Go back

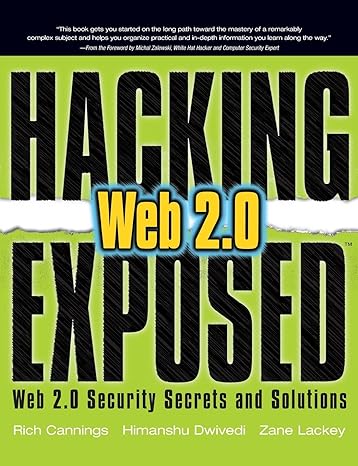
Hacking Exposed Web 2.0 Web 2.0 Security Secrets And Solutions(1st Edition)
Authors:
Rich Cannings ,Himanshu Dwivedi ,Zane Lackey ,Jesse Burns ,Alex Stamos ,Chris Clark
Cover Type:Hardcover
Condition:Used
In Stock
Include with your book
Free shipping: April 30, 2024Popular items with books
Access to 3 Million+ solutions
Free ✝
Ask 10 Questions from expert
200,000+ Expert answers
✝ 7 days-trial
Total Price:
$0
List Price: $4.51
Savings: $4.51(100%)
Book details
ISBN: 0071494618, 978-0071494618
Book publisher: McGraw Hill
Get your hands on the best-selling book Hacking Exposed Web 2.0 Web 2.0 Security Secrets And Solutions 1st Edition for free. Feed your curiosity and let your imagination soar with the best stories coming out to you without hefty price tags. Browse SolutionInn to discover a treasure trove of fiction and non-fiction books where every page leads the reader to an undiscovered world. Start your literary adventure right away and also enjoy free shipping of these complimentary books to your door.