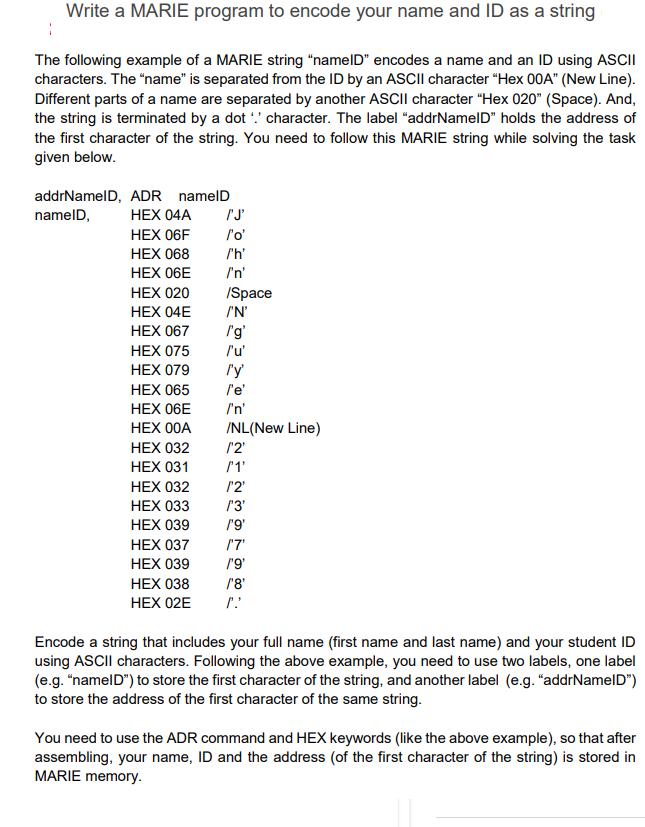
Write a MARIE program to encode your name and ID as a string The following example...
Fantastic news! We've Found the answer you've been seeking!
Question:
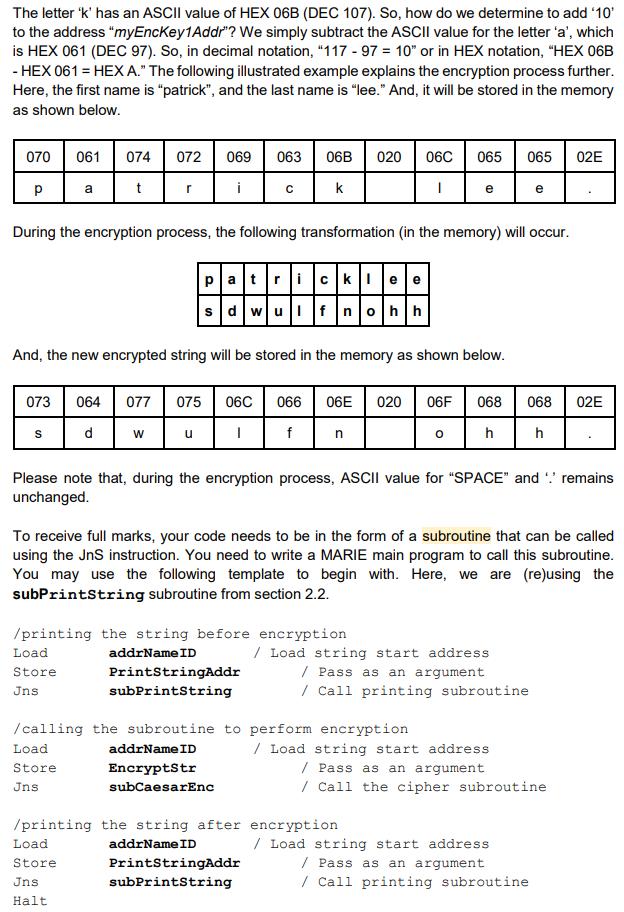
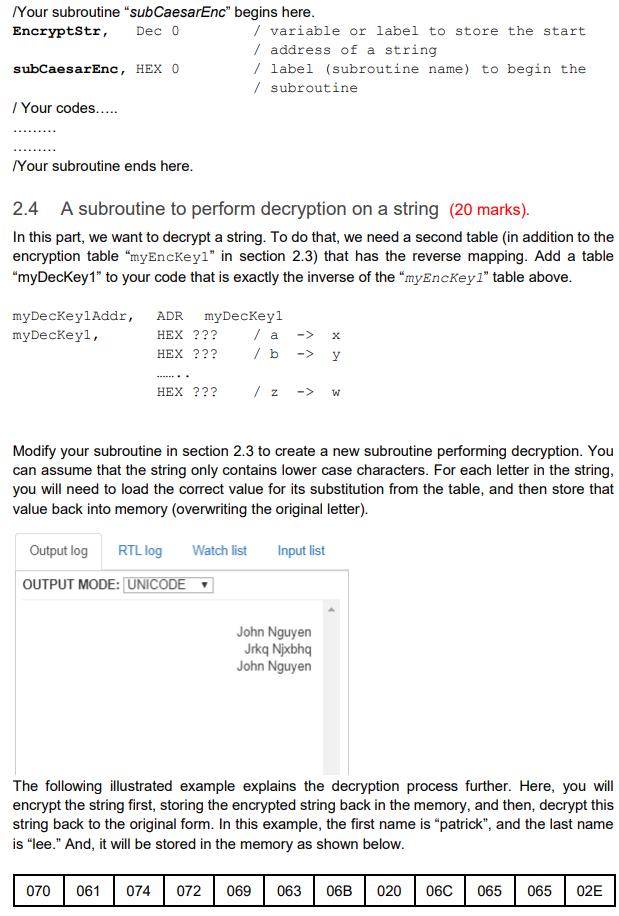
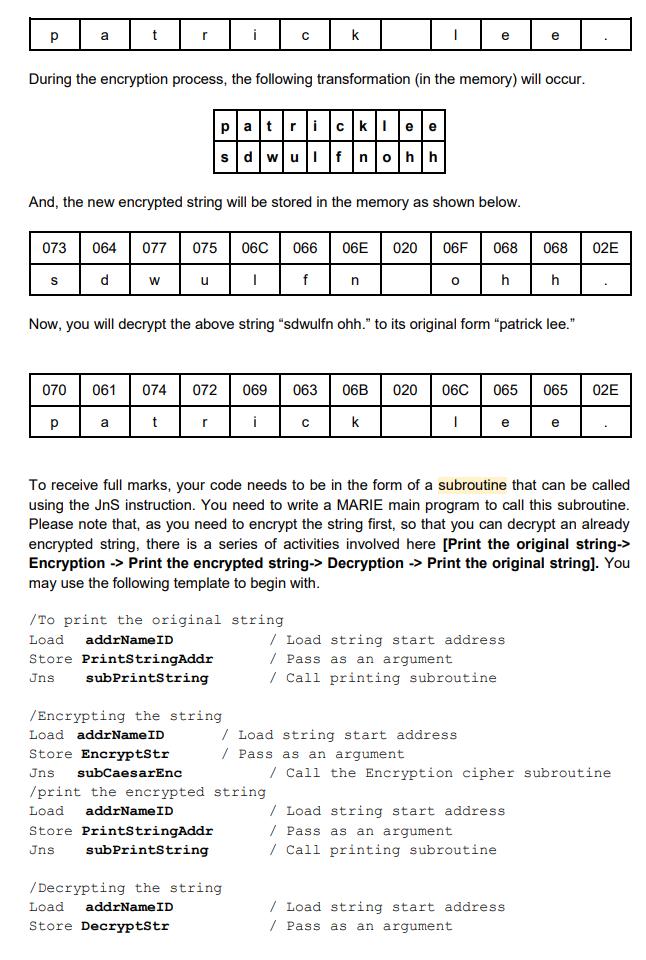
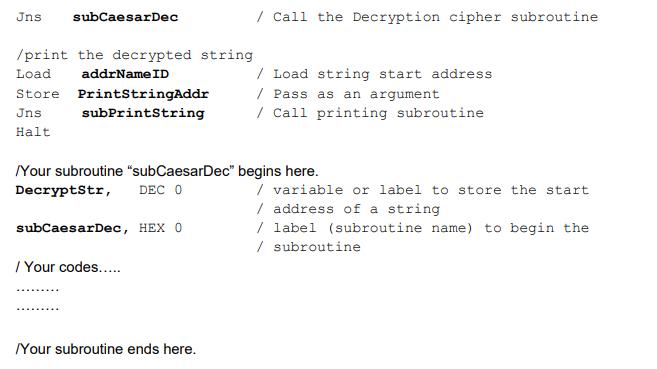
Transcribed Image Text:
Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine Write a MARIE program to encode your name and ID as a string The following example of a MARIE string "nameID" encodes a name and an ID using ASCII characters. The "name" is separated from the ID by an ASCII character "Hex 00A" (New Line). Different parts of a name are separated by another ASCII character "Hex 020" (Space). And, the string is terminated by a dot character. The label "addrNameID" holds the address of the first character of the string. You need to follow this MARIE string while solving the task given below. addrNameID, ADR namelD nameID, HEX 04A HEX 06F HEX 068 HEX 06E HEX 020 HEX 04E HEX 067 HEX 075 HEX 079 HEX 065 HEX 06E HEX 00A HEX 032 HEX 031 HEX 032 HEX 033 HEX 039 HEX 037 HEX 039 HEX 038 HEX 02E ['J' l'o' /'h' /'n' /Space /'N' I'g' l'u' l'y' l'e' /'n' /NL(New Line) /'2' /'1' /'2' /'3' 1'9' ('7' /'9' /'8' Encode a string that includes your full name (first name and last name) and your student ID using ASCII characters. Following the above example, you need to use two labels, one label (e.g. "nameID") to store the first character of the string, and another label (e.g. "addrNameID") to store the address of the first character of the same string. You need to use the ADR command and HEX keywords (like the above example), so that after assembling, your name, ID and the address (of the first character of the string) is stored in MARIE memory. 2.2 Write a MARIE program to print the name and ID using subroutines (15 marks) Prepare a MARIE subroutine called subPrintString that can print the ASCII terminated string of your name and your student ID that you have implemented above. You may use the "Output" instruction to print characters in the MARIE output space. To receive full marks, your program must have a subroutine to print the name and ID string. The subroutine needs to be called from a MARIE main program using a JnS instruction. Hint: In your main program, you need to use a label "StringAdd" that holds the start address of the string (like, addrNameID) that you want to print. Then, you should call the subroutine subPrintString. In the subroutine, the codes should then load a character from the address "StringAdd", print the character, then increment the address by one, and keep doing that upto the character loaded from the address is a' (which signals the end of the string). The output may look similar to the output