This VM quest is based on the Dr. Who television series. This scenario works for the...
Fantastic news! We've Found the answer you've been seeking!
Question:

Transcribed Image Text:
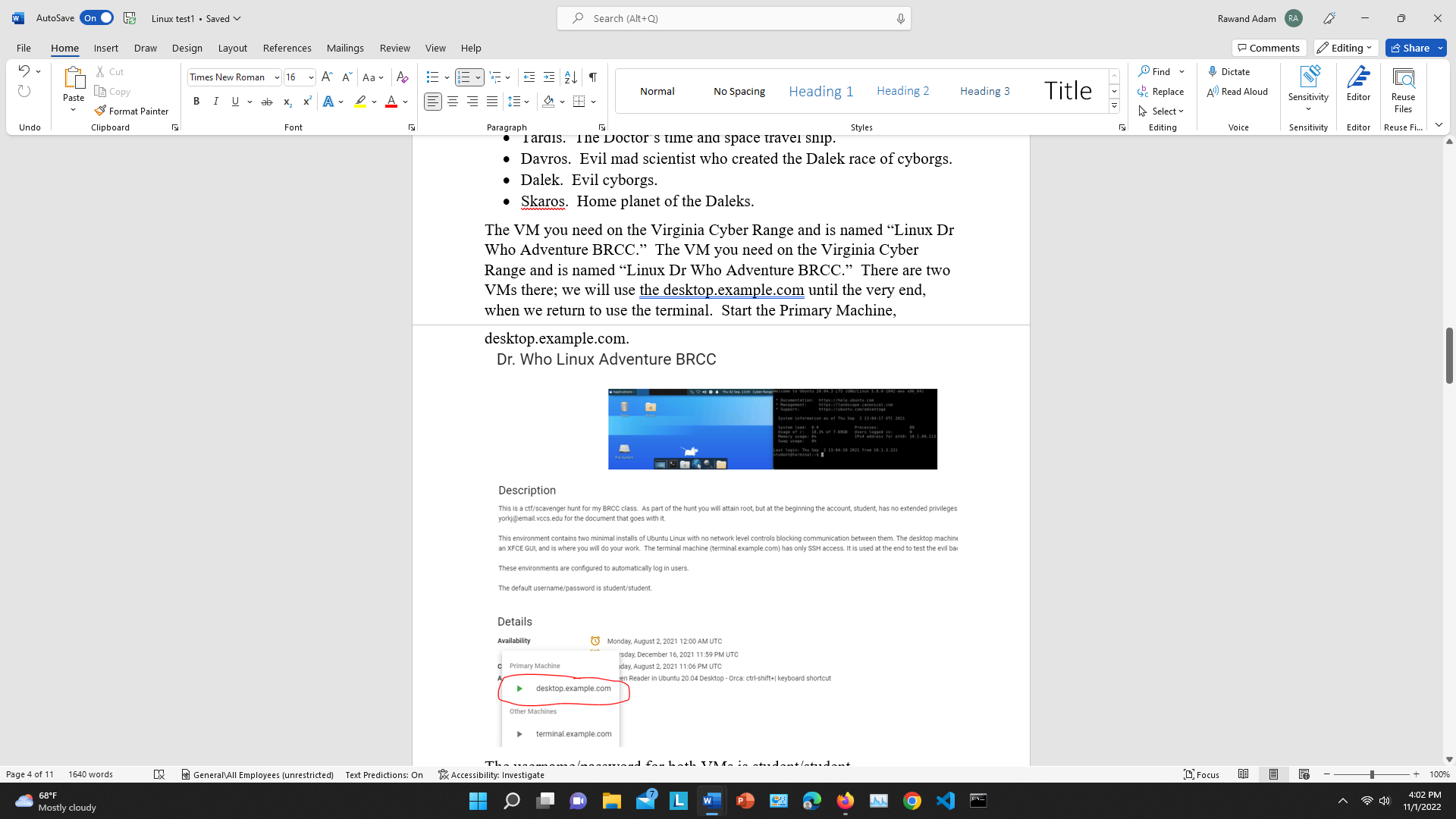
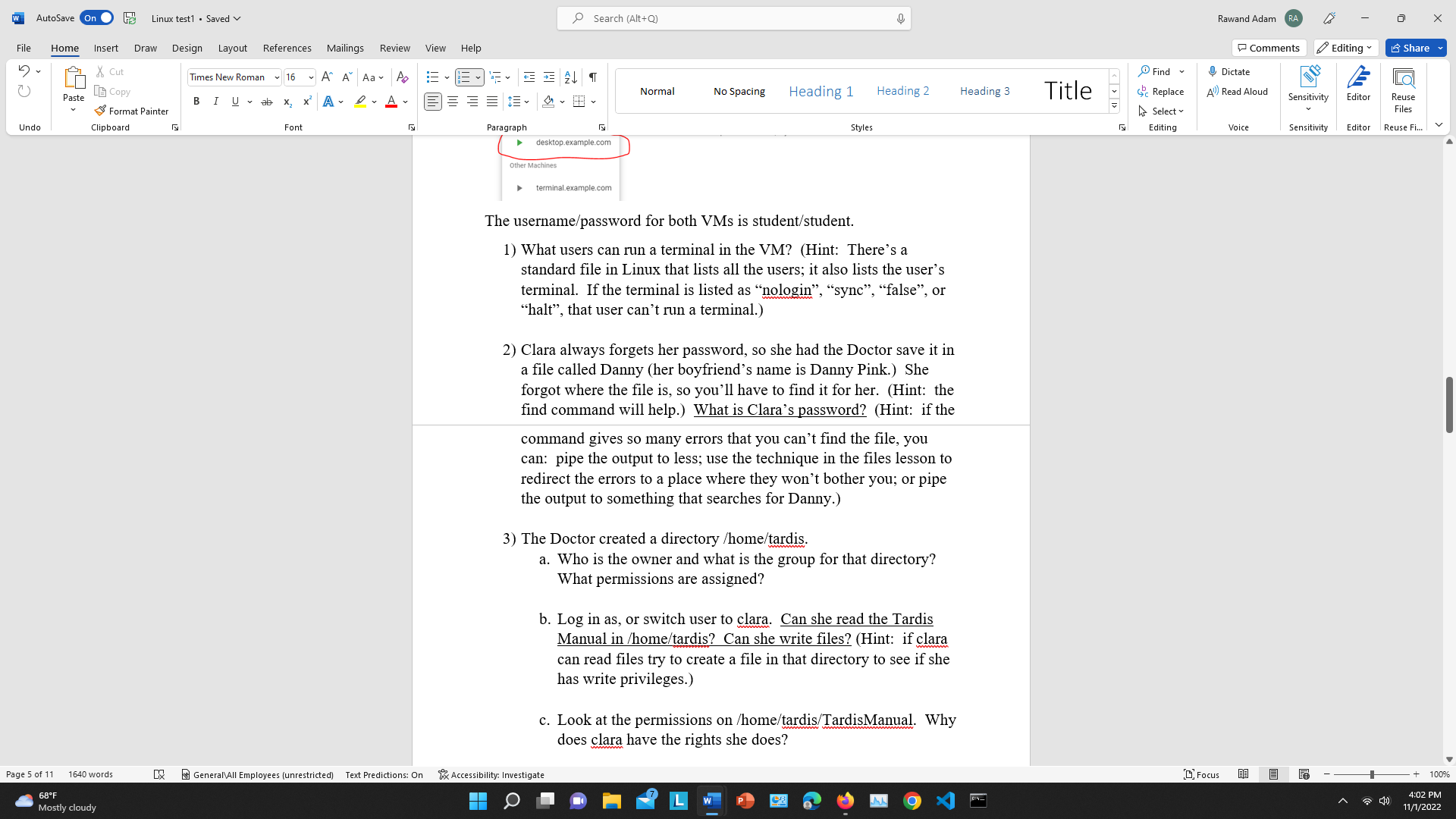
This VM quest is based on the Dr. Who television series. This scenario works for the 12th Doctor (Peter Capaldi). So that Whovians don't get an advantage, here is the cast of characters. All you need to know is who is good and who is evil. . Dr. Who, or the Doctor. The hero. Clara Oswald. The Doctor's traveling companion and co-hero. Tardis. The Doctor's time and space travel ship. Davros. Evil mad scientist who created the Dalek race of cyborgs. .Dalek. Evil cyborgs. Skaros. Home planet of the Daleks. The VM you need on the Virginia Cyber Range and is named "Linux Dr Who Adventure BRCC." The VM you need on the Virginia Cyber Range and is named "Linux Dr Who Adventure BRCC." There are two VMs there; we will use the desktop.example.com until the very end, when we return to use the terminal. Start the Primary Machine, desktop.example.com. Dr. Who Linux Adventure BRCC TONO Secumentation Manage 1:29,44,3 LTS (SMUILLAN 5.8-9-1942-bvs 485_34) tas://lasha.com Mtps://landscape.camnice.com Systen ernaaof The 340 2 13/04/17 TC 2921 feston d Processes Viers Segad DHE Press for 4: 16.1.30.11 Last Jagi: Thu Sep 2:33:44:10 2621 from 18.1.3.221 tel Description This is a ctf/scavenger hunt for my BRCC class. As part of the hunt you will attain root, but at the beginning the account, student, has no extended privileges yorkj@emaill.vccs.edu for the document that goes with it. This environment contains two minimal installs of Ubuntu Linux with no network level controls blocking communication between them. The desktop machine an XFCE GUI, and is where you will do your work. The terminal machine (terminal.example.com) has only SSH access. It is used at the end to test the evil bar These environments are configured to automatically log in users. H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 4 of 11 1640 words 68F Mostly cloudy 8 G References Mailings Review A^ A Aa P Times New Roman 16 B I U ab X Font x ADA 5 General All Employees (unrestricted) Text Predictions: On View Help 13-16 2 = = = =+ Paragraph Search (Alt+Q) T G Iarais. Ine Doctor's time and space travel snip. Davros. Evil mad scientist who created the Dalek race of cyborgs. .Dalek. Evil cyborgs. Skaros. Home planet of the Daleks. Details Availability desktop.example.com. Dr. Who Linux Adventure BRCC c Primary Machine Normal The VM you need on the Virginia Cyber Range and is named Linux Dr Who Adventure BRCC." The VM you need on the Virginia Cyber Range and is named "Linux Dr Who Adventure BRCC." There are two VMs there; we will use the desktop.example.com until the very end, when we return to use the terminal. Start the Primary Machine, Other Machines No Spacing desktop.example.com Accessibility: Investigate Heading 1 terminal.example.com Description This is a ctf/scavenger hunt for my BRCC class. As part of the hunt you will attain root, but at the beginning the account, student, has no extended privileges yorkj@email.vccs.edu for the document that goes with it. Monday, August 2, 2021 12:00 AM UTC Styles This environment contains two minimal installs of Ubuntu Linux with no network level controls blocking communication between them. The desktop machine an XFCE GUI, and is where you will do your work. The terminal machine (terminal.example.com) has only SSH access. It is used at the end to test the evil bar These environments are configured to automatically log in users. The default username/password is student/student. Heading 2 Mps://andscape.canonical.com Systen Information as of The Sep 2:13:04:17 UTC 2021 of 7,68 for th: 18.1.99.111 Last Topin: The Sep 2. 13:04/10 2021 from 10.1.3.221 rsday, December 16, 2021 11:59 PM UTC iday, August 2, 2021 11:06 PM UTC en Reader in Ubuntu 20.04 Desktop - Orca: ctrl-shift+| keyboard shortcut wond for both VM- in stradantlatsidant Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 5 of 11 1640 words 68F Mostly cloudy 8 G References Mailings Review Times New Roman B I U ab 16 X Font View Help A^ A Aa P 15-16 a= x ADA EAT Paragraph Search (Alt+Q) Other Machines desktop.example.com G terminal.example.com Normal No Spacing Heading 1 General All Employees (unrestricted) Text Predictions: On Accessibility: Investigate Styles Heading 2 The username/password for both VMs is student/student. 