Write a program using only the following MIPS instructions: The memory reference instructions load word...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
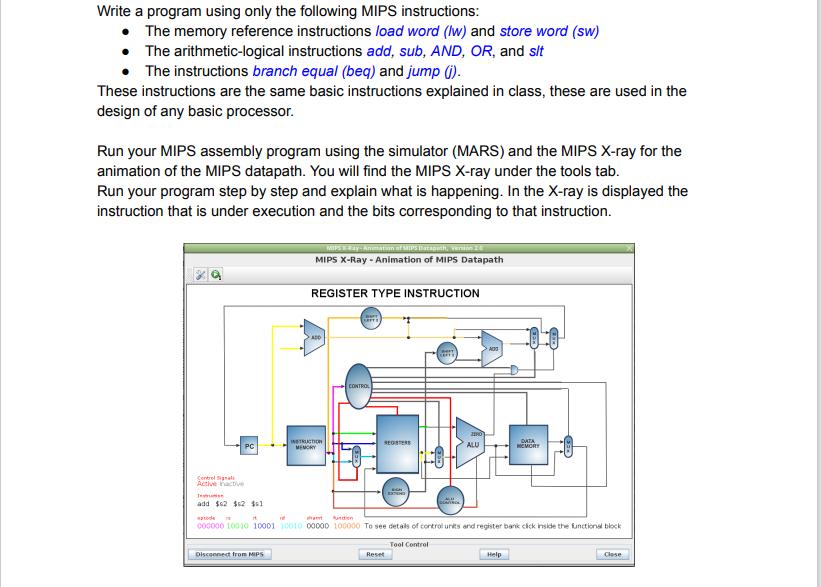
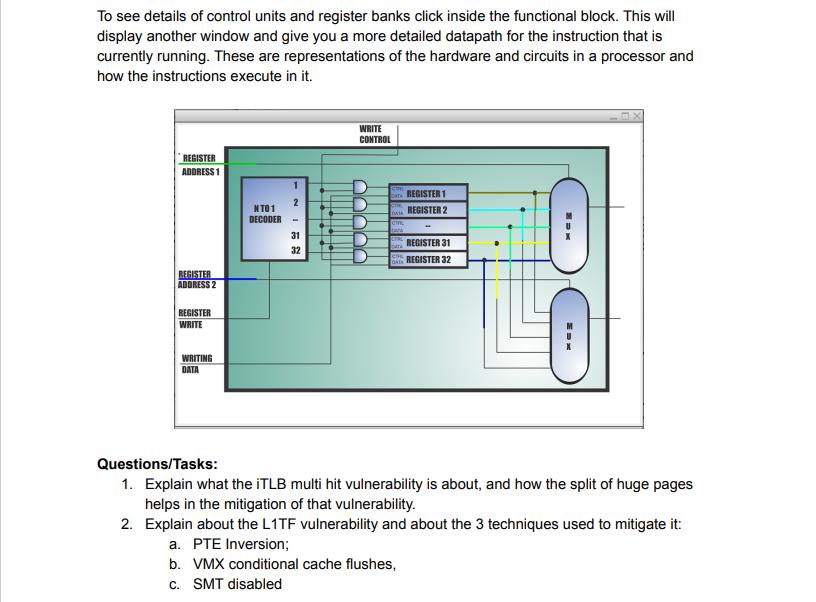
Write a program using only the following MIPS instructions: • The memory reference instructions load word (lw) and store word (sw) The arithmetic-logical instructions add, sub, AND, OR, and sit The instructions branch equal (beq) and jump (j). • These instructions are the same basic instructions explained in class, these are used in the design of any basic processor. Run your MIPS assembly program using the simulator (MARS) and the MIPS X-ray for the animation of the MIPS datapath. You will find the MIPS X-ray under the tools tab. Run your program step by step and explain what is happening. In the X-ray is displayed the instruction that is under execution and the bits corresponding to that instruction. PC Control Signals Active active Jesse add $62 $2 $1 MIPS Ray-Animation of SHIPS Datapeth, version 2.0 MIPS X-Ray - Animation of MIPS Datapath Disconnect from MIPS REGISTER TYPE INSTRUCTION ADD INSTRUCTION MEMORY CONTROL REGSTERS CH EXTING Reset DEAVTROK Tool Control 1180 ALU pode in ht funcion 000000 10010 10001 10010 00000 100000 To see details of control units and register bank cick inside the functional block A00 DATA HOVORY Help Close To see details of control units and register banks click inside the functional block. This will display another window and give you a more detailed datapath for the instruction that is currently running. These are representations of the hardware and circuits in a processor and how the instructions execute in it. REGISTER ADDRESS 1 REGISTER ADDRESS 2 REGISTER WRITE WRITING DATA NT01 DECODER 1 2 - 31 32 6 WRITE CONTROL cm. LUL REGISTER 1 REGISTER 2 REGISTER 31 REGISTER 32 Questions/Tasks: 1. Explain what the iTLB multi hit vulnerability is about, and how the split of huge pages helps in the mitigation of that vulnerability. 2. Explain about the L1TF vulnerability and about the 3 techniques used to mitigate it: a. PTE Inversion; b. VMX conditional cache flushes, c. SMT disabled Write a program using only the following MIPS instructions: • The memory reference instructions load word (lw) and store word (sw) The arithmetic-logical instructions add, sub, AND, OR, and sit The instructions branch equal (beq) and jump (j). • These instructions are the same basic instructions explained in class, these are used in the design of any basic processor. Run your MIPS assembly program using the simulator (MARS) and the MIPS X-ray for the animation of the MIPS datapath. You will find the MIPS X-ray under the tools tab. Run your program step by step and explain what is happening. In the X-ray is displayed the instruction that is under execution and the bits corresponding to that instruction. PC Control Signals Active active Jesse add $62 $2 $1 MIPS Ray-Animation of SHIPS Datapeth, version 2.0 MIPS X-Ray - Animation of MIPS Datapath Disconnect from MIPS REGISTER TYPE INSTRUCTION ADD INSTRUCTION MEMORY CONTROL REGSTERS CH EXTING Reset DEAVTROK Tool Control 1180 ALU pode in ht funcion 000000 10010 10001 10010 00000 100000 To see details of control units and register bank cick inside the functional block A00 DATA HOVORY Help Close To see details of control units and register banks click inside the functional block. This will display another window and give you a more detailed datapath for the instruction that is currently running. These are representations of the hardware and circuits in a processor and how the instructions execute in it. REGISTER ADDRESS 1 REGISTER ADDRESS 2 REGISTER WRITE WRITING DATA NT01 DECODER 1 2 - 31 32 6 WRITE CONTROL cm. LUL REGISTER 1 REGISTER 2 REGISTER 31 REGISTER 32 Questions/Tasks: 1. Explain what the iTLB multi hit vulnerability is about, and how the split of huge pages helps in the mitigation of that vulnerability. 2. Explain about the L1TF vulnerability and about the 3 techniques used to mitigate it: a. PTE Inversion; b. VMX conditional cache flushes, c. SMT disabled
