You've been hired as a network and information security officer for a private IT security firm...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
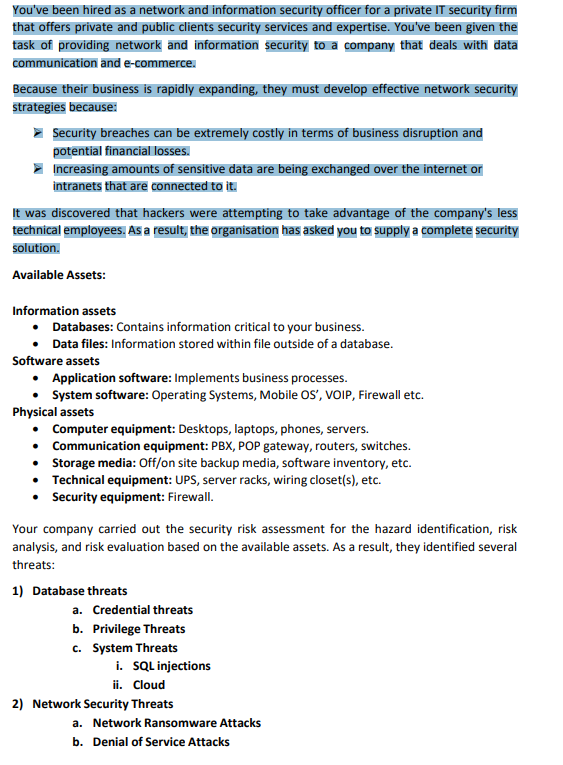
You've been hired as a network and information security officer for a private IT security firm that offers private and public clients security services and expertise. You've been given the task of providing network and information security to a company that deals with data communication and e-commerce. Because their business is rapidly expanding, they must develop effective network security strategies because: ▸ Security breaches can be extremely costly in terms of business disruption and potential financial losses. Increasing amounts of sensitive data are being exchanged over the internet or intranets that are connected to it. It was discovered that hackers were attempting to take advantage of the company's less technical employees. As a result, the organisation has asked you to supply a complete security solution. Available Assets: Information assets • Databases: Contains information critical to your business. • Data files: Information stored within file outside of a database. Software assets Application software: Implements business processes. System software: Operating Systems, Mobile OS', VOIP, Firewall etc. Physical assets Computer equipment: Desktops, laptops, phones, servers. Communication equipment: PBX, POP gateway, routers, switches. • Storage media: Off/on site backup media, software inventory, etc. Technical equipment: UPS, server racks, wiring closet(s), etc. • Security equipment: Firewall. Your company carried out the security risk assessment for the hazard identification, risk analysis, and risk evaluation based on the available assets. As a result, they identified several threats: 1) Database threats a. Credential threats b. Privilege Threats c. System Threats i. SQL injections ii. Cloud 2) Network Security Threats a. Network Ransomware Attacks b. Denial of Service Attacks c. Identity Spoofing d. SSL/TLS Attacks e. Penetration Testing f. Browser Attacks Based on the security risk assessment, your task is to create a report that includes the following information: ➤ Purpose of the Project (Background) > Based on your company's Risk assessment, justify and answer the following questions o Explain briefly about the identified threats (any two from each identified threats) o Based on the identified threats, explain the possible consequences of failing to manage threats. ➤ Propose Solution o Overview of Security Mechanism o Propose a solution, which employs a security mechanism including, cryptographic algorithms, network access control and other possible security solutions. Justify the selection of your security mechanism. o Explain how the company will maintain the security (security policies), considering the CIA triads. o The company has both software and hardware firewalls. Explain the purpose of having both firewalls. Conclusion You've been hired as a network and information security officer for a private IT security firm that offers private and public clients security services and expertise. You've been given the task of providing network and information security to a company that deals with data communication and e-commerce. Because their business is rapidly expanding, they must develop effective network security strategies because: ▸ Security breaches can be extremely costly in terms of business disruption and potential financial losses. Increasing amounts of sensitive data are being exchanged over the internet or intranets that are connected to it. It was discovered that hackers were attempting to take advantage of the company's less technical employees. As a result, the organisation has asked you to supply a complete security solution. Available Assets: Information assets • Databases: Contains information critical to your business. • Data files: Information stored within file outside of a database. Software assets Application software: Implements business processes. System software: Operating Systems, Mobile OS', VOIP, Firewall etc. Physical assets Computer equipment: Desktops, laptops, phones, servers. Communication equipment: PBX, POP gateway, routers, switches. • Storage media: Off/on site backup media, software inventory, etc. Technical equipment: UPS, server racks, wiring closet(s), etc. • Security equipment: Firewall. Your company carried out the security risk assessment for the hazard identification, risk analysis, and risk evaluation based on the available assets. As a result, they identified several threats: 1) Database threats a. Credential threats b. Privilege Threats c. System Threats i. SQL injections ii. Cloud 2) Network Security Threats a. Network Ransomware Attacks b. Denial of Service Attacks c. Identity Spoofing d. SSL/TLS Attacks e. Penetration Testing f. Browser Attacks Based on the security risk assessment, your task is to create a report that includes the following information: ➤ Purpose of the Project (Background) > Based on your company's Risk assessment, justify and answer the following questions o Explain briefly about the identified threats (any two from each identified threats) o Based on the identified threats, explain the possible consequences of failing to manage threats. ➤ Propose Solution o Overview of Security Mechanism o Propose a solution, which employs a security mechanism including, cryptographic algorithms, network access control and other possible security solutions. Justify the selection of your security mechanism. o Explain how the company will maintain the security (security policies), considering the CIA triads. o The company has both software and hardware firewalls. Explain the purpose of having both firewalls. Conclusion
Expert Answer:
Answer rating: 100% (QA)
Project Report Enhancing Network and Information Security Purpose of the Project Background The purpose of this project is to strengthen the network and information security of the client a rapidly ex... View the full answer

