The IEEE Software Engineering Code of Ethics uses eight key principles shown in the right-hand column of
Question:
The IEEE Software Engineering Code of Ethics uses eight key principles shown in the right-hand column of the following diagram.
Tom is employed as a tester with a software company. He is keen to become a trainee programmer.
The middle column in the diagram labels six incidents which have happened to tom this week. The table that follows the diagram describes each incident.
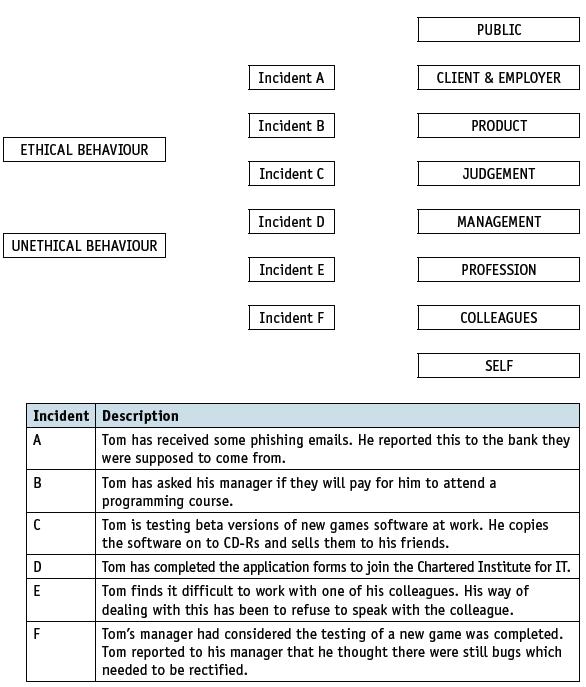
a) Copy the diagram above and connect each of the six incidents to either ethical behaviour or unethical behaviour.
b) Consider each incident you have identified as ethical behaviour. Indicate the IEE category each incident maps to.
Transcribed Image Text:
PUBLIC Incident A CLIENT & EMPLOYER Incident B PRODUCT ETHICAL BEHAVIOUR Incident C JUDGEMENT Incident D MANAGEMENT UNETHICAL BEHAVIOUR Incident E PROFESSION Incident F COLLEAGUES SELF Incident Description A Tom has received some phishing emails. He reported this to the bank they were supposed to come from. B Tom has asked his manager if they will pay for him to attend a programming course. Tom is testing beta versions of new games software at work. He copies the software on to CD-Rs and sells them to his friends. Tom has completed the application forms to join the Chartered Institute for IT. Tom finds it difficult to work with one of his colleagues. His way of dealing with this has been to refuse to speak with the colleague. E F Tom's manager had considered the testing of a new game was completed. Tom reported to his manager that he thought there were still bugs which needed to be rectified.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 80% (10 reviews)
a IEEE Software Engineering Code of Ethics Incident EthicalUnethical Behavior Responsibil...View the full answer

Answered By

James Warinda
Hi! I’m James Otieno and I'm an experienced professional online tutor with countless hours of success in tutoring many subjects in different disciplines. Specifically, I have handled general management and general business as a tutor in Chegg, Help in Homework and Trans tutor accounts.
I believe that my experience has made me the perfect tutor for students of all ages, so I'm confident I can help you too with finding the solution to your problems. In addition, my approach is compatible with most educational methods and philosophies which means it will be easy for you to find a way in which we can work on things together. In addition, my long experience in the educational field has allowed me to develop a unique approach that is both productive and enjoyable.
I have tutored in course hero for quite some time and was among the top tutors awarded having high helpful rates and reviews. In addition, I have also been lucky enough to be nominated a finalist for the 2nd annual course hero award and the best tutor of the month in may 2022.
I will make sure that any student of yours will have an amazing time at learning with me, because I really care about helping people achieve their goals so if you don't have any worries or concerns whatsoever you should place your trust on me and let me help you get every single thing that you're looking for and more.
In my experience, I have observed that students tend to reach their potential in academics very easily when they are tutored by someone who is extremely dedicated to their academic career not just as a businessman but as a human being in general.
I have successfully tutored many students from different grades and from all sorts of backgrounds, so I'm confident I can help anyone find the solution to their problems and achieve
0.00
0 Reviews
10+ Question Solved
Related Book For 

