auipc ecall ebreak Name: 31 Name ADD SUB XOR OR 27 26 25 24 funct7 rs2 imm[11:0] imm[11:5] imm [12 10:5] AND Shift Left Logical Shift Right Logical Shift Right Arith* Set Less Than Set Less Than (U) ADD Immediate XOR Immediate OR Immediate AND Immediate Shift Left Logical Imm Shift Right Logical Imm Shift Right Arith Imm Set Less Than Imm Store Byte Store Half Store Word Set Less Than Imm (U) Load Byte Load Half Load Word Load Byte (U) Load Half (U) Branch == Branch != Branch < Branch > Branch < (U) Branch > (U) rs2 rs2 imm[31:12] imm[20 10:1|11|19:12] Jump And Link Jump And Link Reg Load Upper Imm Add Upper Imm to PC Environment Call Environment Break I I 20 19. FMT Opcode R R R R R R R R R R I I I I I I I I I I I I S S S B B B B B B J I rs1 rs1 rs1 rs1 U U I I 15 14 12 11. funct3 rd funct3 rd funct3 imm[4:0] funct3 imm[4:1|11] rd rd funct3 0110011 0x0 0110011 0x0 0110011 0x4 0110011 0x6 0110011 0x7 0110011 0x1 0110011 0x5 0110011 0x5 0110011 0x2 0110011 0x3 0010011 0x0 0010011 0x4 0010011 0x6 0010011 0x7 0010011 0x1 0010011 0x5 0010011 0x5 0010011 0x2 0010011 0x3 0000011 exe 0000011 0x1 0000011 0x2 0000011 0x4 0000011 0x5 0100011 0x0 0100011 0x1 0100011 0x2 1100011 exe 1100011 0x1 1100011 0x4 1100011 0x5 1100011 0x6 1100011 0x7 1101111 1100111 0x0 0110111 0010111 1110011 0x0 1110011 0x0 funct7 0x00 0x20 0x00 0x00 0x00 0x00 0x00 0x20 0x00 0x00 7 imm=0x0 imm=0x1 Student ID: 6 0 Description (C) rd = rs1 + rs2 rd rs1 rs2 rd = rs1 rs2 rd rs1 < < rs2 rd = rs1 >> rs2 rd = rs1 >> rs2 rd rd rd rs1+ imm rd = rs1 imm rd rs1 | imm rd rs1 & imm rd imm[5:11]=0x00 imm[5:11]=0x00 imm[5:11]=0x20 rd rs1 >> imm[0:4] rs1 < < imm[0:4] rd = rs1 >> imm[0:4] (rs1 < imm)?1:0 rd rd rd rd rd rd M[rs1+imm][0:7] rd M[rs1+imm] [0:15] M[rs1+imm] [0:7] = rs2[0:7] M[rs1+imm] [0:15] = rs2[0:15] M[rs1+imm][0:31] = rs2[0:31] rs2) PC += imm if(rs1 != rs2) PC += imm if(rs1 rs2) PC += imm if(rs1 if(rs1 rs2) PC += imm if(rs1 rs2) PC += imm if(rs1 rs2) PC += imm PC+4; PC += imm PC+4; PC = rs1 + imm imm < < 12 PC+ (imm < < <12) Transfer control to OS Transfer control to debugger rd rd opcode R-type opcode I-type opcode S-type opcode B-type opcode U-type opcode J-type rd = rs1 | rs2 rd = rs1 & rs2 rd rd (rs1 < rs2)?1:0 (rs1 < rs2)?1:0 (rs1 < imm)?1:0 M[rs1+imm] [0:7] M[rs1+imm] [0:15] M[rs1+imm] [0:31] Note msb-extends zero-extends msb-extends zero-extends zero-extends zero-extends zero-extends zero-extends AutoFill can assist with filling out this form. 1. [0.8 pts] The RISC-V add immediate instruction (addi) is of I-format. Answer to the following questions. A. (0.4 pts) Obtain the hexadecimal representation of "addi x5, x6, 3", which stands for x5 x6 +3. Name: B. (0.4 pts) What is the range of numbers that can be represented in an immediate operand in addi? 2. [1.2 pts] Answer to the following questions. A. (0.4 pts) Write a RISC-V assembly code that performs a bitwise NOT operation on the value stored in x1 and stores the result in x2. B. (0.4 pts) Write a RISC-V assembly code that loads a constant value 0xDEADBA11 into register x20. C. (0.4 