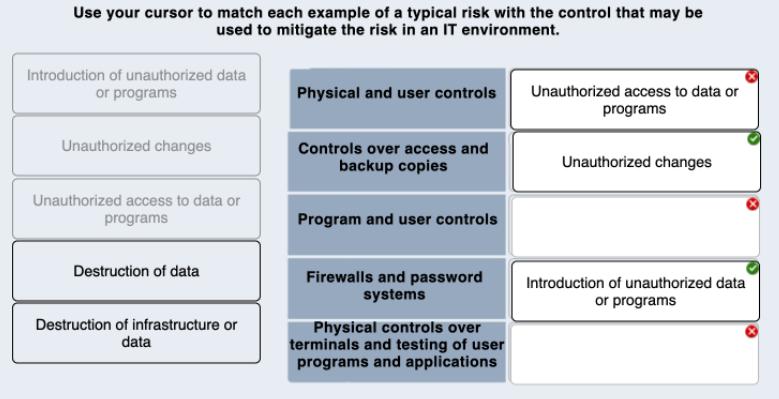
Use your cursor to match each example of a typical risk with the control that may...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Use your cursor to match each example of a typical risk with the control that may be used to mitigate the risk in an IT environment. Introduction of unauthorized data or programs Physical and user controls Unauthorized access to data or programs Unauthorized changes Controls over access and backup copies Unauthorized changes Unauthorized access to data or programs Program and user controls Destruction of data Firewalls and password systems Introduction of unauthorized data or programs Destruction of infrastructure or Physical controls over terminals and testing of user programs and applications data Use your cursor to match each example of a typical risk with the control that may be used to mitigate the risk in an IT environment. Introduction of unauthorized data or programs Physical and user controls Unauthorized access to data or programs Unauthorized changes Controls over access and backup copies Unauthorized changes Unauthorized access to data or programs Program and user controls Destruction of data Firewalls and password systems Introduction of unauthorized data or programs Destruction of infrastructure or Physical controls over terminals and testing of user programs and applications data
Expert Answer:
Answer rating: 100% (QA)
Physical and user controls Unauthorized access to data or programs Destruction of infrastruct... View the full answer

Related Book For 

Posted Date:
Students also viewed these accounting questions
-
While evaluating an Internal Control system in an IT environment an auditor should first understand the Control Activities in IT System. Explain with suitable examples the different Control...
-
List five financial ratios that may be used by your university to monitor operations.
-
List five financial ratios that may be used by your university to monitor operations.
-
A mail-order firm processes 5,300 checks per month. Of these, 60 percent are for $55 and 40 percent are for $80. The $55 checks are delayed two days on average; the $80 checks are delayed three days...
-
Below are account balances of Ducks Company at the end of September. Required: Prepare a trial balance by placing amounts in the appropriate debit or credit column and determining the balance of the...
-
Describe the usual order of current asset accounts in North American SFPs and balance sheets.
-
What are some potential roles for advisory councils? How can organizations use these groups effectively?
-
Describe the advantages and disadvantages of Wal-Marts aggressive union prevention efforts.
-
Georgette Scissors, a hair stylist, is about to open a hair salon in University City. The following data is taken from her business plan. Following the demand projection, one customer arrives every...
-
Embutidos Vallina SA has two direct-cost categories: direct materials and direct manufacturing labour. Its single indirect-cost category (manufacturing overhead) is allocated on the basis of...
-
Classify each cash flow below as operating, O, investing, I, or financing, F. Indicate the effect on cash by leaving the class letter plain if cash increases, or by placing a parenthesis around the...
-
Use the Internet to look for templates and other aids that would help in creating a marketing research proposal. Analyze and assess five of them. In your view, are these standardized formats suitable...
-
What is a linguistic variable? Give 10 examples of linguistic variables that you might use to describe a building.
-
What is the law of the excluded middle? Argue against the need for this law.
-
What is case-based reasoning? From which attributes of human intelligence do you think it is derived? Describe the last time you used case-based reasoning in your normal life.
-
Can semantic networks be used to represent anything that can be represented using temporal logic? Explain your answer.
-
Capstone Co. has $10 million shares outstanding trading at $50 per share. Capstone Co. is thinking of buying BigAL, which has 5 million shares outstanding, at a price of $25 per share. Capstone will...
-
The following processes constitute the air-standard Diesel cycle: 12: isentropic compression,23: constant-volume energy addition (T and P increase),34: constant-pressure energy addition (v...
-
Identify a long-term objective and two supporting annual objectives for a familiar organization.
-
Drucker says the most important time to seriously reexamine the firms vision/mission is when the firm is very successful. Why is this?
-
Would the angle or degrees of the vector in a SPACE Matrix be important in generating alternative strategies? Explain.
-
A job requires ten stages of work. The completion times for each are in the table below. Also listed in the table is the information of which stages cannot begin until other stages are complete,...
-
A large computer program is to be tested and debugged in modules, some of which require other modules to be completely tested before testing on them can proceed. The table below shows the...
-
Finish the proof of Theorem 2 by showing assertion 2: If \((u, v)\) is an omitted edge and \(S(u, v)=0\), then the spanning tree created by substituting \((u, v)\) for the edge \(\left(u_{0}, v...

Study smarter with the SolutionInn App