We have a team that can troubleshoot from afar, but the members are located 25 miles west
Question:
- We have a team that can troubleshoot from afar, but the members are located 25 miles west of this location. We have one of the tech support personnel deployed on site, but there are just too many issues for one person. The support team that is 25 miles west is centrally located to support multiple operational outfits. That team has a virtual private network (VPN) and secure access to our internal servers.
Main Question:
- At times, support team members need to determine which of our hosts are functioning. We use both Microsoft Windows and Linux operating systems, but we don't know what tool will help determine host functionality from afar.**
------------------------------------------------------------------------------------------------------------------------------------------------------------
SITREP - Report
Troubleshooting and Tool Report
Network Problem Selected:
------What goes here: Restate the problem & identified and explain why it is a problem.
Troubleshooting Steps:
------What goes here: List the steps in the Network+ troubleshooting methodology.
Tool and Description: ------What goes here: Name and briefly overview the tool that could solve this problem.
Tool Operational Use Case:
------What goes here: Describe how the tool can be used to solve similar problems in the future.
Tool Functionality:
------What goes here: Provide a detailed overview of the tool's functionality and options.
----------------------------------------------------------------------------------------------------------------------------------------------------------
Sample of a completed report.
TroubleshootingandToolRecommendation:SITREP Sample Report
Problem:
Eachofthenetworked15serversand400hostsaregeneratinglogs.Someoftheselogs are likely due to security issues. We only have 10 network security workers, and they don'thavethetimetoreview eachlogthatisgeneratedacrossthenetwork.Thisisa problembecausethelogscanidentifysecurityissues,hostevents,networkoptimization challenges,anderrors. Weneedanautomatedmethodto collect,centrallystore,and analyzethelogs,onlygeneratinganalertwhenhumaninterventionisneeded.
TroubleshootingSteps:
[Listthenetworkingtroubleshootingmethodology]
ToolandDescription:
Tosolvetheproblemidentified,itisproposedthat[Logstash]beimplementedwithinthe network.Logstash(afictionaltool)isafreeandopenserver-sidedataprocessing pipelinethatingestsdatafromvaryingsources,transformsit,anddisplaytheresults.
This tool allows for the collection of logs from virtually any source to include hosts, network devices, andservers. Mostlogs are inthe format oftheir creator andtherefore arenotstandardizedacrossa networkofsystems. Logstashnormalizesthelogsby converting them into key fields and elements that are most important to network securityandoptimization.ThisallowsuserstoprogramalertsontheLogstashserverand automatically be alerted toonly the most important log alerts. Logstash provides the ability to save time and human capital resources while ensuring network security and optimization capability.
ToolOperationalUseCase:
Logstash is being employed in our network to solve the log analysis problem identified above. Once implemented and properly configured, we expect Logstash to allow us to complywithinternalsecuritypoliciesandoutsideregulationsandaudits,understandand respondtodatabreachersandothersecurityincidents,troubleshootsystems,computer, and network devices, understand user behaviors, and conduct forensics in the event of aninvestigation. ThedeploymentofLogstashwill also saveusvaluabletimeand resources given we only have 10 personnel. The log alerts will enable network support personnel to respond only to the most crucial alerts, while ensuring nothing of critical importance is not known.
Tool Functionality:
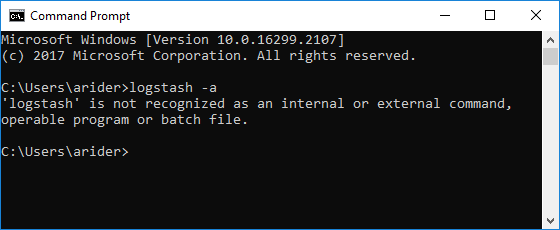
OnceinstalledontheserverandLinuxoperatingsystem,thecommandfunctionality includes multiple options:
- Logstashstart(thiscommandstartstheLogstashservice)
- Logstash-f(thiscommandidentifiesthelogfilelocation)
- Logstash-in(thiscommandingeststhelogfiles)
- Logstash-c(thiscommandsetsthenumberoffilestoingestbeforestopping)
- Logstash-cs(thiscommandsetstheingesttocontinuous)
- Logstash-a(thiscommandsetstheparameterstoanalyzeandalert)

International Marketing And Export Management
ISBN: 9781292016924
8th Edition
Authors: Gerald Albaum , Alexander Josiassen , Edwin Duerr