pts) Add one more RISC-V instruction to the previous answer to make the value of x20 become 0xDEADBEEF (You are not allowed to use addi). Student ID: 3. [1.0 pts] Suppose that we have the following values (RISC-V instructions) stored in instruction memory: Name: Inst. Address # (in decimal) 8000 8004 8008 8012 8016 1 2 3 4 5 Value (in hexadecimal) 0x00300413 0x00a00493 0x00840433 Oxfe944ee3 0x00241a13 e.g., for inst. #1, we have opcode: 0010011 I-type, A. (0.4 pts) Translate this machine code (from instruction #1 to #4) into a RISC-V assembly code. rd: 01000x8, func3: 000 addi, rs1: 00000 x0, imm: 000000000011 3, So, it is translated to "addi x8, x0, 3" Value (in binary) Student ID: 0000 0000 0011 0000 0000 0100 0001 0011 0000 0000 1010 0000 0000 0100 1001 0011 0000 0000 1000 0100 0000 0100 0011 0011 1111 1110 1001 0100 0100 1110 1110 0011 0000 0000 0010 0100 0001 1010 0001 0011 AutoFill Form 1 -G ( x AutoFill can assist with filling out this form. Name: Page 4 of 4 B. (0.2 pts) Among the above five instructions, how many of them are of B-type? C. (0.4 pts) What is the value stored in x20 after executing instruction #5? Student ID: AutoFill Form x The following tables illustrate a list of RIS-V instruction formats and a list of RISC-V instructions and the corresponding opcode and funct3/func7 information. Core Instruction Formats xor or and sll srl sra slt sltu addi xori ori andi slli srli srai slti sltiu RV321 Base Integer Instructions Inst add sub lb 1h lw lbu 1hu sb sh SW beq bne blt bge bltu bgeu jal jalr lui auipc ecall ebreak Name: 31 Name ADD SUB XOR OR 27 26 25 24 funct7 rs2 imm[11:0] imm[11:5] imm [12 10:5] AND Shift Left Logical Shift Right Logical Shift Right Arith* Set Less Than Set Less Than (U) ADD Immediate XOR Immediate OR Immediate AND Immediate Shift Left Logical Imm Shift Right Logical Imm Shift Right Arith Imm Set Less Than Imm Store Byte Store Half Store Word Set Less Than Imm (U) Load Byte Load Half Load Word Load Byte (U) Load Half (U) Branch == Branch != Branch < Branch > Branch < (U) Branch > (U) rs2 rs2 imm[31:12] imm[20 10:1|11|19:12] Jump And Link Jump And Link Reg Load Upper Imm Add Upper Imm to PC Environment Call Environment Break I I 20 19. FMT Opcode R R R R R R R R R R I I I I I I I I I I I I S S S B B B B B B J I rs1 rs1 rs1 rs1 U U I I 15 14 12 11. funct3 rd funct3 rd funct3 imm[4:0] funct3 imm[4:1|11] rd rd funct3 0110011 0x0 0110011 0x0 0110011 0x4 0110011 0x6 0110011 0x7 0110011 0x1 0110011 0x5 0110011 0x5 0110011 0x2 0110011 0x3 0010011 0x0 0010011 0x4 0010011 0x6 0010011 0x7 0010011 0x1 0010011 0x5 0010011 0x5 0010011 0x2 0010011 0x3 0000011 exe 0000011 0x1 0000011 0x2 0000011 0x4 0000011 0x5 0100011 0x0 0100011 0x1 0100011 0x2 1100011 exe 1100011 0x1 1100011 0x4 1100011 0x5 1100011 0x6 1100011 0x7 1101111 1100111 0x0 0110111 0010111 1110011 0x0 1110011 0x0 funct7 0x00 0x20 0x00 0x00 0x00 0x00 0x00 0x20 0x00 0x00 7 imm=0x0 imm=0x1 Student ID: 6 0 Description (C) rd = rs1 + rs2 rd rs1 rs2 rd = rs1 rs2 rd rs1 < < rs2 rd = rs1 >> rs2 rd = rs1 >> rs2 rd rd rd rs1+ imm