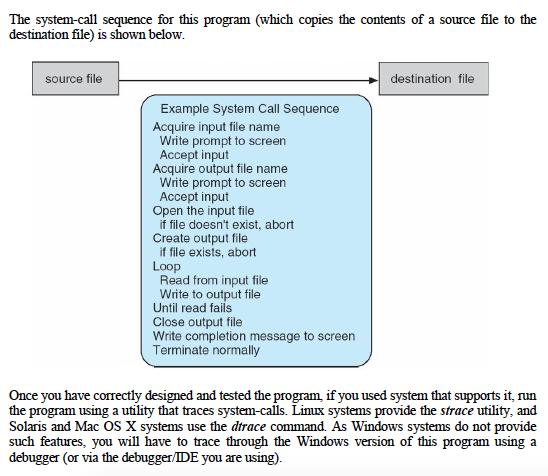
The system-call sequence for this program (which copies the contents of a source file to the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
The system-call sequence for this program (which copies the contents of a source file to the destination file) is shown below. source file Example System Call Sequence Acquire input file name Write prompt to screen Accept input Acquire output file name Write prompt to screen Accept input Open the input file if file doesn't exist, abort Create output file if file exists, abort Loop Read from input file Write to output file Until read fails Close output file Write completion message to screen Terminate normally destination file Once you have correctly designed and tested the program, if you used system that supports it, run the program using a utility that traces system-calls. Linux systems provide the strace utility, and Solaris and Mac OS X systems use the dtrace command. As Windows systems do not provide such features, you will have to trace through the Windows version of this program using a debugger (or via the debugger/IDE you are using). The system-call sequence for this program (which copies the contents of a source file to the destination file) is shown below. source file Example System Call Sequence Acquire input file name Write prompt to screen Accept input Acquire output file name Write prompt to screen Accept input Open the input file if file doesn't exist, abort Create output file if file exists, abort Loop Read from input file Write to output file Until read fails Close output file Write completion message to screen Terminate normally destination file Once you have correctly designed and tested the program, if you used system that supports it, run the program using a utility that traces system-calls. Linux systems provide the strace utility, and Solaris and Mac OS X systems use the dtrace command. As Windows systems do not provide such features, you will have to trace through the Windows version of this program using a debugger (or via the debugger/IDE you are using).
Expert Answer:
Answer rating: 100% (QA)
include include include include include include defi... View the full answer

Related Book For 

Accounting Information Systems
ISBN: 9780132871938
11th Edition
Authors: George H. Bodnar, William S. Hopwood
Posted Date:
Students also viewed these operating system questions
-
\Build the ItemToPurchase class with the following specifications: Attributes:- item_name (string) item_price (float) item_quantity (int) Constructor Initializes item's name, price and quantity...
-
You are required to write a Python program that will manage character (heroes and villain) information. Character (hero and villain) information will be stored in a text file that will be read in...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Suri recently took a job in the marketing department for All Access Cable Company. After just a few days on the job. After just a few days on the job, Suri learned that the company has many layers of...
-
For each function in below Problems find any horizontal and vertical asymptotes, and use information from the first derivative to sketch the graph. 1. f(x) = 2x+2 / x-3 2. f(x) = 5x - 15 / x+2 3. y =...
-
Early in the year Debra Deal and several friends organized a corporation called Markup, Inc. The corporation was authorized to issue 100,000 shares of $100 par value, 5 percent cumulative preferred...
-
a. Design a compressed air energy storage system for a wind turbine you analyzed previously. Assume that a cavity in an abandoned salt mine is available adjacent to the wind turbine. Use all the...
-
Hasselback Company acquired a plant asset at the beginning of Year 1. The asset has an estimated service life of 5 years. An employee has prepared depreciation schedules for this asset using three...
-
Each student shall include a "reflection" piece in the portfolio. This reflection shall be a minimum of seven fifty words. The student will reflect on their experiences and courses at DTCC in the...
-
Ayayai Hotels Ltd. (AHL) is a small boutique hotel that provides 44 suites that can be rented by the day, week, or month. Food service is available through room service as well. In addition, there...
-
Plant Company is contemplating the purchase of a new place of equipment for $59,000. Plant Is In the 20% Income tax bracket. Predicted annual after-tax cash Inflows from thisr Investment are $16,000,...
-
What type of investment risk is associated with an S&P index fund? A. Diversifiable risk. B. Nondiversifiable risk. C. Nonmarket risk. D. Nonsystematic risk.
-
Mr. and Mrs. Wilson want to establish QTPs for Dennis and their three other grandchildren, all of whom are under age11. What is the maximum amount they can contribute in one year without making a...
-
Alternative investments are obtained through the use of A. Commodities. B. Exchange traded funds. C. Hedge funds. D. Mutual funds.
-
Which of the following are examples of income in respect of a decedent? I. Dividends declared but not received at the time of death. II. Medical expenses accrued prior to the time of death. III....
-
Madge and Brent Jones want to establish an education account for their minor child, Tahoe. The Joneses do not want to incur the expense of establishing a trust and they want to gift parcels of real...
-
A.Determine the voltage and power across 40 ohm resistor using Mesh and Nodal Analysis B. Determine the equivalent resistance as seen from the source terminals 40 60 V 20 30 70 www 50 (2 www 10
-
A number of years ago the United Food and Commercial Workers Union organized 800 workers of the 1035 employees at one of the Wilson Brothers food operations in Toronto, Ontario. The employees include...
-
The process of creating customer master records in SAP ERP is complex but results in information that is useful in the sales business process. However, the process of creating customer master records...
-
Consider the online cash receipts application discussed in this chapter. Modify the cash application procedure to allow the operator to process customer remittances with multiple payments or no...
-
1. Which of the following is the most effective control procedure to detect vouchers that were prepared for the payment of goods that were not received? a. Count goods on receipt in the storeroom. b....
-
In Exercise 15.3 what sample sizes would be needed to raise power to 0.70, 0.80, and 0.90? Exercise 15.3 In Section 12.3 we looked at a set of data on whether children who are stressed from their...
-
Following on from Exercise 15.3, suppose that my colleagues were tired of having children tell them what they think we want to hear and gave them a heart-to-heart talk on the necessity of accurate...
-
Diagram the situation described in Exercise 15.6 along the lines of Figure 15.2. E xercise 15.6 Following on from Exercise 15.3, suppose that my colleagues were tired of having children tell them...

Study smarter with the SolutionInn App