. Your host in this example has IP address 172.16.1.1. Someone tries to send e-mail from...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
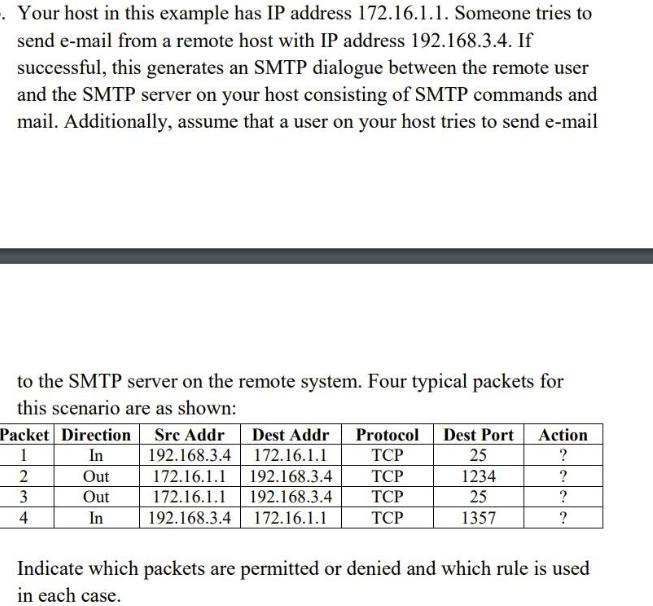
. Your host in this example has IP address 172.16.1.1. Someone tries to send e-mail from a remote host with IP address 192.168.3.4. If successful, this generates an SMTP dialogue between the remote user and the SMTP server on your host consisting of SMTP commands and mail. Additionally, assume that a user on your host tries to send e-mail to the SMTP server on the remote system. Four typical packets for this scenario are as shown: Packet Direction Sre Addr Dest Addr Protocol Dest Port 1 In TCP 2 TCP 3 TCP 4 TCP Out Out In 192.168.3.4 172.16.1.1 172.16.1.1 192.168.3.4 172.16.1.1 192.168.3.4 192.168.3.4 172.16.1.1 25 1234 25 1357 Action ? ? ? ? Indicate which packets are permitted or denied and which rule is used in each case. . Your host in this example has IP address 172.16.1.1. Someone tries to send e-mail from a remote host with IP address 192.168.3.4. If successful, this generates an SMTP dialogue between the remote user and the SMTP server on your host consisting of SMTP commands and mail. Additionally, assume that a user on your host tries to send e-mail to the SMTP server on the remote system. Four typical packets for this scenario are as shown: Packet Direction Sre Addr Dest Addr Protocol Dest Port 1 In TCP 2 TCP 3 TCP 4 TCP Out Out In 192.168.3.4 172.16.1.1 172.16.1.1 192.168.3.4 172.16.1.1 192.168.3.4 192.168.3.4 172.16.1.1 25 1234 25 1357 Action ? ? ? ? Indicate which packets are permitted or denied and which rule is used in each case.
Expert Answer:
Answer rating: 100% (QA)
Answer Typically TCP port 25 is used for SMTP traffic so the first and third packets which are both directed to port 25 would likely be permitted The ... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Posted Date:
Students also viewed these computer network questions
-
Account Number Account Number Cash 101 S. Rey, Capital 301 Accounts Receivable 106 S. Rey, Withdrawals 302 Computer Supplies 126 Computer Services Revenue 403 Prepaid Insurance 128 Wages Expense 623...
-
You wish to build a packet-filter ruleset that allows certain inbound and outbound SMTP traffic to your hosts but blocks all other traffic. SMTP is the standard protocol for transferring mails over a...
-
The three way TCP handshake between sender and receiver A)requires a SYN packet from the sender to be answered by a SYN, ACKpacket from the recipeint which is followed by an ACK packet fromthe sender...
-
Suppose that a surgical ward has gathered the following information for four nursing activities and two types of patients for the current period: Required: 1. Determine the total nursing costs...
-
Martin Manufacturing is preparing its master budget for the first quarter of the upcoming year. The following data pertain to Martin Manufacturing's operations: Current Assets as of December 31...
-
Gabi Gram started The Gram Co., a new business that began operations on May 1. The Gram Co. completed the following transactions during its first month of operations. Required 1. Create the following...
-
State the Type I and Type II errors in complete sentences given the following statements. a. The mean number of years Americans work before retiring is 34. b. At most 60% of Americans vote in...
-
Prepare a flowchart of the field service division process at DEE as described here. Start from the point where a call is received and end when a technician finishes the job. DEF was a multibillion...
-
Nowadays, it is frequent to see companies outsourcing their payroll function. What are the effects of such a decision on the audit of the payroll cycle? (be specific, use examples and audit concepts...
-
A flight simulator is used to train pilots on how to recognize spatial disorientation. It has four degrees of freedom, and can rotate around a planetary axis as well as in yaw, pitch, and roll. The...
-
A number of limits arising from the strict separation of judicial power have been recognized at the Commonwealth level. The existence and scope of these limits reflect the mix of political and legal...
-
What should each worksheet contain besides the audit information?
-
Consider an economy with 10,000 individuals. Of them, 5,000 each earn \($25,000;\) 3,000 each earn \($40,000;\) and 2,000 each earn \($100,000\). (a) What is the Gini coefficient for this economy?...
-
What items of information must be included in a notice of deposition?
-
How can the audit program be used to summarize audit work performed?
-
What kind of background in data processing do you think an internal auditor should have?
-
Consider the tow important financial statements, the balance sheet (BS) and the income statement (IS). Which of the two would you associate with a snapshot and which with a movie?
-
One of the significant and relevant accounts for this cycle is equipment. For this account, what would typically be the most relevant assertions for the auditor to consider? Why is it important for...
-
Suppose Host A sends two TCP segments back to back to Host B over a TCP connection. The first segment has sequence number 90: the second has sequence number I lo. a. How much data is in the first...
-
How arc different RTP streams in different sessions identified by a receiver? How are different streams from within the same session identified?
-
Equation 1.1 gives a formula for the end-to-end delay of sending one packet of length L over N links of transmission rate R. Generalize this formula for sending P such packets back-to-back over the N...
-
Distinguish between the levels of materiality and per vasiveness an auditor considers when assessing how to deal with a non-GAAP condition in the financial statements.
-
At times, for a variety of reasons, an auditor must rely on another firm of auditors to perform part of an audit. What reference does the primary auditor make to the secondary auditor in the...
-
How does an auditor's opinion differ between scope limitations caused by client restrictions and limitations resulting from conditions beyond the client's control? What is the effect of each on the...

Study smarter with the SolutionInn App