1) What users can run a terminal in the VM? (Hint: There's a standard file in Linux that lists all the users; it also lists the user's terminal. If the terminal is listed as "nologin", "sync", "false", or "halt", that user can't run a terminal.) 2) Clara always forgets her password, so she had the Doctor save it in a file called Danny (her boyfriend's name is Danny Pink.) She forgot where the file is, so you'll have to find it for her. (Hint: the find command will help.) What is Clara's password? (Hint: if the command gives so many errors that you can't find the file, you can: pipe the output to less; use the technique in the files lesson to redirect the errors to a place where they won't bother you; or pipe the output to something that searches for Danny.) 3) The Doctor created a directory /home/tardis. a. Who is the owner and what is the group for that directory? What permissions are assigned? b. Log in as, or switch user to clara. Can she read the Tardis Manual in /home/tardis? Can she write files? (Hint: if clara can read files try to create a file in that directory to see if she has write privileges.) c. Look at the permissions on /home/tardis/TardisManual. Why does clara have the rights she does? Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 6 of 11 1640 words 68F Mostly cloudy 8 G Times New Roman 16 U ab B I References X Mailings Review A^ A Aa P x ADA Font General All Employees (unrestricted) Text Predictions: On View Help 13-16 a- === Paragraph Search (Alt+Q) T Normal No Spacing Heading 1 Accessibility: Investigate Styles Heading 2 d. Using the clara user, read the Tardis manual. How do you make the Tardis take off? 4) The Doctor can't remember passwords either. He is in the habit of emailing his password to himself so he can find it later. He thinks it is clever to use the password as the From: address. Usually it looks like From: @tardis.com and To:doctor@tardis.com. There is a large SMTP log file in /var/log/smtp. It would take a long time to page through the entire file, but you should be able to find the password with one simple command. (Don't let it bother you that the SMTP log file is from a Windows server but is stored on an Ubuntu machine. Weird things happen when the Doctor is involved.) a. What is the Doctor's password? 5) Since the Doctor is the hero, he should have root access. Log in as doctor and see if he does. How does the Doctor access his privileges? (Hint: remember there are two ways, and both start with "su". Try both and see if they work.) 6) Now that you have root access using the Doctor's account, let's go back and look at the users again. Examine /etc/shadow, and determine which of the users you found in step 1) can actually log in. (Hint: they need a valid hash. An '!' in the position for the hash means the account is disabled, and an **' means no password has ever been set for that account. Valid hashes are usually long.) 7) Davros tried to create a service that runs when the machine changes run levels. He used the old SysV method for creating services. Can you find it? (Hint: Where are scripts for services Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout References Mailings Review X Cut Copy Format Painter Clipboard Page 7 of 11 1640 words 68F Mostly cloudy 8 G Times New Roman 16 U ab B I X Font A^ A Aa P x ADA General All Employees (unrestricted) Text Predictions: On View Help 13-16 a- Paragraph Search (Alt+Q) T R Accessibility: Investigate Normal No Spacing Heading 1 Styles Heading 2 7) Davros tried to create a service that runs when the machine changes run levels. He used the old SysV method for creating services. Can you find it? (Hint: Where are scripts for services put in SysV? Hint: Look for filenames that might be relevant to this scenario.) What is the full path to the file he made? What are the contents of the file, or, what happens when the student user executes the file? (The answer to this question is a strong hint for the next question.) 