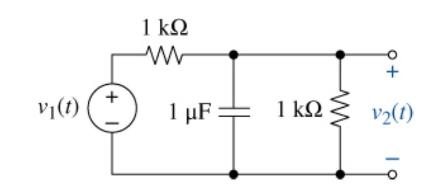
The input in Figure P18-19 is (v_{1}(t)=2 operatorname{sgn}(t) mathrm{V}). Use Fourier transforms to find (v_{2}(t)). V(t) 1
Question:
The input in Figure P18-19 is \(v_{1}(t)=2 \operatorname{sgn}(t) \mathrm{V}\). Use Fourier transforms to find \(v_{2}(t)\).
Transcribed Image Text:
V(t) 1 ww + 1 + 1 F: 1 v2(1) 19
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 0% (1 review)

Answered By

Amar Kumar Behera
I am an expert in science and technology. I provide dedicated guidance and help in understanding key concepts in various fields such as mechanical engineering, industrial engineering, electronics, computer science, physics and maths. I will help you clarify your doubts and explain ideas and concepts that are otherwise difficult to follow. I also provide proof reading services. I hold a number of degrees in engineering from top 10 universities of the US and Europe.
My experience spans 20 years in academia and industry. I have worked for top blue chip companies.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

The Analysis And Design Of Linear Circuits
ISBN: 9781119913023
10th Edition
Authors: Roland E. Thomas, Albert J. Rosa, Gregory J. Toussaint
Question Posted:
Students also viewed these Computer science questions
-
(a) The input in Figure P18-21 is \(v_{1}(t)=3 u(-t) \mathrm{V}\). Use Fourier transforms to find \(v_{2}(t)\). (b) Will the OP AMP saturate? 1 0.1 F ww + V(t) 10 w + V2(t) Vcc = 15 V
-
PLEASE GIVE CORRECT ANSWERS Prove that the number of comparators in any sorting network is (n log n). [4 marks] (ii) What does Part (d)(i) imply in terms of the depth of any sorting network? [1 mark]...
-
The input in Figure P18-22 is \(v_{1}(t)=3 e^{-2|t|} u(-t) \mathrm{V}\). Use Fourier transforms to find \(v_{2}(t)\). 0.1 F 2 10 w ww + + V(1) + V(1)
-
During the software design phase, software engineers define details about the product construction, behavior, components, and interfaces. Explain how you can use the Unified Modeling Language (UML)...
-
In use on a typical human nose, the end-to-end distance is measured to be 30 mm. What force does the strip exert on the nasal passages in this situation? A. 0.23 N B. 0.69 N C. 9.0 N D. 2 N
-
In the simple bending of beams, the bending stress is the beam varies (a) linearly (b) parabolically (c) hyperbolically (d) elliptically
-
Difference and ratio estimation, mean-per-unit estimation, and probability proportional-to-size (PPS) sampling all express sampling results in dollars. How, though, does PPS sampling differ from the...
-
Red Truck Rentals Company faced the following situations. Journalize the adjusting entry needed at December 31, 2014, for each situation. Consider each fact separately. a. The business has interest...
-
Find the absolute maximum and absolute minimum values of the function f(x) = x-6x2 - 63x+9 over each of the indicated intervals. (a) Interval =[-4,0]. 1. Absolute maximum= 2. Absolute minimum = (b)...
-
The input in Figure P18-23 is \(i_{1}(t)=10 e^{-5|t|} \mathrm{mA}\). Use Fourier transforms to find \(i_{2}(t)\). i2(t) i(t) 0.1 uF 10 mH 1
-
The input in Figure P18-19 is \(v_{1}(t)=10 e^{10 t} u(-t)\) V. Use Fourier transforms to find \(v_{2}(t)\). 1 w + V(t) + 1 F 1 V2(1)
-
What are mitigating factors in the context of the going concern assessment? Give some examples of mitigating factors for a loss-making client.
-
Write a query that returns all Employees that have a LastName starting with the letter A . Which WHERE clause should you use ? WHERE LastName = A * O WHERE LastName = LIKE ' % A % ' WHERE LastName...
-
A half adder is implemented with XOR and AND gates. A full adder is implemented with two half adders and one OR gate. The propagation delay of an XOR gate is twice that of an AND / OR gate. The...
-
Four coal mills independently produce sound pressure levels of 94, 94, 96, 93 dBA, respectively. A power plant operator is inspecting the coal mills when they are operating at the same time. What is...
-
Could you elaborate on the implications of regulatory compliance frameworks, such as GDPR in Europe or Dodd-Frank in the United States, on market entry barriers and competitive positioning for...
-
When designing the packaging for your product, what represents all the elements you must consider?
-
Using present value techniques to evaluate alternative investment opportunities Porter Automobile Repair, Inc., currently has three repair shops in Boston. Vincent Porter, the president and chief...
-
In what ways does a well-designed enterprise search software vary from popular search engines (e.g., Bing, DuckDuckGo, and Google)?
-
In Figure 11.11, show what happens in each of the following cases: Figure 11.11 a. The sender is at the ready state and an error-free ACK arrives. b. The sender is at the blocking state and a...
-
In Example 11.3 (Figure 11.12) how many frames are in transit at the same time? Figure 11.12 Receiving node Network Sending node Network Data-link Data-link Packet Frame Legend Packet ACK Start the...
-
In Figure 11.11, show what happens in each of the following cases: Figure 11.11 a. The receiver is in the ready state and a packet comes from the network layer. b. The receiver is in the ready state...
-
Black, an engineer, is injured while visiting the White Manufacturing Company. Black was splattered in the face with hot metal from a die-casting machine which he was observing at the time. What...
-
Fundamental to insider trading is that the practice utilizes an unfair advantage of information not publicly known. This affects stock value, which in turn hurts the company and all shareholders, as...
-
Outline the five different type of intellectual property that's protected through statute law and provide an example of what's protected under each of these types.

Study smarter with the SolutionInn App