below. John Nguyen 21239798 2.3 Implementation of Caesar Cipher Substitution to encrypt a string (20 marks) In this section, we are going to implement Caesar Cipher (a type of substitution cipher) encryption that we have learned in the Cryptography lab. It replaces each character in a string by a different character of the alphabet defined by a simple shift. An encryption "Key" using a shift of 3 positions, shown in the table below. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z defghijklmnopqrstuvwx|yz|ab|c This is a very simple form of encryption. Please note the use of lower case alphabets only, and we will encrypt or decrypt only "alphabets". One more example "Key" below is showing a Caesar Cipher with a shift of 5 positions. |a|b|c|d|e|f|g|h|i|i|k|i|m|n|o|p|q|r|s|t|u|v|w|x|y|z fghijklmnopqrstuvwxyz abcde To encrypt, each letter in the top row is replaced by the corresponding letter in the bottom row, and to decrypt, each letter in the bottom row is replaced by the corresponding letter in the top row. In this part, your task is to implement subroutines that perform Caesar cipher substitution on a string, either performing encryption or decryption (cipher or decipher). You will implement the mapping in MARIE by a lookup table, storing the result of the substitution for each letter. The lookup table below maps an encryption key using a shift of 3 positions. myEncKeylAddr, myEncKeyl, ADR HEX HEX 065 / b HEX 066 / c HEX 067 / d HEX 068 HEX 069 / f HEX 06A / g HEX 06B / h HEX 06C HEX 06D HEX 06E HEX 06F HEX 070 HEX 071 HEX 072 HEX 073/p HEX 074/ q HEX 075 HEX 076 / s HEX 077 / t HEX 078 HEX 079 HEX 07A HEX 061 HEX 062 HEX 063 myEnckey1 064/ a -> d -> e -> -> -> -> / V / W / x / y / z -> j ^ ^ ^ -> k /i -> thi (D / j / k -> / 1 -> / m -> /n -> / 0 HECO 1 m n HQ T S -> -> u < C -> V -> -> -> -> -> -> b -> C W 3 XNQ Z a A subroutine to perform encryption on a string In this task, you will implement a MARIE subroutine called subCaesarEnc that can perform encryption using Caesar cipher substitution on a string whose start address is passed as an argument in the EncryptStr label. You need to use the "name" part of the string referred to in section 2.1 (name/D containing your first name and last name) to encrypt. You need to display the string before and after the encryption process. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table "myEnckey1", and then store that value back into memory (overwriting the original letter). Think about how to get "a value" from a table. E.g., assume that the original letter is 'k', which is the 11th letter in the alphabet. So we need to load the 11th entry in the table- in other words, the entry at address myEncKey1Addr + 10 (which is HEX 06E or DEC 110, or the letter 'n'). The letter 'k' has an ASCII value of HEX 06B (DEC 107). So, how