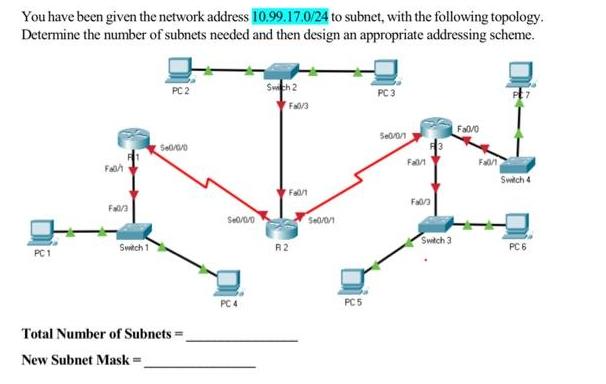
You have been given the network address 10.99.17.0/24 to subnet, with the following topology. Determine the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
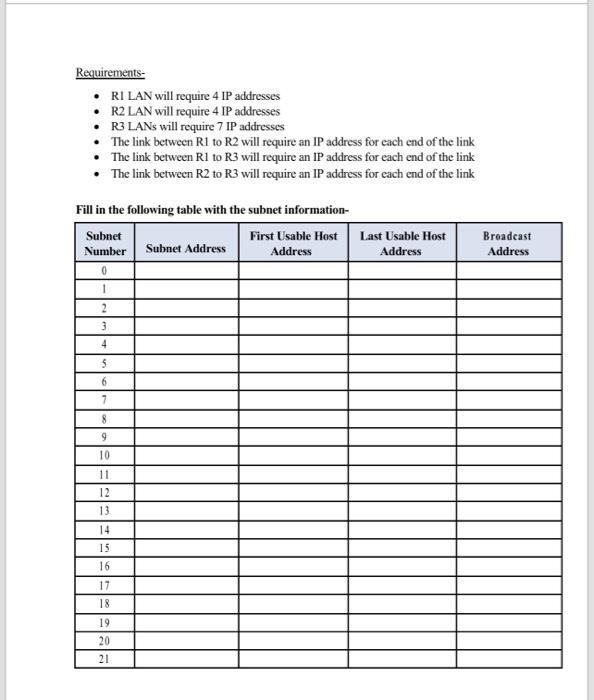
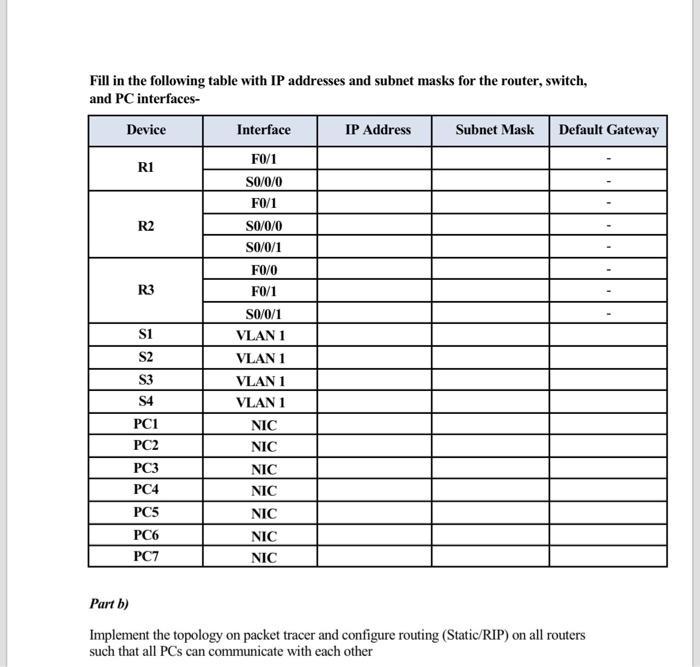
You have been given the network address 10.99.17.0/24 to subnet, with the following topology. Determine the number of subnets needed and then design an appropriate addressing scheme. PC1 Fah Fa0/3 Switch 1 560/0/0 Total Number of Subnets= New Subnet Mask = S+0/0/0 PC 4 Swch 2 Fa0/3 Fa0/1 R2 5+0/0/1 PC 5 PC 3 50/0/1 Fal/1 Fa0/3 Switch 3 Fa0/0 Fa0/1 Switch 4 PC 6 Requirements- RI LAN will require 4 IP addresses R2 LAN will require 4 IP addresses R3 LANs will require 7 IP addresses The link between R1 to R2 will require an IP address for each end of the link The link between R1 to R3 will require an IP address for each end of the link The link between R2 to R3 will require an IP address for each end of the link Fill in the following table with the subnet information- Subnet First Usable Host Number Address 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 Subnet Address Last Usable Host Address Broadcast Address Fill in the following table with IP addresses and subnet masks for the router, switch, and PC interfaces- Device R1 R2 R3 S1 S2 S3 S4 PC1 PC2 PC3 PC4 PC5 PC6 PC7 Interface F0/1 S0/0/0 F0/1 S0/0/0 S0/0/1 FO/0 F0/1 S0/0/1 VLAN 1 VLAN 1 VLAN 1 VLAN 1 NIC NIC NIC NIC NIC NIC NIC IP Address Subnet Mask Default Gateway Part b) Implement the topology on packet tracer and configure routing (Static/RIP) on all routers such that all PCs can communicate with each other You have been given the network address 10.99.17.0/24 to subnet, with the following topology. Determine the number of subnets needed and then design an appropriate addressing scheme. PC1 Fah Fa0/3 Switch 1 560/0/0 Total Number of Subnets= New Subnet Mask = S+0/0/0 PC 4 Swch 2 Fa0/3 Fa0/1 R2 5+0/0/1 PC 5 PC 3 50/0/1 Fal/1 Fa0/3 Switch 3 Fa0/0 Fa0/1 Switch 4 PC 6 Requirements- RI LAN will require 4 IP addresses R2 LAN will require 4 IP addresses R3 LANs will require 7 IP addresses The link between R1 to R2 will require an IP address for each end of the link The link between R1 to R3 will require an IP address for each end of the link The link between R2 to R3 will require an IP address for each end of the link Fill in the following table with the subnet information- Subnet First Usable Host Number Address 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 Subnet Address Last Usable Host Address Broadcast Address Fill in the following table with IP addresses and subnet masks for the router, switch, and PC interfaces- Device R1 R2 R3 S1 S2 S3 S4 PC1 PC2 PC3 PC4 PC5 PC6 PC7 Interface F0/1 S0/0/0 F0/1 S0/0/0 S0/0/1 FO/0 F0/1 S0/0/1 VLAN 1 VLAN 1 VLAN 1 VLAN 1 NIC NIC NIC NIC NIC NIC NIC IP Address Subnet Mask Default Gateway Part b) Implement the topology on packet tracer and configure routing (Static/RIP) on all routers such that all PCs can communicate with each other
Expert Answer:
Answer rating: 100% (QA)
To determine the number of subnets and design an appropriate addressing scheme for the provided topology lets go through the requirements and analyze the network address given You have been provided w... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these computer network questions
-
How do organizations effectively navigate the complexities of organizational change, integrating advanced change management methodologies to mitigate resistance and foster sustainable transformation?
-
What ethical dilemmas and considerations arise in the implementation of diversity initiatives, particularly concerning issues of tokenism, reverse discrimination, and the inadvertent reinforcement of...
-
How do individual differences in coping mechanisms and resilience influence the effectiveness of stress management interventions, and what personalized approaches can organizations implement to...
