There is a mknod system call in Fig. 1-16 but there is no rmnod call. Does this
Question:
There is a mknod system call in Fig. 1-16 but there is no rmnod call. Does this mean that you have to be very, very careful about making nodes this way because there is no way to every remove them?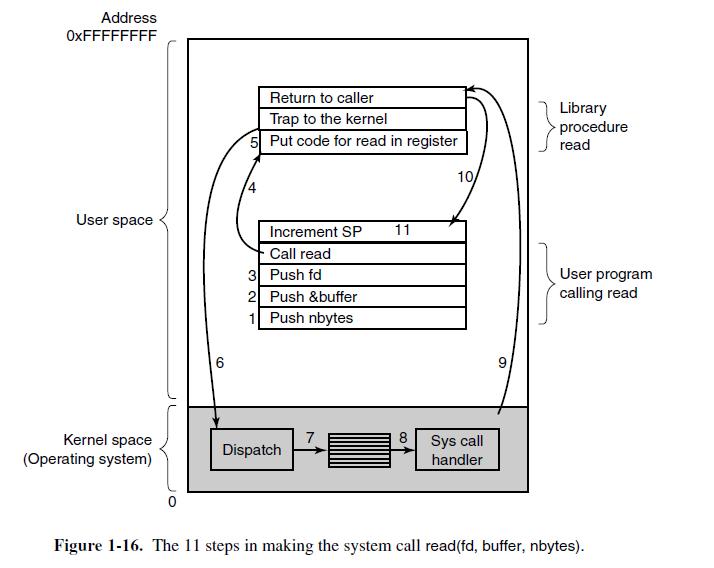
Transcribed Image Text:
Address OxFFFFFFFF User space Kernel space (Operating system) 6 Return to caller Trap to the kernel 5 Put code for read in register Increment SP 11 - Call read 3 Push fd 2 1 Push &buffer Push nbytes Dispatch 7 8 10/ Sys call handler 6 Library procedure read User program calling read Figure 1-16. The 11 steps in making the system call read(fd, buffer, nbytes).
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 40% (5 reviews)
Yes it is true that you have to be very careful about making nodes with the mknod system call becaus...View the full answer

Answered By

Antony Sang
I am a research and academic writer whose work is outstanding. I always have my customer's interests at heart. Time is an important factor in our day to day life so I am always time conscious. Plagiarism has never been my thing whatsoever. I give best Research Papers, Computer science and IT papers, Lab reports, Law, programming, Term papers, English and literature, History, Math, Accounting, Business Studies, Finance, Economics, Business Management, Chemistry, Biology, Physics, Anthropology, Sociology, Psychology, Nutrition, Creative Writing, Health Care, Nursing, and Articles.
5.00+
2+ Reviews
10+ Question Solved
Related Book For 

Operating Systems Design And Implementation
ISBN: 9780131429383
3rd Edition
Authors: Andrew Tanenbaum, Albert Woodhull
Question Posted:
Students also viewed these Computer science questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
John Peters had just arrived at the Memphis branch offices of Bull Steins (BS) brokerage firm. BS is one of the top 50 firms in the industry with a wide range of financial products. Five years prior,...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
In Canada, Canadian teachers and bosses and HIGH AUTHORITY FIGURES are not FEARED but RESPECTED. In CANADA TEACHERS, bosses and AUTHORITY FIGURES encourage feedback, OPINIONS and ENGAGE in discuss....
-
The notes to the Helping Charities financial statements reported the following data on December 31, Year 1 (end of the fiscal year): Helping Charities amortizes bonds by the effective-interest method...
-
Let W, Z be complementary subspaces of a vector space V, as in Exercise 2.2.24. Let V/W denote the quotient vector space, as defined in Exercise 2.2.29. Show that the map L:Z V/W that maps L[z] =...
-
Why does it take strength to admit one is wrong? Why must a transformational leader be willing to admit responsibility? Perry was one of the worst bosses Lia had ever worked for. Perry had arrived...
-
The following information is available for Lowry Company. Instructions (a) Compute cost of goods manufactured. (b) Prepare an income statement through gross profit. (c) Show the presentation of the...
-
1) the 5r do + 2xydy\f
-
Suppose that a computer can execute 1 billion instructions/sec and that a system call takes 1000 instructions, including the trap and all the context switching. How many system calls can the computer...
-
Why is the chroot system call limited to the superuser?
-
Sheen Company reported these income statement data for a 2-year period. Sheen Company uses a periodic inventory system. The inventories at January 1, 2021, and December 31, 2022, are correct....
-
Flying High Pies manufactures gourmet pies for speciality restaurants. The vegetarian filling of the pie is made by the mixing division and is then transferred to the baking division. At the baking...
-
What role does the cost allocation method (which is already in place) play in the method of revenue allocation? Which method would division managers prefer?
-
heat up two slices of pizza in the oven. Each slice has a mass of 1 0 0 g . The pizza ( cheese ) is initially solid at a temperature of 3 9 . 2 F . I place the pizza slices in a 3 5 0 F preheated...
-
In both last year and this year, Karol contributed $ 5 , 0 0 0 to the spousal RRSP of his wife, Magda. At the end of this year, Magda transferred $ 6 , 0 0 0 from her spousal RRSP to a spousal RRIF....
-
A manufacturing plant draws a sample of 28 screws from the production line and finds their diameter has a mean of 4.06 cm and a standard deviation of 0.39 cm. What is the 99% confidence interval for...
-
Economists sometimes make each of the following assumptions when they construct models. Discuss some situations in which each of these assumptions might be a useful simplification in order to think...
-
What is the difference between direct materials and indirect materials?
-
Show how to implement the stack ADT using only a priority queue and one additional integer instance variable.
-
Hillary claims that a postorder traversal of a heap will list its keys in nonincreasing order. Draw an example of a heap that proves her wrong.
-
Bill claims that a preorder traversal of a heap will list its keys in nondecreasing order. Draw an example of a heap that proves him wrong.
-
PROBLEM TO RESOLVE - CVP 8 . Goya Company manufactured 1 0 0 , 0 0 0 units in 2 0 1 8 and reported the following costs: Sandpaper $ 3 2 , 0 0 0 Leasing costs - plant $ 3 8 4 , 0 0 0 Materials...
-
Explore the allocation methods used by Microsoft Corporation in its manufacturing processes. Last quarter, Microsoft incurred total costs of $12,000,000. The manufacturing division operated for...
-
Compute Book Value per Share: Requirements: With the given balance sheet data: Common Stock: $200,000 Total Equity: $900,000 Outstanding Shares: 80,000 Calculate the book value per share. Express the...

Study smarter with the SolutionInn App