do we determine to add '10' to the address "myEncKey1Addr"? We simply subtract the ASCII value for the letter 'a', which is HEX 061 (DEC 97). So, in decimal notation, "117 - 97 = 10" or in HEX notation, "HEX 06B - HEX 061 = HEX A." The following illustrated example explains the encryption process further. Here, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 070 Р 073 S 061 074 072 069 063 t i a r During the encryption process, the following transformation (in the memory) will occur. Load Store Jns sdwulf nohh And, the new encrypted string will be stored in the memory as shown below. W Load Store Jns Halt с u 06B 020 06C k I patricklee 064 077 075 06C 066 06E 020 06F d I f /printing the string before encryption Load addrName ID PrintStringAddr Store Jns subPrintString /printing the string after addrName ID PrintStringAddr subPrintString n /calling the subroutine to perform encryption addrName ID EncryptStr subCaesarEnc 065 065 02E e 0 Please note that, during the encryption process, ASCII value for "SPACE" and remains unchanged. To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. You may use the following template to begin with. Here, we are (re)using the subPrintString subroutine from section 2.2. 068 h e 068 h / Load string start address / Pass as an argument / Call printing subroutine 02E / Load string start address / Pass as an argument / Call the cipher subroutine encryption / Load string start address /Pass as an argument / Call printing subroutine /Your subroutine "subCaesarEnc" EncryptStr, Dec 0 subCaesarEnc, HEX 0 / Your codes..... /Your subroutine ends here. 2.4 A subroutine to perform decryption on a string (20 marks). In this part, we want to decrypt a string. To do that, we need a second table (in addition to the encryption table "myEncKeyl" in section 2.3) that has the reverse mapping. Add a table "myDeckey1" to your code that is exactly the inverse of the "myEncKey1" table above. myDecKeylAddr, myDecKeyl, ADR HEX ??? HEX ??? . 070 begins here. / variable or label to store the start / address of a string label (subroutine name) to begin the / subroutine myDecKeyl /а /b HEX ??? Output log RTL log OUTPUT MODE: UNICODE -> Modify your subroutine in section 2.3 to create a new subroutine performing decryption. You can assume that the string only contains lower case characters. For each letter in the string, you will need to load the correct value for its substitution from the table, and then store that value back into memory (overwriting the original letter). Watch list / 2 -> W X Input list John Nguyen Jrkq Njxbhq John Nguyen The following illustrated example explains the decryption process further. Here, you will encrypt the string first, storing the encrypted string back in the memory, and then, decrypt this string back to the original form. In this example, the first name is "patrick", and the last name is "lee." And, it will be stored in the memory as shown below. 