8) The Doctor says the root password should be the same as his password, but it's not. It appears Davros has changed it. Can you guess the root password? What is it? (Hint: see the answer for question 7 and look for something that is repeated.) 9) Davros was successful in installing a back door that is listening to the network. Use the techniques you learned in the lab on unnecessary services to find it. Note: the open TCP ports 3350 and 3389 are what VA Cyber Range uses to give you a GUI connection to your VM, and VACR uses SSH on TCP 22 as well. Don't mess with them. a. Is there a suspicious port open? b. What is the process ID (PID)? c. What file or command opened the suspicious port? 10) For fun, let's be Davros and use his back door. There is a second VM in this environment called terminal that we can use to connect to Davros' back door on the main VM. To access the second VM, go back to the VACR page for the Dr. Who Linux Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 8 of 11 1640 words 68F Mostly cloudy 8 G References Mailings Review A^ A Aa P Times New Roman 16 B I U ab X Font x ADA 5 General All Employees (unrestricted) Text Predictions: On View Help 15-16 a = = = =+ Paragraph Details Availability Search (Alt+Q) C Primary Machine A T Styles c. What file or command opened the suspicious port? 10) For fun, let's be Davros and use his back door. There is a second VM in this environment called terminal that we can use to connect to Davros' back door on the main VM. To access the second VM, go back to the VACR page for the Dr. Who Linux Adventure and start terminal.example.com. It will open a new tab in your browser with the new VM. Dr. Who Linux Adventure BRCC Other Machines Description This is a ctf/scavenger hunt for my BRCC class. As part of the hunt you will attain root, but at the beginning the account, student, has no extended privileges. Contact yorkj@email.vccs.edu for the document that goes with it Normal desktop.example.com No Spacing This environment contains two minimal installs of Ubuntu Linux with no network level controls blocking communication between them. The desktop machine (desktop.example.com) has an XFCE GUI, and is where you will do your work. The terminal machine (terminal.example.com) has only SSH access. It is used at the end to test the evil backdoor that Davros installed. These environments are configured to automatically log in users. The default username/password is student/student. Accessibility: Investigate Heading 1 terminal.example.com Heading 2 Monday, August 2, 2021 12:00 AM UTC rsday, December 16, 2021 11:59 PM UTC iday, August 2, 2021 11:06 PM UTC en Reader in Ubuntu 20.04 Desktop-Orca: ctrl-shift+ keyboard shortcut https://landscape.canonical.com https://ubuntu.com/advantage Heading 3 console.virginiacyberrange.net/range/#/client/Zjg1 NGUONjgtODNiNy00ZjM5LThjNjEtYWFjMDFIOTQxNDY2L2Y0MTMxZTk2LV Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.8.0-1042-aws x86_64) *Documentation: https://help.ubuntu.com * Management: * Support: Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 9 of 11 1640 words 68F Mostly cloudy 8 G References Times New Roman 16 B I U ab X Font Mailings Review A^ A Aa P x ADA General All Employees (unrestricted) Text Predictions: On View Help 15-16 22 E ALT = = = =+ Paragraph Search (Alt+Q) G Normal No Spacing Accessibility: Investigate Heading 1 Last login: Wed Sep 22 20:43:02 2021 from 10.1.1.188 student@terminal:-$|| Styles Heading 2 The image above shows the new, or audit VM. We want to use the terminal VM to connect to Davros' backdoor on the main VM. To do that we will use nc (netcat), but first we will need to know: 11) a. The IP address of the main VM. The command, ip address, may help. Hint: If you are choosing between addresses, it is not 127.0.0.1; that's the loopback address.) b. The port that Davros' back door listens on. (You should have found that in step 9.) Once you have the information, enter the command below on the audit VM. The audit VM is the one with the blue title bar where you connected with SSH. The output of its hostname command was audit.example.com. nc [ip address of main VM] [port that