rd = rs1 imm rd rs1 | imm rd rs1 & imm rd imm[5:11]=0x00 imm[5:11]=0x00 imm[5:11]=0x20 rd rs1 >> imm[0:4] rs1 < < imm[0:4] rd = rs1 >> imm[0:4] (rs1 < imm)?1:0 rd rd rd rd rd rd M[rs1+imm][0:7] rd M[rs1+imm] [0:15] M[rs1+imm] [0:7] = rs2[0:7] M[rs1+imm] [0:15] = rs2[0:15] M[rs1+imm][0:31] = rs2[0:31] rs2) PC += imm if(rs1 != rs2) PC += imm if(rs1 rs2) PC += imm if(rs1 if(rs1 rs2) PC += imm if(rs1 rs2) PC += imm if(rs1 rs2) PC += imm PC+4; PC += imm PC+4; PC = rs1 + imm imm < < 12 PC+ (imm < < <12) Transfer control to OS Transfer control to debugger rd rd opcode R-type opcode I-type opcode S-type opcode B-type opcode U-type opcode J-type rd = rs1 | rs2 rd = rs1 & rs2 rd rd (rs1 < rs2)?1:0 (rs1 < rs2)?1:0 (rs1 < imm)?1:0 M[rs1+imm] [0:7] M[rs1+imm] [0:15] M[rs1+imm] [0:31] Note msb-extends zero-extends msb-extends zero-extends zero-extends zero-extends zero-extends zero-extends AutoFill can assist with filling out this form. 1. [0.8 pts] The RISC-V add immediate instruction (addi) is of I-format. Answer to the following questions. A. (0.4 pts) Obtain the hexadecimal representation of "addi x5, x6, 3", which stands for x5 x6 +3. Name: B. (0.4 pts) What is the range of numbers that can be represented in an immediate operand in addi? 2. [1.2 pts] Answer to the following questions. A. (0.4 pts) Write a RISC-V assembly code that performs a bitwise NOT operation on the value stored in x1 and stores the result in x2. B. (0.4 pts) Write a RISC-V assembly code that loads a constant value 0xDEADBA11 into register x20. C. (0.4 pts) Add one more RISC-V instruction to the previous answer to make the value of x20 become 0xDEADBEEF (You are not allowed to use addi). Student ID: 3. [1.0 pts] Suppose that we have the following values (RISC-V instructions) stored in instruction memory: Name: Inst. Address # (in decimal) 8000 8004 8008 8012 8016 1 2 3 4 5 Value (in hexadecimal) 0x00300413 0x00a00493 0x00840433 Oxfe944ee3 0x00241a13 e.g., for inst. #1, we have opcode: 0010011 I-type, A. (0.4 pts) Translate this machine code (from instruction #1 to #4) into a RISC-V assembly code. rd: 01000x8, func3: 000 addi, rs1: 00000 x0, imm: 000000000011 3, So, it is translated to "addi x8, x0, 3" Value (in binary) Student ID: 0000 0000 0011 0000 0000 0100 0001 0011 0000 0000 1010 0000 0000 0100 1001 0011 0000 0000 1000 0100 0000 0100 0011 0011 1111 1110 1001 0100 0100 1110 1110 0011 0000 0000 0010 0100 0001 1010 0001 0011 AutoFill Form 1 -G ( x AutoFill can assist with filling out this form. Name: Page 4 of 4 B. (0.2 pts) Among the above five instructions, how many of them are of B-type? C. (0.4 pts) What is the value stored in x20 after executing instruction #5? Student ID: AutoFill Form x
Expert Answer:

Related Book For 

Computer Architecture Fundamentals And Principles Of Computer Design
ISBN: 9781032097336
2nd Edition
Authors: Joseph D. Dumas II
Posted Date:
Students also viewed these algorithms questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
What is Traditional Distributed Computing? Explain it with the easy sentences.