061 074 072 069 063 06B 020 06C 065 065 02E Р 073 S a 070 t Р r During the encryption process, the following transformation (in the memory) will occur. And, the new encrypted string will be stored in the memory as shown below. W a u 061 074 072 t i 064 077 075 06C 066 06E 020 06F d I f r patricklee с sdwulf nohh k /Encrypting the string Load addrName ID Store EncryptStr Jns subCaesarEnc Now, you will decrypt the above string "sdwulfn ohh." to its original form "patrick lee." /To print the original string Load addrName ID Store PrintStringAddr Jns subPrintString 069 063 i /Decrypting the string Load addrName ID Store DecryptStr /print the encrypted string Load addrNameID Store PrintStringAddr Jns subPrintString C n e 0 068 h / Load string start address / Pass as an argument e To receive full marks, your code needs to be in the form of a subroutine that can be called using the JnS instruction. You need to write a MARIE main program to call this subroutine. Please note that, as you need to encrypt the string first, so that you can decrypt an already encrypted string, there is a series of activities involved here [Print the original string-> Encryption -> Print the encrypted string-> Decryption -> Print the original string]. You may use the following template to begin with. e 06B 020 06C 065 065 02E k / Load string start address /Pass as an argument / Call printing subroutine 068 h / Load string start address / Pass as an argument / Call printing subroutine / Load string start address / Pass as an argument 02E e / Call the Encryption cipher subroutine Jns subCaesarDec /print the decrypted string addrName ID Load Store Jns Halt PrintStringAddr subPrintString Your subroutine "subCaesarDec" DecryptStr, DEC 0 subCaesarDec, HEX 0 / Your codes..... /Your subroutine ends here. / Call the Decryption cipher subroutine / Load string start address /Pass as an argument / Call printing subroutine begins here. / variable or label to store the start / address of a string / label (subroutine name) to begin the / subroutine
Expert Answer:
Answer rating: 100% (QA)
Heres a MARIE program that encodes a string with your full name and student ID using ASCII characters ORG 200 addrNameID HEX 0 Placeholder for the address of the string nameID HEX 0 Placeholder for th... View the full answer

Related Book For 

Java An Introduction To Problem Solving And Programming
ISBN: 9780134462035
8th Edition
Authors: Walter Savitch
Posted Date:
Students also viewed these programming questions
-
Perform a preliminary design of a 2-stage solid rocket to lift an 4,000 kg payload to LEO. The composite propellants are 17% by mass Al fuel, 67% AP oxidizer and 16% HTPB binder, ignore the other...
