We want to design a trojan activation circuit. Trojans are HW modules inserted into chips during...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
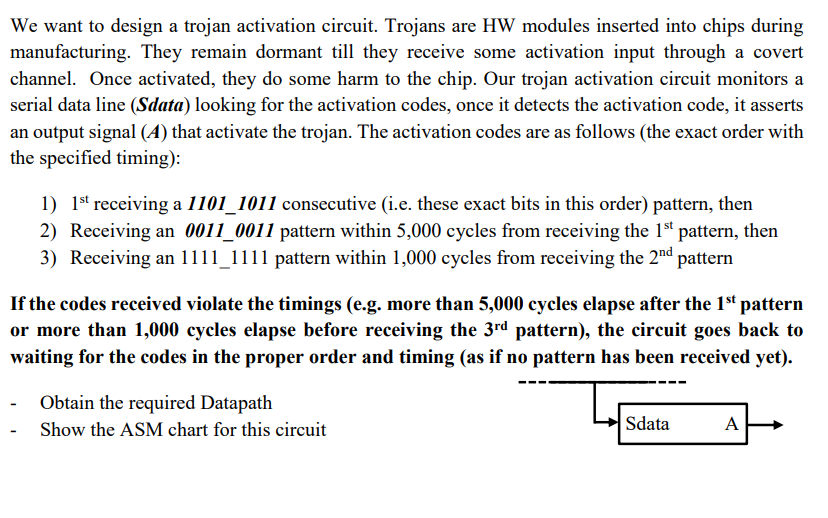
We want to design a trojan activation circuit. Trojans are HW modules inserted into chips during manufacturing. They remain dormant till they receive some activation input through a covert channel. Once activated, they do some harm to the chip. Our trojan activation circuit monitors a serial data line (Sdata) looking for the activation codes, once it detects the activation code, it asserts an output signal (4) that activate the trojan. The activation codes are as follows (the exact order with the specified timing): 1) 1st receiving a 1101_1011 consecutive (i.e. these exact bits in this order) pattern, then 2) Receiving an 0011_0011 pattern within 5,000 cycles from receiving the 1st pattern, then 3) Receiving an 1111_1111 pattern within 1,000 cycles from receiving the 2nd pattern If the codes received violate the timings (e.g. more than 5,000 cycles elapse after the 1st pattern or more than 1,000 cycles elapse before receiving the 3rd pattern), the circuit goes back to waiting for the codes in the proper order and timing (as if no pattern has been received yet). Obtain the required Datapath Show the ASM chart for this circuit Sdata A We want to design a trojan activation circuit. Trojans are HW modules inserted into chips during manufacturing. They remain dormant till they receive some activation input through a covert channel. Once activated, they do some harm to the chip. Our trojan activation circuit monitors a serial data line (Sdata) looking for the activation codes, once it detects the activation code, it asserts an output signal (4) that activate the trojan. The activation codes are as follows (the exact order with the specified timing): 1) 1st receiving a 1101_1011 consecutive (i.e. these exact bits in this order) pattern, then 2) Receiving an 0011_0011 pattern within 5,000 cycles from receiving the 1st pattern, then 3) Receiving an 1111_1111 pattern within 1,000 cycles from receiving the 2nd pattern If the codes received violate the timings (e.g. more than 5,000 cycles elapse after the 1st pattern or more than 1,000 cycles elapse before receiving the 3rd pattern), the circuit goes back to waiting for the codes in the proper order and timing (as if no pattern has been received yet). Obtain the required Datapath Show the ASM chart for this circuit Sdata A
Expert Answer:

Related Book For 

Financial Reporting And Analysis
ISBN: 9781260247848
8th Edition
Authors: Lawrence Revsine, Daniel Collins, Bruce Johnson, Fred Mittelstaedt, Leonard Soffer
Posted Date:
Students also viewed these programming questions
-
Approximately 35%of stowe-arts holdings take advantage of the discount and pay on the 10 th day. The remaining 65% take an average of 35 days to pay off their accounts .what is stowe-arts holdings...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
We want to design a causal discrete-time LTI system with the property that if the input is x(n) = (1/2)nu(n) (1/2) n 1 u(n 1) then the output is y(n) = (1/3)nu(n) (a) Determine the impulse...
-
Like Death Valley, the Dead Sea is a place where you can walk on dry land below sea level, and an apparently unmotivated hole in the ground along a strike-slip fault. How do you think it formed?
-
Find the following for a q-curve with parameters = 4 and = 11. a. The q-value having area 0.05 to its right b. q0.01
-
Consider the RLC circuit in Problem 11. a. Write the governing equation in terms of the electric charge \(q\). b. Assuming initial conditions are \(q(0)=0, \dot{q}(0)=1\), plot \(q\) and \(i\) versus...
-
Use the recursion relation (6.22) to evaluate \(\int_{-1}^{1} x P_{n}(x) P_{m}(x) d x, n \leq\) \(m\). Data from 6.22 (n+1)Pn+1(x) = (2n+1)xPn(x) - nPn-1(x), n = 1,2,....
-
(Computation of Basic and Diluted EPS) The information below pertains to Barkley Company for 2010. Net income for the year.................................................................$1,200,000...
-
Please answer the following question. Thank you very much for your assistance and enjoy your weekend.. A U.S. company's foreign subsidiary had the following amounts in Euros in 2011: Cost of goods...
-
John and Nina Hartwick, married 17 years, have a 13-year-old daughter. Eight years ago, they purchased a home on which they owe about $240,000. They also owe $6,000 on a two-year-old automobile. All...
-
Find the z-score for which the area under the standard normal curve to its right is 0.70. Round to two decimal places.
-
Ultra-Cosmetics Corporation has an average production process time of 40 days. Finished goods are kept on hand for an average of 15 days before they are sold. Accounts receivables are outstanding an...
-
Conlon Chemicals manufactures paint thinner. Information on the work in process follows: Beginning inventory, 40,900 partially complete gallons. Transferred out, 206,000 gallons. Ending inventory...
-
Discuss the Issues, concerns and problems regarding the downfall of the brand Forever 21.
-
Thompson Trailers (TT) manufactures utility trailers for small landscaping companies to haul their equipment to residential sites. Demand for the trailers is fairly even throughout the year, as snow...
-
Please give and define three principles when producing a new product. Please give an example of each.
-
Gerrand Ltd's accounts receivable balances for years ended 30 June 2022 and 30 June 2023 were $150,000 and $250,000, respectively. The number of days in receivables was 146 days. What were the credit...
-
What is the difference between the straight-line method of depreciation and the written down value method? Which method is more appropriate for reporting earnings?
-
Target adopted the new leasing standard for the year ended February 2, 2019, using the modified retrospective approach outlined in ASC Topic 842. All questions relate to the year ended February 2,...
-
1. Lyft has identified the drivers, not the riders, as its customers. a. What arguments support the companys assessment? b. What arguments suggest Lyfts customer is actually the rider? 2. What is/are...
-
The management of Banciu Corporation provides you with comparative balance sheets at December 31, 20X1, and December 31, 20X0, appearing below. Supplemental Information: a. The following table...
-
Which of the following, is not an element of an assurance engagement? (a) A three-party relationship involving a practitioner, a responsible party, and intended users (b) An oral or written assurance...
-
Which of the following characteristics exhibit Suitable criteria under the assurance engagement? (a) Relevance; (b) Completeness; (c) Reliability; (d) Neutrality (e) Understandability (f) All of the...
-
An auditor can accept an assurance engagement only where the practitioners preliminary knowledge of the engagement circumstances indicates that: (a) Relevant ethical requirements, such as...

Study smarter with the SolutionInn App