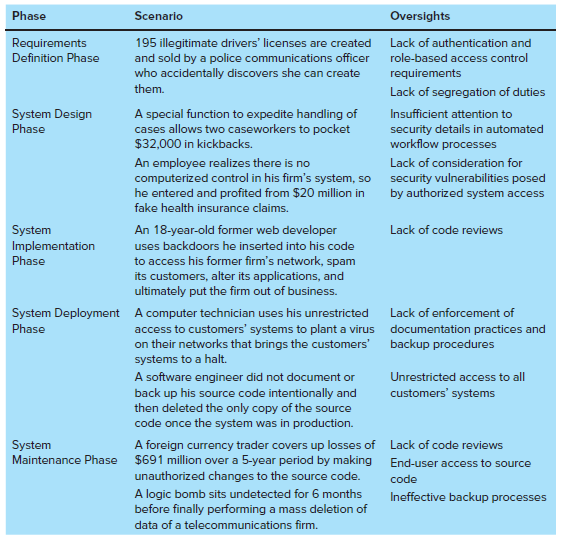
There are five types of fraud schemes in systems development cycles (refer to Figure 12.6)? Identify an
Question:
FIGURE 12.6:
Transcribed Image Text:
Phase Scenario Oversights Requirements Definition Phase 195 illegitimate drivers' licenses are created and sold by a police communications officer who accidentally discovers she can create them. Lack of authentication and role-based access control requirements Lack of segregation of duties System Design A special function to expedite handling of cases allows two caseworkers to pocket $32,000 in kickbacks. Insufficient attention to security details in automated workflow processes Phase An employee realizes there is no computerized control in his firm's system, so he entered and profited from $20 million in Lack of consideration for security vulnerabilities posed by authorized system access fake health insurance claims. An 18-year-old former web developer System Implementation Lack of code reviews uses backdoors he inserted into his code to access his former firm's network, spam its customers, alter its applications, and ultimately put the firm out of business. Phase System Deployment A computer technician uses his unrestricted access to customers' systems to plant a virus on their networks that brings the customers' systems to a halt. Lack of enforcement of Phase documentation practices and backup procedures A software engineer did not document or back up his source code intentionally and then deleted the only copy of the source code once the system was in production. Unrestricted access to all customers' systems System Maintenance Phase A foreign currency trader covers up losses of $691 million over a 5-year period by making Lack of code reviews End-user access to source unauthorized changes to the source code. code A logic bomb sits undetected for 6 months before finally performing a mass deletion of Ineffective backup processes data of a telecommunications firm.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 53% (13 reviews)
a Lack of authentication andor role based acc...View the full answer

Answered By

Aun Ali
I am an Associate Member of Cost and Management Accountants of Pakistan with vast experience in the field of accounting and finance, including more than 17 years of teaching experience at university level. I have been teaching at both undergraduate and post graduate levels. My area of specialization is cost and management accounting but I have taught various subjects related to accounting and finance.
5.00+
13+ Reviews
32+ Question Solved
Related Book For 

Accounting Information Systems
ISBN: 978-1260153156
2nd edition
Authors: Vernon Richardson, Chengyee Chang, Rod Smith
Question Posted:
Students also viewed these Business questions
-
There are five types of management earnings techniques presented in this chapter. Provide two or three specific examples of how corporate leaders could pull off these types of fraud, as well as the...
-
There are five types of boxes whose sizes and demands are given in the table below. The unit cost of a box is equal to its size, and there is an initial cost of $100 to produce each type of box....
-
What are the five types of analytical procedures? Briefly discuss each. There are five types of analytical procedures: (1) Those ratios that compare client and industry data; (2) Ratios that compare...
-
Data visualization can help Broadway theatre analysts to understand ticket pricesExample: Recall the Service Company Insight box How Much Did You Pay for That Seat? presented in the chapter. As...
-
Find g'(x) if g(x) = 1/ x3 - 4x.
-
The unadjusted trial balance of The Rock Industries Ltd. at January 31, 2017, appears below. Adjustment data: a. Accrued service revenue at January 31, $2,000 b. Prepaid rent expired during the...
-
Bruce is a high school senior with a busy fall schedule. He saved enough money to start investing, but he has no time to monitor his investments or make decisions. He wants to let his account...
-
You are provided with the following information for Aylesworth Inc. for the month ended October 31, 2012. Aylesworth uses a periodic method for inventory. Instructions(a) Calculate (i) ending...
-
Required information [The following information applies to the questions displayed below.] Incentive Corporation was authorized to issue 12,000 shares of common stock, each with a $1 par value....
-
V. N. Murti and V. K. Sastri investigated the production characteristics of various Indian industries, including cotton and sugar. They specified CobbDouglas production functions for output (Q) as a...
-
Internal auditors are often tasked with testing vulnerabilities. How would you suggest testing for system intrusion, logical access control, natural disasters, and intentional destruction of...
-
Identify the main components of vulnerability management and assessment? Component a. Prioritize vulnerabilities b. Design a risk response plan c. Monitor vulnerabilities d. Establish policy and...
-
In stating objectives, why should terms such as increase, minimize, maximize, as soon as possible, adequate, and decrease be avoided?
-
If f(x) = 25x + 7, find f'(1).
-
e-Gadget Production (2013) Most common companies that sell electronic devices do not handle their own manufacturing. Production of devices such as cell phones, televisions, and head- sets is handled...
-
Code a method called encrypt to encrypt a String by swapping each pair of its adjacent characters. In the case of Strings with an odd number of characters pad them with a trailing space before...
-
SolarCity retained investment bank Lazard Freres & Co. LLC to help with its valuation and help it evaluate Tesla's offer. SolarCity management projections of net cash flow ($millions): FY2016 FY2017...
-
Larissa leases to Metal Fabrication Corporation a 10,000 square-foot building under a written lease with a twenty-year term, rent payable annually. The lease includes a clause stating that Metal...
-
Financial information for Buckle is presented in Appendix B at the end of the book. Required: 1. The summary of significant accounting policies is located in note A to the financial statements....
-
Consider the following cash flows in Table P5.5. (a) Calculate the payback period for each project. (b) Determine whether it is meaningful to calculate a payback period for project D. (c) Assuming...
-
Why are program change procedures important to auditors?
-
What is the importance of the SPL?
-
What functions does the SPLMS control?
-
Compensating balances: A. are ordered monthly (or quarterly) following forecasts based on cash budget analysis to compensate for shortfalls B. require a commitment fee C. earn high rates of interest...
-
Minimizing bond portfolio duration dispersion is not optimal if: a.Portfolio dispersion exceeds Liability dispersion b.Liability dispersion exceeds Portfolio dispersion c.Liability and Portfolio...
-
Eliminating options that are identified as being incorrect right away is a good strategy. The following are some options that can be eliminated except: Options that mean the same but worded...

Study smarter with the SolutionInn App