Write a SASM program that encrypts a user-entered string using a user-entered key (required algorithm is...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
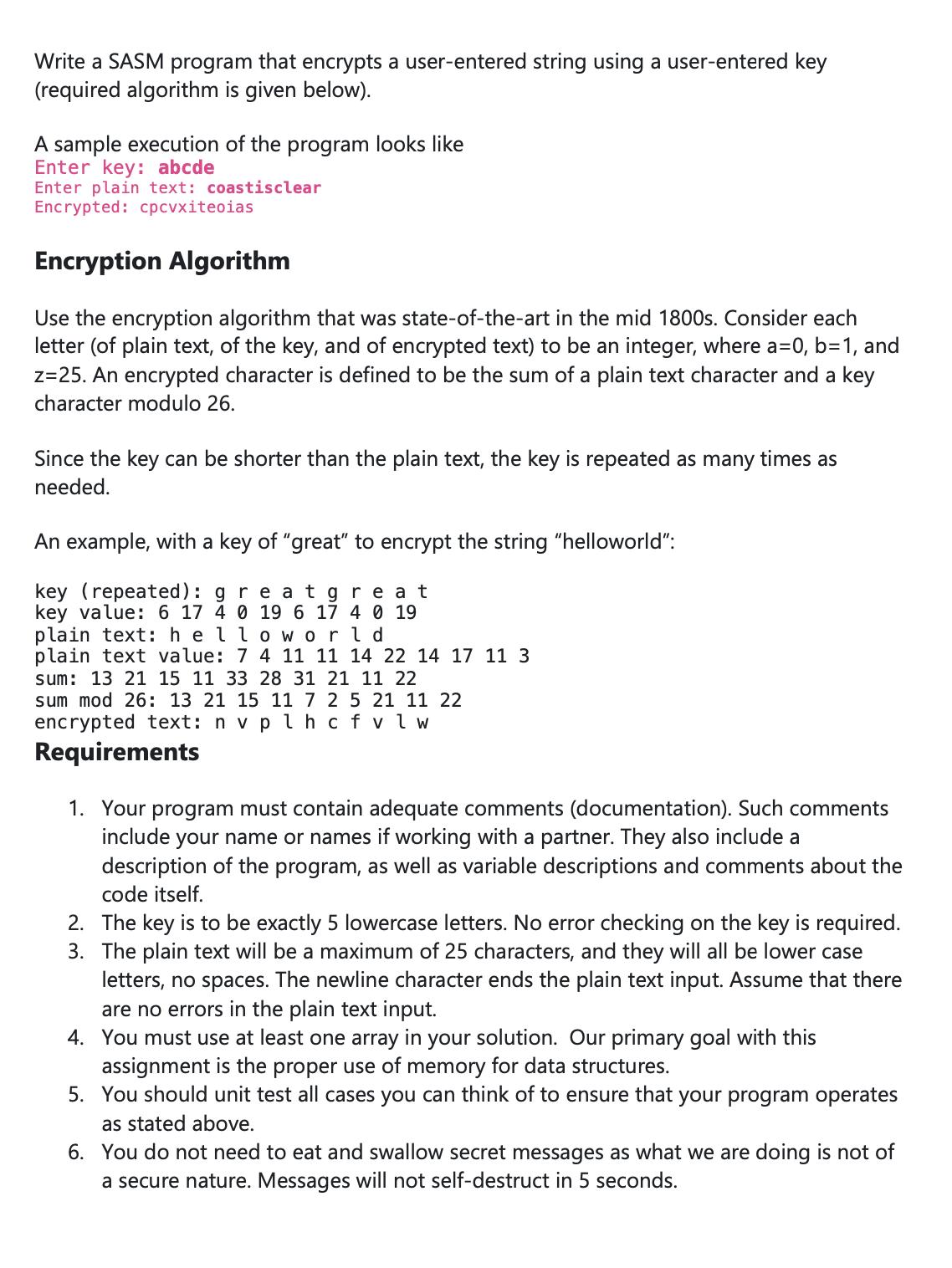
Write a SASM program that encrypts a user-entered string using a user-entered key (required algorithm is given below). A sample execution of the program looks like Enter key: abcde Enter plain text: coastisclear Encrypted: cpcvxiteoias Encryption Algorithm Use the encryption algorithm that was state-of-the-art in the mid 1800s. Consider each letter (of plain text, of the key, and of encrypted text) to be an integer, where a=0, b=1, and z=25. An encrypted character is defined to be the sum of a plain text character and a key character modulo 26. Since the key can be shorter than the plain text, the key is repeated as many times as needed. An example, with a key of "great" to encrypt the string "helloworld": key (repeated): great great key value: 6 17 4 0 19 6 17 4 0 19 plain text: hello world plain text value: 7 4 11 11 14 22 14 17 11 3 sum: 13 21 15 11 33 28 31 21 11 22 sum mod 26: 13 21 15 11 7 2 5 21 11 22 encrypted text: n v plh cf v l w Requirements 1. Your program must contain adequate comments (documentation). Such comments include your name or names if working with a partner. They also include a description of the program, as well as variable descriptions and comments about the code itself. 2. The key is to be exactly 5 lowercase letters. No error checking on the key is required. 3. The plain text will be a maximum of 25 characters, and they will all be lower case letters, no spaces. The newline character ends the plain text input. Assume that there are no errors in the plain text input. 4. You must use at least one array in your solution. Our primary goal with this assignment is the proper use of memory for data structures. 5. You should unit test all cases you can think of to ensure that your program operates as stated above. 6. You do not need to eat and swallow secret messages as what we are doing is not of a secure nature. Messages will not self-destruct in 5 seconds. Write a SASM program that encrypts a user-entered string using a user-entered key (required algorithm is given below). A sample execution of the program looks like Enter key: abcde Enter plain text: coastisclear Encrypted: cpcvxiteoias Encryption Algorithm Use the encryption algorithm that was state-of-the-art in the mid 1800s. Consider each letter (of plain text, of the key, and of encrypted text) to be an integer, where a=0, b=1, and z=25. An encrypted character is defined to be the sum of a plain text character and a key character modulo 26. Since the key can be shorter than the plain text, the key is repeated as many times as needed. An example, with a key of "great" to encrypt the string "helloworld": key (repeated): great great key value: 6 17 4 0 19 6 17 4 0 19 plain text: hello world plain text value: 7 4 11 11 14 22 14 17 11 3 sum: 13 21 15 11 33 28 31 21 11 22 sum mod 26: 13 21 15 11 7 2 5 21 11 22 encrypted text: n v plh cf v l w Requirements 1. Your program must contain adequate comments (documentation). Such comments include your name or names if working with a partner. They also include a description of the program, as well as variable descriptions and comments about the code itself. 2. The key is to be exactly 5 lowercase letters. No error checking on the key is required. 3. The plain text will be a maximum of 25 characters, and they will all be lower case letters, no spaces. The newline character ends the plain text input. Assume that there are no errors in the plain text input. 4. You must use at least one array in your solution. Our primary goal with this assignment is the proper use of memory for data structures. 5. You should unit test all cases you can think of to ensure that your program operates as stated above. 6. You do not need to eat and swallow secret messages as what we are doing is not of a secure nature. Messages will not self-destruct in 5 seconds.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these programming questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