Cambridge International AS & A Level Computer Science
ISBN: 9781510457591
1st Edition
Authors: David Watson, Helen Williams
Question Posted:
Students also viewed these Computer science questions
-
Which clauses in the Software Engineering Code of Ethics and Professional Practice support the legitimacy of whistle-blowing? Which clauses in the code may be violated by a whistle-blower (assuming...
-
In 2016, Micah Johnson (SSN 000-22-1111) is employed as a manager and incurs the following unreimbursed employee business expenses: Airplane and taxi fares ..$ 4,000 Lodging away from home ...5,000...
-
In 2017, Micah Johnson (SSN 000-22-1111) is employed as a manager and incurs the following unreimbursed employee business expenses: Johnson receives a $7,800 reimbursement for the travel expenses. He...
-
Assume that 3-month Treasury bills totaling $23 billion were sold in $10,000 denominations at a discount rate of 5.200%. In addition, the Treasury Department sold 6-month bills totaling $21 billion...
-
What is the minimal sample size needed for a 99% confidence interval to have a maximal margin of error of 0.06: (a) If a preliminary estimate for p is 0.8? (b) If there is no preliminary estimate for...
-
Restaurants do a large volume of business by credit cards and bankcards. Suppose a Chili's restaurant had these transactions on a Saturday: Suppose American Express charges merchants \(2 \%\) and...
-
During the past year, Lite Company had net income of \(\$ 5\) million, and Scanlon Company had net income of \(\$ 8\) million. Both companies manufacture electrical components for the construction...
-
Figure 4-32 shows a class list for Millennium College. Convert this user view to a set of 3NF relations using an enterprise key. Assume the following: ¢ An instructor has a unique location....
-
You are given the following information concerning three portfolios, the market portfolio, and the risk - free asset: Portfolio RP \ sigma P \ beta P X 1 4 . 0 0 % 3 1 . 0 0 % 1 . 3 5 Y 1 3 . 0 0 2 6...
-
The proposed rates were not in the range the CEO expected given the pricing analysis. The CEO has asked the pricing actuary to verify the total projected loss cost excluding potential large storm...
-
a) Computers over the years have been described as first to fifth generation. Identify the generation that is associated with AI. A. First B. Second C. Third D. Fourth E. Fifth b) AI is involved in...
-
A database has been designed to store data about programmers and the programs they have developed. These facts help to define the structure of the database: Each programmer works in a particular...
-
Effluents from metal-finishing plants have the potential of discharging undesirable quantities of metals, such as cadmium, nickel, lead, manganese, and chromium, in forms that are detrimental to...
-
Select any publicly traded company and obtain its most recent 10-K filing (within the last two years). Assume that you have been assigned as the auditor for this company. Choose one of the topics...
-
On January 26, Bella Co. borrowed cash from Conrad Bank by issuing a 30-day note with a face amount of $44,400. Assume a 360-day year. a. Determine the proceeds of the note, assuming the note carries...
-
1. What is the expected boiling point (neglecting ionpairing) of a 0.250 m aqueous Na3PO4 solution (at 1 atm atmosphericpressure)? (ans is 100.512 C, not sure how to getthere) 2. Find the osmotic...
-
When companies offer new debt security issues, they publicize the offerings in the financial press and on Internet sites. Assume the following were among the debt offerings reported in December 2024:...
-
A portion of the statement of earnings for Tea Company is shown below. Provide the missing account titles and amounts. A. Sales returns and allowances C. D. Gross Margin $110,000 B. $100,000 $25,000
-
For a recent year, McDonald's company-owned restaurants had the following sales and expenses (in millions): Sales....................................................$18,169.3 Food and...
-
Research corporate acquisitions using Web resources and then answer the following questions: Why do firms purchase other corporations? Do firms pay too much for the acquired corporation? Why do so...
-
When silicon chips are fabricated, defects in materials (e.g., silicon) and manufacturing errors can result in defective circuits. A very common defect is for one wire to affect the signal in...
-
In this exercise, we examine how pipelining affects the clock cycle time of the processor. Problems in this exercise assume that individual stages of the datapath have the following latencies: Also,...
-
In this exercise, we examine how data dependences affect execution in the basic 5-stage pipeline described in Section 4.5. Problems in this exercise refer to the following sequence of instructions:...
-
In a small town of 5,832 people, the mayor claims that there is a difference in the proportion of voters ages 18-30 who would support an increase in the food tax and the proportion of voters ages...
-
Suppose that the continuously compounding annualized interest rate is 10% and that the price of a S&R stock is $1,000. a. Suppose that you are offered a one-year long forward contract on S&R stocks...
-
Foundation, Incorporated, is comparing two different capital structures: an all - equity plan ( Plan I ) and a levered plan ( Plan II ) . Under Plan I, the company would have 1 6 0 , 0 0 0 shares of...

Study smarter with the SolutionInn App