-
Addison, Inc. makes a single product, an indoor fireplace. Data for last year is as follows: Selling price per fireplace Manufacturing costs: Variable per unit produced: Direct materials Direct labor...
-
An organization lost 125 employees last year, at a cost of $5,000.00 each. (Value is derived from cost to rehire and fill opening, as well as lost investment in the employee.) You suggest that a...
-
A quant jock from your firm used a linear demand specification to estimate the demand for its product and sent you a hard copy of the results. Unfortunately, some entries are missing because the...
-
Two blocks of the same inertia \((10 \mathrm{~kg})\) but different sizes are falling freely. Compare the force exerted by the Earth on the two blocks.
-
Kaiser Exporters buys used medical equipment and sells it to various foreign health care institutions. On June 15, the company committed to sell medical equipment to a foreign hospital for 800,000...
-
A hiker and his dog have discovered a skeleton hidden deep in the woods. The medical examiner has identified this skeleton as female. What characteristics of the skeleton would help the examiner make...
-
Required: 1. Prepare a vertical analysis of Sports Unlimited's 2021 and 2020 balance sheets. Express each amount as a percentage of to assets for that year. (Amounts to be deducted should be...
-
1. Please answer following questions: a. In the specific case of a one- sample t-test, what is the relationship between N and the degrees of freedom? b. What happens to the relationship between tand...
-
On 1 July 2021 the finance department of Wollongong Council entered into a contract with IBM Pty Ltd for the provision of services by Peter Hank, an expert computer programmer who is nominated in the...
-
if we replace the Creative Directors with data-driven processes, as was Peck's call, and given our understanding of consumer behavior, then what is it that data adds in this industry? At the same...
-
You are a value investor and you want to find stocks that are out of favor. From the list below, select 20 stocks that you believe offer the best value and growth potential over the next 10-20 years....
-
Explain professional value for fair compensation of a dual certified FNP who has received her DNP?
-
TechnoLink Berhad is currently an unlevered firm with a weighted average cost of capital (WACC) of 25 percent. The earnings before interest and taxes is forecasted to remain at RM80,000.00 annually....
-
On October 1, 2021, Adoll Company acquired 2,600 shares of its $1 par value stock for $38 per share and held these shares in treasury. On March 1, 2023, Adoll resold all the treasury shares for $34...
-
Why was IEEE 754-1985 a significant development in the history of computing, especially in the fields of scientific and engineering applications?
-
Fill in the blanks below with the most appropriate term or concept discussed in this chapter: The actual, physical realization of a computer system as opposed to the conceptual or block-level design....
-
Name and describe the three most common general types (from the standpoint of functionality) of machine instructions found in executable programs for most computer architectures.
-
If a politician running for office does not speak in general terms, does not try to move to the middle of the political spectrum, and does not take polls, is the median voter model therefore wrong?
-
Voters often criticize politicians running for office who do not speak in specific terms (i.e., who do not specify which spending programs will be cut, whose taxes will be raised, etc.). If voters...
-
Consider Jack who attends both his sons high school football games and a few professional football games too. At which games is Jack more likely to be well behaved? Why?

Study smarter with the SolutionInn App