Davros' back door listens on] Here's an example, but with the wrong IP (10.0.0.1) and port (1234) nc 10.0.0.1 1234 Last login: Wed Sep 22 20:43:02 2021 from 10.1.1.188 student@terminal:~$ nc 10. If the command gives no output, don't panic! Davros' back Heading 3 Title N Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:03 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 10 of 11 1640 words 68F Mostly cloudy & G References Times New Roman B I U ab 16 X Mailings Review A^ A Aa P x ADA Font View Help 13-16 a- General All Employees (unrestricted) Text Predictions: On = = = =+ Paragraph Search (Alt+Q) Accessibility: Investigate T G Normal No Spacing Styles If the command gives no output, don't panic! Davros back door is a shell, not a terminal/console. It does not give you a prompt (ex. student@ip-10-1-169-80:~$). However, if you type a command, you should get a response. In the image below, I typed hostname, and the backdoor responded with ip-10-1-169-80. hostname student@terminal:~$ nc 10. desktop.example.com Heading 1 Heading 2 Try other commands for basic exploration, like pwd (show the current directory, or print working directory) whoami (show the user I'm logged in as) uname -a (show all the info about the Unix version) ls You can also mess around with changing directories, executing programs, or whatever you want. GUI programs and nano will not work, though. When you are finished, you can type exit or hit control-C to get your prompt back on the audit VM. The answer to this question is a screenshot of the audit VM terminal with the response to the hostname command from Davros' back door, just like the image above (without the whiteout, though :-) 12) (Extra Credit) If you kill the back-door process, you should find that it will restart within 5 minutes. Can you (and your friend Google) find something that would cause an application to restart every 5 minutes? Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Sensitivity Te Editing Share Editor Reuse Files Editor Reuse Fi.... 1 100% 4:03 PM 11/1/2022 This VM quest is based on the Dr. Who television series. This scenario works for the 12th Doctor (Peter Capaldi). So that Whovians don't get an advantage, here is the cast of characters. All you need to know is who is good and who is evil. . Dr. Who, or the Doctor. The hero. Clara Oswald. The Doctor's traveling companion and co-hero. Tardis. The Doctor's time and space travel ship. Davros. Evil mad scientist who created the Dalek race of cyborgs. .Dalek. Evil cyborgs. Skaros. Home planet of the Daleks. The VM you need on the Virginia Cyber Range and is named "Linux Dr Who Adventure BRCC." The VM you need on the Virginia Cyber Range and is named "Linux Dr Who Adventure BRCC." There are two VMs there; we will use the desktop.example.com until the very end, when we return to use the terminal. Start the Primary Machine, desktop.example.com. Dr. Who Linux Adventure BRCC TONO Secumentation Manage 1:29,44,3 LTS (SMUILLAN 5.8-9-1942-bvs 485_34) tas://lasha.com Mtps://landscape.camnice.com Systen ernaaof The 340 2 13/04/17 TC 2921 feston d Processes Viers Segad DHE Press for 4: 16.1.30.11 Last Jagi: Thu Sep 2:33:44:10 2621 from 18.1.3.221 tel Description This is a ctf/scavenger hunt for my BRCC class. As part of the hunt you will attain root, but at the beginning the account, student, has no extended privileges yorkj@emaill.vccs.edu for the document that goes with it. This environment contains two minimal installs of Ubuntu Linux with no network level controls blocking communication between them. The desktop machine an XFCE GUI, and is where you will do your work. The terminal machine (terminal.example.com) has only SSH access. It is used at the end to test the evil bar These environments are configured to automatically log in users. H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 4 of 11 1640 words 68F Mostly cloudy 8 G References Mailings Review A^ A Aa P Times New Roman 16 B I U ab X Font x ADA 5 General All Employees (unrestricted) Text Predictions: On View Help 13-16 2 = = = =+ Paragraph Search (Alt+Q) T G Iarais. Ine Doctor's time and space travel snip. Davros. Evil mad scientist who created the Dalek race of cyborgs. .Dalek. Evil