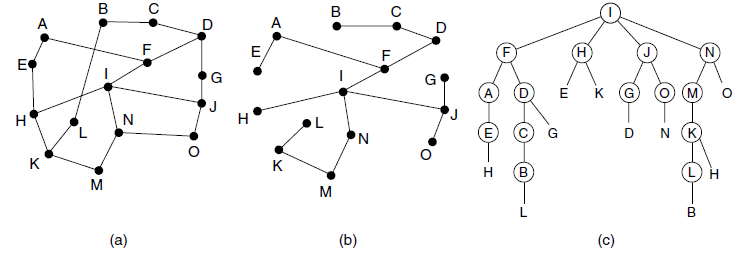
Consider the network of Fig. 5-15(a). Imagine that one new line is added, between F and G,
Question:
Figure 5-15
Transcribed Image Text:
A A D (н G к G M) н (E D N (K K к н M (a) (b) (c) ш
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (9 reviews)
Node F currently has two descendants A and D It now ac...View the full answer

Answered By

Rohith Bellamkonda
I am studying in IIT Indore,the most prestigious institute of India.I love solving maths and enjoy coding
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Consider the network of Fig. 5-12(a). Distance vector routing is used, and the following vectors have just come in to router C: from B: (5, 0, 8, 12, 6, 2); from D: (16, 12, 6, 0, 9, 10); and from E:...
-
Consider the network of Fig. 4-49(a). If machine J were to suddenly become white, would any changes be needed to the labeling? If so what?
-
Consider the network of Fig. 5-7, but ignore the weights on the lines. Suppose that it uses flooding as the routing algorithm. If a packet sent by A to D has a maximum hop count of 3, list all the...
-
Find the median and the mode for the following data: 65, 66, 66, 70, 71, 72, 72, 72, 78, 83, 85, 86, 87, 87, 88, 88, 92, 93, 95, 95, 99, 100, 102, 102, 102, 102, 102, 103, 104, 108, 111, 113, 118,...
-
What type of report should be issued when auditors are not independent with respect to the entity?
-
Tapas Corporation has leased a piece of equipment that has a usefull life of 12 years. The terms of the lease are payments of $43,000 per year for 12 years. Tapas currently is able to borrow money at...
-
The procedure for testing homogeneity is the same as the procedure for testing independence. In Exercises 68, determine whether the statement is true or false. If the statement is false, rewrite it...
-
The accountant of Kooks Shoe Co. has compiled the following information from the companys records as a basis for an income statement for the year ended December 31, 2008. Rental revenue...
-
Johnstone Brewers Inc. uses the FIFO method in its process costing system. The concern the operations of the company's first processing department for a recent Work in process, beginning: Units in...
-
Please complete the 2018 federal income tax return for Tim and Linda Jones. Ignore the requirement to attach the form(s) W-2 to the front page of the Form 1040. If required information is missing,...
-
In Fig. 5-13 the Boolean OR of the two sets of ACF bits are 111 in every row. Is this just an accident here, or does it hold for all networks under all circumstances? Figure 5-13 Send flags ACK flags...
-
Compute a multicast spanning tree for router C in the following network for a group with members at routers A, B, C, D, E, F, I, and K. D A
-
What is the purpose of the Retained Earnings account, and what business events cause it to change during the year?
-
How IP Will traced if I Will Use VPN Because VPN make a Fake Wall Which are Called Fake IP Explain How IP will actually traced if i will use VPN.
-
A bakery makes two types of birthday cakes: chocolate cake which sells for $25, and strawberry cake which sells for $35. Each chocolate cake takes 2 hours to make while the strawberry cake takes 3...
-
Six grocery items have the following prices: $5.82, $10.28, $8.51, $12.13, $6.64, and $11.77. (a) Estimate the total cost of the six items by rounding each price to the nearest dollar, then adding....
-
Evalue ! d2 , 2(2+in) , where c is circle. 12+3:1 F1 by using cauchy's Integral. formula.
-
In Europe, the floor of a building at ground level is called the ground floor. What is called the second floor in America is called the first floor in Europe, and so on. (a) If an elevator in a tall...
-
Determine the truth value for each simple statement. Then use these truth values to determine the truth value of the compound statement. Chevrolet makes trucks or Toyota makes shoes.
-
Consider the advantages and disadvantages of extending property rights so that everyone would have the right to prevent people imposing any costs on them whatsoever (or charging them to do so).
-
The following exercise is concerned with the TCP state FIN_WAIT_2 (see Figure 5.7). (a) Describe how a client might leave a suitable server in state FIN_WAIT_2 indefinitely. What feature of the...
-
TCP is a very symmetric protocol, but the client/server model is not. Consider an asymmetric TCP-like protocol in which only the server side is assigned a port number visible to the application...
-
TCPs simultaneous open feature is seldom used. (a) Propose a change to TCP in which this is disallowed. Indicate what changes would be made in the state diagram (and, if necessary, in the...
-
Rex Metal Fabricators (RMF) buys scrap metal and produces components for buildings and other structures. The purchase contracts specify an average quality level of 86 percent. That is, 86 percent of...
-
The SafeMessage System is a secure instant messaging system that provides various levels of secure communication between individuals over the Internet. A secure instant messaging system integrates...
-
Design a 3-bit INCrementor, that is, the circuit generates the next number after the input number (e.g., 011100. Also, 111 000): a) Show the truth table. b) Show the Boolean expressions for the...

Study smarter with the SolutionInn App