-
This bar chart displays the demographics (age group and gender) of a Business Analysis class Business Analysts Students 23-33 3410 M lem How many male students are in the class? 65 80 130 50
-
Use a graphing utility to graph the function and visually determine the open intervals on which the function is increasing, decreasing, or constant. Use a table of values to verify your results. 1....
-
Refer to question 21 at the end of Chapter 2. Implement a spreadsheet model for this problem and solve it using Solver.
-
Under what conditions is an auditor most likely to confirm payables?
-
(Three Differences, Multiple Rates, Future Taxable Income) During 2010, Graham Co.'s first year of operations, the company reports pretax financial income of $250,000. Graham's enacted tax rate is...
-
Marigold Company manufactures and sells three products. Relevant per unit data concerning each product are given below. Product Selling price $8 A < 00 Variable costs and expenses $5 Machine hours to...
-
Assume that you are the auditor of ABC Inc, for the fiscal year 2006. No audit procedures have been performed other than general information gathering. Please read all the information given below...
-
In managing the operations of Ivanhoe Foods, Helen was trying to determine the total cost of producing its world-famous chicken noodle soup. She understood MOH costs were a large portion of the...
-
The General Social Survey asked a sample of 1294 people whether they performed any volunteer work during the past year. A total of 517 people said they did. Can you conclude that more than \(35 \%\)...
-
In a test to compare yield strengths of two grades of carbon steel bolts, strengths of eight grade 2 bolts and six grade 5 bolts were measured. The results, in MPa, were Find a \(98 \%\) confidence...
-
Let \(X_{1}, \ldots, X_{n}\) be a random sample from a \(N(\mu, 1)\) population. Find the MLE of \(\mu\).
-
Refer to Exercise 17. a. Find a 95 % 95 % upper confidence bound for the mean mass. b. Find a 99.5 % 99.5 % lower confidence bound for the mean mass. Data From Exercise 17: A sample of 75 concrete...
-
A sociologist sampled 200 people who work in computer-related jobs and found that 42 of them have changed jobs in the past six months. Can you conclude that more than \(15 \%\) of computer-related...
-
5.47 Compute the Grammian for the following vectors and draw conclusions about their linear independence. The given y vectors Y = 1.0000000E+00] 1.0000000E+00 1.0000000E+00 L1.0000000E +00 Y =...
-
What are the before image (BFIM) and after image (AFIM) of a data item? What is the difference between in-place updating and shadowing, with respect to their handling of BFIM and AFIM?
-
Provide a filter table and a connection table for a stateful firewall that is restrictive as possible but accomplishes the following: a. Allows all internal users to establish Telnet sessions with...
-
Host A and B are communicating over a TCP connection, and Host B has already received from A all bytes up through byte 126. Suppose Host A then sends two segments to Host B back-to-back. The first...
-
Consider Figure S.38 in problem P14. Provide MAC addresses and IP addresses for the interfaces at Host A, both routers, and Host F. Suppose Host A sends a datagram to Host F. Give the source and...
-
During Chinas Cultural Revolution in the late 1960s and early 1970s, highly educated people were forced to move to farms and work in the fields. Some were common laborers for eight or more years....
-
In elementary school and through middle school, most students have the same teacher throughout the day and for the entire school year. Then, beginning in high school, different subjects are taught by...
-
In Botswana, Zimbabwe, and South Africa, individuals can own and farm elephants. In other African countries, the elephants are put on large reserves. Explain why the elephant population in Botswana,...

Study smarter with the SolutionInn App