cyborgs. Skaros. Home planet of the Daleks. Details Availability desktop.example.com. Dr. Who Linux Adventure BRCC c Primary Machine Normal The VM you need on the Virginia Cyber Range and is named Linux Dr Who Adventure BRCC." The VM you need on the Virginia Cyber Range and is named "Linux Dr Who Adventure BRCC." There are two VMs there; we will use the desktop.example.com until the very end, when we return to use the terminal. Start the Primary Machine, Other Machines No Spacing desktop.example.com Accessibility: Investigate Heading 1 terminal.example.com Description This is a ctf/scavenger hunt for my BRCC class. As part of the hunt you will attain root, but at the beginning the account, student, has no extended privileges yorkj@email.vccs.edu for the document that goes with it. Monday, August 2, 2021 12:00 AM UTC Styles This environment contains two minimal installs of Ubuntu Linux with no network level controls blocking communication between them. The desktop machine an XFCE GUI, and is where you will do your work. The terminal machine (terminal.example.com) has only SSH access. It is used at the end to test the evil bar These environments are configured to automatically log in users. The default username/password is student/student. Heading 2 Mps://andscape.canonical.com Systen Information as of The Sep 2:13:04:17 UTC 2021 of 7,68 for th: 18.1.99.111 Last Topin: The Sep 2. 13:04/10 2021 from 10.1.3.221 rsday, December 16, 2021 11:59 PM UTC iday, August 2, 2021 11:06 PM UTC en Reader in Ubuntu 20.04 Desktop - Orca: ctrl-shift+| keyboard shortcut wond for both VM- in stradantlatsidant Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 5 of 11 1640 words 68F Mostly cloudy 8 G References Mailings Review Times New Roman B I U ab 16 X Font View Help A^ A Aa P 15-16 a= x ADA EAT Paragraph Search (Alt+Q) Other Machines desktop.example.com G terminal.example.com Normal No Spacing Heading 1 General All Employees (unrestricted) Text Predictions: On Accessibility: Investigate Styles Heading 2 The username/password for both VMs is student/student. 1) What users can run a terminal in the VM? (Hint: There's a standard file in Linux that lists all the users; it also lists the user's terminal. If the terminal is listed as "nologin", "sync", "false", or "halt", that user can't run a terminal.) 2) Clara always forgets her password, so she had the Doctor save it in a file called Danny (her boyfriend's name is Danny Pink.) She forgot where the file is, so you'll have to find it for her. (Hint: the find command will help.) What is Clara's password? (Hint: if the command gives so many errors that you can't find the file, you can: pipe the output to less; use the technique in the files lesson to redirect the errors to a place where they won't bother you; or pipe the output to something that searches for Danny.) 3) The Doctor created a directory /home/tardis. a. Who is the owner and what is the group for that directory? What permissions are assigned? b. Log in as, or switch user to clara. Can she read the Tardis Manual in /home/tardis? Can she write files? (Hint: if clara can read files try to create a file in that directory to see if she has write privileges.) c. Look at the permissions on /home/tardis/TardisManual. Why does clara have the rights she does? Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 6 of 11 1640 words 68F Mostly cloudy 8 G Times New Roman 16 U ab B I References X Mailings Review A^ A Aa P x ADA Font General All Employees (unrestricted) Text Predictions: On View Help 13-16 a- === Paragraph Search (Alt+Q) T Normal No Spacing Heading 1 Accessibility: Investigate Styles Heading 2 d. Using the clara user, read the Tardis manual. How do you make the Tardis take off? 4) The Doctor can't remember passwords either. He is in the habit of emailing his password to himself so he can find it later. He thinks it is clever to use the password as the From: address. Usually it looks like From: @tardis.com and To:doctor@tardis.com. There is a large SMTP log file in /var/log/smtp. It would take a long time to page through the entire file, but you should be able to find the password with one simple command. (Don't let it bother you that the SMTP log file is from a Windows server but is stored on an Ubuntu machine. Weird things happen when the Doctor is involved.) a. What is the Doctor's password? 