The UNIX set-user-id bit allows users to run an executable program with the permissions of the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
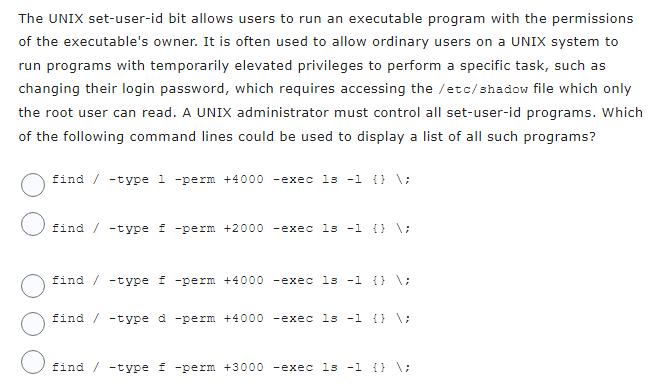
The UNIX set-user-id bit allows users to run an executable program with the permissions of the executable's owner. It is often used to allow ordinary users on a UNIX system to run programs with temporarily elevated privileges to perform a specific task, such as changing their login password, which requires accessing the /etc/shadow file which only the root user can read. A UNIX administrator must control all set-user-id programs. Which of the following command lines could be used to display a list of all such programs? find / -type 1 -perm +4000 -exec 13 -1 {} \; find / -type f -perm +2000 -exec 13 -1 {} \; find / -type f -perm +4000 -exec 13 -1 {} \; find / -type d -perm +4000 -exec ls -1 {} \; find / -type f -perm +3000 -exec ls -1 {} \; The UNIX set-user-id bit allows users to run an executable program with the permissions of the executable's owner. It is often used to allow ordinary users on a UNIX system to run programs with temporarily elevated privileges to perform a specific task, such as changing their login password, which requires accessing the /etc/shadow file which only the root user can read. A UNIX administrator must control all set-user-id programs. Which of the following command lines could be used to display a list of all such programs? find / -type 1 -perm +4000 -exec 13 -1 {} \; find / -type f -perm +2000 -exec 13 -1 {} \; find / -type f -perm +4000 -exec 13 -1 {} \; find / -type d -perm +4000 -exec ls -1 {} \; find / -type f -perm +3000 -exec ls -1 {} \;
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below The correct command line to display a l... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these operating system questions
-
Erica, Deana & Tara had average capital balances of $350,000, $380,000 and $400,000 respectively during the current fiscal year. The partnership agreement provides for an allowance of 4% on the...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
A woman flies from Phoenix to Denver (a distance of 800 mi) at a rate 40 mph faster than on the return trip. If the total time of the trip is 9 hrs, what was her rate going to Denver, and what was...
-
Actual financial statements (rather than the simplified financial statements presented in the chapter) for Shoppers Drug Mart are presented in Appendix A at the end of this book. Instructions (a)...
-
Discuss the advantages and disadvantages of using a questionnaire or checklist in evaluating an internal control system.
-
Robin Ritz mamifactures and sells homemade wine, and he wants to develop a standard cost per gallon. The following are required for production of a 50-gallon batch. 3,000 ounces of grape concentrate...
-
Dove Corporation manufactures and sells climate controlled wine cabinets. Its most popular model sells for $3,000 and comes with a basic 90-day warranty/ For am Extra $150 this warranty is extended...
-
The prepaid insurance account had a balance of $5,900 at the beginning of the year. The account was debited for $6,500 for premiums on policies purchased during the year. Journalize the adjusting...
-
Preparing the Olney Company's Employee Payroll Register for the pay period ending January 8th, 20--. In previous chapters, gross wages were computed for each employee and using this data, FICA...
-
1- Construct a theoretical framework of Finance research example which contains Independent variables (atleast 3), Dependent variable (1), Moderating variable and intervening variable. 2- Explain how...
-
Provide a comprehensive discussion on the impact of technological progress on economic growth in the short, medium, and long run. How does technological progress interact with other economic...
-
Explain Sraffa's critique of the Marshallian industry supply curve based on diminishing returns under the general case. for example when it says that the industry accounts for a very small share of...
-
How do advanced structural health monitoring techniques, such as distributed fiber optic sensing and wireless sensor networks, enhance the safety and performance assessment of bridges and other...
-
Samantha sells homemade cupcakes on the sidewalk in front of her house as a sole proprietor. She does all the work, makes all the sales, and keeps all the profits. If she instead makes and sells...
-
ann=h and dy 1 and u= 34+53
-
What do you find interesting about the ritz carlton hotel organizational culture? What impact do you think the culture has on the company's employees? Do you think the company does a good job of...
-
Integration is a vital concept when applied in one?s life. Integrating your life means making ideal choices. Perfect choices on the other go in line with quality decisions. Quality decisions lead to...
-
Explain that many organizations create or support the development of intellectual property (IP) as part of their business operations. Intellectual property is defined as the ownership of ideas and...
-
I. Define what the Center for Internet Security (CIS) is and their purpose for assisting with cyberattacks and methods to control them through the Multi-State Information Sharing and Analysis Center...
-
Distinguish phishing as an attempt to gain personal or financial information from an individual, usually by posing as a legitimate entity. Emphasize that a variant is spear phishing, a label that...
-
Assume that United Technologies Corporation is evaluating a proposal to change the companys manual design system to a computer-aided design (CAD) system. The proposed system is expected to save...
-
In 2008 the City of Chicago agreed to lease 35,000 parking meters to a Morgan Stanley-led partnership Morgan Stanley for a one-time sum of \($1.15\) billion. The lease has been criticized as an...
-
Pure White Automatic Laundry must either have a complete overhaul of its current dry-cleaning system or purchase a new one. Its cost of capital is 18 percent. Pure Whites accountant has developed the...

Study smarter with the SolutionInn App