Expert Answer:
Answer rating: 100% (QA)
Here is a simple MIPS program that calculates the sum of two numbers and stores the result in m... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Being a marketing manager of Amazon, what are the five important things you can do to continue providing "value" to your customer base?
-
A partial statement of financial position of Century University is shown below. During the fiscal year ended June 30, 2011, the following transactions occurred: 1. A gift of $100,000 was received...
-
The acceleration of a particle is given by ax < t) = -2. (JOm/S2 + (3.oom/s3)t. (a) Find the initial velocity vax such that the particle will have the same x-coordinate at t = 4.00 s as it had at t =...
-
A catchment has four sub-areas. The annual precipitation and evaporation from each of the sub-areas are given below. Assume that there is no change in the groundwater storage on an annual basis and...
-
The Anchor Glass Container Corporation and its parent company, Consumers Packaging, Inc. (CPI), entered into a series of agreements with Encore Glass, Inc., to supply glass containers of a specific...
-
You are the digital marketing director for High West fashions, a regional clothing company that specializes in custom t-shirts. Your company has decided to launch an online advertising campaign that...
-
2. Home Depot (HD) recently paid a annual dividend of $1.50 per share. Using a one period dividend growth model, what is the price of one share of HD stock if the terminal dividend growth rate is 5%?...
-
Complete Tsate's Form 1040-SR, Schedules A, B and D, Form 8949, Form 6252 and Qualified Dividends and Capital Gain Tax Worksheet. Tsate Kongia (birthdate 02/14/1954) is an unmarried high school...
-
The Table below displays the number of books read by different age groups. Fiction Books 15- 20 years 20-30 years 30 years and above 24. 20 10 Biography Books 5 28 40 What is the probability of...
-
Assess the relative strengths of different schedules of reinforcement in a business context.
-
List the common characteristics of an organization.
-
Explain the following terms: (a) primary and secondary reinforcement; (b) positive and negative reinforcement; (c) concurrent reinforcement; (d) avoidance conditioning; and (e) contiguity and...
-
Outline the functions performed by attitudes.
-
List models of decision making and decision biases.
-
9. Management accountants usually prefer the sales value at the split-off point method because? a. it builds on the benefits-received criterion b. it builds on the cause-and-effect criterion. c. it...
-
Wimot Trucking Corporation uses the units-of-production depreciation method because units-of-production best measures wear and tear on the trucks. Consider these facts about one Mack truck in the...
-
Fill in the blanks in each of the following statements: a) ___________are used to document an app and improve its readability. b) A decision can be made in a C# app with a(n) ___________. c)...
-
Explain what happens when a C# app attempts to divide one integer by another. What happens to the fractional part of the calculation? How can you avoid that outcome?
-
Develop a C# app that will determine the gross pay for each of three employees. The company pays straight time for the first 40 hours worked by each employee and time-and-a-half for all hours worked...
-
The truss shown in figure 1.30 has two elements. The members are made of the aluminum hollow square cross section. The outer dimension of the square is \(12 \mathrm{~mm}\), and the inner dimension is...
-
Solve the onedimensional heat conduction problem 6 using the RayleighRitz method. For the heat conduction problem, the total potential can be defined as Use the approximate solution...
-
Consider a system of rigid bodies connected by springs as shown in figure 2.20. The bodies are assumed to move only in the horizontal direction. Further, we consider only the static problem, and...

Study smarter with the SolutionInn App


