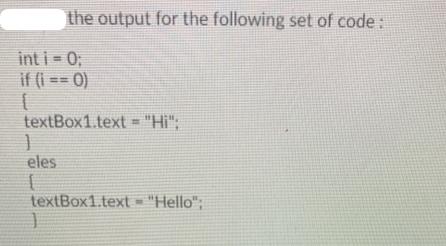
the output for the following set of code: int i=0; if (i == 0) textBox1.text =...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
the output for the following set of code: int i=0; if (i == 0) textBox1.text = "Hi"; ] eles textBox1.text = "Hello"; the output for the following set of code: int i=0; if (i == 0) textBox1.text = "Hi"; ] eles textBox1.text = "Hello";
Expert Answer:
Answer rating: 100% (QA)
Answer It seems like theres a typo in your code Instead of eles it should be ... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
An employer has asked you to develop a game in a Java program that needs to select a number at random between 1 to 10. Then, the user will be prompted to enter a number between 1 to 10 and, if it...
-
: (i) What data structures are maintained by the page manager. (ii) What happens when a machine performs a read operation to a page. (iii) What happens when a machine performs a write operation to a...
-
llustrate different ways of connecting these components together to span a range of performance requirements. [10 marks] For each of the performance categories that you identify state today's typical...
-
Hatch plc has two classes of share capital outstanding: 8%, 20 par preference and 5 par ordinary. At December 31, 2021, the following accounts were included in equity. Share CapitalPreference,...
-
After careful review of your maintenance log, you also realized that you will need to replace a fence post molding machine that sells for $40,000.00. You estimate that you will need to purchase a new...
-
In FIGURE 6-42 we see two blocks connected by a string and tied to a wall. The mass of the lower block is 1.0 kg; the mass of the upper block is 2.0 kg. Given that the angle of the incline is...
-
On February 16, 2005, Joseph and Margaret Buset borrowed $192,000 from Fremont Investment & Loan (the Originator). The loan was secured by a mortgage on a residential condominium. The mortgage named...
-
Boston Celtics Limited Partnership II and Subsidiaries presented these consolidated statements of income for 1998, 1997, and 1996. Required a. Comment on Amortization of NBA Franchise and Other...
-
Consider the Bertrand duopoly discussed in class. Assume each firm has constant marginal cost c = 10 and zero fixed cost. Each firm chooses a price Pi 0. The market demand is given by Q = 130 P,...
-
What is the primary purpose of using Market Ratios such as Price-to-Earnings (P/E) Ratio in financial strategic analysis?
-
How did Cristiano Schena and his team at Caterpillar Brazil use employee engagement and motivation to turn around a struggling business unit? What role did this approach play in sustaining the...
-
GDP and standard of living. What does Gross Domestic Product tell? If GDP increases, what does it mean for the economy? If GDP is higher, does it necessarily mean that living standard of average...
-
Apply relevant behavioural economics theories and concepts to a specific practical problem that an organisation of ownchoice (either in the private or public sector) is facing. Show how these...
-
Identify a firm of your choice, it could be your own company or the one where you work, you do not have to write the name of the company. To make a better case analysis you must first write the most...
-
} The following program contains errors. Find as many as possible and make the correction. #include using namespace std; Class Moon Class Moon Private; double earthWeight; double moonWeight; Public;...
-
It is desired to charge 48 V battery with 10 Amps from 230 Volt rms 50 Hz network by a controlled rectifier . Determine the inductor value to be the least (min. L). Accept the internal resistance of...
-
The maximum pressure that can be developed for a certain fluid power cylinder is 15.0 MPa. Compute the required diameter for the piston if the cylinder must exert a force of 30 kN.
-
Write a procedure that computes the SHA-1 hash of a block of data. The procedure should have two parameters: a pointer to the input buffer and a pointer to a 20-byte output buffer. To see the exact...
-
Consider the network of Fig. 5-12(a). Distance vector routing is used, and the following vectors have just come in to router C: from B: (5, 0, 8, 12, 6, 2); from D: (16, 12, 6, 0, 9, 10); and from E:...
-
The ping program allows you to send a test packet to a given location and see how long it takes to get there and back. Try using ping to see how long it takes to get from your location to several...
-
Which of the following is not an inherent part of Statement on Auditing Standards, No. 99/113? 1. Greater scrutiny of the chief executive and chief financial officers personal financial condition 2....
-
Which of the following statements best describes corporate governance with respect to fraud? 1. Auditors are primarily responsible for the detection of fraud, the Board of Directors for the...
-
Which of the following is not a reason that the prevention and detection of fraud resulting from management override and collusion presents a significant challenge for the antifraud community? 1....

Study smarter with the SolutionInn App


