2. In Diffie-Hellman key exchange, each user chooses a private X, calculates a public Y, and...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
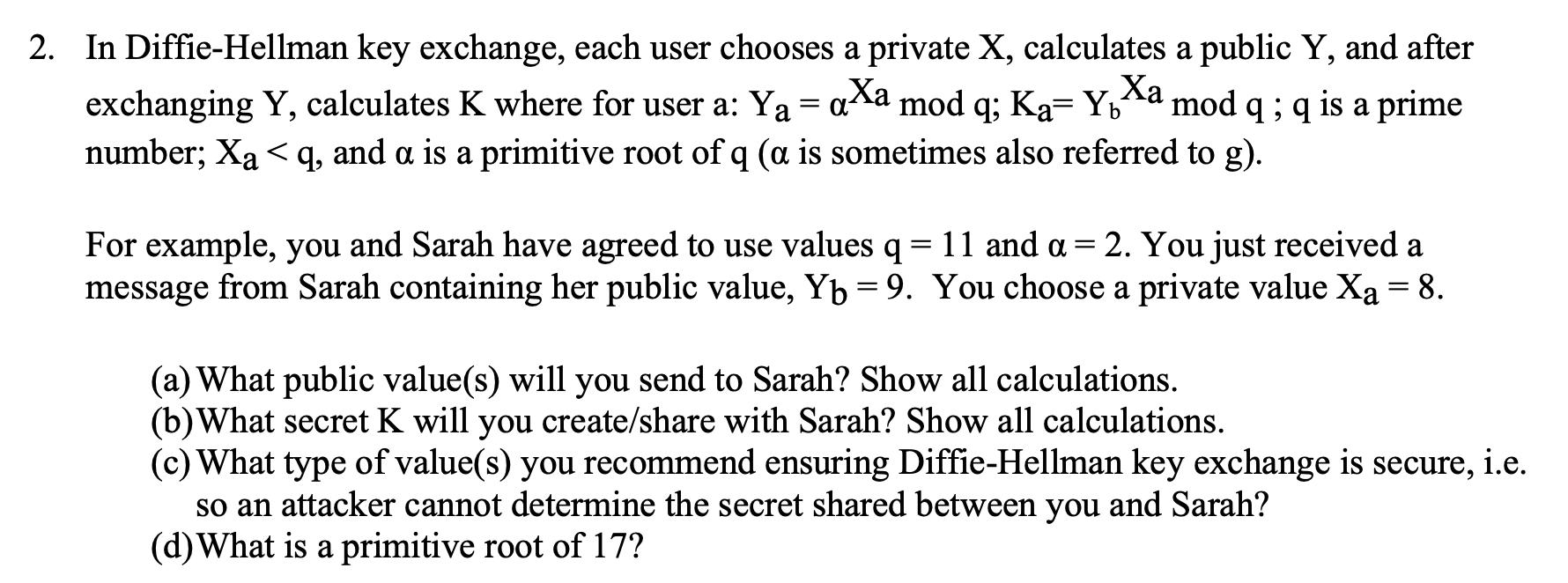
2. In Diffie-Hellman key exchange, each user chooses a private X, calculates a public Y, and after exchanging Y, calculates K where for user a: Y = axa mod q; Ka= Yxa mod q ; q is a prime number; Xaq, and a is a primitive root of q (a is sometimes also referred to g). Ya Yb For example, you and Sarah have agreed to use values q = 11 and a = 2. You just received a message from Sarah containing her public value, Yb = 9. You choose a private value Xa = 8. (a) What public value(s) will you send to Sarah? Show all calculations. (b) What secret K will you create/share with Sarah? Show all calculations. (c) What type of value(s) you recommend ensuring Diffie-Hellman key exchange is secure, i.e. so an attacker cannot determine the secret shared between you and Sarah? (d) What is a primitive root of 17? 2. In Diffie-Hellman key exchange, each user chooses a private X, calculates a public Y, and after exchanging Y, calculates K where for user a: Y = axa mod q; Ka= Yxa mod q ; q is a prime number; Xaq, and a is a primitive root of q (a is sometimes also referred to g). Ya Yb For example, you and Sarah have agreed to use values q = 11 and a = 2. You just received a message from Sarah containing her public value, Yb = 9. You choose a private value Xa = 8. (a) What public value(s) will you send to Sarah? Show all calculations. (b) What secret K will you create/share with Sarah? Show all calculations. (c) What type of value(s) you recommend ensuring Diffie-Hellman key exchange is secure, i.e. so an attacker cannot determine the secret shared between you and Sarah? (d) What is a primitive root of 17?