The victim was stabbed to death, in front of 12 witnesses, during a brawl at the local bar. According to the first officers on the scene, six of the witnesses were too drunk to be reliable. The other...
-
XY is a pharmaceutical company with the head-quarter in the United States. However, its cash flow depends only on sales in Japan. It receives a cash flow of Yen 20 billion with certainty in t=1. The...
-
Evaluate the function for the given values. 1. f(x) = [[x]] (a) f(2.1) (b) f(2.9) (c) f(3.1) (d) f(1/2) 2. h(x) = [[x + 3]] (a) h(2) (b) h(1/2) (c) h(4.2) (d) h(21.6) 3. k(x) = [[2x + 1]] (a) k(1/3)...
-
Brothers Ltd began operations on 1 February 2016. The trial balance at 30 June is as follows. In addition to those accounts listed on the trial balance, the chart of accounts for Brothers Ltd also...
-
You throw a ball straight up in the air. Which of the following forces do work on the ball while you throw it? Consider the interval from the instant the ball is at rest in your hand to the instant...
-
What individual differences, personality traits, and attitudes might contribute to a reasonable person job fit for the position of DVD inspector at a Netflix warehouse? What steps might Netflix take...
-
10.A positively charged particle of specific charge , accelerated by a potential difference V moves through a uniform transverse magnetic field
-
Given the time-phased work packages and network, complete the baseline budget form for theproject. Market Survey Project WBS Work Package Cost by Week WP Design 4 5 2 WP Survey 2244 4 5 WP Report 3 3...
-
Thompson Turf Trimmers, Inc., reported the following financial statements for 2018: (Click the icon to view the income statement.) (Click the icon to view the comparative balance shoots.) a....
-
At the age of 30, you begin saving $6000 each year (with the first deposit one year from now) in an account that pays an annual interest rate of 7%. Your plan is to continue these annual deposits...
-
Consider the angle 0, which is labeled as Q in blue on the graph, with corresponding point P on the circle. Sketch each of the angles given below, then select the point on the circle that best...
-
how HIPAA might adversely influence project communication. How might your own communication bias influence project communication?
-
Prepare financial ratios in evaluating Islamic bank's performance by using Profitability Ratio only. Company No. 719057-X STATEMENTS OF FINANCIAL POSITION AS AT 31 DECEMBER 2019 ASSETS Group Bank...
-
Do you use social media to communicate? What are the strengths and weaknesses of Facebook, Twitter and Instagram? How can you use LinkedIn to advance your career?
-
What can you improve on this income statement: Turnover 840 000.00 Trading Income Commission - Connected Garden 420 000,00 Commission - Free Range 82 000,00 Commission - Macadamia Nut Tree 102 000,00...
-
One of the significant and relevant accounts for this cycle is equipment. For this account, what would typically be the most relevant assertions for the auditor to consider? Why is it important for...
-
Suppose that data are transmitted in blocks of sizes 1000 bits. What is the maximum error rate under which error detection and re-transmission mechanism (1 parity bit per block) is better than using...
-
In the discussion of ARQ protocol in Section 3.3.3, a scenario was outlined that resulted in the receiver accepting two copies of the same frame due to a loss of acknowledgement frame. Is it possible...
-
Consider the network of Fig. 5-15(a). Imagine that one new line is added, between F and G, but the sink tree of Fig. 5-15(b) remains unchanged. What changes occur to Fig. 5-15(c) Figure 5-15 A A D (...
-
Are the initial rates lower on a fixed-rate loan or a variable-rate loan? Why?
-
Why are mortgage payments not included in the debt limit ratio?
-
Credit card fraud is considered almost incidental to the potentially more damaging and costly problem of identity theft. Check the Internet for recent statistics on the number of consumers affected,...

Study smarter with the SolutionInn App