5) Since the Doctor is the hero, he should have root access. Log in as doctor and see if he does. How does the Doctor access his privileges? (Hint: remember there are two ways, and both start with "su". Try both and see if they work.) 6) Now that you have root access using the Doctor's account, let's go back and look at the users again. Examine /etc/shadow, and determine which of the users you found in step 1) can actually log in. (Hint: they need a valid hash. An '!' in the position for the hash means the account is disabled, and an **' means no password has ever been set for that account. Valid hashes are usually long.) 7) Davros tried to create a service that runs when the machine changes run levels. He used the old SysV method for creating services. Can you find it? (Hint: Where are scripts for services Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout References Mailings Review X Cut Copy Format Painter Clipboard Page 7 of 11 1640 words 68F Mostly cloudy 8 G Times New Roman 16 U ab B I X Font A^ A Aa P x ADA General All Employees (unrestricted) Text Predictions: On View Help 13-16 a- Paragraph Search (Alt+Q) T R Accessibility: Investigate Normal No Spacing Heading 1 Styles Heading 2 7) Davros tried to create a service that runs when the machine changes run levels. He used the old SysV method for creating services. Can you find it? (Hint: Where are scripts for services put in SysV? Hint: Look for filenames that might be relevant to this scenario.) What is the full path to the file he made? What are the contents of the file, or, what happens when the student user executes the file? (The answer to this question is a strong hint for the next question.) 8) The Doctor says the root password should be the same as his password, but it's not. It appears Davros has changed it. Can you guess the root password? What is it? (Hint: see the answer for question 7 and look for something that is repeated.) 9) Davros was successful in installing a back door that is listening to the network. Use the techniques you learned in the lab on unnecessary services to find it. Note: the open TCP ports 3350 and 3389 are what VA Cyber Range uses to give you a GUI connection to your VM, and VACR uses SSH on TCP 22 as well. Don't mess with them. a. Is there a suspicious port open? b. What is the process ID (PID)? c. What file or command opened the suspicious port? 10) For fun, let's be Davros and use his back door. There is a second VM in this environment called terminal that we can use to connect to Davros' back door on the main VM. To access the second VM, go back to the VACR page for the Dr. Who Linux Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 8 of 11 1640 words 68F Mostly cloudy 8 G References Mailings Review A^ A Aa P Times New Roman 16 B I U ab X Font x ADA 5 General All Employees (unrestricted) Text Predictions: On View Help 15-16 a = = = =+ Paragraph Details Availability Search (Alt+Q) C Primary Machine A T Styles c. What file or command opened the suspicious port? 10) For fun, let's be Davros and use his back door. There is a second VM in this environment called terminal that we can use to connect to Davros' back door on the main VM. To access the second VM, go back to the VACR page for the Dr. Who Linux Adventure and start terminal.example.com. It will open a new tab in your browser with the new VM. Dr. Who Linux Adventure BRCC Other Machines Description This is a ctf/scavenger hunt for my BRCC class. As part of the hunt you will attain root, but at the beginning the account, student, has no extended privileges. Contact yorkj@email.vccs.edu for the document that goes with it Normal desktop.example.com No Spacing This environment contains two minimal installs of Ubuntu Linux with no network level controls blocking communication between them. The desktop machine (desktop.example.com) has an XFCE GUI, and is where you will do your work. The terminal machine (terminal.example.com) has only SSH access. It is used at the end to test the evil backdoor that Davros installed. These environments are configured