]: ]: ]: This one definitely falls in the category of pointless exercises. You're going to...
Fantastic news! We've Found the answer you've been seeking!
Question:
![]: ]: ]: This one definitely falls in the category of](https://dsd5zvtm8ll6.cloudfront.net/si.experts.images/questions/2023/09/64f6d3b87e3cc_1693897655085.jpg)
![[ ]: Exercise 6 sections to reference: lists So, now that you're an expert in sorting lists of food, let's](https://dsd5zvtm8ll6.cloudfront.net/si.experts.images/questions/2023/09/64f6d3cd0d555_1693897677262.jpg)
Transcribed Image Text:
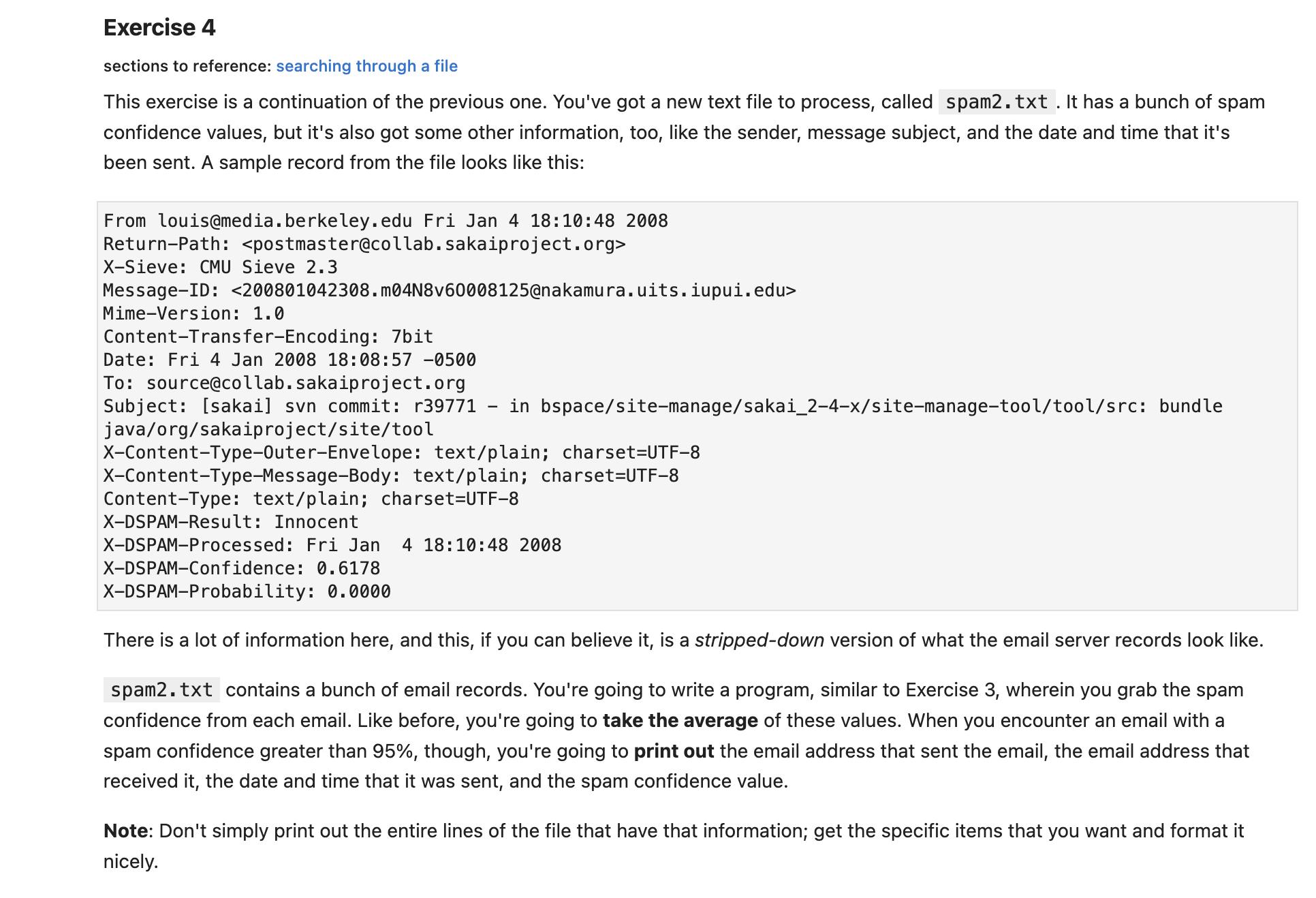
]: ]: ]: This one definitely falls in the category of "pointless exercises". You're going to make a program that prompts for a filename. If the file exists, quit the program! Don't print anything out, don't do anything with the file, don't do anything. Just quit. If the file doesn't exist, complain, and prompt the user for a filename again. Do this until the user gives you a valid filename or pours water on their computer in frustration. (Just kidding. Don't pour water on your computer.) You're going to want to put the filename prompt inside a loop, so you can ask the user for a filename as many times as you want. But what kind of loop? And how will you get out of the loop once you've got a valid file? Exercise 4 sections to reference: searching through a file This exercise is a continuation of the previous one. You've got a new text file to process, called spam2.txt. It has a bunch of spam confidence values, but it's also got some other information, too, like the sender, message subject, and the date and time that it's been sent. A sample record from the file looks like this: From louis@media.berkeley.edu Fri Jan 4 18:10:48 2008 Return-Path: <postmaster@collab.sakaiproject.org> X-Sieve: CMU Sieve 2.3 Message-ID: Mime-Version: 1.0 <200801042308.m04N8v60008125@nakamura.uits.iupui.edu> Content-Transfer-Encoding: 7bit Date: Fri 4 Jan 2008 18:08:57 -0500 To: source@collab.sakaiproject.org Subject: [sakai] svn commit: r39771 in bspace/site-manage/sakai_2-4-x/site-manage-tool/tool/src: bundle java/org/sakaiproject/site/tool X-Content-Type-Outer-Envelope: X-Content-Type-Message-Body: text/plain; charset=UTF-8 text/plain; charset=UTF-8 Content-Type: text/plain; charset=UTF-8 X-DSPAM-Result: Innocent X-DSPAM-Processed: Fri Jan 4 18:10:48 2008 X-DSPAM-Confidence: 0.6178 X-DSPAM-Probability: 0.0000 There is a lot of information here, and this, if you can believe it, is a stripped-down version of what the email server records look like. spam2.txt contains a bunch of email records. You're going to write a program, similar to Exercise 3, wherein you grab the spam confidence from each email. Like before, you're going to take the average of these values. When you encounter an email with a