The main memory of a computer is organized as 256 blocks, with a block size of...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
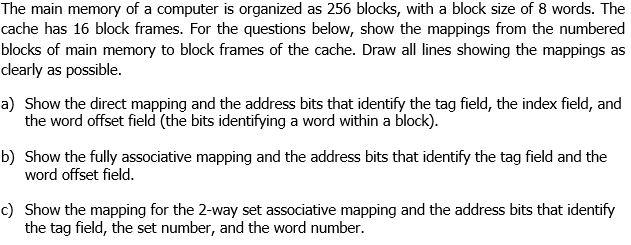
The main memory of a computer is organized as 256 blocks, with a block size of 8 words. The cache has 16 block frames. For the questions below, show the mappings from the numbered blocks of main memory to block frames of the cache. Draw all lines showing the mappings as clearly as possible. a) Show the direct mapping and the address bits that identify the tag field, the index field, and the word offset field (the bits identifying a word within a block). b) Show the fully associative mapping and the address bits that identify the tag field and the word offset field. c) Show the mapping for the 2-way set associative mapping and the address bits that identify the tag field, the set number, and the word number. The main memory of a computer is organized as 256 blocks, with a block size of 8 words. The cache has 16 block frames. For the questions below, show the mappings from the numbered blocks of main memory to block frames of the cache. Draw all lines showing the mappings as clearly as possible. a) Show the direct mapping and the address bits that identify the tag field, the index field, and the word offset field (the bits identifying a word within a block). b) Show the fully associative mapping and the address bits that identify the tag field and the word offset field. c) Show the mapping for the 2-way set associative mapping and the address bits that identify the tag field, the set number, and the word number.
Expert Answer:
Answer rating: 100% (QA)
Mapping in the context of computer architecture and memory hierarchy refers to the process of associating addresses from the main memory to locations in the cache The goal of mapping is to efficiently ... View the full answer

Related Book For 

Computer Organization and Design The Hardware Software Interface
ISBN: 978-0124077263
5th edition
Authors: David A. Patterson, John L. Hennessy
Posted Date:
Students also viewed these programming questions
-
Portray in words what transforms you would have to make to your execution to some degree (a) to accomplish this and remark on the benefits and detriments of this thought.You are approached to compose...
-
(a) For a fiber-reinforced composite, the efficiency of reinforcement ? is dependent on fiber length l according to where x represents the length of the fiber at each end that does not contribute to...
-
Suppose a company's average costs are given by (a) Express the average-cost formula as a single fraction. (b) Write the expression that gives the company's total costs. Use this equation, A company's...
-
A tubular heater with a black inner surface of uniform temperature T s = 1000 K irradiates a coaxial disk. (a) Determine the radiant power from the heater which is incident on the disk, q s?1 . What...
-
For each of the following, calculate the \(t\)-test for independent means. a. X 17.00, SX 1 X 2 = 1.17 - b. X 1 65.56, - sX 1 X 2 = 2.88 X 2 11.00, X-2=60.92, c. X 1 137.73, X-2=114.09, SX 1 X 2 =...
-
1. What other management development approaches could the firm use to improve managerial skills other than I-MBA programs? 2. What criteria should the firm use to determine if it will pay for...
-
What approaches do adaptive leaders employ to promote organizational agility and responsiveness, fostering a culture of experimentation and iterative improvement ?
-
Your firm must respond to a notice from the Internal Revenue Service announcing that the company owes a penalty because it underreported its income in the previous fiscal year. a. channel...
-
Use the vertical analysis of the company and a horizontal analysis of the company downloaded from Ascension Health . Discuss your findings by answering the following: Is Ascension Health growing? How...
-
Compute the present values of the following bond using three (3) different discount rates. 4 marks $1,000 Face Value Coupon rate 12% Coupons are paid once in a year. Compute the PV of the bond using:...
-
(d) Consider the RSA crypto scheme with the following configuration: = Alice's public key is (na, ea) = (33, 7), her private key is da = 3. Bob's public key is (no, eb) (65,7), his private key is d...
-
Consider the reference patterns and targets given below. We want to use these data to train a linear associator network. P1 P = = [4]." = [26] } 41 P2 {P = [2]-12= [26]} {P = [2] = [-26]} P3 13 i....
-
Using the schema of the tables, write relational algebra expressions for the following queries. 1 List the name and rating of the products that do not use Windows system. 2 List the user IDs and...
-
If A is the unit circle in R2, find H5(A). 1.5
-
Use the T account for Cash below to record the portion of each of the following transactions, if any that affect cash. How do these transactions affect the companys liquidity? Jan. 2 Provided...
-
If the current value of the PC is 0x00000600, can you use a single branch instruction to get to the PC address as shown in Exercise 2.39? Exercise 2.39 Write the MIPS assembly code that creates the...
-
Given the following logic diagram for an accumulator, write down the Verilog module implementation of it. Assume a positive edgetriggered register and asynchronous Rst. In Adder 16 16 Out Load Clk...
-
What is the function implemented by the following Verilog modules: module FUNC1 (10, I1, S, out); input I0, I1; input S; output out; out = S? Il: I0; endmodule module FUNC2 (out,ctl, clk,reset);...
-
Action Quest Games adjusts its accounts annually. The following information is available for the year ended December 31, 2025. 1. Purchased a 1-year insurance policy on June 1 for $1,800 cash. 2....
-
Why is carbon such a special atom?
-
With each pass of a comet about the Sun, the comets mass (a) remains virtually unchanged. (b) actually increases. (c) is appreciably reduced.

Study smarter with the SolutionInn App