to automatically log in users. The default username/password is student/student. Accessibility: Investigate Heading 1 terminal.example.com Heading 2 Monday, August 2, 2021 12:00 AM UTC rsday, December 16, 2021 11:59 PM UTC iday, August 2, 2021 11:06 PM UTC en Reader in Ubuntu 20.04 Desktop-Orca: ctrl-shift+ keyboard shortcut https://landscape.canonical.com https://ubuntu.com/advantage Heading 3 console.virginiacyberrange.net/range/#/client/Zjg1 NGUONjgtODNiNy00ZjM5LThjNjEtYWFjMDFIOTQxNDY2L2Y0MTMxZTk2LV Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.8.0-1042-aws x86_64) *Documentation: https://help.ubuntu.com * Management: * Support: Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:02 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 9 of 11 1640 words 68F Mostly cloudy 8 G References Times New Roman 16 B I U ab X Font Mailings Review A^ A Aa P x ADA General All Employees (unrestricted) Text Predictions: On View Help 15-16 22 E ALT = = = =+ Paragraph Search (Alt+Q) G Normal No Spacing Accessibility: Investigate Heading 1 Last login: Wed Sep 22 20:43:02 2021 from 10.1.1.188 student@terminal:-$|| Styles Heading 2 The image above shows the new, or audit VM. We want to use the terminal VM to connect to Davros' backdoor on the main VM. To do that we will use nc (netcat), but first we will need to know: 11) a. The IP address of the main VM. The command, ip address, may help. Hint: If you are choosing between addresses, it is not 127.0.0.1; that's the loopback address.) b. The port that Davros' back door listens on. (You should have found that in step 9.) Once you have the information, enter the command below on the audit VM. The audit VM is the one with the blue title bar where you connected with SSH. The output of its hostname command was audit.example.com. nc [ip address of main VM] [port that Davros' back door listens on] Here's an example, but with the wrong IP (10.0.0.1) and port (1234) nc 10.0.0.1 1234 Last login: Wed Sep 22 20:43:02 2021 from 10.1.1.188 student@terminal:~$ nc 10. If the command gives no output, don't panic! Davros' back Heading 3 Title N Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Editing Editor Reuse Files Sensitivity Editor Reuse Fi.... Te Share 100% 4:03 PM 11/1/2022 H File 5 U AutoSave On t Linux test1. Saved Undo Home Paste Insert Draw Design Layout X Cut Copy Format Painter Clipboard Page 10 of 11 1640 words 68F Mostly cloudy & G References Times New Roman B I U ab 16 X Mailings Review A^ A Aa P x ADA Font View Help 13-16 a- General All Employees (unrestricted) Text Predictions: On = = = =+ Paragraph Search (Alt+Q) Accessibility: Investigate T G Normal No Spacing Styles If the command gives no output, don't panic! Davros back door is a shell, not a terminal/console. It does not give you a prompt (ex. student@ip-10-1-169-80:~$). However, if you type a command, you should get a response. In the image below, I typed hostname, and the backdoor responded with ip-10-1-169-80. hostname student@terminal:~$ nc 10. desktop.example.com Heading 1 Heading 2 Try other commands for basic exploration, like pwd (show the current directory, or print working directory) whoami (show the user I'm logged in as) uname -a (show all the info about the Unix version) ls You can also mess around with changing directories, executing programs, or whatever you want. GUI programs and nano will not work, though. When you are finished, you can type exit or hit control-C to get your prompt back on the audit VM. The answer to this question is a screenshot of the audit VM terminal with the response to the hostname command from Davros' back door, just like the image above (without the whiteout, though :-) 12) (Extra Credit) If you kill the back-door process, you should find that it will restart within 5 minutes. Can you (and your friend Google) find something that would cause an application to restart every 5 minutes? Heading 3 Title Find Replace Select Editing Rawand Adam Dictate A Read Aloud Focus Comments Voice Sensitivity Sensitivity Te Editing Share Editor Reuse Files Editor Reuse Fi.... 1 100% 4:03 PM 11/1/2022
Expert Answer:

Related Book For 

Quantitative Methods for Business
ISBN: 978-0324651751
11th Edition