-
Precision Systems, Inc. (PSI)* Precision Systems, Inc. (PSI) has been in business for more than 40 years and has generally reported a positive net income. The company manufactures and sells...
-
Consider a binomial distribution with n = 5 trials. Use the probabilities given in Table 2 of the Appendix to make histograms showing the probabilities of r = 0, 1, 2, 3, 4, and 5 successes for each...
-
1. What velocity will a 300 kg snowmobile acquire if pushed from rest by a force of 6240 N [E] for 1.25 s? What average force will stop this snowmobile from moving at this speed in 1.25 s? (v = 26.0...
-
A hydrogen atom undergoes a transition from a 2p state to the Is ground state. In the absence of a magnetic field, the energy of the photon emitted is 122 nm. The atom is then placed in a strong...
-
Refer to Exercise 55. Suppose that Gallup wanted to cut the margin of error in half from 3 percentage points to 1.5 percentage points. How should they adjust their sample size? a. Multiply the sample...
-
Consider the automobile gasoline mileage data in Table B.3. a. Build a linear regression model relating gasoline mileage \(y\) to engine displacement \(x_{1}\) and the type of transmission...
-
The owner of an automobile repair shop studied the waiting times for customers who arrive at the shop for an oil change. The following data with waiting times in minutes were collected over a 1-month...
-
sked byChina699 BEMIDJI STATE UNIVERSITY Department of Technology, Art & Design TADT 3217 : Materials Science & Metallurgy Hardness Testing [A continued look at the Heat Treatment of Steel] ...
-
Add minimum and maximum cardinality notation to each of the following figures, as appropriate: a. Figure 2-5 b. Figure 2-10a c. Figure 2-11b d. Figure 2-12 (all parts) e. Figure 2-13c f. Figure 2-14
-
Question: Today's spot USD/Yen rate is 110. You bought $10 million against yen today. The next day the spot went up to 120. How much money, in terms of USD, have you made by the end of tomorrow?
-
(a) (23 points) Suppose z = x + iy, where x and y are real. Write the following complex numbers in the Cartesian form a + ib, where a and b are real: (al) 2+2 1 + z' (a2) (1 + i) 2023 (b) (4 points)...
-
WATCH DOCUMENTARY: https://youtu.be/V3kJ6OticrY Questions: 1. What insights did you gain from watching the documentary? List and explain at least three. Timestamp each point from the video. 2. For...
-
1. (a) Determine a parametrization (t) of the curve defined by the intersection of the surfaces z=x+ y and z = 5. V (b) Write an equation of the tangent line to r(t) (from part (a)) at the point...
-
research the foreclosure process in a state other than Florida. Then compare your selected state's procedures and laws to what you discovered about the process in Florida. Is one state more...
-
7. (a) Evaluate the function te ',t>0 by the Fourier sine and cosine integral formulas. (b) Evaluate x +x2)2 sin(ax)dx and So (+12)25 1-2 To (1 + 2/2 cos(ax) dr.
-
Determine the average rate of change of B from t=0 s to t=202s. A --> 2B Time (s) Concentration of A(M) 0 0.640 101 0.380 202 0.120 Answer in M/s. Show work and explain
-
The following selected accounts and normal balances existed at year-end. Notice that expenses exceed revenue in this period. Make the four journal entries required to close the books: Accounts...
-
Write a parameterized class definition for a doubly linked list that has a parameter for the type of data stored in a node. Make the node class an inner class. Choosing which methods to define is...
-
Suppose we want to implement a drawing program that creates various shapes using keyboard characters. Implement an abstract base class DrawableShape that knows the center (two integer values) and the...
-
What does the following Java statement display? System.out.println("\"\tTest\\\\ It\'"); Does replacing the r with an n make a difference in what is displayed?
-
From the following figures, compile accounts receivable ledger and accounts payable ledger control accounts for the month, and ascertain what the net balances of the respective ledgers should be on...
-
Why may some people consider this to be incorrect? That is, why is the fact that the control account is kept in the General Ledger not enough to justify saying that the control account is part of the...
-
The financial year of The Better Trading Company ended on 30 November 2014. You have been asked to prepare a Total Accounts Receivable Account and a Total Accounts Payable Account in order to produce...

Study smarter with the SolutionInn App