Expert Answer:
Answer rating: 100% (QA)
Lets break down each part of the DiffieHellman key exchange scenario Public Value for Sarah Yb You r... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these programming questions
-
On February 14, 2012, Therese Company established a sales agency in Tagbilaran. Upon establishment of the sales agency, the home office sent samples costing P8,000 and a working fund of P3,000 to be...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Travis owned a home with a first mortgage dated Oct. 1, 2000. On May 1, 2014, Travis took out a home equity loan (second mortgage). He then hired Builder Company to build a swimming pool at the home....
-
Reading material Raymond Frost, Alexa K. Fox & Judy Strauss (2019). Product: The Online Offer. E-Marketing , 9, 206 - 228. Raymond Frost, Alexa K. Fox & Judy Strauss (2019). Price: The Online Value....
-
p-Nitrophenyl esters are made from Z-protected amino acids by reaction with p-nitrophenol in the presence of N,N-dicyclohexylcarbodiimide. Suggest a reasonable mechanism for this reaction.
-
Briefly describe design classes: utility, control, and boundary. How do they differ from entity classes?
-
Suppose the exchange rate for the Swiss franc is quoted as SF 1.50 in the spot market and SF 1.53 in the 90-day forward market. a. Is the dollar selling at a premium or a discount relative to the...
-
Louisville Sports manufactures baseball bats for use by players in the major leagues. A critical requirement for elite players is that each bat they use have an identical look and feel. As a result,...
-
2. James Consol Company currently pays a dividend of$1.60 per share on its common stock.The company expects to increase the dividend at a 20 percent annualrate for the first fouryears and at a 13 2...
-
Auditors would use financial analysis to ________________. Question content area bottom Part 1 A. compare with other companies for accuracy B. analyze stock investment C. determine credit risk D....
-
A bank estimates that their average balance on demand deposit accounts is $ 1 , 6 2 0 , net of float. Each account costs the bank $ 1 7 7 per year in processing costs. The bank collects an average of...
-
Steam enters a well-insulated turbine operating at steady state at 4 MPa with a specific enthalpy of 2961.0 kJ/kg and a velocity of 12 m/s. The steam expands to the turbine exit where the pressure is...
-
An Axis Pension investment adviser is helping you to plan your retirement portfolio. The adviser has recommended three stocks namely; Goil, Ecobank, and Fan Milk. The information provided in Tables 2...
-
The Annual Return is the average Annual Percentage Yield ( APY ) of an investment over a - year time period. Annual Return Christa pays $ 9 , 5 0 0 for shares in a new company. She sells the shares 1...
-
A vendor offers a 1 5 % discount on orders greater than and including 5 0 0 0 . If your store needs to order 4 0 0 0 units at $ 4 . 0 0 each, should you increase the order to get the discount? Why or...
-
Explore the applications of Building Information Modeling (BIM) and integrated project delivery (IPD) methodologies in enhancing collaboration and coordination among multidisciplinary project teams,...
-
What did Lennox gain by integrating their WMS, TMS, and labor management systems?
-
Which statement is false? a. Waste Management made top drawer entries. b. Richard Scrushy of Tyco was never convicted. c. Adelphia used special purpose entities to commit their fraud. d....
-
Which statement is false? a. SASNo. 99 does not prohibit clients from preparing confirmations. b. Enron issued \(\$ 1.2\) billion of stock to an SPE and recorded a \(\$ 1.2\) billion notes...
-
Who is responsible for internal controls? a. External auditors b. Internal auditors c. Management d. Audit Committee e. Board of Directors

Study smarter with the SolutionInn App