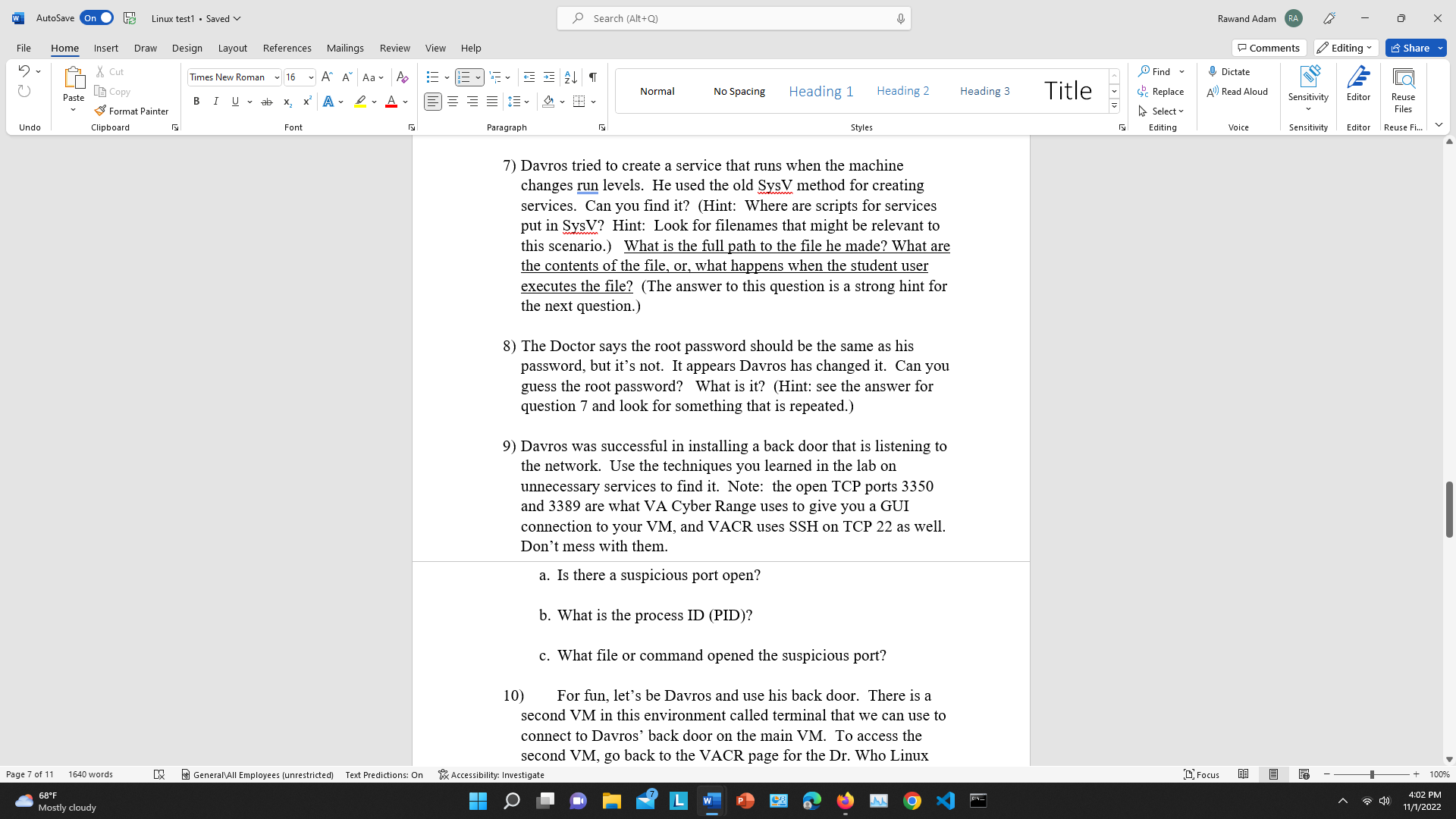
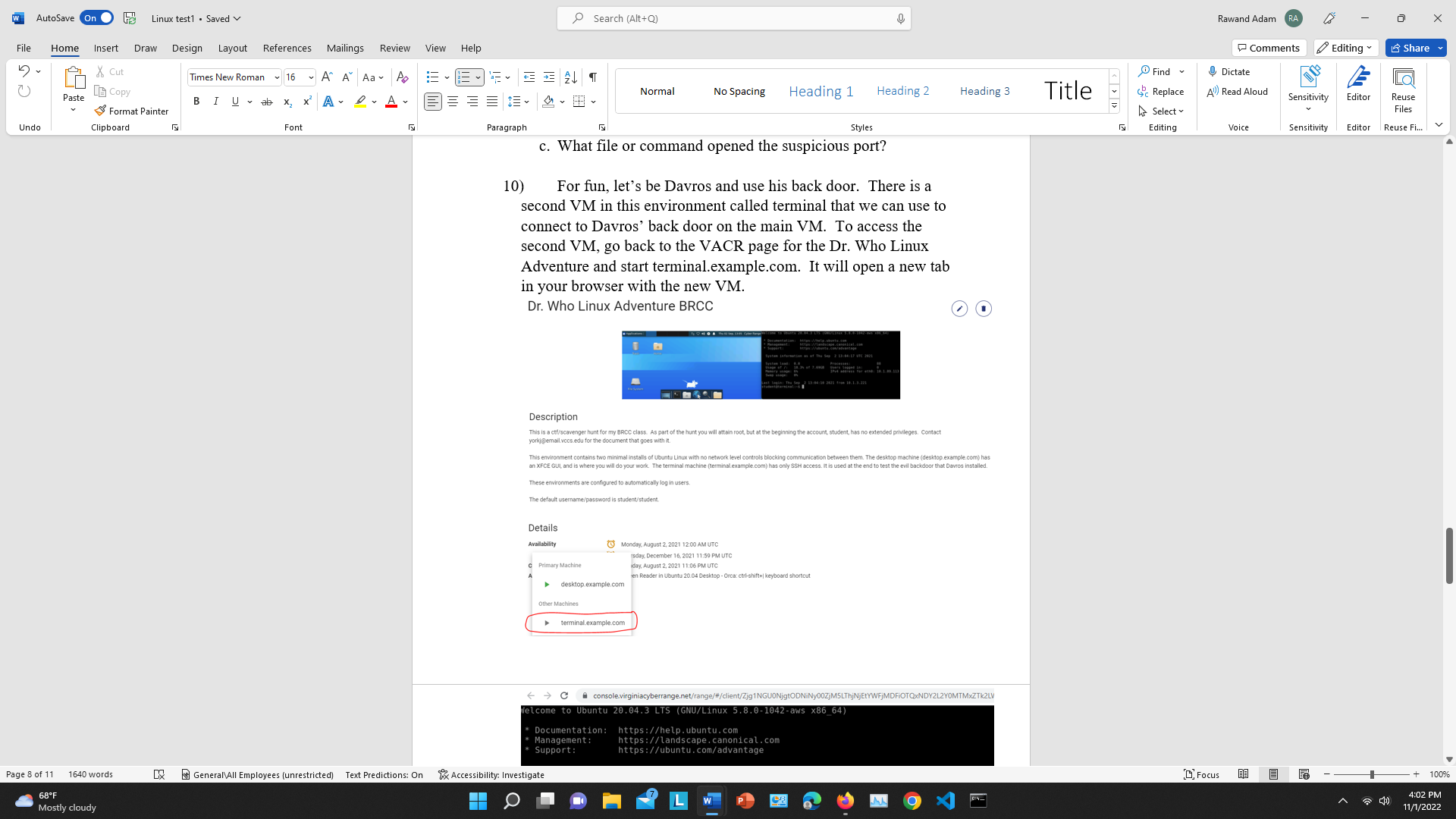
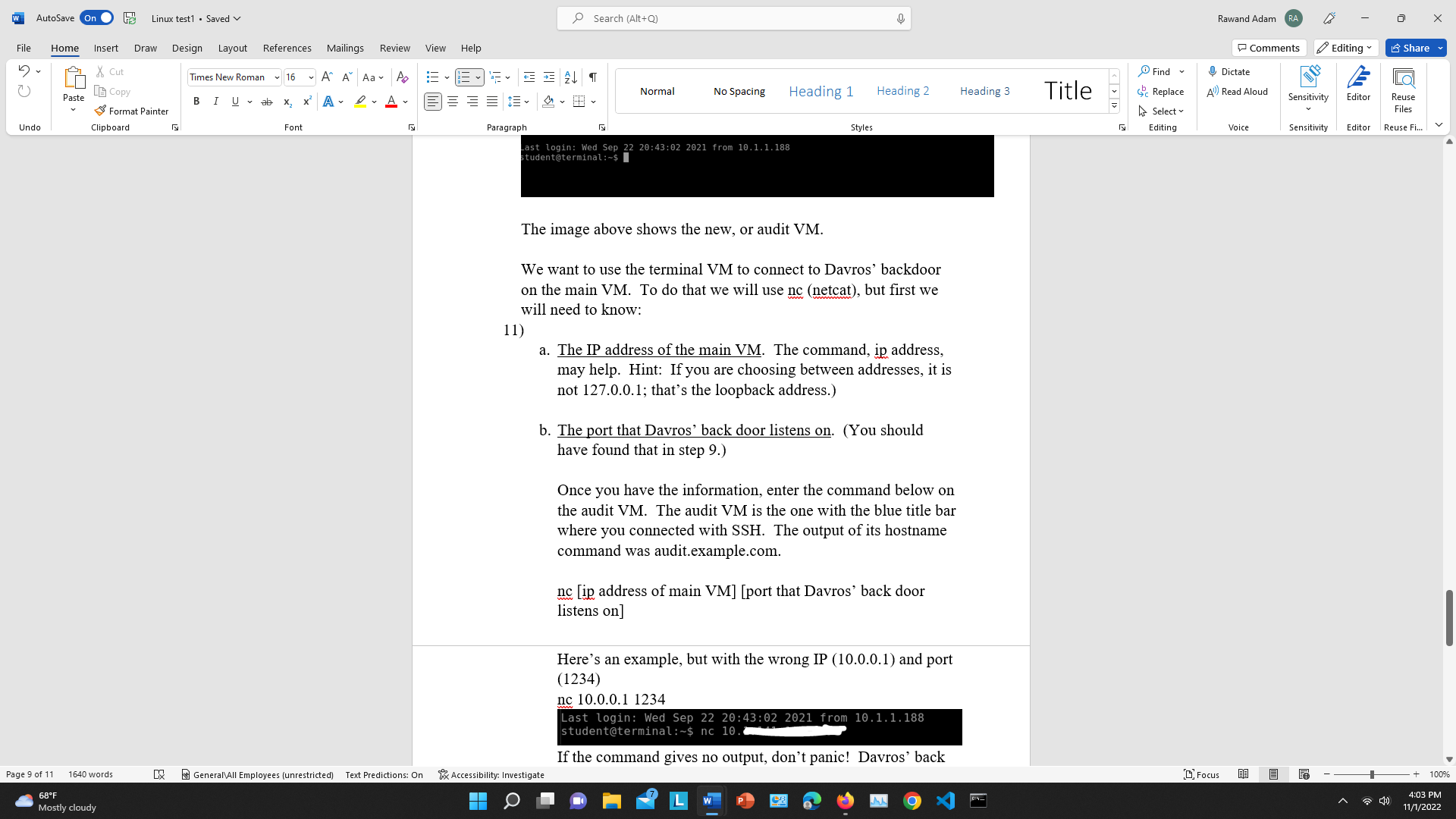
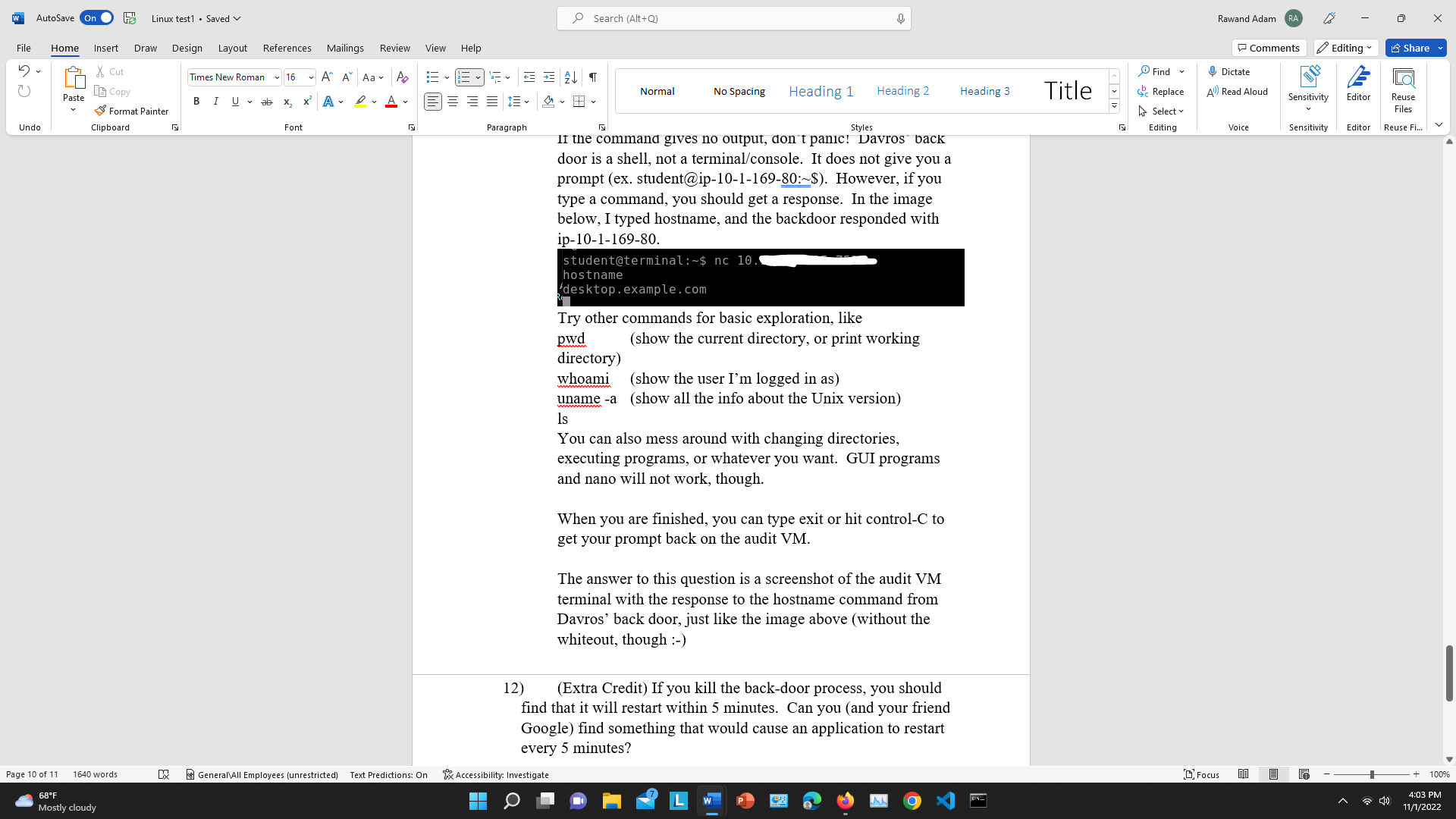
Authors: David Anderson, Dennis Sweeney, Thomas Williams, Jeffrey cam
Posted Date:
Students also viewed these computer network questions
-
Salem Screen Corporation manufactures and sells 50-inch television sets and uses standard costing. Actual data relating to January, February, and March 2020 are as follows: (Click to view the data.)...
-
Sabato io (incontrare) i miei amici. Noi (telefonare) a mia cugina e lei (decidere) di venire a casa mia. lo e mia cugina (giocare) a ping-pong e i miei amici (guardare) la televisione. Domenica...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Adam Hoover bought 72 shares of General Oil Co. stock at a par value of $85 per share. The stock paid annual dividends of 7 1/2%. How much did Adam receive in dividends this year? Commissions 0. Mrs....
-
In 2007, U.S. consumption of renewable energy was 6.8 quadrillion Btu (or 6.8 1015 Btu). Since the 1960s, consumption has been growing at a rate (in quadrillion Btu's per year) given by f'{t)=...
-
A new cure has been developed for a certain type of cement that results in a compressive strength of 5000 kilograms per square centimeter and a standard deviation of 120. To test the hypothesis that...
-
Jim Logan, owner of the Sports Exports Company, is concerned about the value of the British pound over time because his firm receives pounds as payment for footballs exported to the United Kingdom....
-
A sample of the 2011 MTF survey suggests that adolescents are divided in terms of their attitudes toward others trying marijuana at least once. In fact, 49.3% of the 1,202 respondents who answered...
-
4. A soccer field is bordered on thre length of the field and parking lo of the field is 30,000 m. How wide
-
The received signal in a digital base band system is either +A or -A, equally likely, for T-second contiguous intervals. However, the timing is off at the receiver so that the integration starts...
-
Fresh Water, Inc. sold an issue of 23-year $1,000 par value bonds to the public. The bonds have a 9.90 percent coupon rate and pay interest annually. The current market rate of interest on the Fresh...
-
What does VaR measure?
-
Does the valuation of an asset-backed security require the use of Monte Carlo simulation?
-
Explain how an accrual or Z bond works.
-
Explain the difference between diversified and undiversified VaR.
-
What is the relationship between the value of an MBS and the assumed volatility?
-
a. Use the appropriate formula to find the value of the annuity. b. Find the interest. Periodic Deposit $6000 at the end of each year Rate Time 4.5% compounded annually 20 years i Click the icon to...
-
Some people argue that the internal control requirements of the Sarbanes-Oxley Act (SOX) put U.S. companies at a competitive disadvantage to companies outside the United States. Discuss the...
-
The Statewide Auto Insurance Company developed the following probability distribution for automobile collision claims paid during the past year: Payment ($) Probability 0 ............ 0.83 500...
-
Micromedia offers computer training seminars on a variety of topics. In the seminars each student works at a personal computer, practicing the particular activity that the instructor is presenting....
-
A perishable dairy product is ordered daily at a particular supermarket. The product, which costs $1.19 per unit, sells for $1.65 per unit. If units are unsold at the end of the day, the supplier...
-
Leeds Architectural Consultants began operations on January 2. The following activity was recorded in the company's Work in Process account for the first month of operations: Leeds Architectural...
-
Estimated cost and operating data for three companies for the upcoming year follow: Predetermined overhead rates are computed using the following bases in the three companies: Required: 1. Compute...
-
Dillon Products manufactures various machined parts to customer specifications. The company uses a job-order costing system and applies overhead cost to jobs on the basis of machine-hours. At the...

Study smarter with the SolutionInn App