spam confidence greater than 95%, though, you're going to print out the email address that sent the email, the email address that received it, the date and time that it was sent, and the spam confidence value. Note: Don't simply print out the entire lines of the file that have that information; get the specific items that you want and format it nicely. [ ]: Exercise 6 sections to reference: lists So, now that you're an expert in sorting lists of food, let's get a little bit more literary. richard3.txt contains the text of Richard's opening soliloquy from Shakespeare's play Richard III. You can watch a performance of it here, if you're interested. You're going to write a program that reads in the soliloquy from the file line by line. Then, using the split function, split each line into a list of words. Create a list to contain all of your words. Going word by word, check if the word is already in the list. If not, add it. Once you've gone through the whole file, sort the list of words in alphabetical order, and print it out. fh = open ("richard3.txt") 1st = list() for line in fh: words= line.split() for word in words: if word in 1st: continue 1st.append(word) print (sorted (lst)) Exercise 7 sections to reference: dictionaries and files In the previous exercise, you just discarded words that were duplicates, but what if you wanted to count them? You're going to read in richard3.txt again, but this time use a dictionary. Iterate through the lines in the file and, for each word, if this is its first occurence, add the word as a key to the dictionary and the number "1" as a value. If the word exists in the dictionary, add one to its value. Then, print out your word-frequency dictionary. ]: ]: ]: This one definitely falls in the category of "pointless exercises". You're going to make a program that prompts for a filename. If the file exists, quit the program! Don't print anything out, don't do anything with the file, don't do anything. Just quit. If the file doesn't exist, complain, and prompt the user for a filename again. Do this until the user gives you a valid filename or pours water on their computer in frustration. (Just kidding. Don't pour water on your computer.) You're going to want to put the filename prompt inside a loop, so you can ask the user for a filename as many times as you want. But what kind of loop? And how will you get out of the loop once you've got a valid file? Exercise 4 sections to reference: searching through a file This exercise is a continuation of the previous one. You've got a new text file to process, called spam2.txt. It has a bunch of spam confidence values, but it's also got some other information, too, like the sender, message subject, and the date and time that it's been sent. A sample record from the file looks like this: From