Related Book For 

Auditing An International Approach
ISBN: 978-0071051415
6th edition
Authors: Wally J. Smieliauskas, Kathryn Bewley
Posted Date:
Students also viewed these programming questions
-
The upcoming Liability Trading 3 (LT3) case involves accepting or rejecting a series of institutional orders. Suppose that you will accept an institutional sell (buy) order if, following the...
-
This case was written by Professor Michele Greenwald, Visiting Professor of Marketing at HEC Paris, for use with Advertising and Promotion: An Integrated Marketing Communications Perspective 7th...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Can standing waves be formed of transverse waves, longitudinal waves, or both?
-
Distinguish between a calorie and a Calorie.
-
Use the data in Table 1.11 to determine the percentage increase in the CPI between 1978 and 1981. (Do not calculate the annual rate of increase, just the overall percentage increase.) Date Introduced...
-
Using the Internet or print media, find some examples of off-balance sheet ideas.
-
Ridenour Ltd. is preparing its first-quarter monthly cash budget for 2011. The following information is available about actual 2010 sales and expected 2011 sales: Tracing collections from prior year...
-
Wolverine Corp. currently has no existing 4) The ?xed costs. such as overhead expenses. business in New Zealand but is considering to are estimated to be N256 million per year. The establish a subs...
-
To evaluate the quality of its airline service, airline managers want to randomly sample passengers traveling between two large airports. On a particular day, all 578 passengers flying between the...
-
Question 4 Sylvia is the sole shareholder of Strained Ltd., a taxable Canadian corporation. Sylvia transferred a non-depreciable capital property having an adjusted cost base of $40,000 and a fair...
-
For exporters, what is easier, keeping costs low or keeping revenue high? Why?
-
"The "Big Three" global credit rating agenciesU.S.-based Standard and Poor's (S&P), Moody's, and Fitch Rating shave come under intense scrutiny in the wake of the global financial crisis. Meant to...
-
you picked Reliance Industries Limited website: https://www.ril.com/ Indian multinational conglomerate Reliance Industries Limited (RIL) has its headquarters in Mumbai. The corporation works in a...
-
A survey conducted on behalf of the Mental Health Commission of Canada (MHCC), found that many people in Canada have seen their stress levels double since the onset of COVID-19, with fears over...
-
1.Consider the following Treasury bond spot rates r1 = 12%, r5 = 10%, r10 = 8% and r30 =5% (the subscript indicates the year). These rates may be indicative of: i. A decreasing inflation premium ii....
-
Quartz Corporation is a relatively new firm. Quartz has experienced enough losses during its early years to provide it with at least eight years of tax loss carryforwards, so Quartz s effective tax...
-
Give the products of the following reaction, where T is tritium: dioldehydrase Ad- CH CH3C-COH CoIII) coenzyme B12
-
What are some of the specific, relevant aspects of managements control over the production of accounting estimates? What are some enquiries auditors can make?
-
What is the difference between inspection and re-performance in control testing?
-
What is the relationship between business risk and audit risk?
-
What are the characteristics of closed-end mutual funds?
-
Noah is thinking about investing $1,000 in a global mutual fund. However, the fund is a load fund, which charges a commission of 8.5 percent. The investment company would deduct this fee from Noahs...
-
What are three ways in which you can receive income from your mutual fund investments?

Study smarter with the SolutionInn App