louis@media.berkeley.edu Fri Jan 4 18:10:48 2008 Return-Path: <postmaster@collab.sakaiproject.org> X-Sieve: CMU Sieve 2.3 Message-ID: Mime-Version: 1.0 <200801042308.m04N8v60008125@nakamura.uits.iupui.edu> Content-Transfer-Encoding: 7bit Date: Fri 4 Jan 2008 18:08:57 -0500 To: source@collab.sakaiproject.org Subject: [sakai] svn commit: r39771 in bspace/site-manage/sakai_2-4-x/site-manage-tool/tool/src: bundle java/org/sakaiproject/site/tool X-Content-Type-Outer-Envelope: X-Content-Type-Message-Body: text/plain; charset=UTF-8 text/plain; charset=UTF-8 Content-Type: text/plain; charset=UTF-8 X-DSPAM-Result: Innocent X-DSPAM-Processed: Fri Jan 4 18:10:48 2008 X-DSPAM-Confidence: 0.6178 X-DSPAM-Probability: 0.0000 There is a lot of information here, and this, if you can believe it, is a stripped-down version of what the email server records look like. spam2.txt contains a bunch of email records. You're going to write a program, similar to Exercise 3, wherein you grab the spam confidence from each email. Like before, you're going to take the average of these values. When you encounter an email with a spam confidence greater than 95%, though, you're going to print out the email address that sent the email, the email address that received it, the date and time that it was sent, and the spam confidence value. Note: Don't simply print out the entire lines of the file that have that information; get the specific items that you want and format it nicely. [ ]: Exercise 6 sections to reference: lists So, now that you're an expert in sorting lists of food, let's get a little bit more literary. richard3.txt contains the text of Richard's opening soliloquy from Shakespeare's play Richard III. You can watch a performance of it here, if you're interested. You're going to write a program that reads in the soliloquy from the file line by line. Then, using the split function, split each line into a list of words. Create a list to contain all of your words. Going word by word, check if the word is already in the list. If not, add it. Once you've gone through the whole file, sort the list of words in alphabetical order, and print it out. fh = open ("richard3.txt") 1st = list() for line in fh: words= line.split() for word in words: if word in 1st: continue 1st.append(word) print (sorted (lst)) Exercise 7 sections to reference: dictionaries and files In the previous exercise, you just discarded words that were duplicates, but what if you wanted to count them? You're going to read in richard3.txt again, but this time use a dictionary. Iterate through the lines in the file and, for each word, if this is its first occurence, add the word as a key to the dictionary and the number "1" as a value. If the word exists in the dictionary, add one to its value. Then, print out your word-frequency dictionary.
Expert Answer:
Answer rating: 100% (QA)
Exercise 4 Prompting for a Filename Heres a Python program that prompts the user for a filename until they provide a valid one or decide to quit pytho... View the full answer

Related Book For 

A Concise Introduction to Logic
ISBN: 978-1305958098
13th edition
Authors: Patrick J. Hurley, Lori Watson
Posted Date:
Students also viewed these programming questions
-
Many groups have treasury policies that use hedging of net positions . solve They would look at their group-wide exposure in, e . solveg . solve foreign currency and then take forward contracts to...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Five Smithtown High School students are saving up to buy their first cars. They all have after-school jobs, and their weekly salaries are listed in the table. Emily ..........................$110 Sam...
-
On January 1, 2016, Leo paid $15,000 for 5 percent of the stock in BLS, an S corporation. In November, he loaned $8,000 to BLS in return for a promissory note. BLS generated a $600,000 operating loss...
-
Paper-and-pencil honesty tests are most frequently used to determine whether someone has committed a crime. (True/False)
-
List four stakeholder groups with an interest in the typical firm.
-
Abigail Trenkamp owns and operates the Trenkamp Collection Agency. Listed on the following page are the name, number of allowances claimed, marital status, information from time cards on hours worked...
-
Detailed explanation for answer (excel breakdown if possible). ABC, Inc.'s revenues have been $300,000 and total costs have been $150,000; both costs and revenues are expected to remain the same in...
-
a. To simplify the analysis, assume for now that there is virtually no turnaround time between flights so the next flight can begin as soon as the current flight ends. (If an immediate next flight is...
-
Use the following data: 1 2 3 4 5 6 7 8 9 10 11 12 1 13 14 x 430 440 520 500 400 480 420 520 600 500 540 480 520 420 P 0.48 0.88 0.69 0.82 0.17 0.64 0.85 0.47 0.62 0.72 0.51 0.37 0.45 0.23 (a) Find...
-
A publisher finds that the mean number of grammatical errors per page of a book is six. Find the probability that the number of grammatical errors found on any given page is (a) exactly four, (b) at...
-
Define monetary base. How does the monetary base differ from the money supply?
-
A river barge, whose cross section is approximately rectangular, carries a load of grain. The barge is \(28 \mathrm{ft}\) wide and \(90 \mathrm{ft}\) long. When unloaded, its draft (depth of...
-
Can the approaches discussed in this chapter be used in emerging economies? What adjustments, if any, would you recommend?
-
How many real positive values of \(r\) satisfy the following. (a) \(\frac{d R}{d r}(r, 0.05)=0\) (b) \(\frac{d R}{d r}(r, 0.4)=0\) (c) \(\frac{d R}{d r}(r, 0.8)=0\)
-
Suppose you are working with an Indian commercial Bank, which has sanctioned a portfolio loan of 100 accounts with an average sanction limit of Rs. 1,000,00/- to an NBFC. Based on history on an...
-
Derive Eq. (18.33) from Eq. (18.32).
-
Some ATM locations are places criminals lurk. All places criminals lurk are places to avoid at night. Therefore, some places to avoid at night are ATM locations. Use Venn diagrams to determine...
-
[X (R F)] [(X R) F ] Use truth tables to determine whether the following symbolized statements are tautologous, self-contradictory, or contingent.
-
Nothing that is brittle is ductile. Superconductors are all ceramics. Only ductile things can be pulled into wires. Ceramics are brittle. Superconductors cannot be pulled into wires. The following...
-
Toner Corporation computed the following taxable income and loss: 2020 taxable income, \(\$ 10,000\) and 2021 taxable loss, \(\$ 40,000\). At the end of 2021 , Toner made the following estimates:...
-
DNSE Inc. began operations in 2019. In its first year the company had a net operating loss of \(\$ 10,000\), which was carried forward and used to reduce income tax payable in 2020. In 2020, DNSE had...
-
The financial statements of Gibson Corporation for the first two years of operations reflected the following amounts. Assume a tax rate of \(25 \%\) for 2020 and 2021. Estimates of future earnings at...

Study smarter with the SolutionInn App


